15 KiB
53 - Pentesting DNS
Jifunze kuhack AWS kutoka sifuri hadi shujaa na htARTE (Mtaalam wa Timu Nyekundu ya AWS ya HackTricks)!
Njia nyingine za kusaidia HackTricks:
- Ikiwa unataka kuona kampuni yako ikitangazwa kwenye HackTricks au kupakua HackTricks kwa PDF Angalia MIPANGO YA KUJIUNGA!
- Pata bidhaa rasmi za PEASS & HackTricks
- Gundua Familia ya PEASS, mkusanyiko wetu wa NFTs ya kipekee
- Jiunge na 💬 Kikundi cha Discord au kikundi cha telegram au tufuate kwenye Twitter 🐦 @carlospolopm.
- Shiriki mbinu zako za kuhack kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.

Usanidi uliopo mara moja kwa tathmini ya udhaifu & upenyezaji wa mtihani. Tekeleza pentest kamili kutoka popote na zana & vipengele zaidi ya 20 vinavyoanzia uchunguzi hadi ripoti. Hatuchukui nafasi ya wapentesta - tunatengeneza zana za desturi, moduli za ugunduzi & uchexploitation ili kuwarudishia muda wa kuchimba kwa kina, kufungua makompyuta, na kufurahi.
{% embed url="https://pentest-tools.com/" %}
Taarifa Msingi
Mfumo wa Jina la Kikoa (DNS) hutumika kama daftari la mtandao, kuruhusu watumiaji kupata tovuti kupitia majina rahisi kukumbuka ya kikoa kama google.com au facebook.com, badala ya anwani za Itifaki ya Mtandao (IP) za nambari. Kwa kutafsiri majina ya kikoa kuwa anwani za IP, DNS inahakikisha vivinjari vya wavuti vinaweza kupakia haraka rasilimali za mtandao, kufanya iwe rahisi jinsi tunavyotembea ulimwengu wa mtandaoni.
Bandari ya chaguo: 53
PORT STATE SERVICE REASON
53/tcp open domain Microsoft DNS 6.1.7601 (1DB15D39) (Windows Server 2008 R2 SP1)
5353/udp open zeroconf udp-response
53/udp open domain Microsoft DNS 6.1.7601 (1DB15D39) (Windows Server 2008 R2 SP1)
Seva tofauti za DNS
- Seva za Mzizi wa DNS: Hizi ziko juu kabisa mwa mfuatano wa DNS, zikisimamia uwanja wa juu kabisa na kuingilia tu ikiwa seva za ngazi ya chini hazijajibu. Shirika la Mtandao kwa Majina na Nambari (ICANN) linaangalia uendeshaji wao, na idadi ya kimataifa ni 13.
- Seva za Mamlaka: Seva hizi ndizo zinaamua mwisho kwa maswali katika maeneo yao yaliyotengwa, zikitoa majibu ya mwisho. Ikiwa hawawezi kutoa jibu, swali linapelekwa kwa seva za mzizi.
- Seva Zisizo na Mamlaka: Zisizo na umiliki wa maeneo ya DNS, seva hizi hukusanya habari za uwanja kupitia maswali kwa seva nyingine.
- Seva ya Kuhifadhi Kache ya DNS: Aina hii ya seva inakumbuka majibu ya maswali ya awali kwa muda uliowekwa ili kuharakisha majibu kwa maombi ya baadaye, na muda wa kache unadhibitiwa na seva ya mamlaka.
- Seva ya Kuelekeza: Kutoa jukumu la moja kwa moja, seva za kuelekeza tu zinapeleka maswali kwa seva nyingine.
- Mtatuzi: Imeunganishwa ndani ya kompyuta au rutuba, watauzi hutekeleza ufumbuzi wa jina kwa kiasili na hawaonekani kuwa na mamlaka.
Uorodheshaji
Kukamata Bango
Hakuna mabango katika DNS lakini unaweza kukamata swali la kichawi kwa version.bind. CHAOS TXT ambalo litafanya kazi kwa seva nyingi za BIND.
Unaweza kutekeleza swali hili kwa kutumia dig:
dig version.bind CHAOS TXT @DNS
Zaidi ya hayo, zana fpdns inaweza pia kutambua alama ya seva.
