mirror of
https://github.com/carlospolop/hacktricks
synced 2024-11-22 04:33:28 +00:00
GITBOOK-4208: change request with no subject merged in GitBook
This commit is contained in:
parent
1699aa01ac
commit
a6d32b1828
2 changed files with 51 additions and 57 deletions
|
|
@ -1,37 +1,32 @@
|
|||
|
||||
# Reversing Native Libraries
|
||||
|
||||
<details>
|
||||
|
||||
<summary><a href="https://cloud.hacktricks.xyz/pentesting-cloud/pentesting-cloud-methodology"><strong>☁️ HackTricks Cloud ☁️</strong></a> -<a href="https://twitter.com/hacktricks_live"><strong>🐦 Twitter 🐦</strong></a> - <a href="https://www.twitch.tv/hacktricks_live/schedule"><strong>🎙️ Twitch 🎙️</strong></a> - <a href="https://www.youtube.com/@hacktricks_LIVE"><strong>🎥 Youtube 🎥</strong></a></summary>
|
||||
|
||||
- Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
|
||||
- Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
|
||||
- Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
|
||||
- **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
|
||||
|
||||
- **Share your hacking tricks by submitting PRs to the [hacktricks repo](https://github.com/carlospolop/hacktricks) and [hacktricks-cloud repo](https://github.com/carlospolop/hacktricks-cloud)**.
|
||||
* Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
* Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
* Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
* **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks\_live)**.**
|
||||
* **Share your hacking tricks by submitting PRs to the** [**hacktricks repo**](https://github.com/carlospolop/hacktricks) **and** [**hacktricks-cloud repo**](https://github.com/carlospolop/hacktricks-cloud).
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
**Information copied from **[**https://maddiestone.github.io/AndroidAppRE/reversing_native_libs.html**](https://maddiestone.github.io/AndroidAppRE/reversing_native_libs.html)** (you can find solutions there)**
|
||||
**Information copied from** [**https://maddiestone.github.io/AndroidAppRE/reversing\_native\_libs.html**](https://maddiestone.github.io/AndroidAppRE/reversing\_native\_libs.html) **(you can find solutions there)**
|
||||
|
||||
Android applications can contain compiled, native libraries. Native libraries are code that the developer wrote and then compiled for a specific computer architecture. Most often, this means code that is written in C or C++. The benign, or legitimate, reasons a developer may do this is for mathematically intensive or time sensitive operations, such as graphics libraries. Malware developers have begun moving to native code because reverse engineering compiled binaries tends to be a less common skillset than analyzing DEX bytecode. This is largely due to DEX bytecode can be decompiled to Java whereas native, compiled code, often must be analyzed as assembly.
|
||||
|
||||
## Goal
|
||||
### Goal
|
||||
|
||||
The goal of this section is not to teach you assembly (ASM) or how to reverse engineer compiled code more generally, but instead how to apply the more general binary reverse engineering skills, specifically to Android. Because the goal of this workshop is not to teach you the ASM architectures, all exercises will include an ARM _and_ an x86 version of the library to be analyzed so that each person can choose the architecture that they are more comfortable with.
|
||||
|
||||
### Learning ARM Assembly <a href="learning-arm-assembly" id="learning-arm-assembly"></a>
|
||||
#### Learning ARM Assembly <a href="#learning-arm-assembly" id="learning-arm-assembly"></a>
|
||||
|
||||
If you don’t have previous binary reverse engineering/ assembly experience, here are some suggested resources. Most Android devices run on ARM, but all exercises in this workshop also include an x86 version of the library.
|
||||
|
||||
To learn and/or review ARM assembly, I highly suggest the [ARM Assembly Basics](https://azeria-labs.com/writing-arm-assembly-part-1/) from [Azeria Labs](https://azeria-labs.com).
|
||||
|
||||
## Introduction to the Java Native Interface (JNI) <a href="introduction-to-the-java-native-interface-jni" id="introduction-to-the-java-native-interface-jni"></a>
|
||||
### Introduction to the Java Native Interface (JNI) <a href="#introduction-to-the-java-native-interface-jni" id="introduction-to-the-java-native-interface-jni"></a>
|
||||
|
||||
The Java Native Interface (JNI) allows developers to declare Java methods that are implemented in native code (usually compiled C/C++). JNI interface is not Android-specific, but is available more generally to Java applications that run on different platforms.
|
||||
|
||||
|
|
@ -41,7 +36,7 @@ The Android Native Development Kit (NDK) is the Android-specific toolset on top
|
|||
|
||||
Together, JNI and NDK allow Android developers to implement some of their app’s functionality in native code. The Java (or Kotlin) code will call a Java-declared native method which is implemented in the compiled, native library.
|
||||
|
||||
### References <a href="references" id="references"></a>
|
||||
#### References <a href="#references" id="references"></a>
|
||||
|
||||
**Oracle JNI Docs**
|
||||
|
||||
|
|
@ -53,7 +48,7 @@ Together, JNI and NDK allow Android developers to implement some of their app’
|
|||
* [Android JNI Tips](https://developer.android.com/training/articles/perf-jni) <– Highly suggest reading the “Native Libraries” section to start
|
||||
* [Getting Started with the NDK](https://developer.android.com/ndk/guides/) <– This is guidance for how developers develop native libraries and understanding how things are built, makes it easier to reverse.
|
||||
|
||||
## Target of Analysis - Android Native Libraries <a href="target-of-analysis---android-native-libraries" id="target-of-analysis---android-native-libraries"></a>
|
||||
### Target of Analysis - Android Native Libraries <a href="#target-of-analysis---android-native-libraries" id="target-of-analysis---android-native-libraries"></a>
|
||||
|
||||
For this section, we are focusing on how to reverse engineer app functionality that has been implemented in Android native libraries. When we say Android native libraries, what do we mean?
|
||||
|
||||
|
|
@ -71,7 +66,7 @@ Because native code is compiled for specific CPUs, if a developer wants their ap
|
|||
| ARMv7 | `lib/armeabi-v7a/libcalc.so` |
|
||||
| ARM64 | `lib/arm64-v8a/libcalc.so` |
|
||||
|
||||
## Loading the Library <a href="loading-the-library" id="loading-the-library"></a>
|
||||
### Loading the Library <a href="#loading-the-library" id="loading-the-library"></a>
|
||||
|
||||
Before an Android app can call and execute any code that is implemented in a native library, the application (Java code) must load the library into memory. There are two different API calls that will do this:
|
||||
|
||||
|
|
@ -91,7 +86,7 @@ When either of these two (`loadLibrary` or `load`) APIs are called by the Java c
|
|||
|
||||
To reiterate, before executing any native methods, the native library has to be loaded by calling `System.loadLibrary` or `System.load` in the Java code. When either of these 2 APIs is executed, the `JNI_OnLoad` function in the native library is also executed.
