mirror of
https://github.com/carlospolop/hacktricks
synced 2024-12-03 09:59:40 +00:00
148 lines
9.1 KiB
Markdown
148 lines
9.1 KiB
Markdown
# 135, 593 - Pentesting MSRPC
|
|
|
|
{% hint style="success" %}
|
|
Learn & practice AWS Hacking:<img src="/.gitbook/assets/arte.png" alt="" data-size="line">[**HackTricks Training AWS Red Team Expert (ARTE)**](https://training.hacktricks.xyz/courses/arte)<img src="/.gitbook/assets/arte.png" alt="" data-size="line">\
|
|
Learn & practice GCP Hacking: <img src="/.gitbook/assets/grte.png" alt="" data-size="line">[**HackTricks Training GCP Red Team Expert (GRTE)**<img src="/.gitbook/assets/grte.png" alt="" data-size="line">](https://training.hacktricks.xyz/courses/grte)
|
|
|
|
<details>
|
|
|
|
<summary>Support HackTricks</summary>
|
|
|
|
* Check the [**subscription plans**](https://github.com/sponsors/carlospolop)!
|
|
* **Join the** 💬 [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** us on **Twitter** 🐦 [**@hacktricks\_live**](https://twitter.com/hacktricks\_live)**.**
|
|
* **Share hacking tricks by submitting PRs to the** [**HackTricks**](https://github.com/carlospolop/hacktricks) and [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repos.
|
|
|
|
</details>
|
|
{% endhint %}
|
|
|
|
<figure><img src="../.gitbook/assets/image (380).png" alt=""><figcaption></figcaption></figure>
|
|
|
|
Join [**HackenProof Discord**](https://discord.com/invite/N3FrSbmwdy) server to communicate with experienced hackers and bug bounty hunters!
|
|
|
|
**Hacking Insights**\
|
|
Engage with content that delves into the thrill and challenges of hacking
|
|
|
|
**Real-Time Hack News**\
|
|
Keep up-to-date with fast-paced hacking world through real-time news and insights
|
|
|
|
**Latest Announcements**\
|
|
Stay informed with the newest bug bounties launching and crucial platform updates
|
|
|
|
**Join us on** [**Discord**](https://discord.com/invite/N3FrSbmwdy) and start collaborating with top hackers today!
|
|
|
|
## Basic Information
|
|
|
|
Protokol Microsoft Remote Procedure Call (MSRPC), model klijent-server koji omogućava programu da zatraži uslugu od programa koji se nalazi na drugom računaru bez razumevanja specifičnosti mreže, prvobitno je izveden iz softvera otvorenog koda, a kasnije je razvijen i zaštićen autorskim pravima od strane Microsoft-a.
|
|
|
|
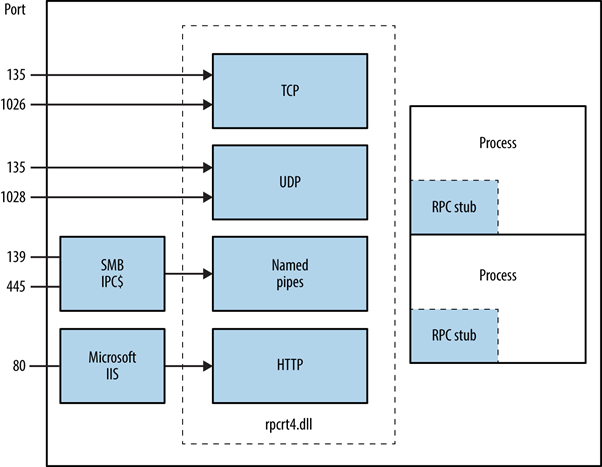
RPC endpoint mapper može se pristupiti putem TCP i UDP porta 135, SMB na TCP 139 i 445 (sa null ili autentifikovanom sesijom), i kao web servis na TCP portu 593.
|
|
```
|
|
135/tcp open msrpc Microsoft Windows RPC
|
|
```
|
|
## Kako funkcioniše MSRPC?
|
|
|
|
Iniciran od strane klijentske aplikacije, MSRPC proces uključuje pozivanje lokalne stub procedure koja zatim interaguje sa klijentskom runtime bibliotekom kako bi pripremila i prenela zahtev serveru. Ovo uključuje konvertovanje parametara u standardni format Network Data Representation. Izbor transportnog protokola određuje runtime biblioteka ako je server udaljen, osiguravajući da se RPC isporučuje kroz mrežni stek.