Pia ni rahisi kunasa bango pia na script ya nmap:
--script dns-nsid
Rekodi yoyote
Rekodi ya ANY itaomba seva ya DNS kurejesha masharti yote yanayopatikana ambayo inakubali kufichua.
dig any victim.com @<DNS_IP>
Uhamisho wa Eneo
Mchakato huu unaitwa Uhamisho Kamili wa Eneo la Asynchronous (AXFR).
dig axfr @<DNS_IP> #Try zone transfer without domain
dig axfr @<DNS_IP> <DOMAIN> #Try zone transfer guessing the domain
fierce --domain <DOMAIN> --dns-servers <DNS_IP> #Will try toperform a zone transfer against every authoritative name server and if this doesn'twork, will launch a dictionary attack
Maelezo zaidi
dig ANY @<DNS_IP> <DOMAIN> #Any information
dig A @<DNS_IP> <DOMAIN> #Regular DNS request
dig AAAA @<DNS_IP> <DOMAIN> #IPv6 DNS request
dig TXT @<DNS_IP> <DOMAIN> #Information
dig MX @<DNS_IP> <DOMAIN> #Emails related
dig NS @<DNS_IP> <DOMAIN> #DNS that resolves that name
dig -x 192.168.0.2 @<DNS_IP> #Reverse lookup
dig -x 2a00:1450:400c:c06::93 @<DNS_IP> #reverse IPv6 lookup
#Use [-p PORT] or -6 (to use ivp6 address of dns)
Uendeshaji wa Kiotomatiki
for sub in $(cat <WORDLIST>);do dig $sub.<DOMAIN> @<DNS_IP> | grep -v ';\|SOA' | sed -r '/^\s*$/d' | grep $sub | tee -a subdomains.txt;done
dnsenum --dnsserver <DNS_IP> --enum -p 0 -s 0 -o subdomains.txt -f <WORDLIST> <DOMAIN>
Kutumia nslookup
nslookup
> SERVER <IP_DNS> #Select dns server
> 127.0.0.1 #Reverse lookup of 127.0.0.1, maybe...
> <IP_MACHINE> #Reverse lookup of a machine, maybe...
Moduli muhimu ya metasploit
auxiliary/gather/enum_dns #Perform enumeration actions
Skripti za nmap Zinazoweza Kusaidia
#Perform enumeration actions
nmap -n --script "(default and *dns*) or fcrdns or dns-srv-enum or dns-random-txid or dns-random-srcport" <IP>
DNS - Reverse BF
DNS - Kinyume cha BF
dnsrecon -r 127.0.0.0/24 -n <IP_DNS> #DNS reverse of all of the addresses
dnsrecon -r 127.0.1.0/24 -n <IP_DNS> #DNS reverse of all of the addresses
dnsrecon -r <IP_DNS>/24 -n <IP_DNS> #DNS reverse of all of the addresses
dnsrecon -d active.htb -a -n <IP_DNS> #Zone transfer
{% hint style="info" %} Ikiwa unaweza kupata subdomains zinazotatuliwa kwa anwani za IP za ndani, unapaswa kujaribu kutekeleza reverse dns BF kwa NSs ya kikoa ukiuliza kwa safu hiyo ya IP. {% endhint %}
Chombo kingine cha kufanya hivyo: https://github.com/amine7536/reverse-scan
Unaweza kuuliza safu za IP za nyuma kwa https://bgp.he.net/net/205.166.76.0/24#_dns (chombo hiki pia ni muhimu na BGP).
DNS - Subdomains BF
dnsenum --dnsserver <IP_DNS> --enum -p 0 -s 0 -o subdomains.txt -f subdomains-1000.txt <DOMAIN>
dnsrecon -D subdomains-1000.txt -d <DOMAIN> -n <IP_DNS>
dnscan -d <domain> -r -w subdomains-1000.txt #Bruteforce subdomains in recursive way, https://github.com/rbsec/dnscan
Seva za Active Directory
dig -t _gc._tcp.lab.domain.com
dig -t _ldap._tcp.lab.domain.com
dig -t _kerberos._tcp.lab.domain.com
dig -t _kpasswd._tcp.lab.domain.com
nslookup -type=srv _kerberos._tcp.<CLIENT_DOMAIN>
nslookup -type=srv _kerberos._tcp.domain.com
nmap --script dns-srv-enum --script-args "dns-srv-enum.domain='domain.com'"
DNSSec
DNSSec ni itifaki inayotumiwa kuhakikisha usalama na uthibitisho wa data ya DNS.