|
||||
|
||||
## The Java to Native Code Connection <a href="the-java-to-native-code-connection" id="the-java-to-native-code-connection"></a>
|
||||
### The Java to Native Code Connection <a href="#the-java-to-native-code-connection" id="the-java-to-native-code-connection"></a>
|
||||
|
||||
In order to execute a function from the native library, there must be a Java-declared native method that the Java code can call. When this Java-declared native method is called, the “paired” native function from the native library (ELF/.so) is executed.
|
||||
|
||||
|
|
@ -108,7 +103,7 @@ There are 2 different ways to do this pairing, or linking:
|
|||
1. Dynamic Linking using JNI Native Method Name Resolving, or
|
||||
2. Static Linking using the `RegisterNatives` API call
|
||||
|
||||
### Dynamic Linking <a href="dynamic-linking" id="dynamic-linking"></a>
|
||||
#### Dynamic Linking <a href="#dynamic-linking" id="dynamic-linking"></a>
|
||||
|
||||
In order to link, or pair, the Java declared native method and the function in the native library dynamically, the developer names the method and the function according to the specs such that the JNI system can dynamically do the linking.
|
||||
|
||||
|
|
@ -118,7 +113,7 @@ According to the spec, the developer would name the function as follow for the s
|
|||
2. a mangled fully-qualified class name
|
||||
3. an underscore (“\_”) separator
|
||||
4. a mangled method name
|
||||
5. for overloaded native methods, two underscores (“\__”) followed by the mangled argument signature
|
||||
5. for overloaded native methods, two underscores (“\_\_”) followed by the mangled argument signature
|
||||
|
||||
In order to do dynamic linking for the Java-declared native method below and let’s say it’s in the class `com.android.interesting.Stuff`
|
||||
|
||||
|
|
@ -134,7 +129,7 @@ Java_com_android_interesting_Stuff_doThingsInNativeLibrary
|
|||
|
||||
If there is not a function in the native library with that name, that means that the application must be doing static linking.
|
||||
|
||||
### Static Linking <a href="static-linking" id="static-linking"></a>
|
||||
#### Static Linking <a href="#static-linking" id="static-linking"></a>
|
||||
|
||||
If the developer doesn’t want to or can not name the native functions according to the spec (Ex. wants to strip debug symbols), then they must use static linking with the `RegisterNatives` ([doc](https://docs.oracle.com/javase/7/docs/technotes/guides/jni/spec/functions.html#wp5833)) API in order to do the pairing between the Java-declared native method and the function in the native library. The `RegisterNatives` function is called from the native code, not the Java code and is most often called in the `JNI_OnLoad` function since `RegisterNatives` must be executed prior to calling the Java-declared native method.
|
||||
|
||||
|
|
@ -193,7 +188,7 @@ It has the type signature:
|
|||
(ILjava/lang/String;[I)J
|
||||
```
|
||||
|
||||
### Exercise #5 - Find the Address of the Native Function <a href="exercise-5---find-the-address-of-the-native-function" id="exercise-5---find-the-address-of-the-native-function"></a>
|
||||
#### Exercise #5 - Find the Address of the Native Function <a href="#exercise-5---find-the-address-of-the-native-function" id="exercise-5---find-the-address-of-the-native-function"></a>
|
||||
|
||||
In Exercise #5 we’re going to learn to load native libraries in a disassembler and identify the native function that is executed when a native method is called. For this particular exercise, the goal is not to reverse engineer the native method, just to find the link between the call to the native method in Java and the function that is executed in the native library. For this exercise, we will be using the sample Mediacode.apk. This sample is available at `~/samples/Mediacode.apk` in the VM. Its SHA256 hash is a496b36cda66aaf24340941da8034bd53940d1b08d83a97f17a65ae144ebf91a.
|
||||
|
||||
|
|
@ -209,8 +204,8 @@ The goal of this exercise is to:
|
|||
|
||||
**Instructions**
|
||||
|
||||
1. Open Mediacode.apk in jadx. Refer back to [Exercise #1](https://maddiestone.github.io/AndroidAppRE/reversing_intro.html#exercise-1---beginning-re-with-jadx)
|
||||
2. This time, if you expand the Resources tab, you will see that this APK has a `lib/` directory. The native libraries for this APK are in the default CPU paths.
|
||||
1. Open Mediacode.apk in jadx. Refer back to [Exercise #1](https://maddiestone.github.io/AndroidAppRE/reversing\_intro.html#exercise-1---beginning-re-with-jadx)
|
||||
2. This time, if you expand the Resources tab, you will see that this APK has a `lib/` directory. The native libraries for this APK are in the default CPU paths.
|
||||
3. Now we need to identify any declared native methods. In jadx, search and list all declared native methods. There should be two.
|
||||
4. Around the declared native method, see if there is anywhere that a native library is loaded. This will provide guidance of what native library to look in for the function to be implemented.
|
||||
5. Extract the native library from the APK by creating a new dir and copying the APK into that folder. Then run the command `unzip Mediacode.APK`. You will see all of the files extracted from APK, which includes the `lib/` directory.
|
||||
|
|
@ -218,7 +213,7 @@ The goal of this exercise is to:
|
|||
7. Start ghidra by running `ghidraRun`. This will open Ghidra.
|
||||
8. To open the native library for analysis, select “New Project”, “Non-Shared Project”, select a path to save the project to and give it a name. This creates a project that you can then load binary files into.
|
||||
9. Once you’ve created your project, select the dragon icon to open the Code Browser. The go to “File” > “Import File” to load the native library into the tool. You can leave all defaults.
