mirror of
https://github.com/carlospolop/hacktricks
synced 2024-11-30 00:20:59 +00:00
132 lines
8.3 KiB
Markdown
132 lines
8.3 KiB
Markdown
# 135, 593 - Kupima MSRPC
|
|
|
|
<details>
|
|
|
|
<summary><strong>Jifunze kuhusu kudukua AWS kutoka sifuri hadi shujaa na</strong> <a href="https://training.hacktricks.xyz/courses/arte"><strong>htARTE (Mtaalam wa Timu Nyekundu ya AWS ya HackTricks)</strong></a><strong>!</strong></summary>
|
|
|
|
Njia nyingine za kusaidia HackTricks:
|
|
|
|
* Ikiwa unataka kuona **kampuni yako ikitangazwa kwenye HackTricks** au **kupakua HackTricks kwa PDF** Angalia [**MIPANGO YA KUJIUNGA**](https://github.com/sponsors/carlospolop)!
|
|
* Pata [**bidhaa rasmi za PEASS & HackTricks**](https://peass.creator-spring.com)
|
|
* Gundua [**Familia ya PEASS**](https://opensea.io/collection/the-peass-family), mkusanyiko wetu wa [**NFTs**](https://opensea.io/collection/the-peass-family) ya kipekee
|
|
* **Jiunge na** 💬 [**Kikundi cha Discord**](https://discord.gg/hRep4RUj7f) au [**kikundi cha telegram**](https://t.me/peass) au **tufuate** kwenye **Twitter** 🐦 [**@carlospolopm**](https://twitter.com/hacktricks\_live)**.**
|
|
* **Shiriki mbinu zako za kudukua kwa kuwasilisha PRs kwa** [**HackTricks**](https://github.com/carlospolop/hacktricks) na [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) repos za github.
|
|
|
|
</details>
|
|
|
|
<figure><img src="../.gitbook/assets/image (377).png" alt=""><figcaption></figcaption></figure>
|
|
|
|
Jiunge na [**HackenProof Discord**](https://discord.com/invite/N3FrSbmwdy) server ili kuwasiliana na wadukuzi wenye uzoefu na wawindaji wa zawadi za mdudu!
|
|
|
|
**Machapisho ya Kudukua**\
|
|
Shiriki na yaliyomo yanayochimba katika msisimko na changamoto za kudukua
|
|
|
|
**Machapisho ya Kudukua ya Wakati Halisi**\
|
|
Kaa sawa na ulimwengu wa kudukua unaobadilika haraka kupitia habari za wakati halisi na ufahamu
|
|
|
|
**Matangazo ya Karibuni**\
|
|
Baki mwelekezwa na zawadi mpya za mdudu zinazoanzishwa na sasisho muhimu za jukwaa
|
|
|
|
**Jiunge nasi kwenye** [**Discord**](https://discord.com/invite/N3FrSbmwdy) na anza kushirikiana na wadukuzi bora leo!
|
|
|
|
## Taarifa Msingi
|
|
|
|
Itifaki ya Kuita Kijijini ya Microsoft (MSRPC), mfano wa mteja-seva unaozingatia programu kuomba huduma kutoka kwa programu iliyoko kwenye kompyuta nyingine bila kuelewa maelezo ya mtandao, ilichochewa awali kutoka kwa programu ya chanzo wazi na baadaye ikafanyiwa maendeleo na kuhakikiwa na Microsoft.
|
|
|
|
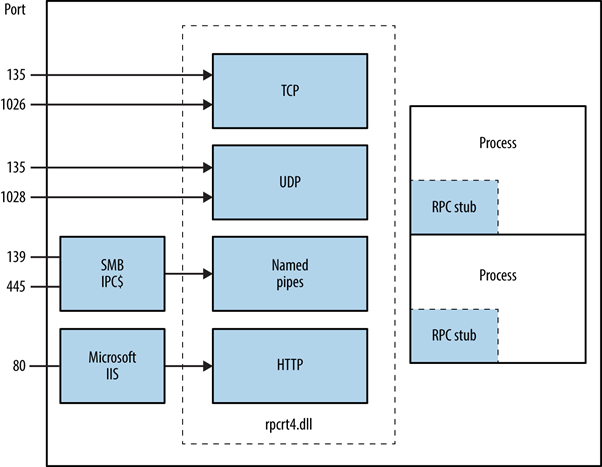
Mwambo wa mwisho wa RPC unaweza kufikiwa kupitia bandari za TCP na UDP 135, SMB kwenye TCP 139 na 445 (na kikao cha null au kilichoidhinishwa), na kama huduma ya wavuti kwenye bandari ya TCP 593.