|
|
|
|
|
|
|
|
## **Identifikacija izloženih RPC usluga**
|
|
|
|
Izloženost RPC usluga preko TCP, UDP, HTTP i SMB može se odrediti upitom RPC locator servisa i pojedinačnih krajnjih tačaka. Alati kao što je rpcdump olakšavaju identifikaciju jedinstvenih RPC usluga, označenih **IFID** vrednostima, otkrivajući detalje usluga i komunikacione veze:
|
|
```
|
|
D:\rpctools> rpcdump [-p port] <IP>
|
|
**IFID**: 5a7b91f8-ff00-11d0-a9b2-00c04fb6e6fc version 1.0
|
|
Annotation: Messenger Service
|
|
UUID: 00000000-0000-0000-0000-000000000000
|
|
Binding: ncadg_ip_udp:<IP>[1028]
|
|
```
|
|
Pristup RPC lokatorskoj usluzi omogućen je putem specifičnih protokola: ncacn\_ip\_tcp i ncadg\_ip\_udp za pristup preko porta 135, ncacn\_np za SMB veze, i ncacn\_http za web-baziranu RPC komunikaciju. Sledeće komande ilustruju korišćenje Metasploit modula za audite i interakciju sa MSRPC uslugama, prvenstveno fokusirajući se na port 135:
|
|
```bash
|
|
use auxiliary/scanner/dcerpc/endpoint_mapper
|
|
use auxiliary/scanner/dcerpc/hidden
|
|
use auxiliary/scanner/dcerpc/management
|
|
use auxiliary/scanner/dcerpc/tcp_dcerpc_auditor
|
|
rpcdump.py <IP> -p 135
|
|
```
|
|
All options except `tcp_dcerpc_auditor` are specifically designed for targeting MSRPC on port 135.
|
|
|
|
#### Notable RPC interfaces
|
|
|
|
* **IFID**: 12345778-1234-abcd-ef00-0123456789ab
|
|
* **Named Pipe**: `\pipe\lsarpc`
|
|
* **Description**: LSA interfejs, koristi se za enumeraciju korisnika.
|
|
* **IFID**: 3919286a-b10c-11d0-9ba8-00c04fd92ef5
|
|
* **Named Pipe**: `\pipe\lsarpc`
|
|
* **Description**: LSA interfejs za usluge direktorijuma (DS), koristi se za enumeraciju domena i odnosa poverenja.
|
|
* **IFID**: 12345778-1234-abcd-ef00-0123456789ac
|
|
* **Named Pipe**: `\pipe\samr`
|
|
* **Description**: LSA SAMR interfejs, koristi se za pristup javnim elementima SAM baze podataka (npr. korisnička imena) i brute-force napade na lozinke korisnika bez obzira na politiku zaključavanja naloga.
|
|
* **IFID**: 1ff70682-0a51-30e8-076d-740be8cee98b
|
|
* **Named Pipe**: `\pipe\atsvc`
|
|
* **Description**: Planer zadataka, koristi se za daljinsko izvršavanje komandi.
|
|
* **IFID**: 338cd001-2244-31f1-aaaa-900038001003
|
|
* **Named Pipe**: `\pipe\winreg`
|
|
* **Description**: Usluga daljinskog registra, koristi se za pristup i modifikaciju sistemskog registra.
|
|
* **IFID**: 367abb81-9844-35f1-ad32-98f038001003
|
|
* **Named Pipe**: `\pipe\svcctl`
|
|
* **Description**: Menadžer kontrole usluga i server usluga, koristi se za daljinsko pokretanje i zaustavljanje usluga i izvršavanje komandi.
|
|
* **IFID**: 4b324fc8-1670-01d3-1278-5a47bf6ee188
|
|
* **Named Pipe**: `\pipe\srvsvc`
|
|
* **Description**: Menadžer kontrole usluga i server usluga, koristi se za daljinsko pokretanje i zaustavljanje usluga i izvršavanje komandi.
|
|
* **IFID**: 4d9f4ab8-7d1c-11cf-861e-0020af6e7c57
|
|
* **Named Pipe**: `\pipe\epmapper`
|
|
* **Description**: DCOM interfejs, koristi se za brute-force napade na lozinke i prikupljanje informacija putem WM.