|
||||
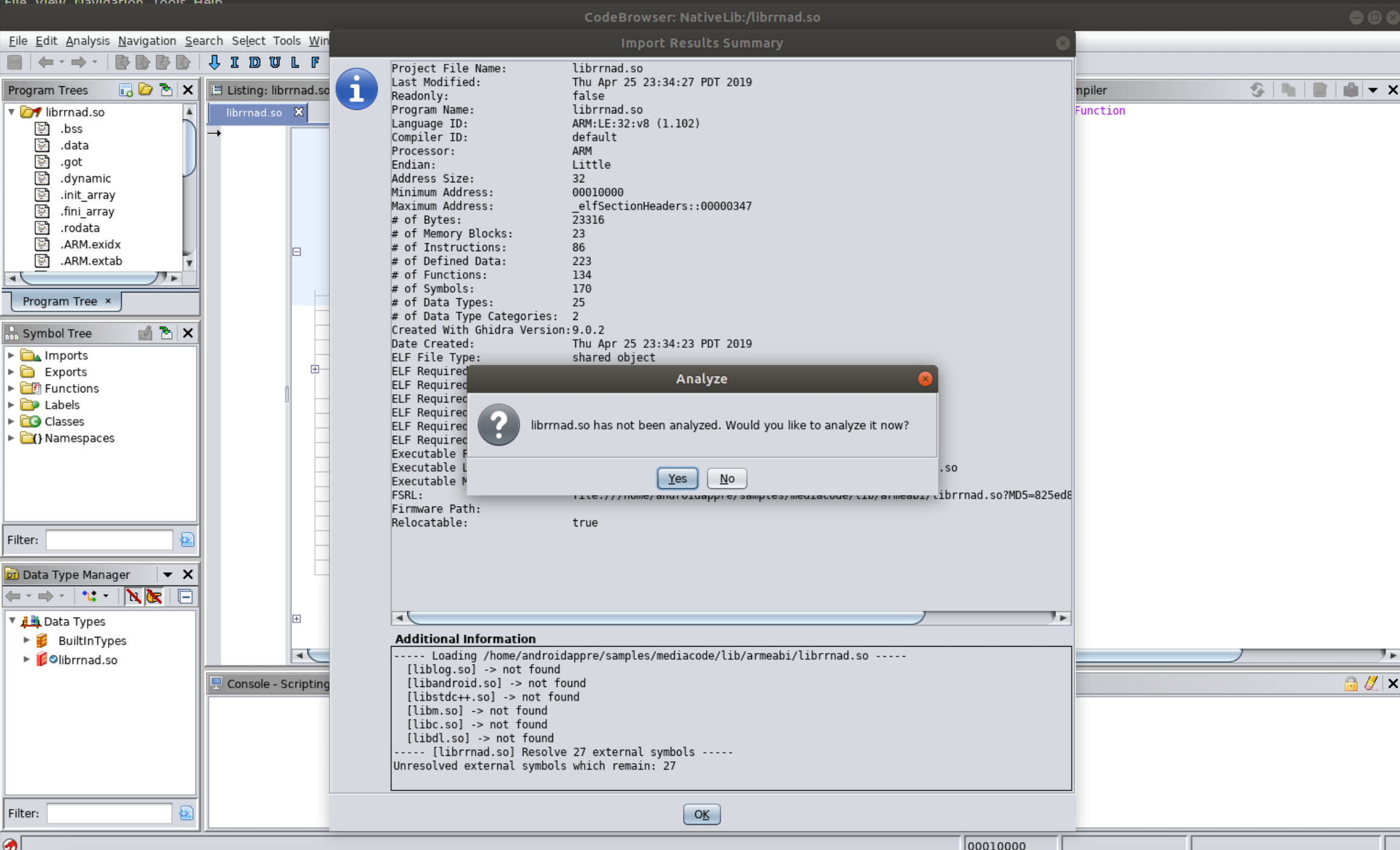
10. You will see the following screen. Select “Analyze”.
|
||||
10. You will see the following screen. Select “Analyze”.
|
||||
11. Using the linking information above, identify the function in the native library that is executed when the Java-declared native method is called.
|
||||
|
||||
|
||||
|
|
@ -227,22 +222,22 @@ The goal of this exercise is to:
|
|||
|
||||
**Solution**
|
||||
|
||||
## Reversing Android Native Libraries Code - JNIEnv <a href="reversing-android-native-libraries-code---jnienv" id="reversing-android-native-libraries-code---jnienv"></a>
|
||||
### Reversing Android Native Libraries Code - JNIEnv <a href="#reversing-android-native-libraries-code---jnienv" id="reversing-android-native-libraries-code---jnienv"></a>
|
||||
|
||||
When beginning to reverse engineer Android native libraries, one of the things I didn’t know I needed to know, was about `JNIEnv`. `JNIEnv` is a struct of function pointers to [JNI Functions](https://docs.oracle.com/javase/7/docs/technotes/guides/jni/spec/functions.html). Every JNI function in Android native libraries, takes `JNIEnv*` as the first argument.
|
||||
|
||||
From the Android [JNI Tips](https://developer.android.com/training/articles/perf-jni) documentation:
|
||||
|
||||
> The C declarations of JNIEnv and JavaVM are different from the C++ declarations. The “jni.h” include file provides different typedefs depending on whether it’s included into C or C++. For this reason it’s a bad idea to include JNIEnv arguments in header files included by both languages. (Put another way: if your header file requires #ifdef \__cplusplus, you may have to do some extra work if anything in that header refers to JNIEnv.)
|
||||
> The C declarations of JNIEnv and JavaVM are different from the C++ declarations. The “jni.h” include file provides different typedefs depending on whether it’s included into C or C++. For this reason it’s a bad idea to include JNIEnv arguments in header files included by both languages. (Put another way: if your header file requires #ifdef \_\_cplusplus, you may have to do some extra work if anything in that header refers to JNIEnv.)