|
|
```
|
|
135/tcp open msrpc Microsoft Windows RPC
|
|
```
|
|
## Jinsi gani MSRPC inavyofanya kazi?
|
|
|
|
Kuanzishwa na programu ya mteja, mchakato wa MSRPC unahusisha kuita utaratibu wa mbadala wa ndani ambao kisha huingiliana na maktaba ya muda wa mteja ili kuandaa na kutuma ombi kwa seva. Hii ni pamoja na kubadilisha parameta kuwa muundo wa Uwakilishi wa Data wa Mtandao wa kawaida. Chaguo la itifaki ya usafirishaji linapangwa na maktaba ya muda wa mteja ikiwa seva iko mbali, ikihakikisha RPC inatumwa kupitia safu ya mtandao.
|
|
|
|
|
|
|
|
## **Kutambua Huduma za RPC Zilizofichuliwa**
|
|
|
|
Ufunuo wa huduma za RPC kote TCP, UDP, HTTP, na SMB unaweza kugunduliwa kwa kuuliza huduma ya mchotaji wa RPC na vituo vya mwisho binafsi. Zana kama rpcdump hufanikisha kutambua huduma za RPC za kipekee, zinazotambuliwa na thamani za **IFID**, zikifunua maelezo ya huduma na vifungo vya mawasiliano:
|
|
```
|
|
D:\rpctools> rpcdump [-p port] <IP>
|
|
**IFID**: 5a7b91f8-ff00-11d0-a9b2-00c04fb6e6fc version 1.0
|
|
Annotation: Messenger Service
|
|
UUID: 00000000-0000-0000-0000-000000000000
|
|
Binding: ncadg_ip_udp:<IP>[1028]
|
|
```
|
|
Upatikanaji wa huduma ya RPC locator unawezeshwa kupitia itifaki maalum: ncacn\_ip\_tcp na ncadg\_ip\_udp kwa kupata kupitia bandari 135, ncacn\_np kwa uunganisho wa SMB, na ncacn\_http kwa mawasiliano ya RPC yanayotegemea wavuti. Amri zifuatazo zinaonyesha matumizi ya moduli za Metasploit kufanya ukaguzi na kuingiliana na huduma za MSRPC, zikilenga hasa bandari 135:
|
|
```bash
|
|
use auxiliary/scanner/dcerpc/endpoint_mapper
|
|
use auxiliary/scanner/dcerpc/hidden
|
|
use auxiliary/scanner/dcerpc/management
|
|
use auxiliary/scanner/dcerpc/tcp_dcerpc_auditor
|
|
rpcdump.py <IP> -p 135
|
|
```
|
|
Hakuna chaguo ila `tcp_dcerpc_auditor` iliyoundwa kwa kuchunguza MSRPC kwenye bandari 135.
|
|
|
|
#### Violezo vya RPC vya Kumbukumbu
|
|
|
|
* **IFID**: 12345778-1234-abcd-ef00-0123456789ab
|
|
* **Mbombaji wa Majina**: `\pipe\lsarpc`
|
|
* **Maelezo**: Kiolesura cha LSA, hutumika kuchambua watumiaji.
|
|
* **IFID**: 3919286a-b10c-11d0-9ba8-00c04fd92ef5
|
|
* **Mbombaji wa Majina**: `\pipe\lsarpc`
|
|
* **Maelezo**: Kiolesura cha Huduma za Mwongozo wa LSA (DS), hutumika kuchambua udomo na mahusiano ya uaminifu.
|
|
* **IFID**: 12345778-1234-abcd-ef00-0123456789ac
|
|
* **Mbombaji wa Majina**: `\pipe\samr`
|
|
* **Maelezo**: Kiolesura cha LSA SAMR, hutumika kufikia vipengele vya kumbukumbu ya SAM ya umma (k.m., majina ya watumiaji) na kuvunja nguvu nywila za mtumiaji bila kujali sera ya kufunga akaunti.
|
|
* **IFID**: 1ff70682-0a51-30e8-076d-740be8cee98b
|
|
* **Mbombaji wa Majina**: `\pipe\atsvc`
|
|
* **Maelezo**: Mipangilio ya kazi, hutumika kutekeleza amri kijijini.
|
|
* **IFID**: 338cd001-2244-31f1-aaaa-900038001003
|
|
* **Mbombaji wa Majina**: `\pipe\winreg`
|
|
* **Maelezo**: Huduma ya usajili wa kijijini, hutumika kufikia na kurekebisha usajili wa mfumo.
