11 KiB
Objection Tutorial
🎙️ HackTricks LIVE Twitch Wednesdays 5.30pm (UTC) 🎙️ - 🎥 Youtube 🎥
- Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access to the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
- Discover The PEASS Family, our collection of exclusive NFTs
- Get the official PEASS & HackTricks swag
- Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
- Share your hacking tricks by submitting PRs to the hacktricks repo and hacktricks-cloud repo.

Bug bounty tip: sign up for Intigriti, a premium bug bounty platform created by hackers, for hackers! Join us at https://go.intigriti.com/hacktricks today, and start earning bounties up to $100,000!
{% embed url="https://go.intigriti.com/hacktricks" %}
Introduction
objection - Runtime Mobile Exploration
objection is a runtime mobile exploration toolkit, powered by Frida. It was built with the aim of helping assess mobile applications and their security posture without the need for a jailbroken or rooted mobile device.
Note: This is not some form of jailbreak / root bypass. By using objection, you are still limited by all of the restrictions imposed by the applicable sandbox you are facing.
Resume
The goal of objection is let the user call the main actions that offers Frida. Otherwise, the user will need to create a single script for every application that he wants to test.
Tutorial
For this tutorial I am going to use the APK that you can download here:
{% file src="../../../.gitbook/assets/app-release.zip" %}
Or from its original repository (download app-release.apk)
Installation
pip3 install objection
Connection
Make a regular ADB conection and start the frida server in the device (and check that frida is working in both the client and the server).
If you are using a rooted device it is needed to select the application that you want to test inside the --gadget option. in this case:
objection --gadget asvid.github.io.fridaapp explore
Basic Actions
Not all possible commands of objections are going to be listed in this tutorial, only the ones that I have found more useful.
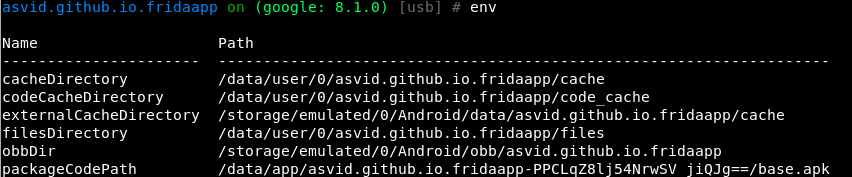
Environment
Some interesting information (like passwords or paths) could be find inside the environment.
env
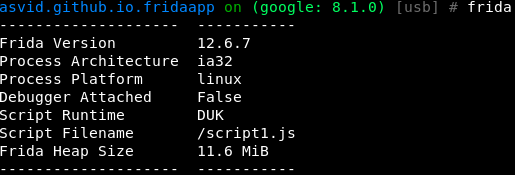
Frida Information
frida
Upload/Download
file download <remote path> [<local path>]
file upload <local path> [<remote path>]
Import frida script
import <local path frida-script>
SSLPinning
android sslpinning disable #Attempts to disable SSL Pinning on Android devices.
Root detection
android root disable #Attempts to disable root detection on Android devices.