|
||||
|
||||
Here are some commonly used functions (and their offsets in JNIEnv):
|
||||
|
||||
* JNIEnv + 0x18: jclass (\*FindClass)(JNIEnv_, const char_);
|
||||
* JNIEnv + 0x18: jclass (\*FindClass)(JNIEnv\_, const char\_);
|
||||
* JNIEnv + 0x34: jint (\*Throw)(JNIEnv\*, jthrowable);
|
||||
* JNIEnv + 0x70: jobject (\*NewObject)(JNIEnv\*, jclass, jmethodID, …);
|
||||
* JNIEnv + 0x84: jobject (\*NewObject)(JNIEnv\*, jclass, jmethodID, …);
|
||||
* JNIEnv + 0x28C: jstring (\*NewString)(JNIEnv_, const jchar_, jsize);
|
||||
* JNIEnv + 0x35C: jint (\*RegisterNatives)(JNIEnv_, jclass, const JNINativeMethod_, jint);
|
||||
* JNIEnv + 0x28C: jstring (\*NewString)(JNIEnv\_, const jchar\_, jsize);
|
||||
* JNIEnv + 0x35C: jint (\*RegisterNatives)(JNIEnv\_, jclass, const JNINativeMethod\_, jint);
|
||||
|
||||
When analyzing Android native libraries, the presence of JNIEnv means that:
|
||||
|
||||
|
|