|
|
|
|
### Identifying IP addresses
|
|
|
|
Using [https://github.com/mubix/IOXIDResolver](https://github.com/mubix/IOXIDResolver), comes from [Airbus research](https://www.cyber.airbus.com/the-oxid-resolver-part-1-remote-enumeration-of-network-interfaces-without-any-authentication/) is possible to abuse the _**ServerAlive2**_ method inside the _**IOXIDResolver**_ interface.
|
|
|
|
This method has been used to get interface information as **IPv6** address from the HTB box _APT_. See [here](https://0xdf.gitlab.io/2021/04/10/htb-apt.html) for 0xdf APT writeup, it includes an alternative method using rpcmap.py from [Impacket](https://github.com/SecureAuthCorp/impacket/) with _stringbinding_ (see above).
|
|
|
|
### Executing a RCE with valid credentials
|
|
|
|
It is possible to execute remote code on a machine, if the credentials of a valid user are available using [dcomexec.py](https://github.com/fortra/impacket/blob/master/examples/dcomexec.py) from impacket framework.
|
|
|
|
**Remember to try with the different objects available**
|
|
|
|
* ShellWindows
|
|
* ShellBrowserWindow
|
|
* MMC20
|
|
|
|
## Port 593
|
|
|
|
The **rpcdump.exe** from [rpctools](https://resources.oreilly.com/examples/9780596510305/tree/master/tools/rpctools) can interact with this port.
|
|
|
|
## References
|
|
|
|
* [https://www.cyber.airbus.com/the-oxid-resolver-part-1-remote-enumeration-of-network-interfaces-without-any-authentication/](https://www.cyber.airbus.com/the-oxid-resolver-part-1-remote-enumeration-of-network-interfaces-without-any-authentication/)
|
|
* [https://www.cyber.airbus.com/the-oxid-resolver-part-2-accessing-a-remote-object-inside-dcom/](https://www.cyber.airbus.com/the-oxid-resolver-part-2-accessing-a-remote-object-inside-dcom/)
|
|
* [https://0xffsec.com/handbook/services/msrpc/](https://0xffsec.com/handbook/services/msrpc/)
|
|
|
|
<figure><img src="../.gitbook/assets/image (380).png" alt=""><figcaption></figcaption></figure>
|
|
|
|
Join [**HackenProof Discord**](https://discord.com/invite/N3FrSbmwdy) server to communicate with experienced hackers and bug bounty hunters!
|
|
|
|
**Hacking Insights**\
|
|
Engage with content that delves into the thrill and challenges of hacking
|
|
|
|
**Real-Time Hack News**\
|
|
Keep up-to-date with fast-paced hacking world through real-time news and insights
|
|
|
|
**Latest Announcements**\
|
|
Stay informed with the newest bug bounties launching and crucial platform updates
|
|
|
|
**Join us on** [**Discord**](https://discord.com/invite/N3FrSbmwdy) and start collaborating with top hackers today!
|
|
|
|
{% hint style="success" %}
|
|
Learn & practice AWS Hacking:<img src="/.gitbook/assets/arte.png" alt="" data-size="line">[**HackTricks Training AWS Red Team Expert (ARTE)**](https://training.hacktricks.xyz/courses/arte)<img src="/.gitbook/assets/arte.png" alt="" data-size="line">\
|
|
Learn & practice GCP Hacking: <img src="/.gitbook/assets/grte.png" alt="" data-size="line">[**HackTricks Training GCP Red Team Expert (GRTE)**<img src="/.gitbook/assets/grte.png" alt="" data-size="line">](https://training.hacktricks.xyz/courses/grte)
|
|
|
|
<details>
|
|
|
|
<summary>Support HackTricks</summary>
|
|
|
|
* Check the [**subscription plans**](https://github.com/sponsors/carlospolop)!
|
|
* **Join the** 💬 [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** us on **Twitter** 🐦 [**@hacktricks\_live**](https://twitter.com/hacktricks\_live)**.**
|
|
* **Share hacking tricks by submitting PRs to the** [**HackTricks**](https://github.com/carlospolop/hacktricks) and [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repos.
|
|
|
|
</details>
|
|
{% endhint %}
|