android root simulate #Attempts to simulate a rooted Android environment.
Exec Command
android shell_exec whoami
Screenshots
android ui screenshot /tmp/screenshot
android ui FLAG_SECURE false #This may enable you to take screenshots using the hardware keys
Static analysis made Dynamic
In a real application we should know all of the information discovered in this part before using objection thanks to static analysis. Anyway, this way maybe you can see something new as here you will only have a complete list of classes, methods and exported objects.
This is also usefull if somehow you are unable to get some readable source code of the app.
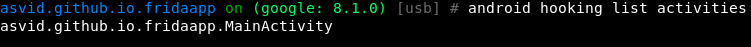
List activities, receivers and services
android hooking list activities
android hooking list services
android hooking list receivers
Frida will launch an error if none is found
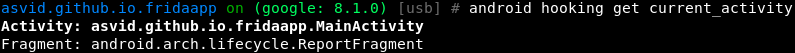
Getting current activity
android hooking get current_activity
Search Classes
Lets start looking for classes inside our application
android hooking search classes asvid.github.io.fridaapp
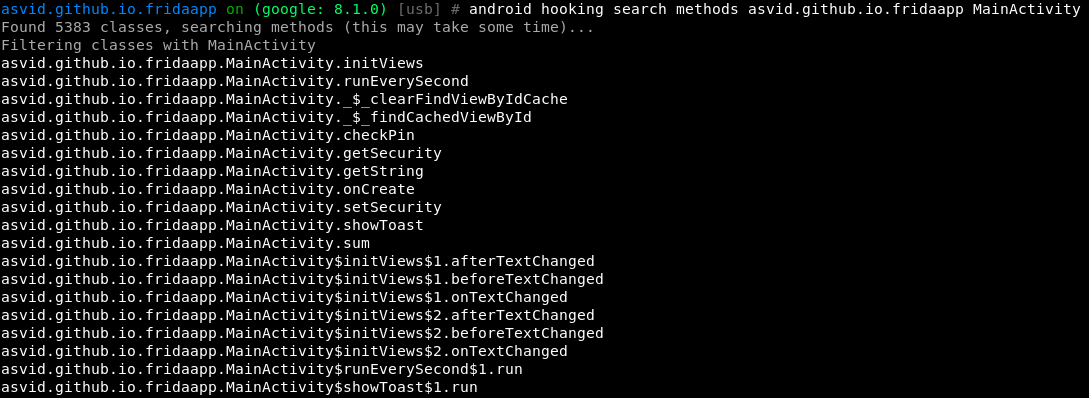
Search Methods of a class
Now lets extract the methods inside the class MainActivity:
android hooking search methods asvid.github.io.fridaapp MainActivity
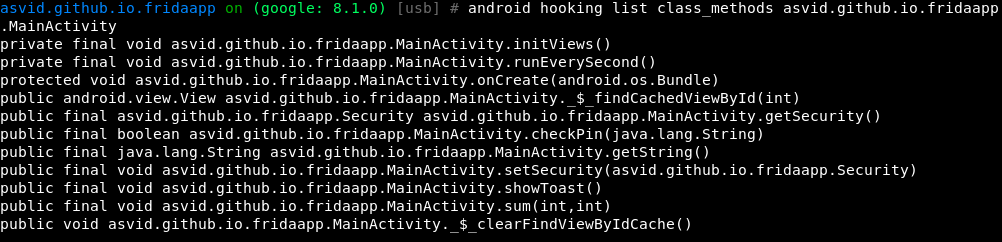
List declared Methods of a class with their parameters
Lets figure out wich parameters does the methods of the class need:
android hooking list class_methods asvid.github.io.fridaapp.MainActivity
List classes
You could also list all the classes that were loaded inside the current applicatoin:
android hooking list classes #List all loaded classes, As the target application gets usedmore, this command will return more classes.
This is very useful if you want to hook the method of a class and you only know the name of the class. You coul use this function to search which module owns the class and then hook its method.
Hooking being easy
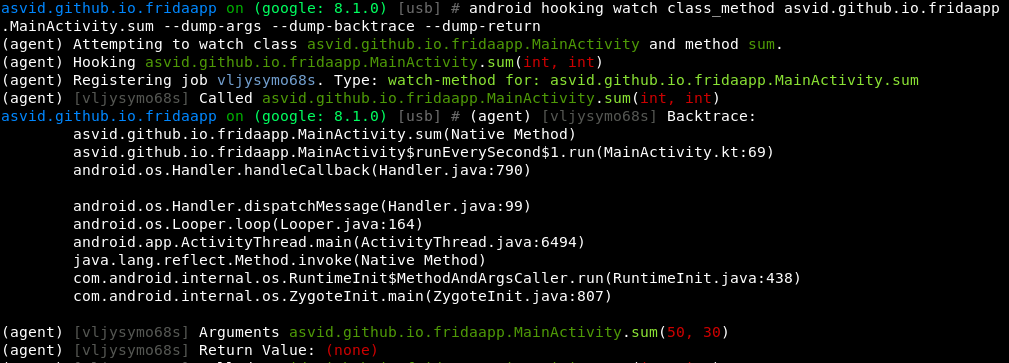
Hooking (watching) a method
From the source code of the application we know that the function sum() from MainActivity is being run every second. Lets try to dump all possible information each time the function is called (arguments, return value and backtrace):
android hooking watch class_method asvid.github.io.fridaapp.MainActivity.sum --dump-args --dump-backtrace --dump-return
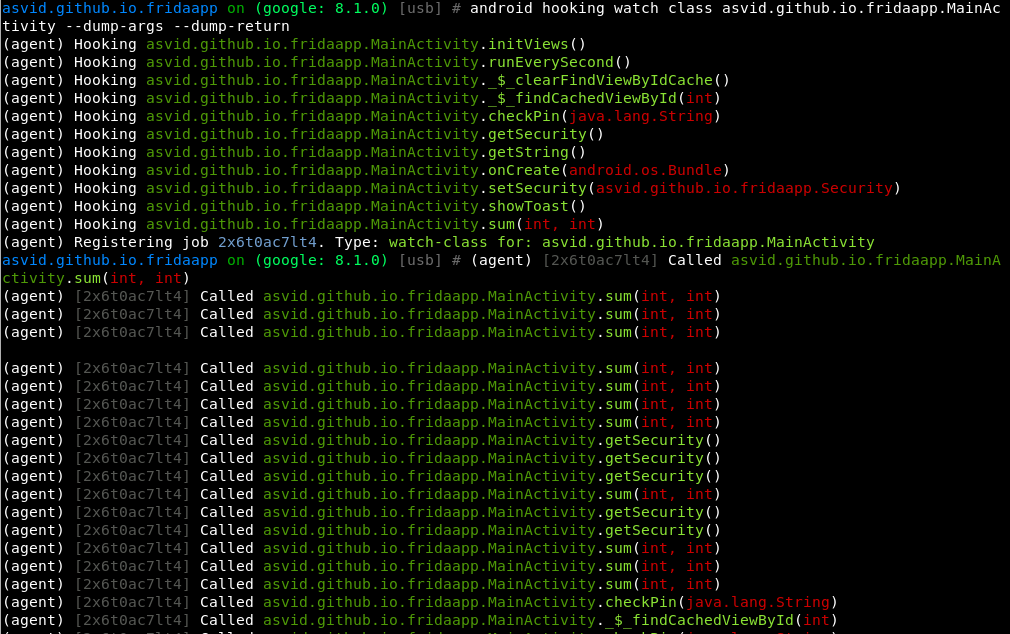
Hooking (watching) an entire class
Actually I find all the methods of the class MainActivity really interesting, lets hook them all. Be careful, this could crash an application.