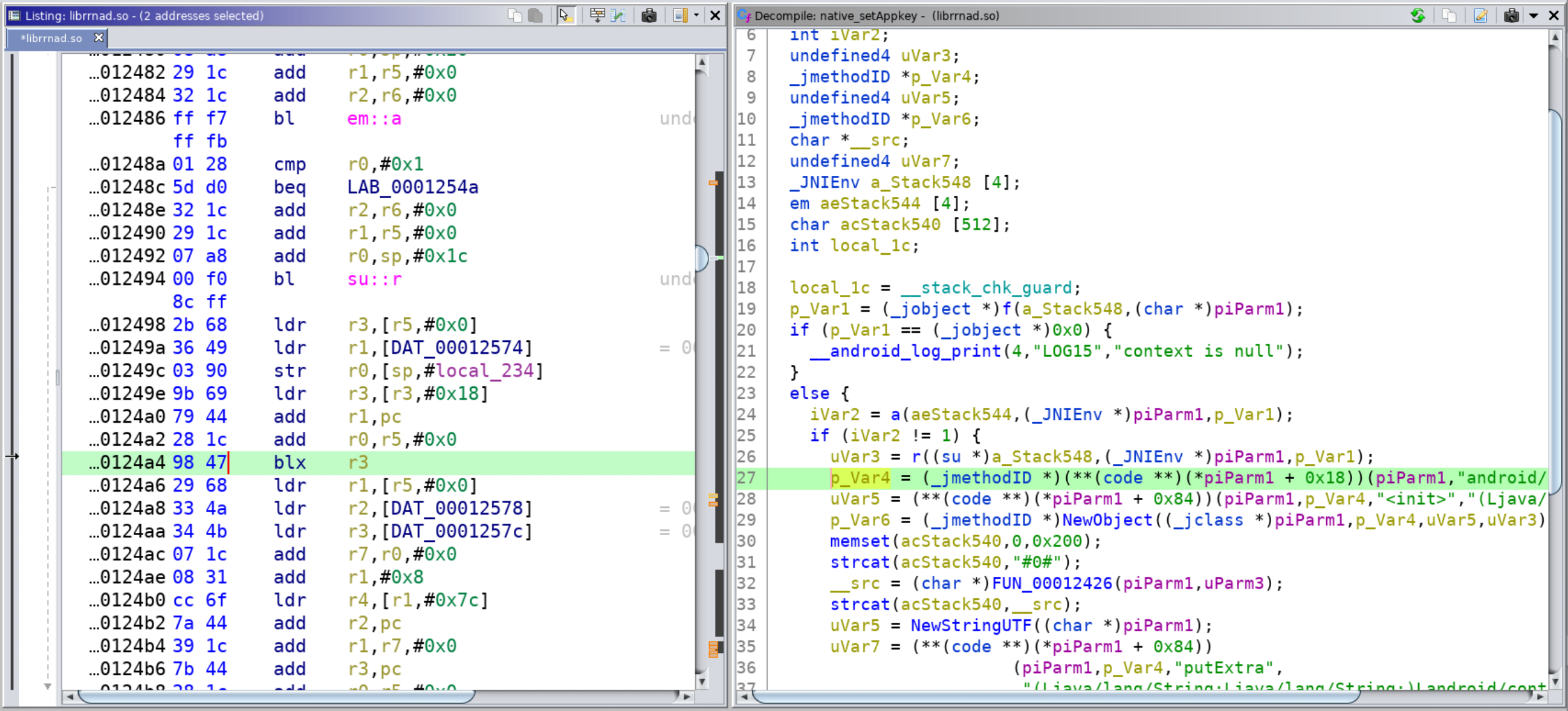
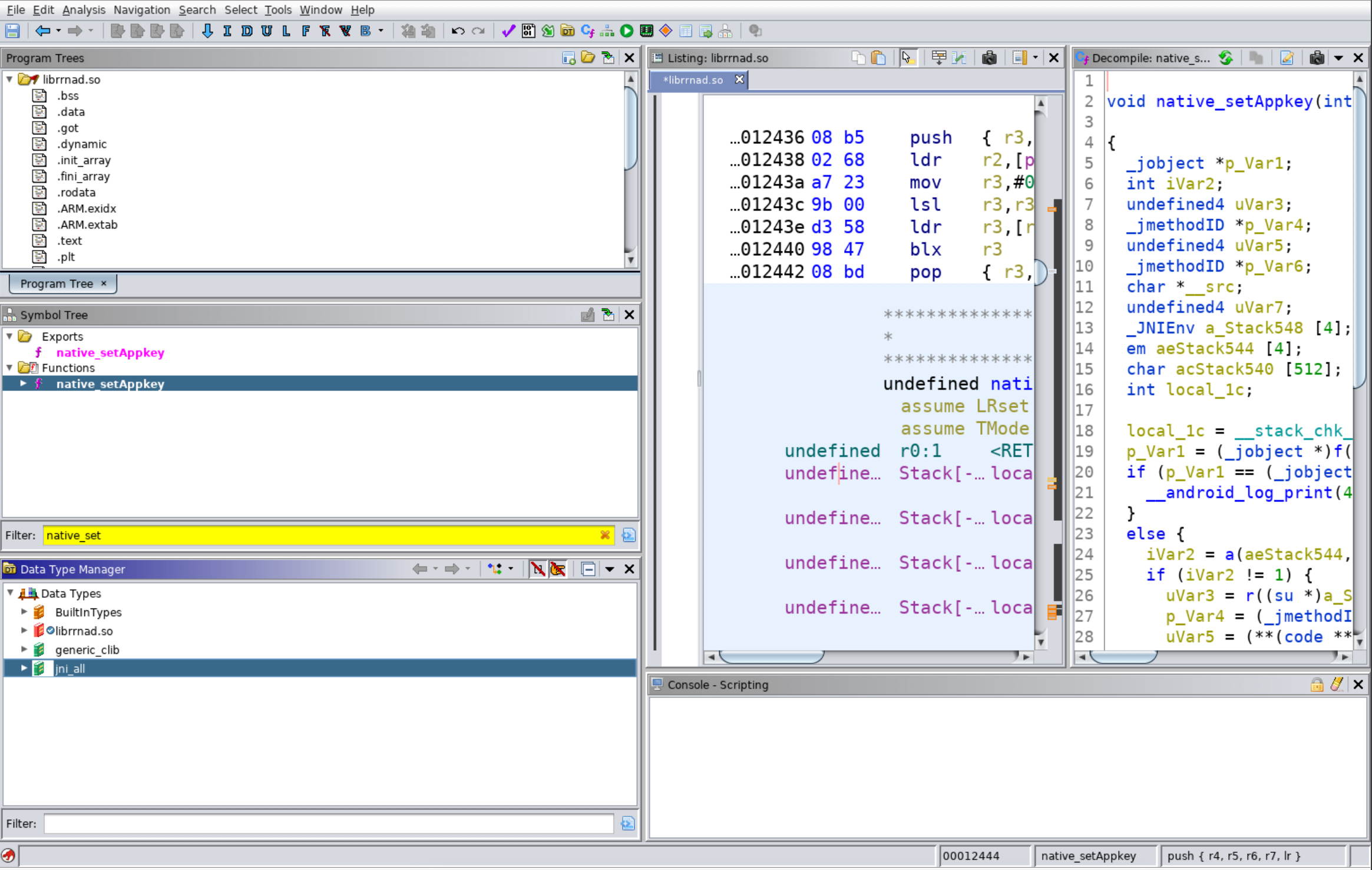
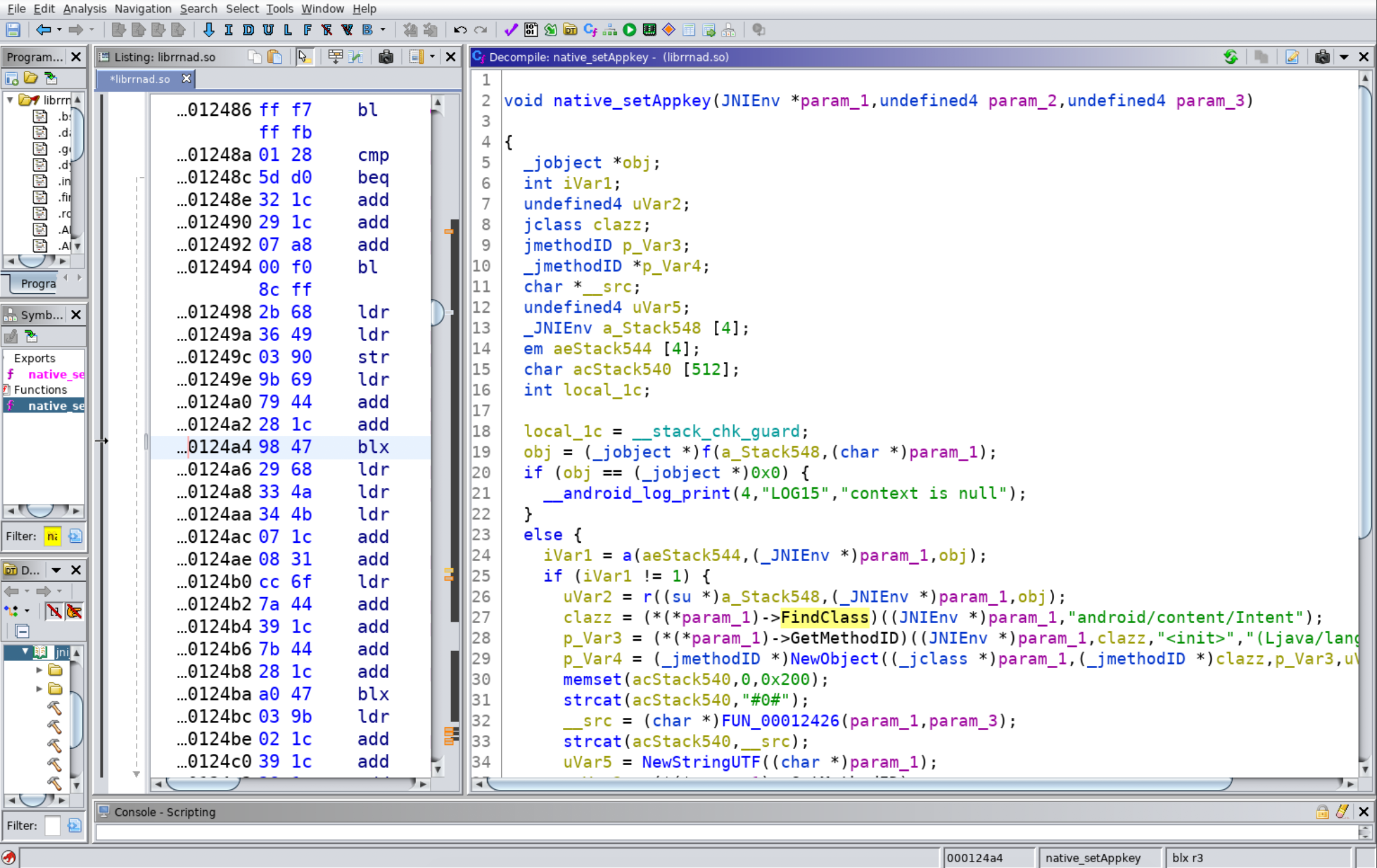
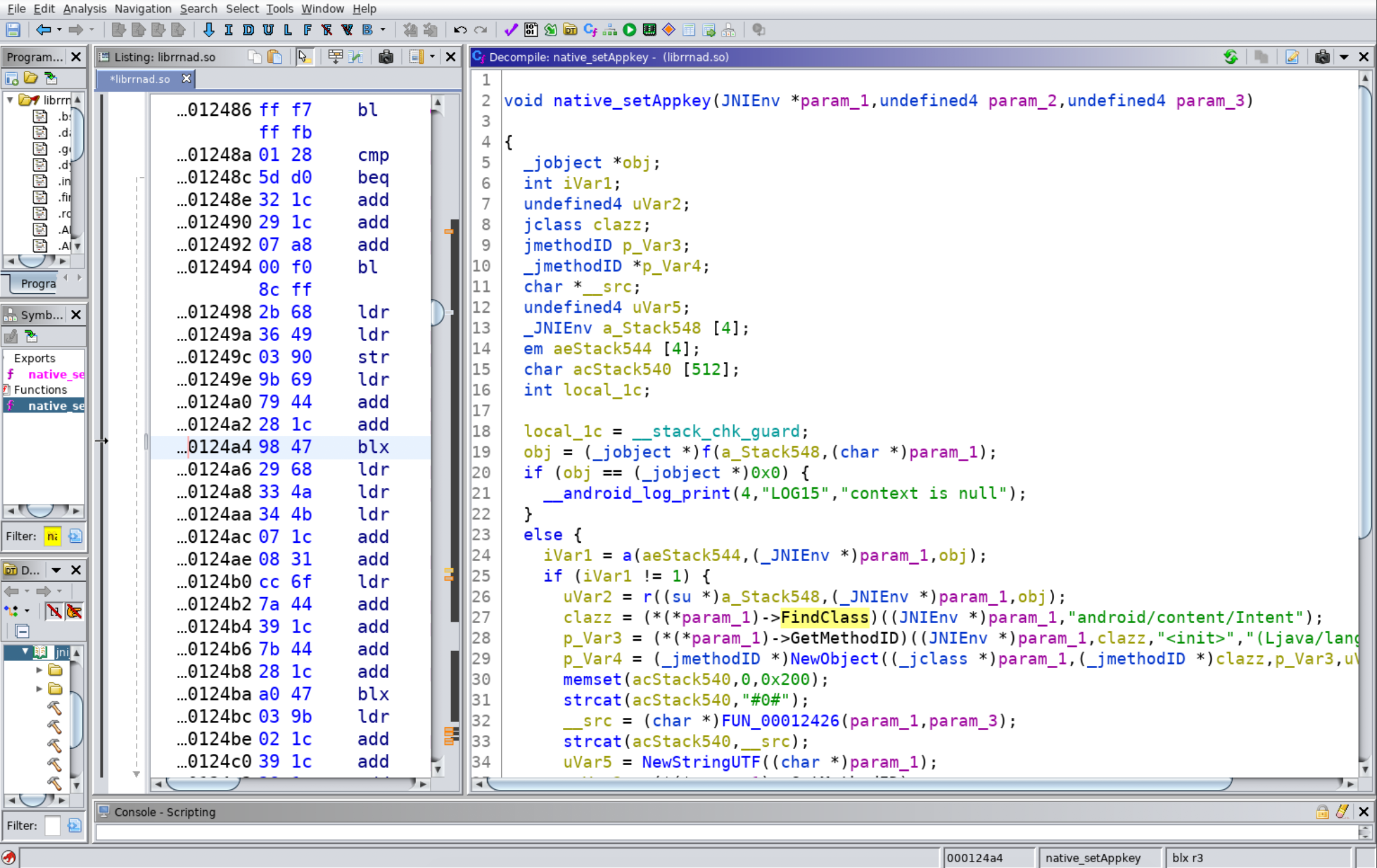
@ -259,21 +254,21 @@ Therefore `blx r3` on line 0x124a4 is calling `FindClass`. We can look up inform
|
|||
|
||||
|
||||
|
||||
Thankfully, there’s a way to get the JNI function without doing all of this manually! In both the Ghidra and IDA Pro decompilers you can re-type the first argument in JNI functions to `JNIEnv *` type and it will automatically identify the JNI Functions being called. In IDA Pro, this work out of the box. In Ghidra, you have to load the JNI types (either the jni.h file or a Ghidra Data Types archive of the jni.h file) first. For ease, we will load the JNI types from the Ghidra Data Types archive (gdt) produced by Ayrx and available [here](https://github.com/Ayrx/JNIAnalyzer/blob/master/JNIAnalyzer/data/jni_all.gdt). For ease, this file is available in the VM at `~/jni_all.gdt`.