#Query paypal subdomains to ns3.isc-sns.info
nmap -sSU -p53 --script dns-nsec-enum --script-args dns-nsec-enum.domains=paypal.com ns3.isc-sns.info
IPv6
Kutumia nguvu kubwa kwa kutumia maombi ya "AAAA" kukusanya IPv6 za subdomains.
dnsdict6 -s -t <domain>
Bruteforce reverse DNS in using IPv6 addresses
Kufanya nguvu ya bruteforce ya DNS ya nyuma kwa kutumia anwani za IPv6
dnsrevenum6 pri.authdns.ripe.net 2001:67c:2e8::/48 #Will use the dns pri.authdns.ripe.net
DNS Recursion DDoS
Ikiwa kurudishiwa DNS imewezeshwa, mshambuliaji anaweza kughushi asili kwenye pakiti ya UDP ili kufanya DNS itume jibu kwa seva ya mwathiriwa. Mshambuliaji anaweza kutumia rekodi za ANY au DNSSEC kwani zina majibu makubwa zaidi.
Njia ya kuangalia ikiwa DNS inasaidia kurudishiwa ni kuuliza jina la kikoa na kuangalia ikiwa alama "ra" (kurudishiwa inapatikana) iko kwenye jibu:
dig google.com A @<IP>
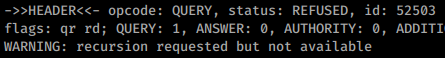
Hapatikani:
Inapatikana:

Usanidi wa haraka wa upimaji wa hatari & uchunguzi wa kuingilia. Tekeleza upimaji kamili kutoka mahali popote na zana na vipengele zaidi ya 20 vinavyoanzia uchunguzi hadi ripoti. Hatuchukui nafasi ya wapimaji wa kuingilia - tunaendeleza zana za desturi, moduli za ugunduzi & uchexploitation ili kuwapa muda wa kuchimba kwa kina, kufungua makompyuta, na kufurahi.
{% embed url="https://pentest-tools.com/" %}
Barua pepe kwa akaunti isiyopo
Kupitia uchunguzi wa taarifa ya kutofika (NDN) iliyosababishwa na barua pepe iliyotumwa kwa anwani isiyopo ndani ya kikoa cha lengo, maelezo muhimu ya mtandao wa ndani mara nyingi hufunuliwa.
Ripoti ya kutofika iliyotolewa inajumuisha maelezo kama vile:
- Seva ya kuzalisha iligunduliwa kama
server.example.com. - Taarifa ya kushindwa kwa
user@example.comna nambari ya kosa#550 5.1.1 RESOLVER.ADR.RecipNotFound; haipatikaniilirudishwa. - Anwani za IP za ndani na majina ya mwenyeji yalifunuliwa katika vichwa vya ujumbe wa asili.
The original message headers were modified for anonymity and now present randomized data:
Generating server: server.example.com
user@example.com
#550 5.1.1 RESOLVER.ADR.RecipNotFound; not found ##
Original message headers:
Received: from MAILSERVER01.domain.example.com (192.168.1.1) by
mailserver02.domain.example.com (192.168.2.2) with Microsoft SMTP Server (TLS)
id 14.3.174.1; Mon, 25 May 2015 14:52:22 -0700
Received: from filter.example.com (203.0.113.1) by
MAILSERVER01.domain.example.com (192.168.1.1) with Microsoft SMTP Server (TLS)
id 14.3.174.1; Mon, 25 May 2015 14:51:22 -0700
X-ASG-Debug-ID: 1432576343-0614671716190e0d0001-zOQ9WJ
Received: from gateway.domainhost.com (gateway.domainhost.com [198.51.100.37]) by
filter.example.com with ESMTP id xVNPkwaqGgdyH5Ag for user@example.com; Mon,
25 May 2015 14:52:13 -0700 (PDT)
X-Envelope-From: sender@anotherdomain.org
X-Apparent-Source-IP: 198.51.100.37
Faili za Mipangilio
host.conf
/etc/resolv.conf
/etc/bind/named.conf
/etc/bind/named.conf.local
/etc/bind/named.conf.options
/etc/bind/named.conf.log
/etc/bind/*
Mipangilio hatari wakati wa kusanidi seva ya Bind:
| Chaguo | Maelezo |
|---|---|
allow-query |
Inaainisha ni mwenyeji gani anaruhusiwa kutuma maombi kwa seva ya DNS. |
allow-recursion |
Inaainisha ni mwenyeji gani anaruhusiwa kutuma maombi ya kurudia kwa seva ya DNS. |
allow-transfer |
Inaainisha ni mwenyeji gani anaruhusiwa kupokea uhamisho wa eneo kutoka kwa seva ya DNS. |
zone-statistics |
Inakusanya data za takwimu za maeneo. |
Marejeo
- https://www.myrasecurity.com/en/knowledge-hub/dns/
- Kitabu: Tathmini ya Usalama wa Mtandao toleo la 3
Protocol_Name: DNS #Protocol Abbreviation if there is one.