android hooking watch class asvid.github.io.fridaapp.MainActivity --dump-args --dump-return
If you play with the application while the class is hooked you will see when each function is being called, its arguments and the return value.
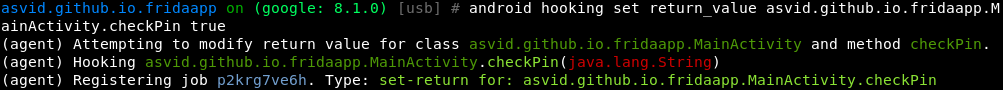
Changing boolean return value of a function
From the source code you can see that the function checkPin gets a String as argument and returns a boolean. Lets make the function always return true:
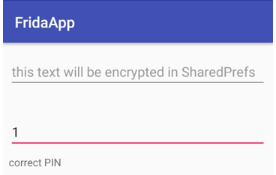
Now, If you write anything in the text box for the PIN code you will see tat anything is valid:
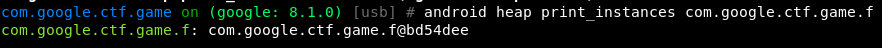
Class instances
Search for and print live instances of a specific Java class, specified by a fully qualified class name. Out is the result of an attempt at getting a string value for a discovered objection which would typically contain property values for the object.
android heap print_instances <class>
Keystore/Intents
You can play with the keystore and intents using:
android keystore list
android intents launch_activity
android intent launch_service
Memory
Dump
memory dump all <local destination> #Dump all memory
memory dump from_base <base_address> <size_to_dump> <local_destination> #Dump a part
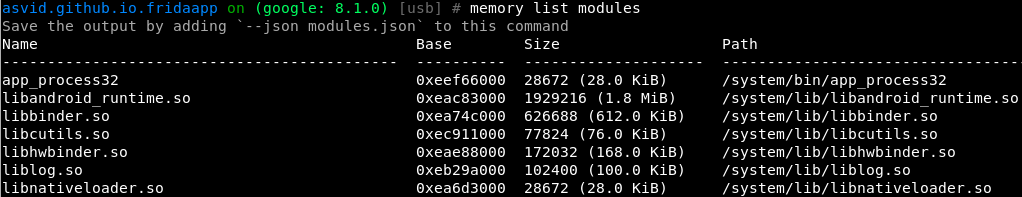
List
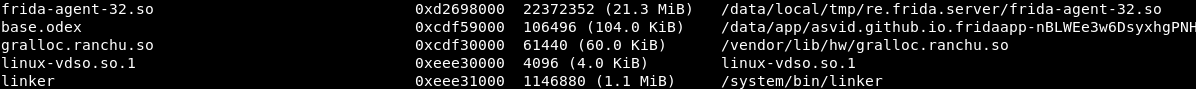
memory list modules
At the bottom os the list you can see frida:
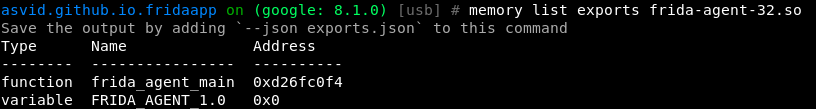
Lets checks what is frida exporting:
Search/Write
You can alse search and write inside memory with objection:
memory search "<pattern eg: 41 41 41 ?? 41>" (--string) (--offsets-only)
memory write "<address>" "<pattern eg: 41 41 41 41>" (--string)
SQLite
You cals can use the command sqlite to interact with sqlite databases.
Exit
exit
What I miss in Objection
- The hooking methods sometimes crashes the application (this is also because of Frida).
- You can't use the instaces of the classes to call functions of the instance. And you can't create new instances of classes and use them to call functions.
- There isn't a shortcut (like the one for sslpinnin) to hook all the common crypto methods being used by the application to see cyphered text, plain text, keys, IVs and algorithms used.

Bug bounty tip: sign up for Intigriti, a premium bug bounty platform created by hackers, for hackers! Join us at https://go.intigriti.com/hacktricks today, and start earning bounties up to $100,000!
{% embed url="https://go.intigriti.com/hacktricks" %}
🎙️ HackTricks LIVE Twitch Wednesdays 5.30pm (UTC) 🎙️ - 🎥 Youtube 🎥
- Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access to the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
- Discover The PEASS Family, our collection of exclusive NFTs
- Get the official PEASS & HackTricks swag
- Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
- Share your hacking tricks by submitting PRs to the hacktricks repo and hacktricks-cloud repo.