|
||||
Thankfully, there’s a way to get the JNI function without doing all of this manually! In both the Ghidra and IDA Pro decompilers you can re-type the first argument in JNI functions to `JNIEnv *` type and it will automatically identify the JNI Functions being called. In IDA Pro, this work out of the box. In Ghidra, you have to load the JNI types (either the jni.h file or a Ghidra Data Types archive of the jni.h file) first. For ease, we will load the JNI types from the Ghidra Data Types archive (gdt) produced by Ayrx and available [here](https://github.com/Ayrx/JNIAnalyzer/blob/master/JNIAnalyzer/data/jni\_all.gdt). For ease, this file is available in the VM at `~/jni_all.gdt`.
|
||||
|
||||
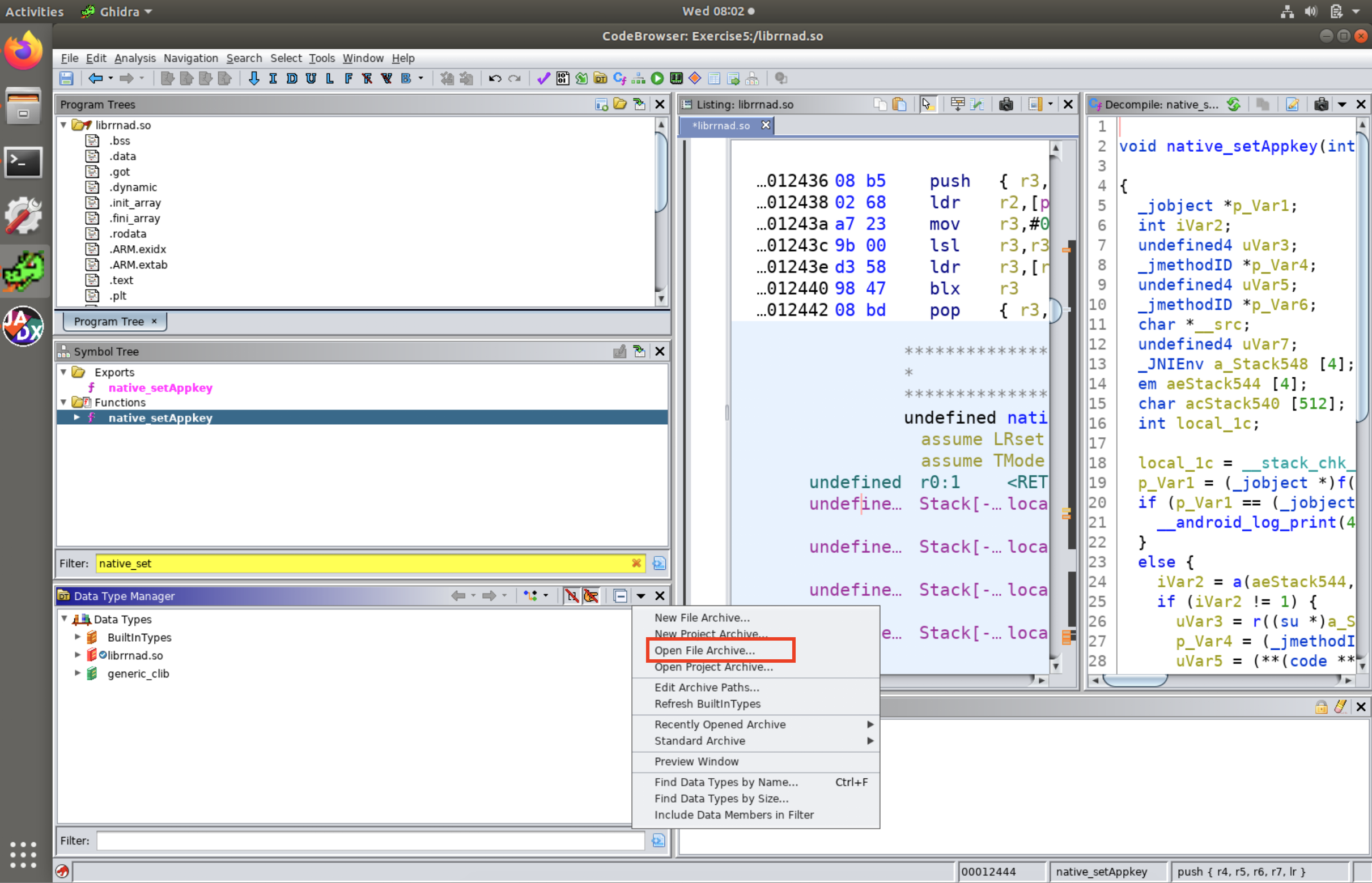
To load it for use in Ghidra, in the Data Type Manager Window, click on the down arrow in the right-hand corner and select “Open File Archive”.
