4 KiB
| description |
|---|
| source: https://medium.com/@shari7a0x/how-i-hacked-nasa-and-get-8-bugs-e5cd397a6af9 |
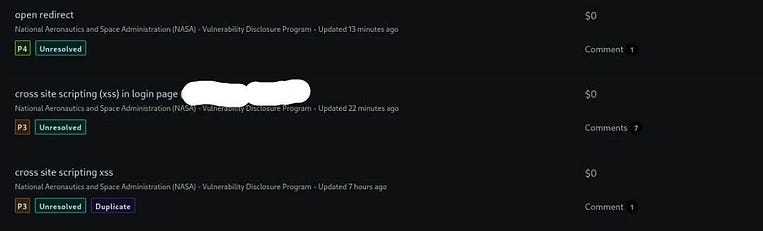
🔎 How I hacked NASA and got 8 bugs ?
Hi hackers ,
I will explain , How did i get 8 bugs in NASA .
It’s about 7 cross site scripting (xss) and one open redirect .
First step collect subdomains and check live domains .
I always use tool subfinder and add to it some API’s .
I always use tool HTTPX .
subfinder -d host.com -silent | httpx -mc 200 -o live txt
second step collecting parameters .
I always use two tools paramspider and waybackurls .
wait , are you real to collect parameters form domains by yourself ?
it’s many subdomains and paraspider can’t automate this alone .
I use simple bash script ,to automate collect parameters from subdomains .
for URL in $(</path-of-live-domains ); do (python3 paramspider.py -d "${URL}" --level high );done
little not before run this script you should open directory of Paramspider .
what after this ?
You want to check parameters if you can add (tags <>) .or not
I used KXSS , it’s very nice tool but not work at all the time .
Cat parameters.txt |kxss

done .
what after this ?
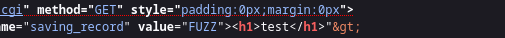
I can write html code .
You can use tool for discovering hidden parameters also like Arjun and check parameters if it work, you can use tool like dalfox very cool tool .
Arjun -u host.com
Dalfox url host.com?parameters=xss

boom xss is done .
You can use automation by NUCLEI . templates .
Nuclei -l parameters -t /fuzzing-templates/xss
I get open redirect by NUCLEI .
cat parameters.txt | grep "redirect" | NUCLEI -t /fuzzing-templates/redirect/open-redirect.yaml
if you think i finish you are wrong .
lol .
but that are two bug only , where are others ?
after i got first xss i had an idea , i can use some google dorks .
google dorks for xss !!!! yep .
some google dorks for discovering parameters
site:*.host.com ext:asp
site:*.host.com ext:jsp
site:*.host.com ext:aspx
site:*.host.com ext:jspx
site:*.host.com ext:do
site:*.host.com ext:action
I use them but didn't have useful parameters .
I check subdomain if i can use it to search about it in google .
I found something doesn’t see it usually it’s index.cgi .
I asked myself why didn’t try to use google dorks about it .
site: *.host.com ext:cgi
site:*.nasa.gov inurl:index.cgi
I see good result , i checked this result it’s like last domain ,that i had found xss in it ,I tried to use same parameter lol it is working nice .
I checked about 11 domains but 7 had xss .

thinks for reading .
give me feedback .