4.2 KiB
FZ - 125kHz RFID
{% hint style="success" %}
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.

{% embed url="https://websec.nl/" %}
Intro
For more info about how 125kHz tags work check:
{% content-ref url="../pentesting-rfid.md" %} pentesting-rfid.md {% endcontent-ref %}
Actions
For more info about these types of tags read this intro.
Read
Tries to read the card info. Then it can emulate them.
{% hint style="warning" %} Note that some intercoms try to protect themselves from key duplication by sending a write command prior to reading. If the write succeeds, that tag is considered fake. When Flipper emulates RFID there is no way for the reader to distinguish it from the original one, so no such problems occur. {% endhint %}
Add Manually
You can create fake cards in Flipper Zero indicating the data you manually and then emulate it.
IDs on cards
Some times, when you get a card you will find the ID (or part) of it written in the card visible.
- EM Marin
For example in this EM-Marin card in the physical card is possible to read the last 3 of 5 bytes in clear.
The other 2 can be brute-forced if you cannot read them from the card.

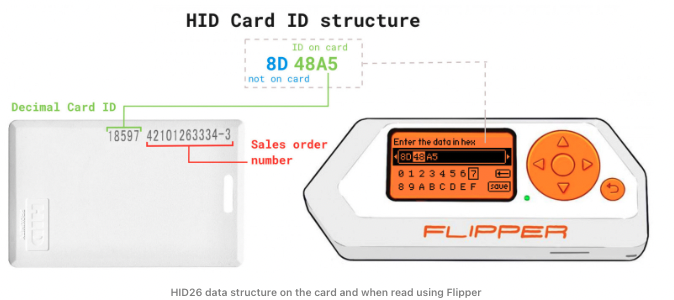
- HID
Same happens in this HID card where only 2 out of 3 bytes can be found printed in the card
Emulate/Write
After copying a card or entering the ID manually it's possible to emulate it with Flipper Zero or write it in a real card.
References

{% embed url="https://websec.nl/" %}
{% hint style="success" %}
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.