|
||||
|
||||
|
||||
|
||||
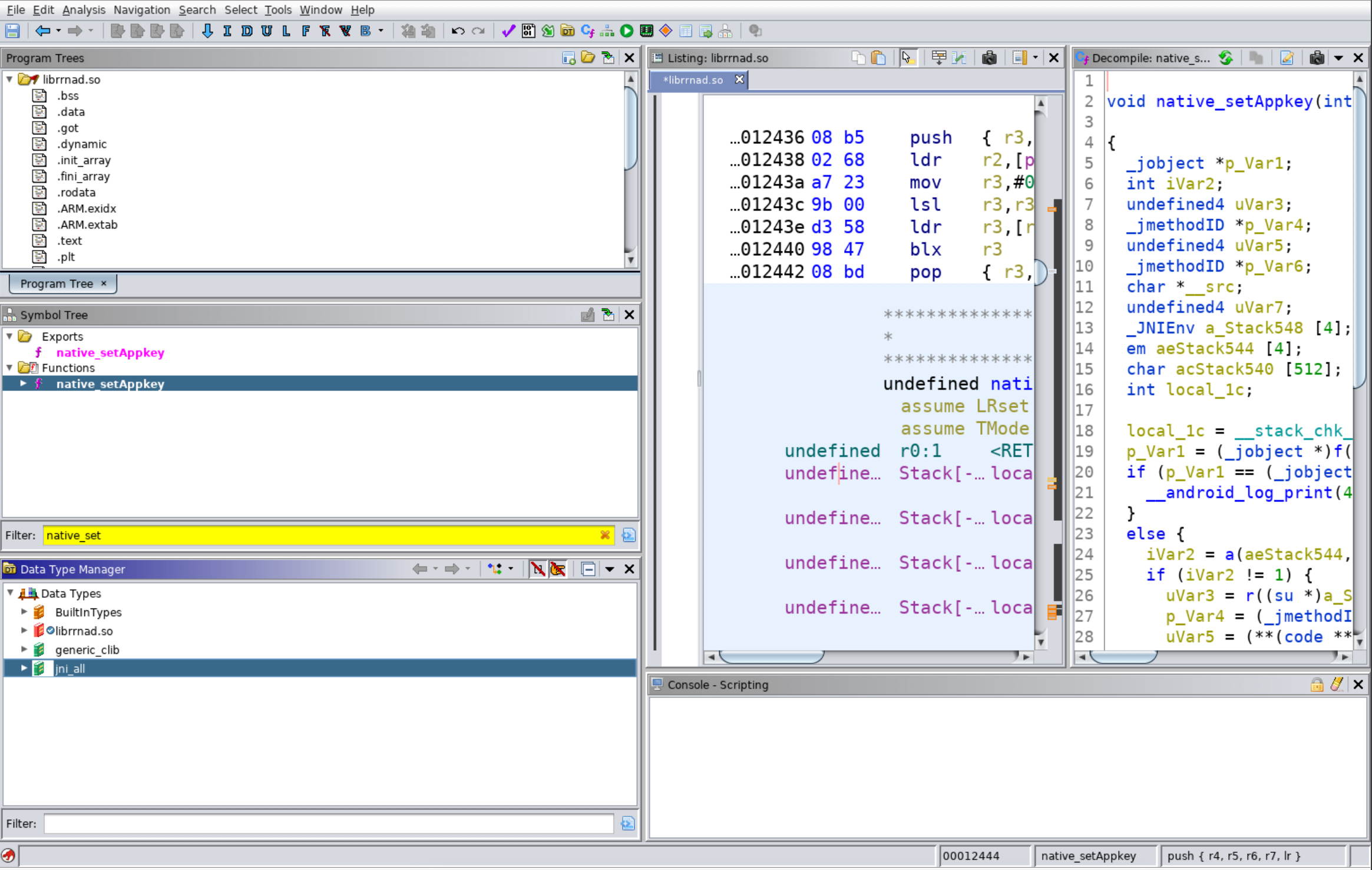
Then select `jni_all.gdt` file to load. Once it’s loaded, you should see jni_all in the Data Type Manager List as shown below.
|
||||
Then select `jni_all.gdt` file to load. Once it’s loaded, you should see jni\_all in the Data Type Manager List as shown below.
|
||||
|
||||
|
||||
|
||||
|
||||
Once this is loaded in Ghidra, you can then select any argument types in the decompiler and select “Retype Variable”. Set the new type to JNIEnv \*. This will cause the decompiler to now show the names of the JNIFunctions called rather than the offsets from the pointer.
|
||||
|
||||
|
||||
|
||||
|
||||
### Exercise #6 - Find and Reverse the Native Function <a href="exercise-6---find-and-reverse-the-native-function" id="exercise-6---find-and-reverse-the-native-function"></a>
|
||||
#### Exercise #6 - Find and Reverse the Native Function <a href="#exercise-6---find-and-reverse-the-native-function" id="exercise-6---find-and-reverse-the-native-function"></a>
|
||||
|
||||
We are going to point all of our previous skills together: identifying starting points for RE, reversing DEX, and reversing native code to analyze an application that may have moved its harmful behaviors in native code. The sample is `~/samples/HDWallpaper.apk`.
|
||||
|
||||
|
|
@ -296,21 +291,18 @@ Go on and reverse!
