<summary><strong>Impara l'hacking di AWS da zero a eroe con</strong><ahref="https://training.hacktricks.xyz/courses/arte"><strong>htARTE (HackTricks AWS Red Team Expert)</strong></a><strong>!</strong></summary>
* Se vuoi vedere la tua **azienda pubblicizzata su HackTricks** o **scaricare HackTricks in PDF** Controlla i [**PACCHETTI DI ABBONAMENTO**](https://github.com/sponsors/carlospolop)!
* Ottieni il [**merchandising ufficiale di PEASS & HackTricks**](https://peass.creator-spring.com)
* Scopri [**The PEASS Family**](https://opensea.io/collection/the-peass-family), la nostra collezione di [**NFT esclusivi**](https://opensea.io/collection/the-peass-family)
* **Unisciti al** 💬 [**gruppo Discord**](https://discord.gg/hRep4RUj7f) o al [**gruppo telegram**](https://t.me/peass) o **seguici** su **Twitter** 🐦 [**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
* **Condividi i tuoi trucchi di hacking inviando PR a** [**HackTricks**](https://github.com/carlospolop/hacktricks) e [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repos.
SAP sta per Systems Applications and Products in Data Processing. SAP, per definizione, è anche il nome del software ERP \(Enterprise Resource Planning\) così come il nome dell'azienda.
Il sistema SAP è composto da una serie di moduli completamente integrati, che coprono praticamente ogni aspetto della gestione aziendale.
Ogni istanza SAP \(o SID\) è composta da tre livelli: database, applicazione e presentazione\), ogni ambiente di sviluppo di solito è composto da quattro istanze: dev, test, QA e produzione.
Ogni livello può essere sfruttato in qualche misura, ma il maggior effetto può essere ottenuto **attaccando il database**.
> La sezione successiva è principalmente tratta da [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures) dell'utente shipcod3!
* Controlla il campo di applicazione o il riepilogo del programma per il testing. Prendi nota dei nomi host o delle istanze di sistema per la connessione a SAP GUI.
* Utilizza OSINT \(open source intelligence\), Shodan e Google Dorks per verificare la presenza di file, sottodomini e informazioni interessanti se l'applicazione è accessibile via Internet o pubblica:
* Utilizza nmap per verificare le porte aperte e i servizi noti (router sap, webdnypro, servizi web, server web, ecc.)
* Esegui il crawling degli URL se è in esecuzione un server web.
* Fuzzare le directory (puoi utilizzare Burp Intruder) se ci sono server web su determinate porte. Ecco alcuni buoni wordlist forniti dal progetto SecLists per trovare percorsi SAP ICM predefiniti e altre directory o file interessanti:
* Verificare le credenziali predefinite (Nella tassonomia di valutazione delle vulnerabilità di Bugcrowd, questo è considerato come P1 -> Configurazione errata della sicurezza del server \| Utilizzo di credenziali predefinite \| Server di produzione):
* Esegui Wireshark, quindi autenticati al client (SAP GUI) utilizzando le credenziali ottenute perché alcuni client trasmettono le credenziali senza SSL. Ci sono due plugin noti per Wireshark che possono analizzare gli header principali utilizzati dal protocollo SAP DIAG: il plugin di dissezione SAP di SecureAuth Labs e il plugin SAP DIAG di Positive Research Center.
* Verifica le scalate di privilegi utilizzando alcuni codici di transazione SAP (tcodes) per gli utenti a basso privilegio:
* SU01 - Per creare e mantenere gli utenti
* SU01D - Per visualizzare gli utenti
* SU10 - Per la manutenzione di massa
* SU02 - Per la creazione manuale dei profili
* SM19 - Audit di sicurezza - configurazione
* SE84 - Sistema informativo per le autorizzazioni SAP R/3
* Verifica se puoi eseguire comandi di sistema / eseguire script nel client.
* Verifica se puoi eseguire XSS su BAPI Explorer.
# Test dell'interfaccia web
* Esplora gli URL (vedi fase di scoperta).