Port_Number: 53 #Comma separated if there is more than one.
Protocol_Description: Domain Name Service #Protocol Abbreviation Spelled out
Entry_1:
Name: Notes
Description: Notes for DNS
Note: |
#These are the commands I run every time I see an open DNS port
dnsrecon -r 127.0.0.0/24 -n {IP} -d {Domain_Name}
dnsrecon -r 127.0.1.0/24 -n {IP} -d {Domain_Name}
dnsrecon -r {Network}{CIDR} -n {IP} -d {Domain_Name}
dig axfr @{IP}
dig axfr {Domain_Name} @{IP}
nslookup
SERVER {IP}
127.0.0.1
{IP}
Domain_Name
exit
https://book.hacktricks.xyz/pentesting/pentesting-dns
Entry_2:
Name: Banner Grab
Description: Grab DNS Banner
Command: dig version.bind CHAOS TXT @DNS
Entry_3:
Name: Nmap Vuln Scan
Description: Scan for Vulnerabilities with Nmap
Command: nmap -n --script "(default and *dns*) or fcrdns or dns-srv-enum or dns-random-txid or dns-random-srcport" {IP}
Entry_4:
Name: Zone Transfer
Description: Three attempts at forcing a zone transfer
Command: dig axfr @{IP} && dix axfr @{IP} {Domain_Name} && fierce --dns-servers {IP} --domain {Domain_Name}
Entry_5:
Name: Active Directory
Description: Eunuerate a DC via DNS
Command: dig -t _gc._{Domain_Name} && dig -t _ldap._{Domain_Name} && dig -t _kerberos._{Domain_Name} && dig -t _kpasswd._{Domain_Name} && nmap --script dns-srv-enum --script-args "dns-srv-enum.domain={Domain_Name}"
Entry_6:
Name: consolesless mfs enumeration
Description: DNS enumeration without the need to run msfconsole
Note: sourced from https://github.com/carlospolop/legion
Command: msfconsole -q -x 'use auxiliary/scanner/dns/dns_amp; set RHOSTS {IP}; set RPORT 53; run; exit' && msfconsole -q -x 'use auxiliary/gather/enum_dns; set RHOSTS {IP}; set RPORT 53; run; exit'

Mipangilio inapatikana mara moja kwa tathmini ya udhaifu na upenyezaji. Tekeleza pentest kamili kutoka popote ukiwa na zana na vipengele zaidi ya 20 vinavyoanzia uchunguzi hadi ripoti. Hatuchukui nafasi ya wapimaji wa pentest - tunatengeneza zana za desturi, moduli za ugunduzi na uvamizi ili kuwapa muda wa kuchimba kwa kina, kufungua makasha, na kufurahi.
{% embed url="https://pentest-tools.com/" %}
Jifunze AWS hacking kutoka sifuri hadi shujaa na htARTE (HackTricks AWS Red Team Expert)!
Njia nyingine za kusaidia HackTricks:
- Ikiwa unataka kuona kampuni yako ikionekana katika HackTricks au kupakua HackTricks kwa PDF Angalia MIPANGO YA KUJIUNGA!
- Pata bidhaa rasmi za PEASS & HackTricks
- Gundua Familia ya PEASS, mkusanyiko wetu wa NFTs ya kipekee
- Jiunge na 💬 Kikundi cha Discord au kikundi cha telegram au tufuate kwenye Twitter 🐦 @carlospolopm.
- Shiriki mbinu zako za udukuzi kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud github repos.