|
|||
|
||||
**Solution**
|
||||
|
||||
## **JEB - Debug Android Native Libraries**
|
||||
|
||||
**Checkout this blog:** [**https://medium.com/@shubhamsonani/how-to-debug-android-native-libraries-using-jeb-decompiler-eec681a22cf3**](https://medium.com/@shubhamsonani/how-to-debug-android-native-libraries-using-jeb-decompiler-eec681a22cf3)
|
||||
|
||||
<details>
|
||||
|
||||
<summary><a href="https://cloud.hacktricks.xyz/pentesting-cloud/pentesting-cloud-methodology"><strong>☁️ HackTricks Cloud ☁️</strong></a> -<a href="https://twitter.com/hacktricks_live"><strong>🐦 Twitter 🐦</strong></a> - <a href="https://www.twitch.tv/hacktricks_live/schedule"><strong>🎙️ Twitch 🎙️</strong></a> - <a href="https://www.youtube.com/@hacktricks_LIVE"><strong>🎥 Youtube 🎥</strong></a></summary>
|
||||
|
||||
- Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
|
||||
- Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
|
||||
- Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
|
||||
- **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
|
||||
|
||||
- **Share your hacking tricks by submitting PRs to the [hacktricks repo](https://github.com/carlospolop/hacktricks) and [hacktricks-cloud repo](https://github.com/carlospolop/hacktricks-cloud)**.
|
||||
* Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
* Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
* Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
* **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks\_live)**.**
|
||||
* **Share your hacking tricks by submitting PRs to the** [**hacktricks repo**](https://github.com/carlospolop/hacktricks) **and** [**hacktricks-cloud repo**](https://github.com/carlospolop/hacktricks-cloud).
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
|
|||
|
|
@ -7,15 +7,14 @@
|
|||
* Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
* Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
* Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
* **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
|
||||
* **Share your hacking tricks by submitting PRs to the [hacktricks repo](https://github.com/carlospolop/hacktricks) and [hacktricks-cloud repo](https://github.com/carlospolop/hacktricks-cloud)**.
|
||||
* **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks\_live)**.**
|
||||
* **Share your hacking tricks by submitting PRs to the** [**hacktricks repo**](https://github.com/carlospolop/hacktricks) **and** [**hacktricks-cloud repo**](https://github.com/carlospolop/hacktricks-cloud).
|
||||
|
||||
</details>
|
||||
|
||||
## Regex Bypasses
|
||||
Different techniques can be used to bypass the regex filters on the firewalls. Examples include alternating case, adding line breaks,
|
||||
and encoding payloads. Resources for the various bypasses can be found at [PayloadsAllTheThings](https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/XSS%20Injection/README.md#filter-bypass-and-exotic-payloads)
|
||||
and [OWASP](https://cheatsheetseries.owasp.org/cheatsheets/XSS_Filter_Evasion_Cheat_Sheet.html). The examples below were pulled from [this article](https://medium.com/@allypetitt/5-ways-i-bypassed-your-web-application-firewall-waf-43852a43a1c2).
|
||||
|
||||
Different techniques can be used to bypass the regex filters on the firewalls. Examples include alternating case, adding line breaks, and encoding payloads. Resources for the various bypasses can be found at [PayloadsAllTheThings](https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/XSS%20Injection/README.md#filter-bypass-and-exotic-payloads) and [OWASP](https://cheatsheetseries.owasp.org/cheatsheets/XSS\_Filter\_Evasion\_Cheat\_Sheet.html). The examples below were pulled from [this article](https://medium.com/@allypetitt/5-ways-i-bypassed-your-web-application-firewall-waf-43852a43a1c2).
|
||||
|
||||
```bash
|
||||
<sCrIpT>alert(XSS)</sCriPt> #changing the case of the tag
|
||||
|
|
@ -38,7 +37,6 @@ data:text/html;base64,PHN2Zy9vbmxvYWQ9YWxlcnQoMik+ #base64 encoding the javascri
|
|||
<BODY onload!#$%&()*~+-_.,:;?@[/|\]^`=confirm()> # use any chars that aren't letters, numbers, or encapsulation chars between event handler and equal sign (only works on Gecko engine)
|
||||
```
|
||||
|
||||
|
||||
## Charset Encoding
|
||||
|
||||
```bash
|
||||
|
|
@ -72,8 +70,8 @@ Content-Length: 61
|
|||
```
|
||||
|
||||
## Unicode Compatability
|
||||
Depending on the implementation of Unicode normalization (more info [here](https://jlajara.gitlab.io/Bypass_WAF_Unicode)), characters that share Unicode
|
||||
compatability may be able to bypass the WAF and execute as the intended payload. Compatible characters can be found [here](https://www.compart.com/en/unicode)
|
||||
|
||||
Depending on the implementation of Unicode normalization (more info [here](https://jlajara.gitlab.io/Bypass\_WAF\_Unicode)), characters that share Unicode compatability may be able to bypass the WAF and execute as the intended payload. Compatible characters can be found [here](https://www.compart.com/en/unicode)
|
||||
|
||||
### Example
|
||||
|
||||
|
|
@ -87,6 +85,10 @@ compatability may be able to bypass the WAF and execute as the intended payload.
|
|||
|
||||
It's common in cloud based WAFs that if the payload is bigger than X size, the request won't be checked by the WAF. You can simply use that to bypass them.
|
||||
|
||||
### IP Rotation
|
||||
|
||||
* [https://github.com/rootcathacking/catspin](https://github.com/rootcathacking/catspin)
|
||||
|
||||
<details>
|
||||
|
||||
<summary><a href="https://cloud.hacktricks.xyz/pentesting-cloud/pentesting-cloud-methodology"><strong>☁️ HackTricks Cloud ☁️</strong></a> -<a href="https://twitter.com/hacktricks_live"><strong>🐦 Twitter 🐦</strong></a> - <a href="https://www.twitch.tv/hacktricks_live/schedule"><strong>🎙️ Twitch 🎙️</strong></a> - <a href="https://www.youtube.com/@hacktricks_LIVE"><strong>🎥 Youtube 🎥</strong></a></summary>
|
||||
|
|
@ -94,7 +96,7 @@ It's common in cloud based WAFs that if the payload is bigger than X size, the r
|
|||
* Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
* Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
* Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
* **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
|
||||
* **Share your hacking tricks by submitting PRs to the [hacktricks repo](https://github.com/carlospolop/hacktricks) and [hacktricks-cloud repo](https://github.com/carlospolop/hacktricks-cloud)**.
|
||||
* **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks\_live)**.**
|
||||
* **Share your hacking tricks by submitting PRs to the** [**hacktricks repo**](https://github.com/carlospolop/hacktricks) **and** [**hacktricks-cloud repo**](https://github.com/carlospolop/hacktricks-cloud).
|
||||
|
||||
</details>
|
||||
|
|
|
|||
Loading…
Reference in a new issue