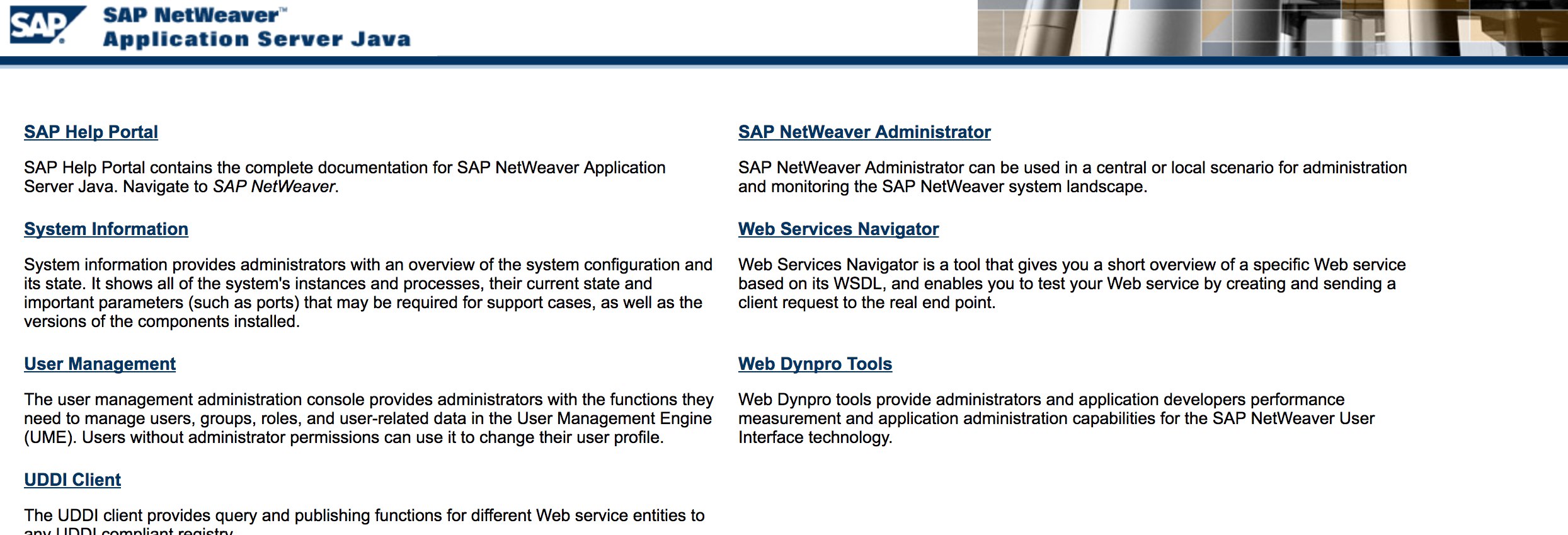
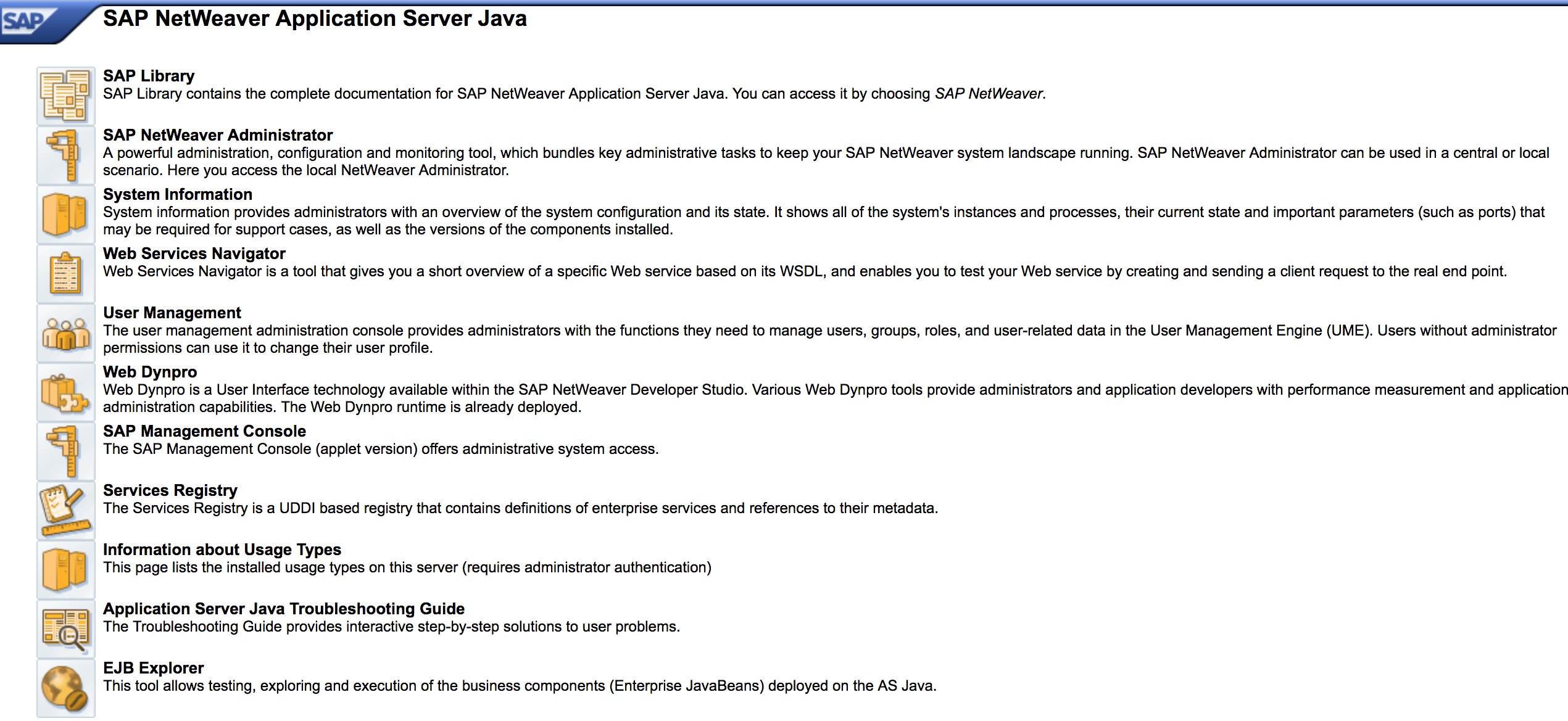
* Fai il fuzzing degli URL come nella fase di scoperta. Ecco come appare [http://SAP:50000/index.html](http://sap:50000/index.html):
* Cerca vulnerabilità web comuni (fare riferimento a OWASP Top 10) perché ci sono vulnerabilità XSS, RCE, XXE, ecc. in alcuni punti.