|
|
* **IFID**: 367abb81-9844-35f1-ad32-98f038001003
|
|
* **Mbombaji wa Majina**: `\pipe\svcctl`
|
|
* **Maelezo**: Meneja wa udhibiti wa huduma na huduma za seva, hutumika kuanza na kusitisha huduma kijijini na kutekeleza amri.
|
|
* **IFID**: 4b324fc8-1670-01d3-1278-5a47bf6ee188
|
|
* **Mbombaji wa Majina**: `\pipe\srvsvc`
|
|
* **Maelezo**: Meneja wa udhibiti wa huduma na huduma za seva, hutumika kuanza na kusitisha huduma kijijini na kutekeleza amri.
|
|
* **IFID**: 4d9f4ab8-7d1c-11cf-861e-0020af6e7c57
|
|
* **Mbombaji wa Majina**: `\pipe\epmapper`
|
|
* **Maelezo**: Kiolesura cha DCOM, hutumika kwa kuvunja nguvu nywila na kukusanya habari kupitia WM.
|
|
|
|
### Kutambua Anwani za IP
|
|
|
|
Kwa kutumia [https://github.com/mubix/IOXIDResolver](https://github.com/mubix/IOXIDResolver), inayotoka kwenye [utafiti wa Airbus](https://www.cyber.airbus.com/the-oxid-resolver-part-1-remote-enumeration-of-network-interfaces-without-any-authentication/), inawezekana kutumia njia ya _**ServerAlive2**_ ndani ya kiolesura cha _**IOXIDResolver**_.
|
|
|
|
Njia hii imekuwa ikitumika kupata habari za kiolesura kama anwani ya **IPv6** kutoka kwenye sanduku la HTB _APT_. Angalia [hapa](https://0xdf.gitlab.io/2021/04/10/htb-apt.html) kwa mwongozo wa 0xdf APT, inajumuisha njia mbadala ya kutumia rpcmap.py kutoka [Impacket](https://github.com/SecureAuthCorp/impacket/) na _stringbinding_ (angalia hapo juu).
|
|
|
|
### Kutekeleza RCE na sifa halali
|
|
|
|
Inawezekana kutekeleza msimbo wa kijijini kwenye mashine, ikiwa sifa za mtumiaji halali zinapatikana kwa kutumia [dcomexec.py](https://github.com/fortra/impacket/blob/master/examples/dcomexec.py) kutoka kwenye mfumo wa impacket.
|
|
|
|
**Kumbuka kujaribu na vitu tofauti vinavyopatikana**
|
|
|
|
* ShellWindows
|
|
* ShellBrowserWindow
|
|
* MMC20
|
|
|
|
## Bandari 593
|
|
|
|
**rpcdump.exe** kutoka [rpctools](https://resources.oreilly.com/examples/9780596510305/tree/master/tools/rpctools) inaweza kuingiliana na bandari hii.
|
|
|
|
## Marejeo
|
|
|
|
* [https://www.cyber.airbus.com/the-oxid-resolver-part-1-remote-enumeration-of-network-interfaces-without-any-authentication/](https://www.cyber.airbus.com/the-oxid-resolver-part-1-remote-enumeration-of-network-interfaces-without-any-authentication/)
|
|
* [https://www.cyber.airbus.com/the-oxid-resolver-part-2-accessing-a-remote-object-inside-dcom/](https://www.cyber.airbus.com/the-oxid-resolver-part-2-accessing-a-remote-object-inside-dcom/)
|
|
* [https://0xffsec.com/handbook/services/msrpc/](https://0xffsec.com/handbook/services/msrpc/)
|
|
|
|
<figure><img src="../.gitbook/assets/image (377).png" alt=""><figcaption></figcaption></figure>
|
|
|
|
Jiunge na [**HackenProof Discord**](https://discord.com/invite/N3FrSbmwdy) server ili kuwasiliana na wadukuzi wenye uzoefu na wawindaji wa tuzo za mdudu!
|
|
|
|
**Machapisho ya Udukuzi**\
|
|
Shiriki na yaliyomo yanayochimba kina cha udukuzi na changamoto zake
|
|
|
|
**Habari za Udukuzi za Wakati Halisi**\
|
|
Kaa sawa na ulimwengu wa udukuzi wenye kasi kupitia habari za wakati halisi na ufahamu
|
|
|
|
**Matangazo Mapya Zaidi**\
|
|
Baki mwelekezi na tuzo mpya za mdudu zinazoanzishwa na sasisho muhimu za jukwaa
|
|
|
|
**Jiunge nasi kwenye** [**Discord**](https://discord.com/invite/N3FrSbmwdy) na anza kushirikiana na wadukuzi bora leo!
|