| .. | ||
| drupal-rce.md | ||
| README.md | ||
Drupal
{% hint style="success" %}
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.

{% embed url="https://websec.nl/" %}
Discovery
- Check meta
curl https://www.drupal.org/ | grep 'content="Drupal'
- Node: Drupal indexes its content using nodes. A node can hold anything such as a blog post, poll, article, etc. The page URIs are usually of the form
/node/<nodeid>.
curl drupal-site.com/node/1
Enumeration
Drupal supports three types of users by default:
Administrator: This user has complete control over the Drupal website.Authenticated User: These users can log in to the website and perform operations such as adding and editing articles based on their permissions.Anonymous: All website visitors are designated as anonymous. By default, these users are only allowed to read posts.
Version
- Check
/CHANGELOG.txt
curl -s http://drupal-site.local/CHANGELOG.txt | grep -m2 ""
Drupal 7.57, 2018-02-21
{% hint style="info" %}
Newer installs of Drupal by default block access to the CHANGELOG.txt and README.txt files.
{% endhint %}
Username enumeration
Register
In /user/register just try to create a username and if the name is already taken it will be notified:
Request new password
If you request a new password for an existing username:
If you request a new password for a non-existent username:
Get number of users
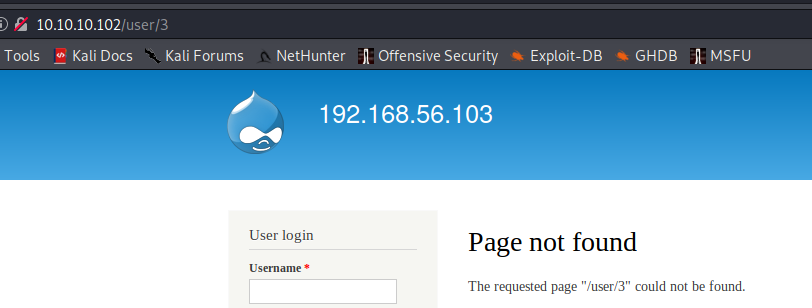
Accessing /user/<number> you can see the number of existing users, in this case is 2 as /users/3 returns a not found error:
Hidden pages
Fuzz /node/$ where $ is a number (from 1 to 500 for example).
You could find hidden pages (test, dev) which are not referenced by the search engines.
Installed modules info
#From https://twitter.com/intigriti/status/1439192489093644292/photo/1
#Get info on installed modules
curl https://example.com/config/sync/core.extension.yml
curl https://example.com/core/core.services.yml
# Download content from files exposed in the previous step
curl https://example.com/config/sync/swiftmailer.transport.yml
Automatic
droopescan scan drupal -u http://drupal-site.local
RCE
If you have access to the Drupal web console check these options to get RCE:
{% content-ref url="drupal-rce.md" %} drupal-rce.md {% endcontent-ref %}
Drupal From XSS to RCE
Through this technique, it is possible to achieve Remote Code Execution (RCE) in Drupal via Cross-Site Scripting (XSS). https://github.com/nowak0x01/Drupalwned
For more detailed steps check: https://nowak0x01.github.io/papers/76bc0832a8f682a7e0ed921627f85d1d.html
Post Exploitation
Read settings.php
find / -name settings.php -exec grep "drupal_hash_salt\|'database'\|'username'\|'password'\|'host'\|'port'\|'driver'\|'prefix'" {} \; 2>/dev/null
Dump users from DB
mysql -u drupaluser --password='2r9u8hu23t532erew' -e 'use drupal; select * from users'
References

{% embed url="https://websec.nl/" %}
{% hint style="success" %}
Learn & practice AWS Hacking: HackTricks Training AWS Red Team Expert (ARTE)
HackTricks Training AWS Red Team Expert (ARTE)
Learn & practice GCP Hacking:  HackTricks Training GCP Red Team Expert (GRTE)
HackTricks Training GCP Red Team Expert (GRTE)
Support HackTricks
- Check the subscription plans!
- Join the 💬 Discord group or the telegram group or follow us on Twitter 🐦 @hacktricks_live.
- Share hacking tricks by submitting PRs to the HackTricks and HackTricks Cloud github repos.