* Dai un'occhiata alla metodologia di Jason Haddix [“The Bug Hunters Methodology”](https://github.com/jhaddix/tbhm) per testare le vulnerabilità web.
* Bypass dell'autenticazione tramite manipolazione del verbo? Forse :)
* Apri `http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#` quindi premi il pulsante "Choose" e poi nella finestra aperta premi "Search". Dovresti essere in grado di vedere un elenco di utenti SAP (Riferimento alla vulnerabilità: [ERPSCAN-16-010](https://erpscan.com/advisories/erpscan-16-010-sap-netweaver-7-4-information-disclosure/))
* Le credenziali vengono inviate tramite HTTP? In tal caso, viene considerato come P3 in base alla [Vulnerability Rating Taxonomy](https://bugcrowd.com/vulnerability-rating-taxonomy) di Bugcrowd: Autenticazione non valida e gestione delle sessioni | Funzione di accesso debole tramite HTTP. Suggerimento: Dai un'occhiata anche a [http://SAP:50000/startPage](http://sap:50000/startPage) o ai portali di accesso :)
* Prova `/irj/go/km/navigation/` per possibili elenchi di directory o bypass dell'autenticazione
* [http://SAP/sap/public/info](http://sap/sap/public/info) contiene alcune informazioni interessanti:
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
* Prova ad utilizzare alcuni exploit noti (controlla Exploit-DB) o attacchi come il vecchio ma affidabile "Esecuzione remota del codice di SAP ConfigServlet" nel SAP Portal:
* Prima di eseguire il comando `start` nello script bizploit nella fase di Discovery, è possibile aggiungere anche quanto segue per eseguire una valutazione delle vulnerabilità:
* [SAP NetWeaver ABAP security configuration part 3: Default passwords for access to the application](https://erpscan.com/press-center/blog/sap-netweaver-abap-security-configuration-part-2-default-passwords-for-access-to-the-application/)
* [Elenco dei codici di transazione ABAP relativi alla sicurezza SAP](https://wiki.scn.sap.com/wiki/display/Security/List+of+ABAP-transaction+codes+related+to+SAP+security)
* [Le 10 vulnerabilità e attacchi SAP più interessanti](https://erpscan.com/wp-content/uploads/presentations/2012-Kuwait-InfoSecurity-Top-10-most-interesting-vulnerabilities-and-attacks-in-SAP.pdf)
* [Valutazione della sicurezza degli ecosistemi SAP con bizploit: Discovery](https://www.onapsis.com/blog/assessing-security-sap-ecosystems-bizploit-discovery)
<summary><strong>Impara l'hacking di AWS da zero a eroe con</strong><ahref="https://training.hacktricks.xyz/courses/arte"><strong>htARTE (HackTricks AWS Red Team Expert)</strong></a><strong>!</strong></summary>
* Se vuoi vedere la tua **azienda pubblicizzata in HackTricks** o **scaricare HackTricks in PDF** Controlla i [**PACCHETTI DI ABBONAMENTO**](https://github.com/sponsors/carlospolop)!
* Ottieni il [**merchandising ufficiale di PEASS & HackTricks**](https://peass.creator-spring.com)
* Scopri [**The PEASS Family**](https://opensea.io/collection/the-peass-family), la nostra collezione di esclusive [**NFT**](https://opensea.io/collection/the-peass-family)
* **Unisciti al** 💬 [**gruppo Discord**](https://discord.gg/hRep4RUj7f) o al [**gruppo telegram**](https://t.me/peass) o **seguici** su **Twitter** 🐦 [**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
* **Condividi i tuoi trucchi di hacking inviando PR ai** [**HackTricks**](https://github.com/carlospolop/hacktricks) e [**HackTricks Cloud**](https://github.com/carlospolop/hacktricks-cloud) github repos.