13 KiB
BrowExt - permissions & host_permissions
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.
Basic Information
permissions
Permissions are defined in the extension's manifest.json file using the permissions property and allow access to almost anything a browser can access (Cookies or Physical Storage):
The previous manifest declares that the extension requires the storage permission. This means that it can use the storage API to store its data persistently. Unlike cookies or localStorage APIs which give users some level of control, extension storage can normally only be cleared by uninstalling the extension.
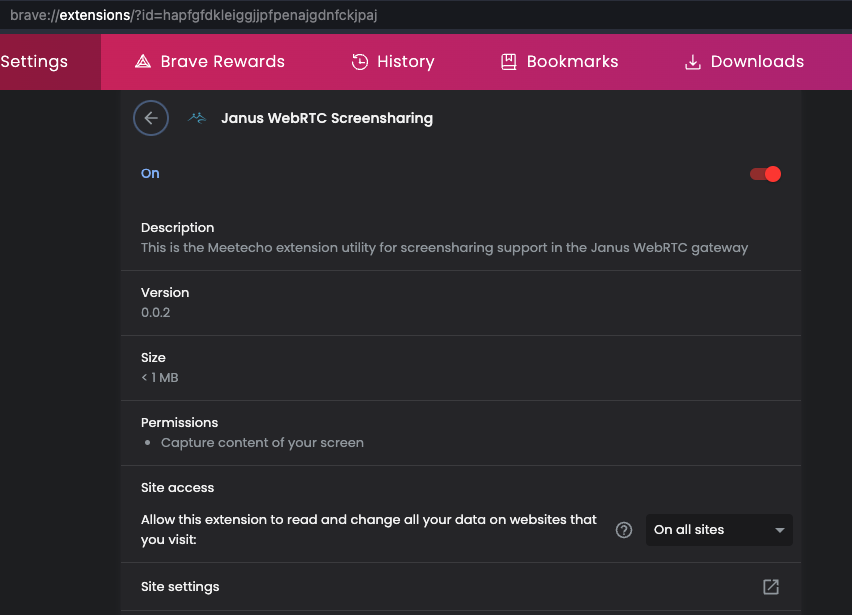
An extension will request the permissions indicated in its manifest.json file and After installing the extension, you can always check its permissions in your browser, as shown in this image:
You can find the complete list of permissions a Chromium Browser Extension can request here and a complete list for Firefox extensions here.
host_permissions
The optional but powerful setting host_permissions indicates with which hosts the extension is going to be able to interact via apis such as cookies, webRequest, and tabs.
The following host_permissions basically allow every web:
"host_permissions": [
"*://*/*"
]
// Or:
"host_permissions": [
"http://*/*",
"https://*/*"
]
// Or:
"host_permissions": [
"<all_urls>"
]
These are the hosts that the browser extension can access freely. This is because when a browser extension calls fetch("https://gmail.com/") it's not restricted by CORS.
Abusing permissions and host_permissions
Tabs
Moreover, host_permissions also unlock “advanced” tabs API functionality. They allow the extension to call tabs.query() and not only get a list of user’s browser tabs back but also learn which web page (meaning address and title) is loaded.
{% hint style="danger" %} Not only that, listeners like tabs.onUpdated become way more useful as well. These will be notified whenever a new page loads into a tab. {% endhint %}
Running content scripts
Content scripts aren’t necessarily written statically into the extension manifest. Given sufficient host_permissions, extensions can also load them dynamically by calling tabs.executeScript() or scripting.executeScript().
Both APIs allow executing not merely files contained in the extensions as content scripts but also arbitrary code. The former allows passing in JavaScript code as a string while the latter expects a JavaScript function which is less prone to injection vulnerabilities. Still, both APIs will wreak havoc if misused.
{% hint style="danger" %} In addition to the capabilities above, content scripts could for example intercept credentials as these are entered into web pages. Another classic way to abuse them is injecting advertising on each an every website. Adding scam messages to abuse credibility of news websites is also possible. Finally, they could manipulate banking websites to reroute money transfers. {% endhint %}
Implicit privileges
Some extension privileges don’t have to be explicitly declared. One example is the tabs API: its basic functionality is accessible without any privileges whatsoever. Any extension can be notified when you open and close tabs, it merely won’t know which website these tabs correspond with.
Sounds too harmless? The tabs.create() API is somewhat less so. It can be used to create a new tab, essentially the same as window.open() which can be called by any website. Yet while window.open() is subject to the pop-up blocker, tabs.create() isn’t.
{% hint style="danger" %} An extension can create any number of tabs whenever it wants. {% endhint %}
If you look through possible tabs.create() parameters, you’ll also notice that its capabilities go way beyond what window.open() is allowed to control. And while Firefox doesn’t allow data: URIs to be used with this API, Chrome has no such protection. Use of such URIs on the top level has been banned due to being abused for phishing.
tabs.update() is very similar to tabs.create() but will modify an existing tab. So a malicious extension can for example arbitrarily load an advertising page into one of your tabs, and it can activate the corresponding tab as well.
Webcam, geolocation and friends
You probably know that websites can request special permissions, e.g. in order to access your webcam (video conferencing tools) or geographical location (maps). It’s features with considerable potential for abuse, so users each time have to confirm that they still want this.
{% hint style="danger" %} Not so with browser extensions. If a browser extension wants access to your webcam or microphone, it only needs to ask for permission once {% endhint %}
Typically, an extension will do so immediately after being installed. Once this prompt is accepted, webcam access is possible at any time, even if the user isn’t interacting with the extension at this point. Yes, a user will only accept this prompt if the extension really needs webcam access. But after that they have to trust the extension not to record anything secretly.
With access to your exact geographical location or contents of your clipboard, granting permission explicitly is unnecessary altogether. An extension simply adds geolocation or clipboard to the permissions entry of its manifest. These access privileges are then granted implicitly when the extension is installed. So a malicious or compromised extension with these privileges can create your movement profile or monitor your clipboard for copied passwords without you noticing anything.
Adding the history keyword to the permissions entry of the extension manifest grants access to the history API. It allows retrieving the user’s entire browsing history all at once, without waiting for the user to visit these websites again.
The bookmarks permission has similar abuse potential, this one allows reading out all bookmarks via the bookmarks API.
Storage permission
The extension storage is merely a key-value collection, very similar to localStorage that any website could use. So no sensitive information should be stored here.
However, advertising companies could also abuse this storage.
More permissions
You can find the complete list of permissions a Chromium Browser Extension can request here and a complete list for Firefox extensions here.
Prevention
The policy of Google's developer explicitly forbids extensions from requesting more privileges than necessary for their functionality, effectively mitigating excessive permission requests. An instance where a browser extension overstepped this boundary involved its distribution with the browser itself rather than through an add-on store.
Browsers could further curb the misuse of extension privileges. For instance, Chrome's tabCapture and desktopCapture APIs, used for screen recording, are designed to minimize abuse. The tabCapture API can only be activated through direct user interaction, such as clicking on the extension icon, while desktopCapture requires user confirmation for the window to be recorded, preventing clandestine recording activities.
However, tightening security measures often results in decreased flexibility and user-friendliness of extensions. The activeTab permission illustrates this trade-off. It was introduced to eliminate the need for extensions to request host privileges across the entire internet, allowing extensions to access only the current tab upon explicit activation by the user. This model is effective for extensions requiring user-initiated actions but falls short for those requiring automatic or pre-emptive actions, thereby compromising convenience and immediate responsiveness.
References
- https://palant.info/2022/08/17/impact-of-extension-privileges/
- https://www.cobalt.io/blog/introduction-to-chrome-browser-extension-security-testing
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.